New Finance Scam Discovered Abusing Niche X/Twitter Advertising Loophole
Key Findings
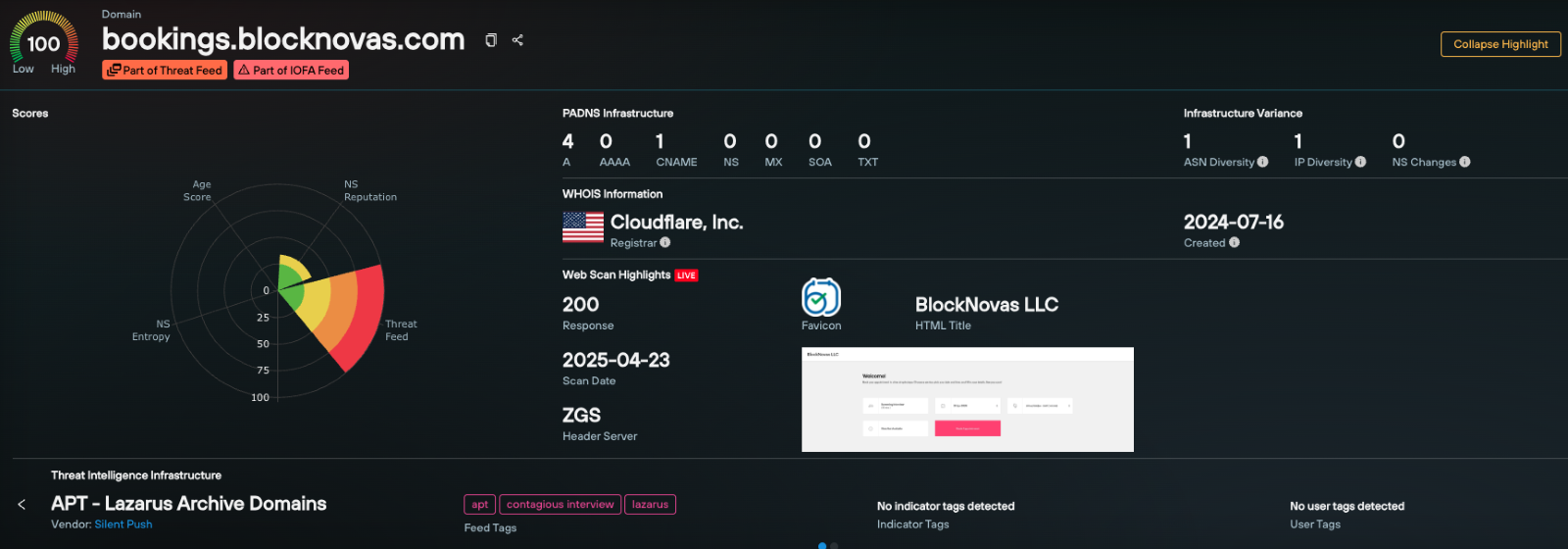
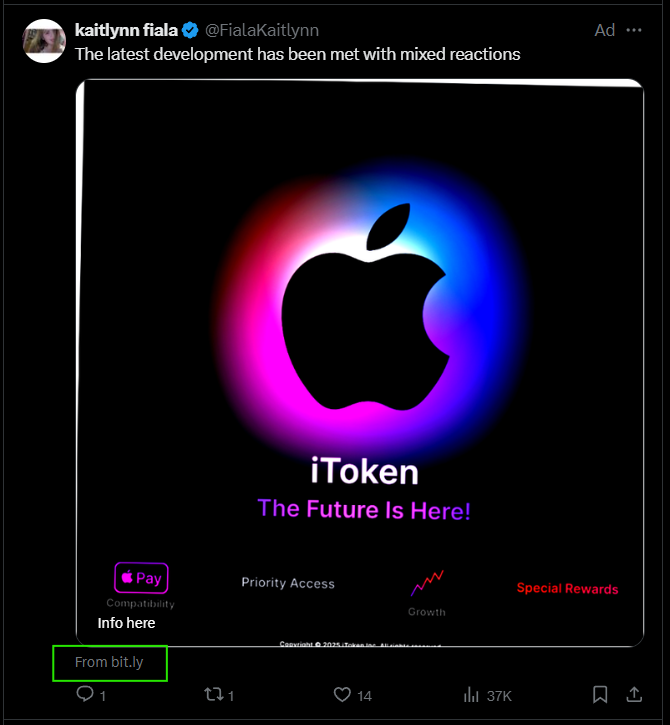
- Silent Push Threat Analysts have uncovered a new finance scam exploiting an X/Twitter advertising display URL feature to spoof “cnn[.]com” while directing visitors to a crypto scam website impersonating Apple’s brand.
