- Company
Silent Push Inc. ©2025
Silent Push Threat Analysts have been hunting a malicious threat actor group we’re calling “Payroll Pirates. ” The group is responsible for an ongoing human resources (HR) payroll redirection phishing scam against numerous organizations’ employees. Workday customers have been a primary target at high-profile victim companies, many of which we have redacted for privacy.
While many of the HR phishing websites we are tracking are currently down, in part due to our outreach efforts, we’re creating these feeds and sharing this research due to the scale and sophistication of the effort and the likelihood that it will continue. Our threat research team continues to monitor this campaign, alerting our clients and their organizations to help protect them from costly attacks by these nefarious threat actors.
Silent Push Enterprise users have access to two dedicated IOFA Feeds containing all the true positive domains and IPs we gathered during our research.
For operational security reasons, we are unable to share the exact specifics of each query and pivots utilized. Silent Push Enterprise customers have access to a dedicated Payroll Pirates TLP: Amber report, which contains the relevant data types and pivot points we used to track the infrastructure referenced in this blog.
Silent Push Community Edition is a free threat hunting, DNS, and scanning toolkit that contains all the queries and lookups we used to locate and traverse the infrastructure included in this blog.
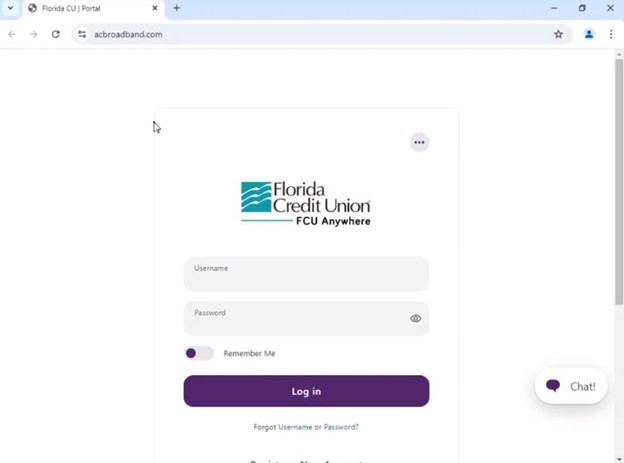
Silent Push Threat Analysts have been hunting a malicious threat actor group we’re calling “Payroll Pirates,” responsible for an ongoing malicious campaign targeting companies’ employees with human resources (HR) phishing scams to carry out payroll redirects. We have identified hundreds of domains primarily focused on Workday users and high-profile organizations, including the California Employment Development Department (EDD), Kaiser Permanente, Macy’s, New York Life, and Roche.
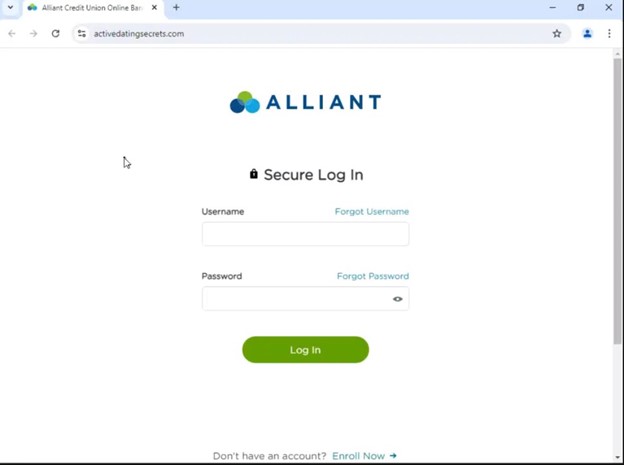
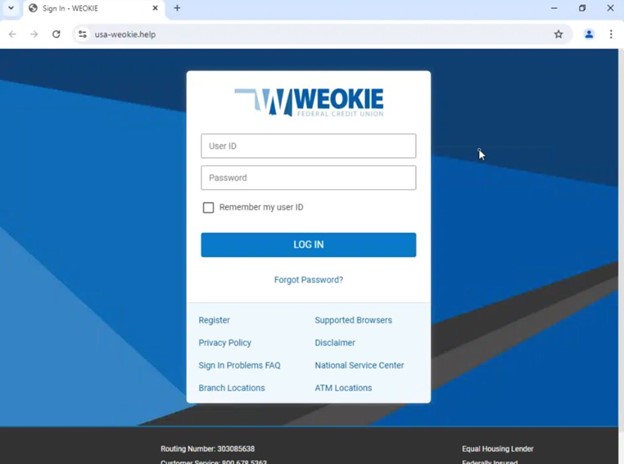
The threat actors have been utilizing malicious search advertising campaigns with sponsored phishing websites and spoofed HR pages via Google to lure unsuspecting victims into providing access to their employee portals. Armed with additional credential information, such as social security numbers likely obtained from underground forums, once the scammers get into an employee’s portal account, they change the individual’s banking information to redirect funds to a fraudulent bank account, which the threat actors control.
