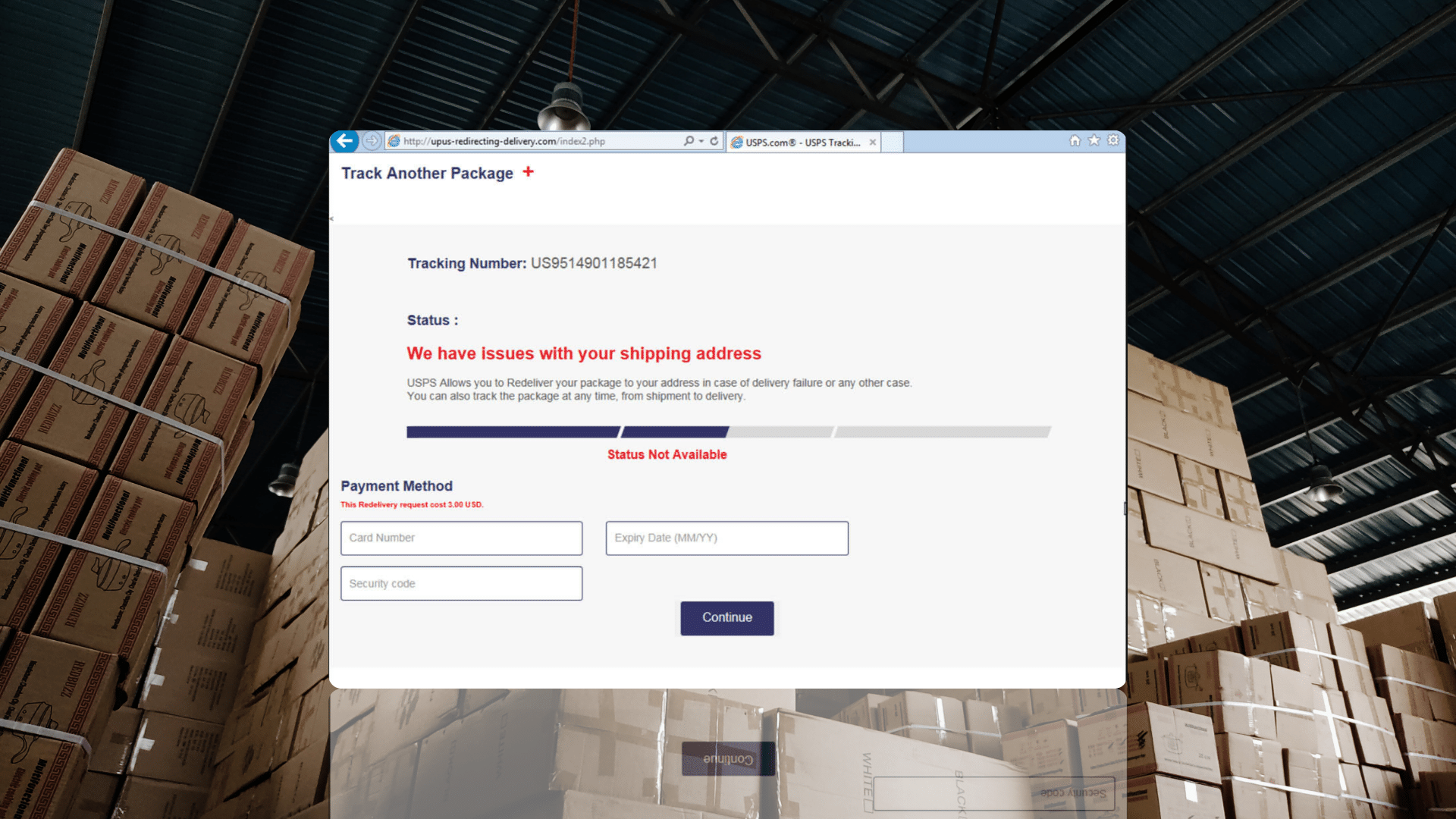
If, like me, you regularly use the international postal system to send parcels to friends abroad, you will be familiar with tracking pages like that of the United States Postal Service. And if, like me, you have at times been frustrated with parcels that sometimes disappear for weeks from tracking systems, you will understand someone may be keen to open a link to a site that looks like USPS to learn when a parcel will be delivered and then even enter their credit card details to pay a supposed $3 redelivery fee.

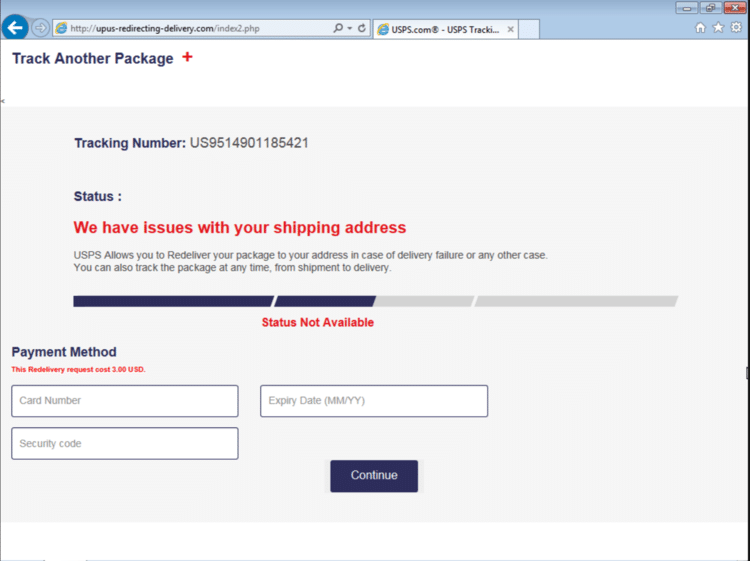
This site is of course fake and set up to phish for credit card and address details.
The domain, upus-redirecting-delivery[.]com, was registered only yesterday at REG.ru, a Russian domain registrar, and hosted at 185.185.70[.]247, which belongs to Sprinthost (AS35278), a web hosting company also based in Russia.
The IP address is part of a bulletproof hosting network that cycles through IP addresses quickly and of which the IP addresses serve as proxies for the actual content served. The domain is likely to soon move to another IP address at a different network and so on, until it is eventually taken down.
Indeed, the related but slightly older domain upus-delivery-repayment[.]com (registered on the 1st of January of this year) was initially hosted at 109.234.36[.]121 (AS48282, VDSINA; also Russia) before moving to 185.185.70[.]247. It has since been taken down.
In its short lifespan, the domain will probably have made its owners enough money to make it worth it, while the use of a bulletproof hosting network means that the real infrastructure behind this phishing campaign remains hidden to both security researchers and law enforcement.
The bulletproof hosting network, which we internally track under the name ‘Sasha’, has hosted many phishing domains, but also malware C&C domains, web skimmers (Magecart) and cryptocurrency scams.