- When testing the redirect found in the ad, our team found that a user is not taken to “cnn[.]com,” but instead to ipresale[.]world, which features a classic cryptocurrency “presale scam.”
- The scam encourages visitors to create an account and buy a token positioned as coming from Apple; the website also includes a fake testimonial from Apple CEO Tim Cook.
- There were 22 wallet options for sending money into the scam, and each website within the network has/had unique crypto wallets.
- We found nearly 90 sites going back to 2024, with almost identical financial lures, all appearing to be from the same threat actor group. The ipresale[.]world campaign was the first example found that purchased X/Twitter advertising with a spoofed display URL.
Executive Summary
Silent Push Threat Analysts discovered an X/Twitter post on May 1, 2025, promoting the non-existent product, “Apple iToken.” The advertising display URL showed “From CNN[.]com,” which appeared to be done via a known exploit for spoofing a URL on X/Twitter.
![Screenshot of the X/Twitter ad abusing Apple's brand and spoofing cnn[.]com](https://www.silentpush.com/wp-content/uploads/x-twit-apple-ad-image-1.png)
This campaign is abusing a known loophole in X/Twitter display URLs. In March 2024, Bleeping Computer reported on a similar cryptocurrency scam that spoofed the forbes[.]com domain on X/Twitter.
The simplest way to explain how this is done is that the exploit is possible on X/Twitter because of a few features:
- When an X/Twitter user inputs a URL into a tweet, Twitter sends their bot to request the page and load up metadata via a Twitter card.
- The Twitter bot uses a consistent User Agent (UA) string. The UA string is a device’s declaration to a server that helps ensure the correct version of a page can be served. However, this also allows a server to identify a request from a real browser compared to a request from something like Twitter’s bot.
- A malicious actor can then redirect the Twitter bot to one page, like cnn[.]com or forbes[.]com, while redirecting real visitors to their chosen (i.e. malicious) landing page.
- Afterwards, Twitter will show a card for the content it was redirected to—in this instance, the benign cnn[.]com domain, despite those who click the link being redirected to a separate domain.
A similar version of this spoofing effort can be done using URL shorteners, as in this current live example. The threat actors merely set up the URL shortener to initially redirect people to a benign website like CNN[.]com. After submitting the URL to Twitter and posting the card with the CNN metadata, they then updated the URL shortener with a new URL so that it sends everyone else to the new destination.
After the final X/Twitter redirect, the visitor is taken to ipresale[.]world, which features the previously mentioned classic cryptocurrency “presale scam,” encouraging them to navigate the process of creating an account and buy an “iToken” that’s positioned as coming from Apple.
Table of contents
- Key Findings
- Executive Summary
- Sign Up for a Free Silent Push Community Edition Account
- Background
- Details About the ipresale[.]world Pages and Purchase Process
- New Twitter Ad and Website Indicate Ongoing Campaign
- Pivoting into More Cryptocurrency Scam Websites
- Pivoting on the chopinkos[.]digital Redirection Domain
- Dedicated IP Address Used by Crypto Investment Scammers
- Continuing to Track the New Finance Scheme Abusing Apple and X/Twitter
- Threat Mitigation
- Indicators Of Future Attack TM (IOFA TM ) List
Sign Up for a Free Silent Push Community Edition Account
Register now for our free Community Edition to use all the tools and queries highlighted in this blog.