Website builders, including Leadpages, Mobirise, Wix, and potentially others, are being used to create domains in the campaign to aid in rapid setup. Our threat research team found dedicated IP ranges connected to entirely new pools of infrastructure and observed tactical shifts aligning with specific timeframes. The phishing content is typically hosted among the threat actor’s preferred registrars, Dynadot, Porkbun, and Namecheap.
This threat was originally shared with Silent Push analysts from a research-sharing organization. Malwarebytes has written about this threat publicly and how it targeted Lowes by using a custom directory structure to match the real Lowes HR portal page structure and further increase the credibility of the phishing site. We haven’t seen this same behavior widely, but we believe some organizations could see custom directories and page structures associated with their phishing kits.

Some of the phishing sites built with Mobirise have domains that appear to be set up for phishing corporate targets with titles like “Welcome to Roche Login” – but without a live phishing page.

The site mentalroccehget[.]com has the same properties as the known malicious result website andandorconnect[.]com, and its host (Cloudflare) and provider (Google) are also identical.
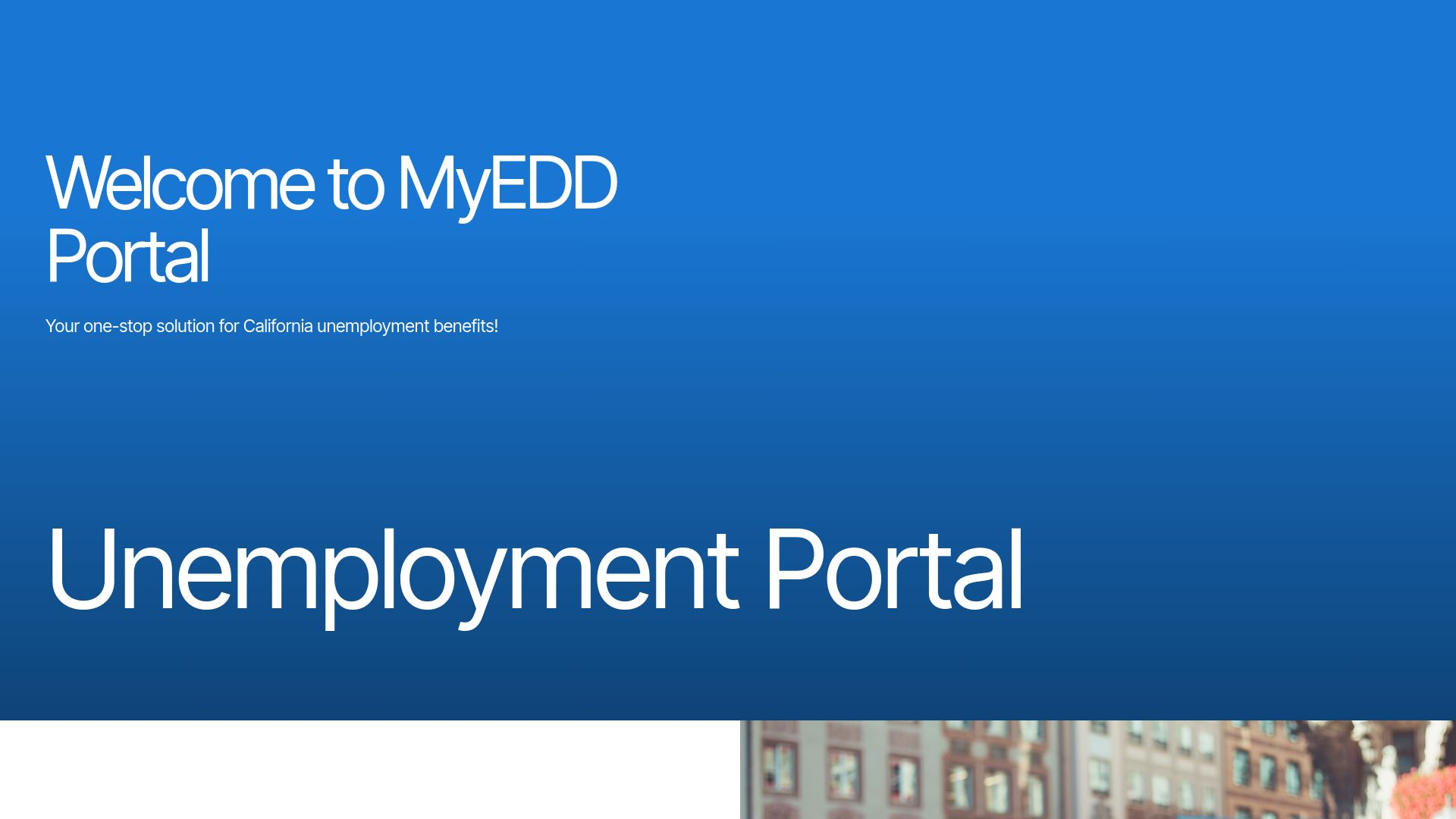
Using the same host, among other values, as both andandorconnect[.]com and mentalroccehget[.]com, we found a new flavor of their phishing kit located at guideulca[.]com targeting an unemployment portal in California.
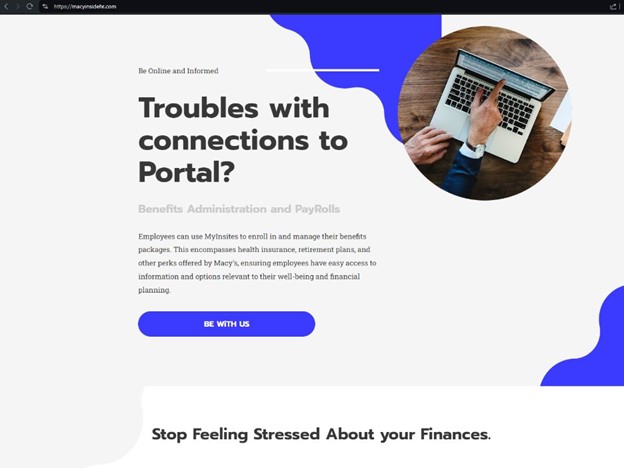
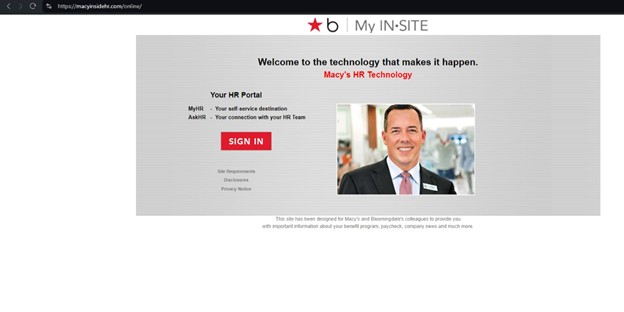
When analyzing a potential phishing site, myinstitehr[.]com, we noticed strange language on the homepage: “These programs offer support for personal and professional challenges, providing resources for mental health, financial advice, and other forms of assistance.” This same language can be found on macyinsidehr[.]com, which also hosts a phishing page.
