How To Outsmart Adversaries with Preemptive Threat Intelligence
We’ve previously looked at how Preemptive Threat Intelligence discovers and stops attacks before they’re launched, but how does a preemptive approach keep you one step ahead of adversaries as they evolve their strategies to evade detection?
In this blog, we’ll explore how Preemptive Threat Intelligence acts as an early warning system by using a threat actor’s own tactics against them, forming a comprehensive picture of how a threat campaign is prepped and launched, so that security teams can proactively defend themselves against known and hidden attacks using Indicators of Future Attack™ (IOFA)™.
How to stop an attack by knowing threat actor tactics and behavior
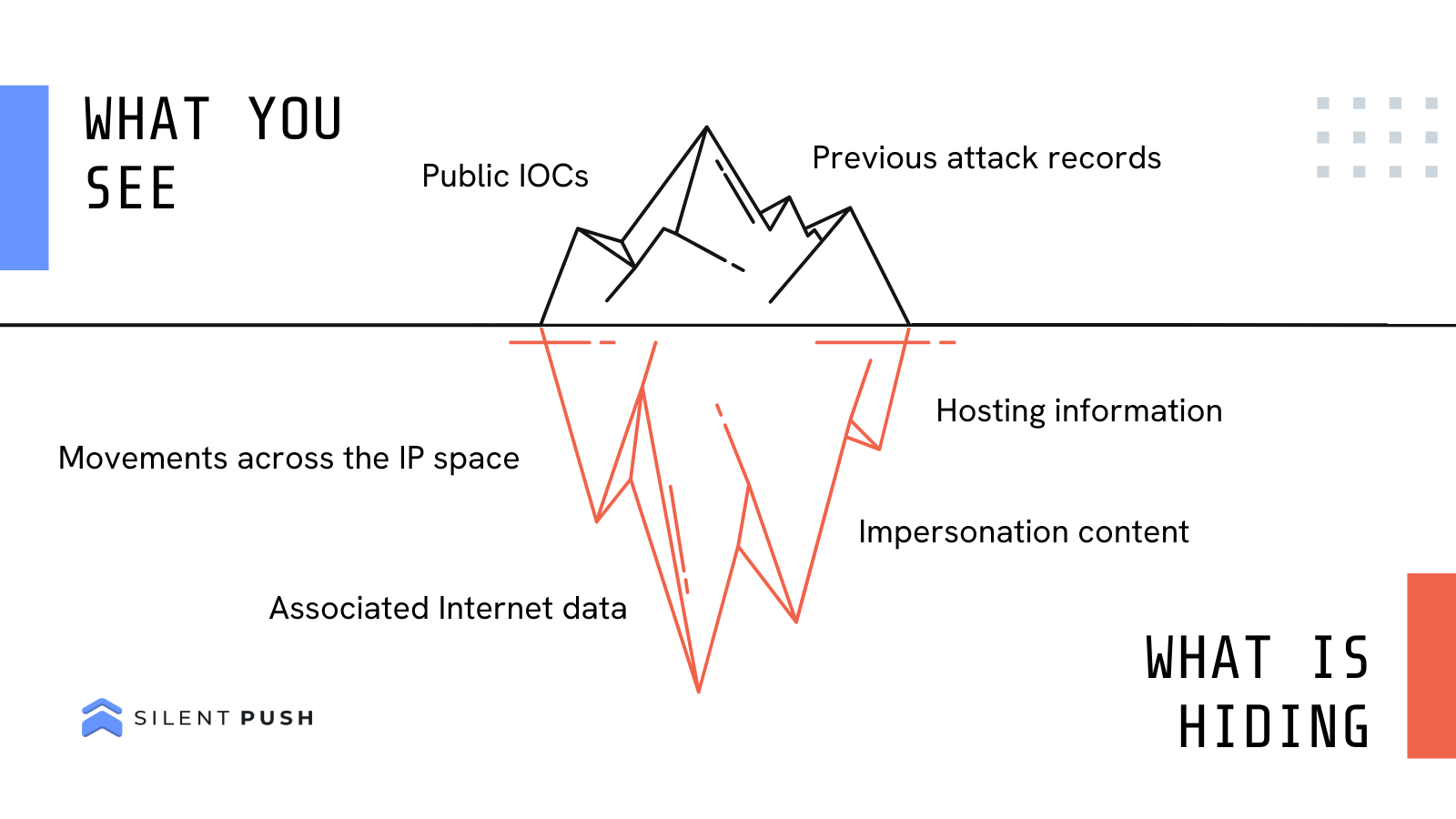
Preemptive Threat Intelligence allows security teams to locate and block the 98% of global threat infrastructure that’s yet to be discovered, and lurking under the surface.
Most importantly, it helps you head off any future attacks by knowing where threat actors are going to strike, based on how they behave.

When a law enforcement agency needs to find and arrest a perpetrator, they gather as much information they can on the person to understand where they are, and where they’re going to strike next.
We’ve all watched crime shows where the agency builds a file to capture who a criminal associated with, what methods they use to commit a crime, what their motive is, and any other crimes they’re involved in. They also look for behaviors to document such as places they frequent, company they keep, and even what brand of cigarettes they smoke.
All of this enables the good guys to be one step ahead of the bad guys, and lay a trap to put them behind bars.
How does Silent Push profile attacker behavior?
At Silent Push, Preemptive Threat Intelligence works in a similar way, but in the digital world.
Instead of only relying on information that’s easily obtainable and available everywhere – such as a domain that’s already been involved in an attack – it’s essential to understand a threat actors’ motivation and modus operandi, and use their own methods as identifiers against them to anticipate and prevent any future attacks.
Silent Push achieves this through our unique digital behavioral fingerprinting process.
We go beyond stale lists of post-breach IOCs, and help security teams to proactively profile threat actor behavior in a way that makes it easy to understand how they set up their infrastructure before an attack, and where to expect the next digital assault.
Our digital behavioral fingerprint breaks down a domain, website or IP address into hundreds of searchable categories, and connects the dots between billions of datapoints across the Internet by giving security teams a comprehensive criminal profile of online threat activity, wherever it occurs and whoever is propagating it.
How does Silent Push provide a cyber early warning system to stop hidden attacks?
Behavioral fingerprints and IOFA™ are unique to Silent Push. No other threat intelligence provider has the same ability to scan, aggregate, and correlate global Internet data, and deliver it in a way that makes it immediately actionable, and easy to use, in the form of IOFA™.
Think of all the questions your team needs to answer as they track down malicious infrastructure targeting your organization…
What favicon is that brand impersonation site using that’s targeting your organization, and what are all the other domains that have ever used that favicon? What domains are linked with the same nameserver? How has that threat actor moved between different hosting providers? Where are they now, where have they been before, and where are they likely to go to next? How does that website interact with users, and what other sites behave in the same way?
All of this, and more, is available only within Silent Push.
Learn more about our unique approach to Preemptive Threat Intelligence
Find out how your organization can use Preemptive Threat Intelligence to outsmart adversaries and stop attacks before they’re launched.
Contact us here for more information.