Background
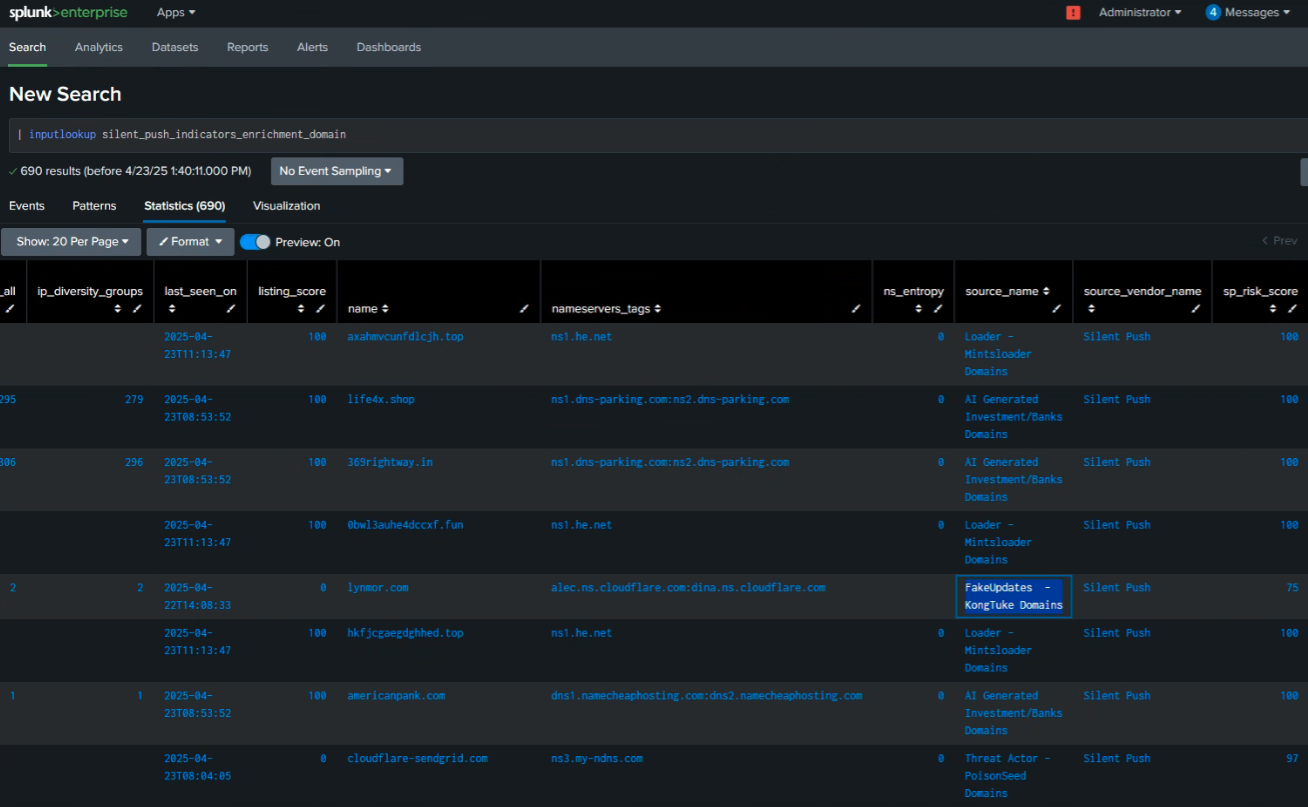
The initial X/Twitter ad appeared to come “From CNN[.]com.” However, if one clicks on the ad, the chain actually goes through the following URLs:
- bit[.]ly/4k4X1Tz
- t[.]co/OswjDCIcFI
- ipresale[.]world/
The first Bitly URL was created on May 1, 2025, at 19:22 UTC – likely right before the ad launched on X/Twitter:
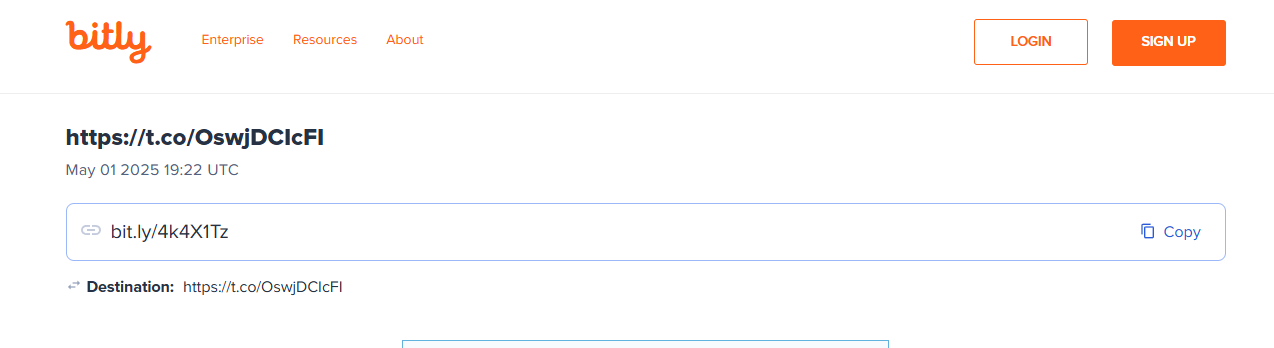
The Bitly URL redirects to an X/Twitter URL-shortened link, t[.]co/OswjDCIcFI, essentially returning the user to Twitter before redirecting to the final domain in the scheme.
It appeared that the original user who paid for and posted the X/Twitter ad posted a separate tweet linking to this domain and then copied the X/Twitter tracking URL to embed into the Bitly redirect flow.