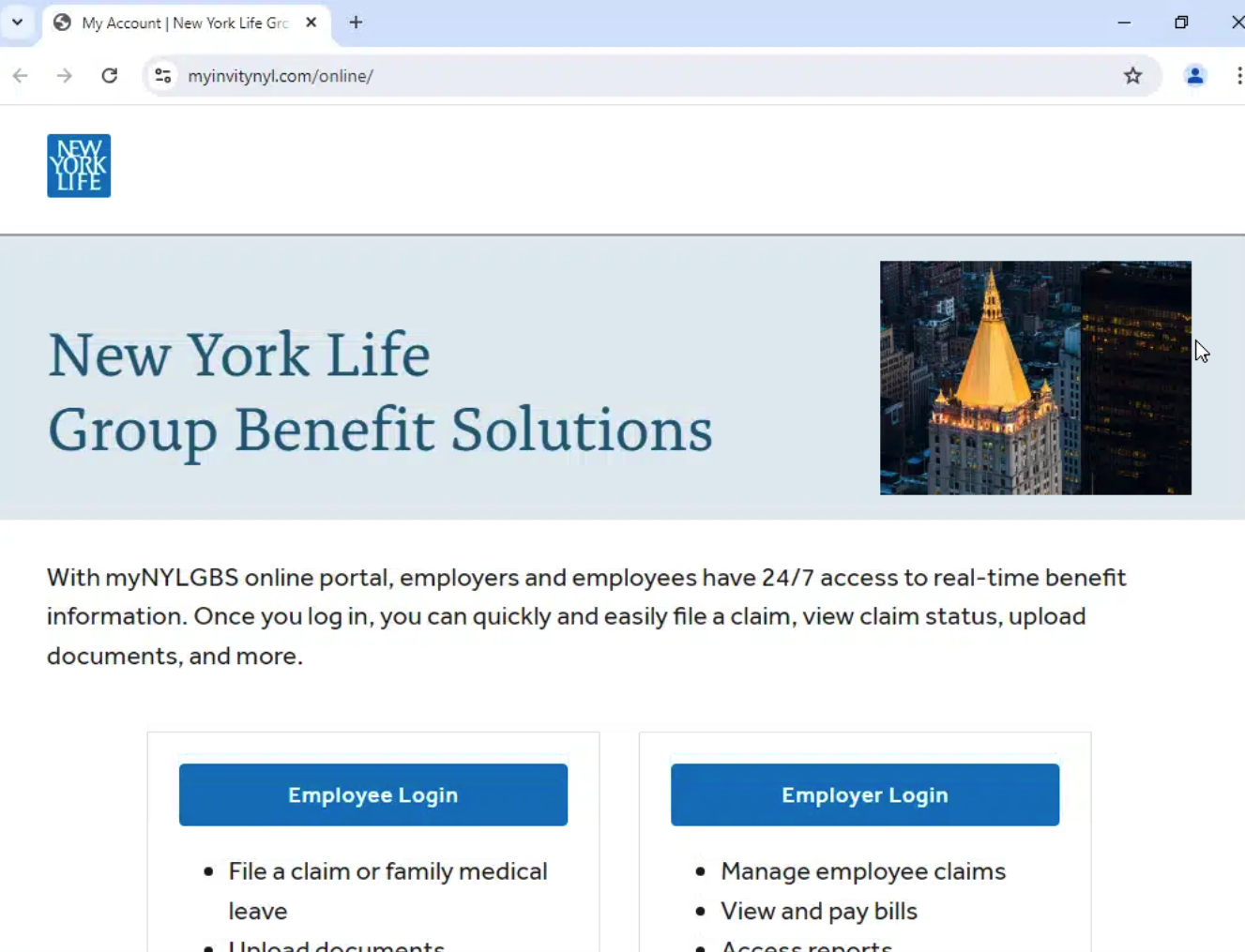
Examining an active phishing page targeting New York Life, we found it was hosted via Leadpages, another website builder.