After the final X/Twitter redirect, the visitor was taken to ipresale[.]world, which featured a classic crypto “presale scam.” The website spoofing Apple and a fake “iToken” product even includes a phony endorsement from Apple CEO Tim Cook during the crypto scam sales completion step.
Details About the ipresale[.]world Pages and Purchase Process
![Screenshot of the site ipresale[.]world](https://www.silentpush.com/wp-content/uploads/x-twit-ipresaleworld-image-3.png)
If you click on the “Buy Now” link, you’re taken to a “/register” page that further features (and abuses) the Apple brand:
![The Register page on ipresale[.]world](https://www.silentpush.com/wp-content/uploads/x-twit-login-image-4.png)
We tested the account creation process, and once we logged in, the interface looked like this:
![Screenshot of the Buy Tokens page on ipresale[.]world](https://www.silentpush.com/wp-content/uploads/x-twit-buy-tokens-image-5.png)
Here is a short video that shows the process to buy an “iToken” via Bitcoin:
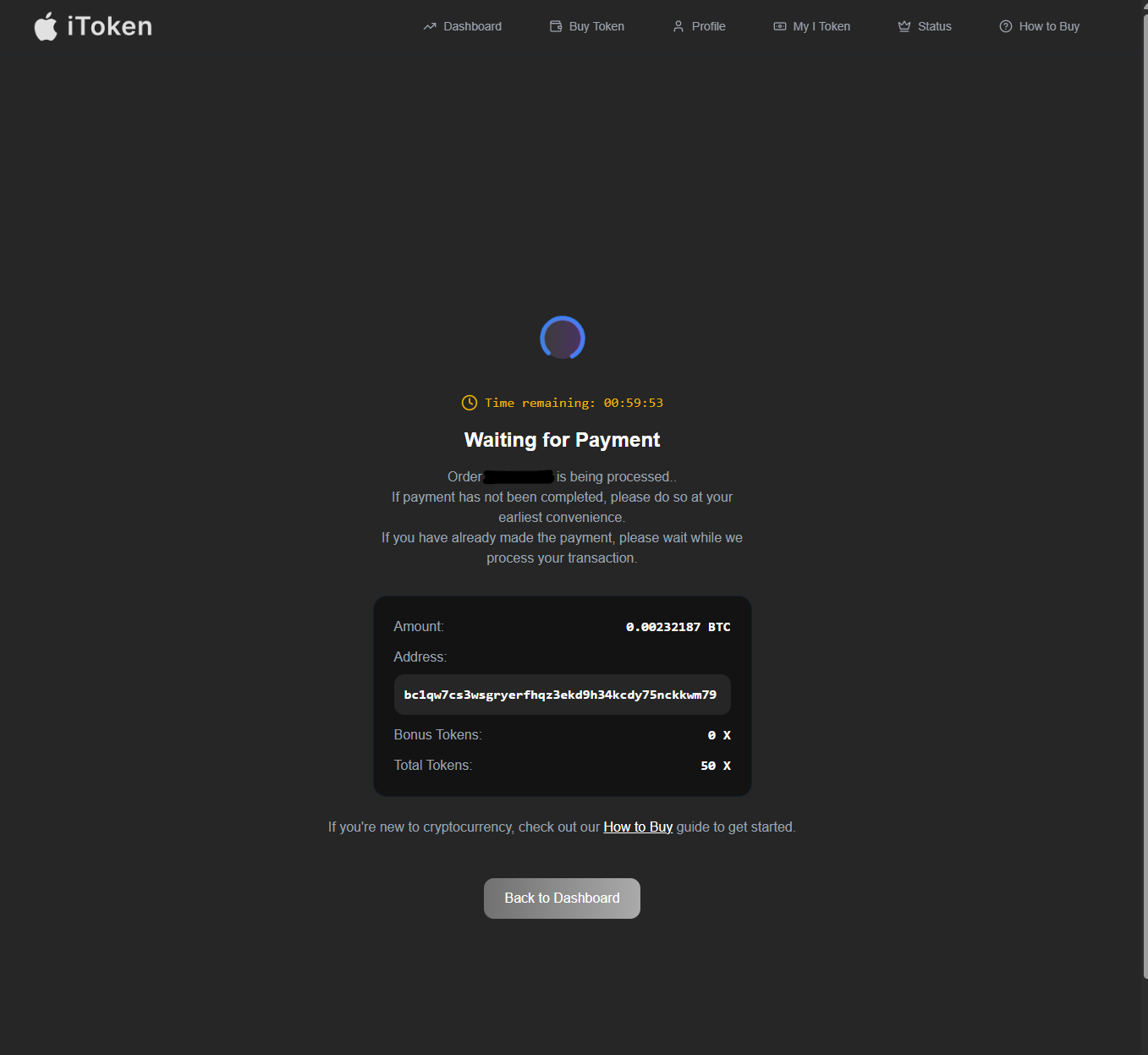
There were 22 wallet options for sending money into this scam. Since we found the scam site early after it was launched, there were no transactions at the time of our initial checks on the wallets:
- Bitcoin: bc1qw7cs3wsgryerfhqz3ekd9h34kcdy75nckkwm79
- Ethereum: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- XRP: rBHmEDWWLcHotT4CPAsTDXE6bibLvhJkAb
- USDT: TPcd4VVBxHANJSBmoXqNuSBJv3Uwc698kg
- TON: UQBoGdZs1wNwjP7jDmyMeMtuRAS0Iu9YvJtuRQ9kkpaRUmgY
- XLM: GCR6PHAVXIQM4ZVS5V2I4JW355DDRD5PFWEAPMEZKRMKGZS64BTTSYIW
- BCH: qzpdumzud7q3qdumkzmk3cgjz3v3hmhlxgylrkac06
- BNB: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- TRX: TPcd4VVBxHANJSBmoXqNuSBJv3Uwc698kg
- USDC ERC20: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- DASH: XrhJzDg4zqaTSgxwPoa4gdkMKksRgDRHHt
- WAVES: 3P6eR4Jq22z48WmMDEX982H3suXB353FCWx
- BUSD: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- ADA: addr1qxjlfj53m20s7w8fynxwzekfzwwxq7a2fm80q46cya5w6uwege7nej8arztk7ngskxlk4rq80zfe2z4c2sfe8fzw2l2q0240nm
- DOGE: DRawCZTyQNa9nmPcuYL7uHMLH1Khjkncs6
- SOL: 4UbupKa7DdMyHt2xJq5G8ucjLXb4SQRCxLhKYJu9NMrn
- UNI: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- CAKE: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- AVAX: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- DOT: 1j6CTKbhZSeKq2cH9MpV3hULn4qkCdZ2zYYWFfZ3h1DTEjv
- SHIB: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
- CRO: 0x2a4Ca7B6D5FEA094e02f152D712bFD49de6D3410
After initiating the process to send a payment into one of the wallets, a “Waiting for Payment” interstitial is loaded:
If you try to access the URL without a working orderID, the page gives an error:
![The ipresale[.]world site gave an error message of "No Data Found"](https://www.silentpush.com/wp-content/uploads/x-twit-error-msg-image-7.png)
If you click “Back to Dashboard,” you will see details about any transfers and a fake quote from Apple CEO Tim Cook.
![Example of the ipresale[.]world dashboard screen](https://www.silentpush.com/wp-content/uploads/x-twit-dashboard-view-image-8.png)
The phony Cook quote reads, “Excited for the future of blockchain with I Coin. Stage 3 presale is live at $4.5—next stop, $27.50. Secure, transparent, and built for the decentralized world ahead. Now’s the time. #ICoin #BlockchainFuture”
![Example of the ipresale[.]world dashboard with the fake Time Cook quote](https://www.silentpush.com/wp-content/uploads/x-twit-tcook-quote-image-9.png)
Other pages on the site included a “My Profile” page:
![Screenshot of My Profile page on ipresale[.]world](https://www.silentpush.com/wp-content/uploads/x-twit-my-profile-image-10.png)
The “My Token” page that follows would likely be populated with details if a funds transfer was successful. At the bottom of the page, “Recent Activity” included pending transactions:
![The My iToken page on ipresale[.]world](https://www.silentpush.com/wp-content/uploads/x-twit-my-itoken-image-11.png)
There was also a “Status Tiers” page – essentially a purchase loyalty program that the threat actor was promoting, which featured tiers for: Bronze, Silver, Gold, Platinum, Diamond, and Legendary.
Finally, there was a “How to Buy” page with additional instructions for purchasing tokens via crypto wallets or exchanges:
![Screenshot of the How to Buy page on ipresale[.]world](https://www.silentpush.com/wp-content/uploads/x-twit-how-to-buy-image-12.png)
New Twitter Ad and Website Indicate Ongoing Campaign
On May 5, 2025, Silent Push Threat Analysts picked up another X/Twitter ad from this campaign using the bit[.]ly domain shortener domain instead of a more prominent domain like cnn[.]com.