Searching further returned more domains related to this campaign:
Starting with the new domains: hrocneddiwserv[.]com, myhrkp[.]website, myidmlogin[.]world, myidmportal[.]site, and mypayaramark[.]online, we saw that a couple of them had the HTML title “MyPay” before changing it to “hrkp.”
Repeating the search, but this time with the filter “MyPay” returned very interesting results:
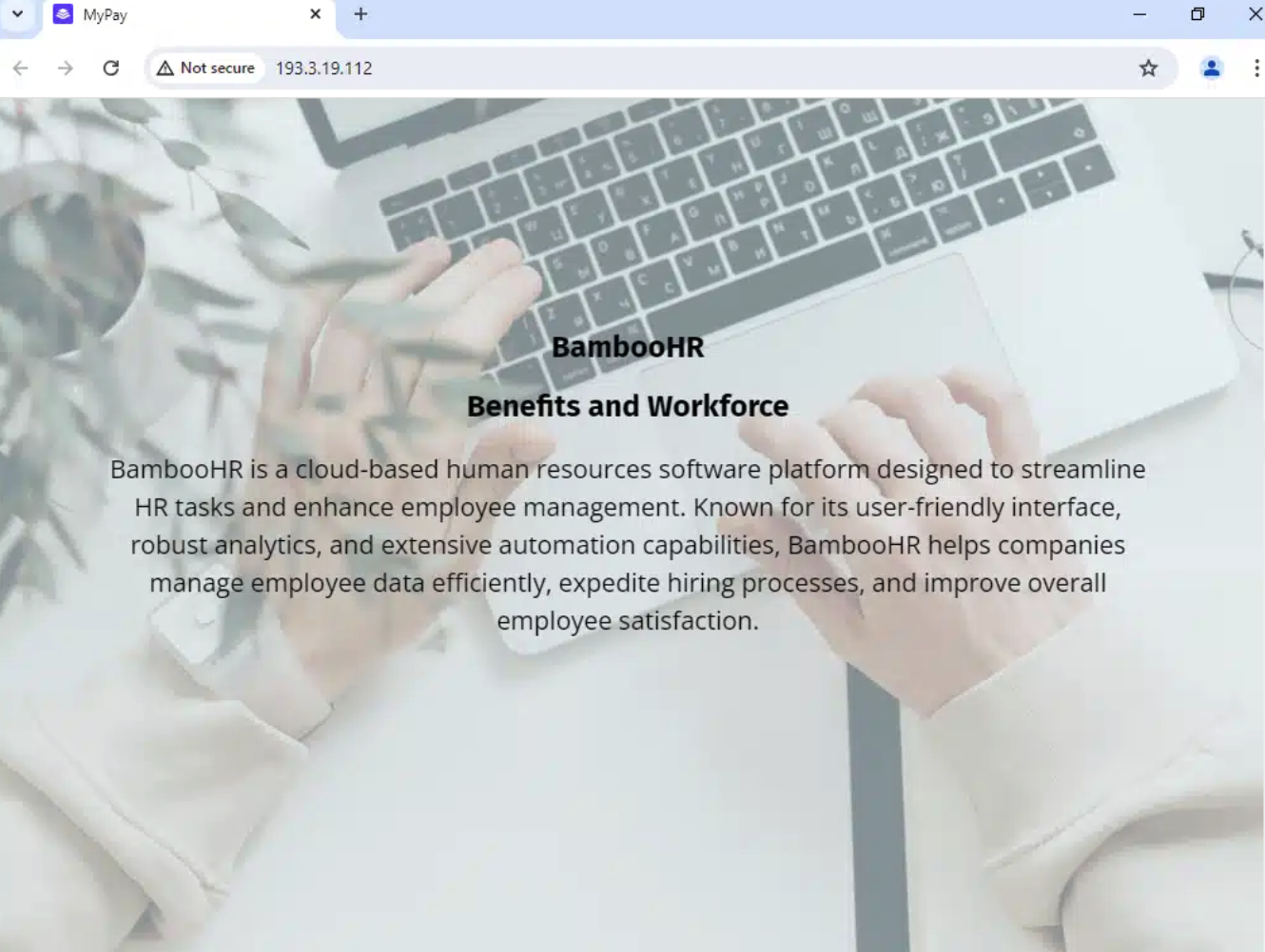
From the “MyPay” filter, the most interesting part lies within one particular result. Not a domain, but an IP address: 193.3.19[.]112 on AS50340(SELECTEL-MSK, RU).