The tweet can be found here. It redirects through a third domain via a redirect flow like this:
- bit[.]ly/4iS1W9p
- chopinkos[.]digital
- itokensale[.]live/landing
![Screenshot of the Bitly redirect page showing a new domain: "chopinkos[.]digital"](https://www.silentpush.com/wp-content/uploads/x-twit-bitly-domain-image-2-1.png)
The “iToken” website (itokensale[.]live/landing) shown after the redirects was nearly identical to the first site that we found.
![Landing page of itokensale[.]live](https://www.silentpush.com/wp-content/uploads/x-twit-landing-page-image-15.png)
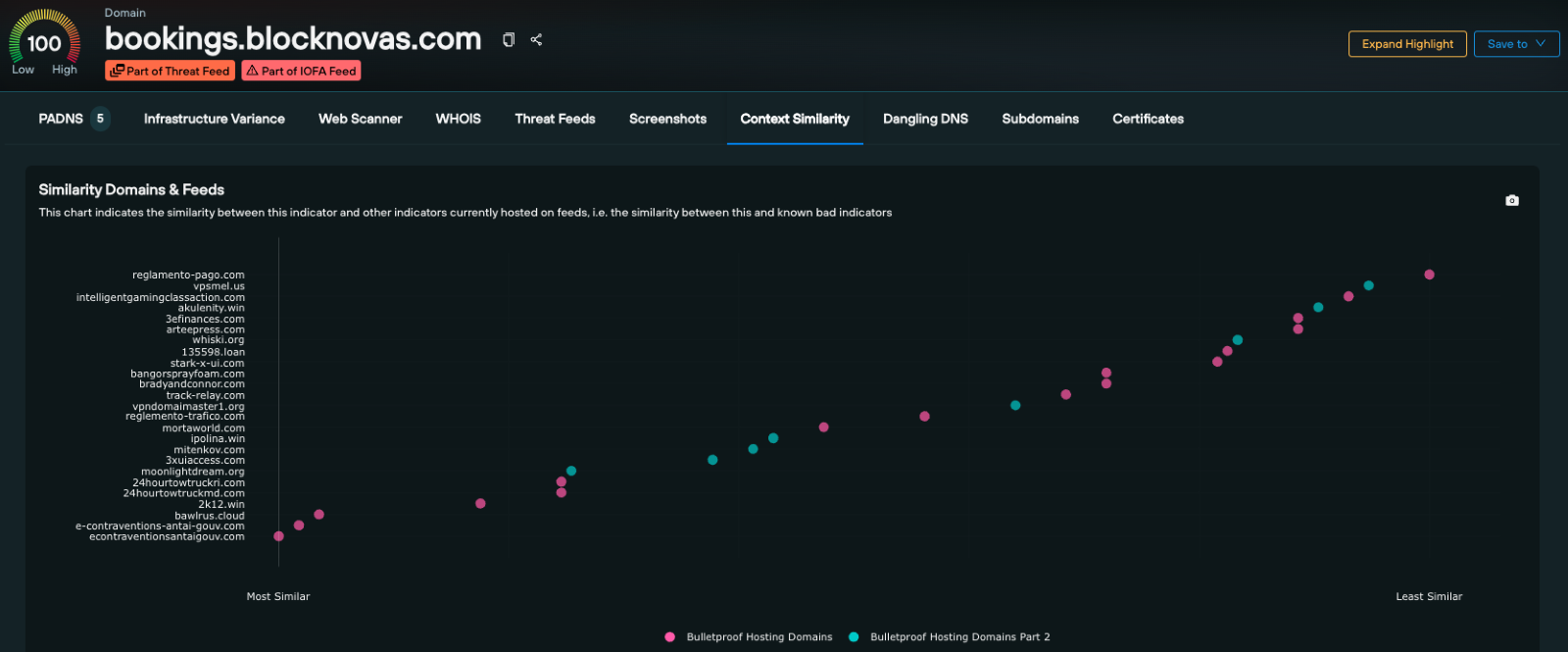
Pivoting into More Cryptocurrency Scam Websites
So, why cover this particular threat?
Because the domains found in pivots above, including ipresale[.]world, are a perfect use case for our new Silent Push “Web Resource Scan” data source, which provides essentially all the files that load on any scanned webpage, from HTML and CSS to images and JavaScript and everything in between.
We started this investigation by searching our new data source for the suspicious domain to expose all the files seen on that domain.
Web Scanner domain search query link
- datasource = [“webresources”] AND domain = “ipresale.world”
![Silent Push Web Resources domain search for "ipresale[.]world"](https://www.silentpush.com/wp-content/uploads/x-twit-web-scanner-1-image-16.png)
Analyzing the data our Web Resources Scan returned for the domain, we found a few different unique files were being reused across a grouping of similar domains:
- saved_resource.html
- SHA256: b976f96367b70125ec5241cb8e4848090cee6f7bff8cbed9bc01b61678ba6343
- 19 results
- index-BQ2l81Eq.css
- SHA256: f26aef6cf2a8e1de87fcec846af71b073e9d39947ed18f226e1ca159463c638d
- 19 results
The overlapping queries returned unique domains, all hosted on Hetzner (ASN24940):
- ipresale[.]world – ONLINE
- isale[.]ltd – ONLINE
- i-token[.]live – OFFLINE
- i-token[.]org – OFFLINE
- i-token[.]sale – OFFLINE
The other site that was live within the network looked identical to the first:
![Screenshot of isale[.]ltd fake token presale page](https://www.silentpush.com/wp-content/uploads/x-twit-isale-phase-alpha-image-17.png)
We can conduct a similar search for Web Resources Scan data from the domain we found used in the most recent X/Twitter ad campaign, itokensale[.]live. This resulted in the discovery of a similar CSS file and a SHA256 hash of that CSS file, which can be used to pivot into even more domains.
We started with a broad search for all files found in the Web Resources Scan data source for the itokensale[.]live domain.
Web Scanner Domain search query link
- datasource = [“webresources”] AND domain = “itokensale.live”
And if we grab the SHA256 for the “index-DIX1ewrp.css” file found above, we find it’s another solid pivot into more of these sites:
Web Scanner SHA256 search query link
- datasource = [“webresources”] AND sha256 = “5836f691a8657a91c16d2ff418d85afcddccf39804a9e8c7fe9d1fb838e12071”
The query above returned seven domains, all matching the previously-seen patterns:
- itokensale[.]live
- isale[.]run
- isale[.]live
- itoken[.]run
- itoken[.]foundation
- itoken[.]tech
- itoken[.]sale
Pivoting on the chopinkos[.]digital Redirection Domain
The most recent campaign included a redirect from chopinkos[.]digital to itokensale[.]live.
Investigating chopinkos[.]digital, we found that the domain was registered on May 5, 2025, on PublicDomainRegistry[.]com (PDR) and immediately weaponized.
The Silent Push Web Scanner picked up content from the newly registered domain, which included the HTML title “iToken,” hosted on Cloudflare (ASN13335) with the path “/landing”
These fingerprints can be searched to find even more of the domains used by this campaign, including some that look like this interstitial redirect domain.
Web Scanner HTML title + geoip.asn + path query link
- datasource = [“webscan”] AND htmltitle = “iToken” AND geoip.asn = 13335 AND path = “/landing”
The query above returned a few domains found via previous fingerprints, as well as some new ones:
- chopinkos[.]digital
- itokensale[.]live
- samsomisan[.]digital
- lopinak[.]com
- itoken[.]run
- blastindok[.]com
- itoken[.]foundation
- bestionkip[.]com
Pivoting into a Suspicious Name Server
The previously seen domain, isale[.]ltd, was registered on PDR on April 28, 2025, and mapped to an IP address on Hetzner the next day.
The NameServer records are for “ns1.chsw.host” + “ns2.chsw.host” – this “chsw.host” NS record is only used by 268 hosts, and many of its domains are suspect .ru sites, while others appeared to be financial scams.
After a review, it appears to be safe to block, or at least alert on, domains using this NameServer:
Silent Push Explore Indicator DNS Data search query link
- Reverse NS lookup for *.chsw.host
![Silent Push Community Edition of Explore Indicator DNS Data search for "*.chsw[.]host"](https://www.silentpush.com/wp-content/uploads/x-twit-explore-indicator-dns-image-19.png)
But within all the sites that used this NameServer were results from the previous file searches, along with a series of other domains that were live in 2024 and 2025 that appeared to target X/Twitter users with financial scams, as well as many that appeared to abuse Apple trademarks:
- x-token24[.]xyz
- elon-meme[.]org
- x-token24[.]org
- itoken2025[.]com
- i-token[.]xyz
- i-token[.]sale
- i-token[.]space
- i-token[.]org
- i-token[.]live
- itoken[.]site
- isale[.]ltd
- ipresale[.]world
Pivoting on Favicon Reuse
Across the previous pivots and domains found, four favicons were being reused within the campaign – three impersonate Apple and one impersonates X/Twitter:



These favicons are unique and exclusively used by this threat actor group. Knowing that, we could easily find even more of their sites with a simple query:
Web Scanner Favicon search query link
- datasource = [“webscan”] AND favicon_md5 = [“4f658b9a7d067de5238644b78d8d09cc”, “351088175f3645744cbd3b701ccce43a”, “e8c5c5829b630dcf61b55f271ac6c085”, “ccbc468b0f4f7e6e7615bb6743279d0c”]
This query returned 82 results, including some overlap from the previous queries, some dedicated IPs used, and some “random-looking domains” that appear to have been used for URL redirections (like the previously found “chopinkos[.]digital”).
Dedicated IP Address Used by Crypto Investment Scammers
Many of the domains that used the previous NameServer, including the X/Twitter/Apple crypto investment scam websites, were also mapped to a specific IP address:
51.15.17[.]214 hosted on ASN 12876 “Online SAS, FR”, which can be seen in our platform here:
https://explore.silentpush.com/explore-result?name=51.15.17.214&queryType=query&type=ANYIPV4
Continuing to Track the New Finance Scheme Abusing Apple and X/Twitter
While it’s no surprise that there are financial scams on X/Twitter, especially those that impersonate major brands, this most recent campaign’s ability to spoof the visible X advertising URL is a novel method for tricking potential victims, one only occasionally seen in the wild.
Given what our team uncovered during its research, the threat actor group behind this most recent X/Twitter advertising exploit is likely also behind many other similar domains and schemes.
This group also appears to have connections to numerous “.ru” domains. Although this can indicate ties to Russia, we have low confidence in that assessment. We will continue to track this campaign and share our findings as we learn more.
Threat Mitigation
Silent Push believes all domains related to this financial scam on X/Twitter offer some level of risk to individuals and organizations. We provide client-only Indicators Of Future AttackTM (IOFATM) feeds for tracking malicious threats’ and APT groups’ associated domains and IPs.
Silent Push IOFATM Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFATM Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Indicators Of Future AttackTM (IOFATM) List
Silent Push is sharing an IOFATM list we have associated with the new crypto scam abusing Apple and X/Twitter to support ongoing efforts within the community.
- 185[.]43[.]221[.]144
- 31[.]129[.]105[.]111
- 44[.]215[.]182[.]57
- 52[.]204[.]15[.]166
- 52[.]54[.]80[.]210
- 52[.]55[.]103[.]40
- 52[.]6[.]59[.]94
- 54[.]157[.]160[.]135
- 54[.]225[.]230[.]248
- 2025sale-x[.]com
- 2025token[.]space
- 2025xsale[.]digital
- accs343[.]xyz
- ajinkyap[.]dev
- alokozay[.]digital
- apollon-store[.]ru
- appleworld[.]com[.]mx
- appleworld[.]tech
- bestionkip[.]com
- blastindok[.]com
- cartaoapp[.]store
- chopinkos[.]digital
- cleversfor[.]com
- coin-x-presale[.]digital
- elon-meme[.]org
- elon-sale[.]live
- eshkere[.]digital
- finikistor[.]com
- gadget-universe[.]ru
- icoin2025[.]com
- i-coins[.]org
- i-finance[.]top
- i-foundators[.]com
- i-presale[.]com
- ipresale[.]world
- ipresales[.]top
- isale[.]live
- isale[.]ltd
- isale[.]run
- i-sale25[.]com
- i-sales[.]digital
- isale-stage[.]shop
- itoken[.]foundation
- i-token[.]live
- i-token[.]org
- itoken[.]run
- itoken[.]sale
- i-token[.]sale
- itoken[.]site
- i-token[.]space
- itoken[.]tech
- i-token[.]xyz
- itoken2025[.]com
- itokenlaunch[.]com
- itokenpresale[.]com
- i-tokens[.]com
- itokensale[.]live
- jackpewpew[.]com
- jimmyneytronus[.]com
- keremh[.]dev
- lopinak[.]com
- midikan[.]com
- mynewairplane[.]com
- presale-i[.]com
- robertoornick[.]com
- sale2025[.]org
- sale25[.]info
- sale25[.]org
- salesx[.]digital
- sale-x25[.]digital
- samsomisan[.]digital
- tokensx[.]store
- tokenxsale[.]com
- token-x-sale[.]com
- xcoin25[.]com
- xcoins25[.]com
- xcoins27[.]com
- xpresale[.]run
- x-presale[.]tech
- xpresale[.]xyz
- xpresales[.]pro
- x-sale25[.]com
- xsale-25[.]digital
- xsales[.]sale
- xsales[.]space
- x-token24[.]org
- x-token24[.]xyz
- x-token-sale[.]com



![Silent Push Enrichment search for domain "chopinkos[.]digital"](https://www.silentpush.com/wp-content/uploads/x-twit-chopinkos-enrichment-image-18.png)