Direct access to the IP showed an HR-themed page that mentions “BambooHR” (example below).
This IP address, 193.3.19[.]112, which hosted the BambooHR content on the root directory path, had a new domain mapped to it recently: myrocshe[.]com – which also had a phishing page targeting Roche:
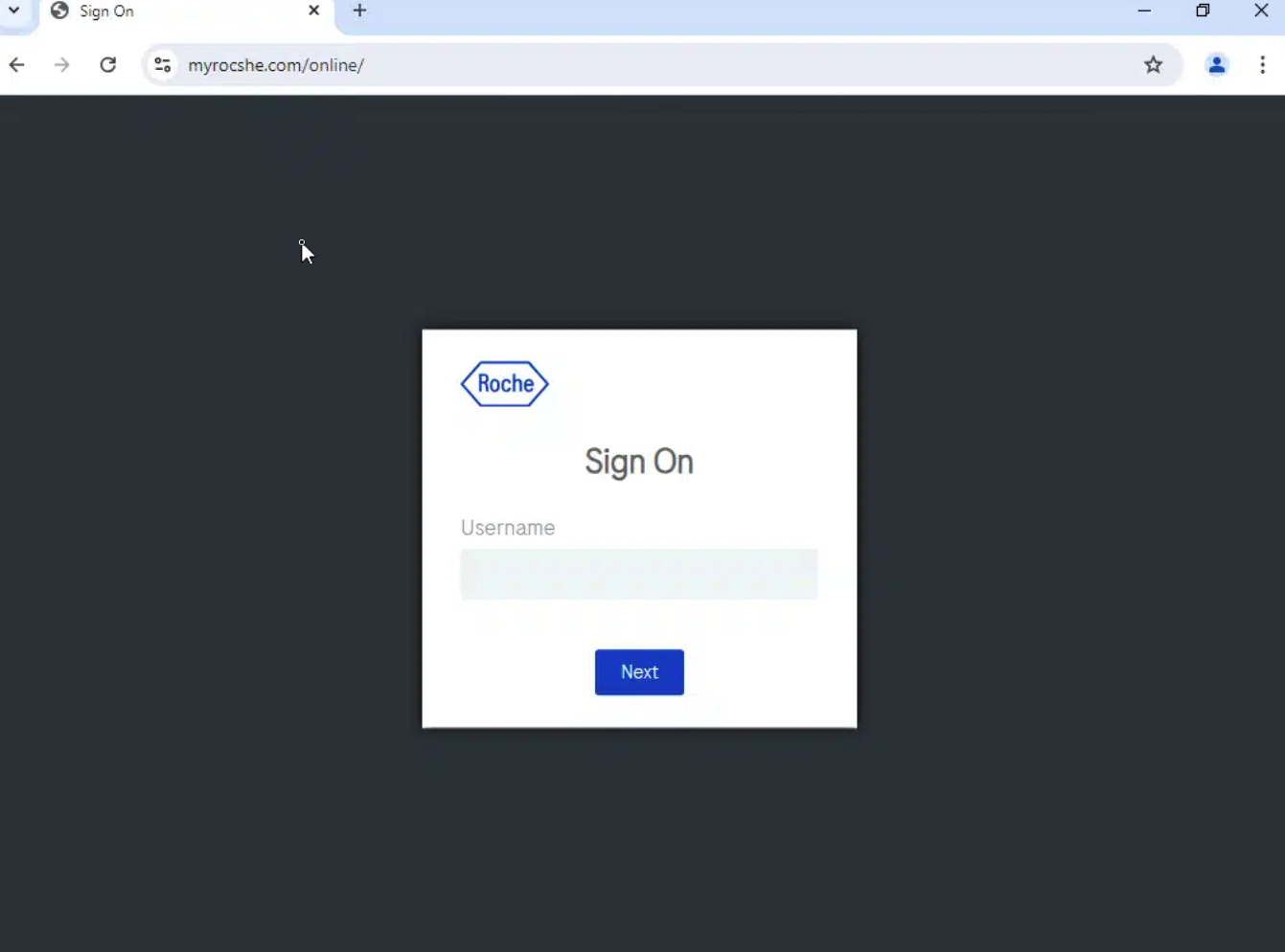
The phishing site targeting Roche was registered on Dynadot the week of August 11, 2024, and Silent Push was able to catch it before the threat actors had time to proxy it through Cloudflare.
Analyzing historical scans featuring this IP address, 193.3.19[.]112, we see the threat actor was running an Unemployment Benefits scam targeting Kroger Grocery before switching to payroll phishing and that they seem to have changed to Mobirise templates after the second quarter of 2024.

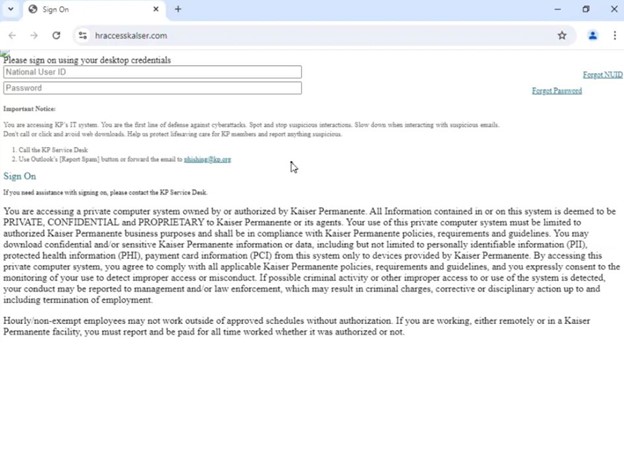
The majority of the domains found so far only hosted the phishing page on the /online path, but we noticed when we rescanned hraccesskalser[.]com, it returned a poorly crafted Kaiser phishing page:
An additional proprietary fingerprint used by these threat actors was queried, returning a large pool of similar results. We haven’t definitively proven these bank phishing sites are directly connected to the payroll redirection scheme yet, but they are clearly malicious and potentially created by the same threat actors.
We set up monitors to find new domains that matched our existing queries tracking this campaign. This allows us to keep track of the actors as they continue adding to their network. Within just a few hours of running these monitors, we picked up over 100 new domains, likely related to this campaign.
A brief sample list is below:
Silent Push will continue to track the Payroll Pirates threat actors’ activity and report our findings to the security community. For operational security, some of the information in this public blog has been omitted.
We’ve also published a TLP Amber report for Enterprise users that contains links to the specific queries we’ve used to identify and traverse the Payroll Redirects’ infrastructure—including proprietary queries that we’ve omitted from this blog for operational security reasons.
Silent Push believes all Payroll Redirects domains offer some level of risk.
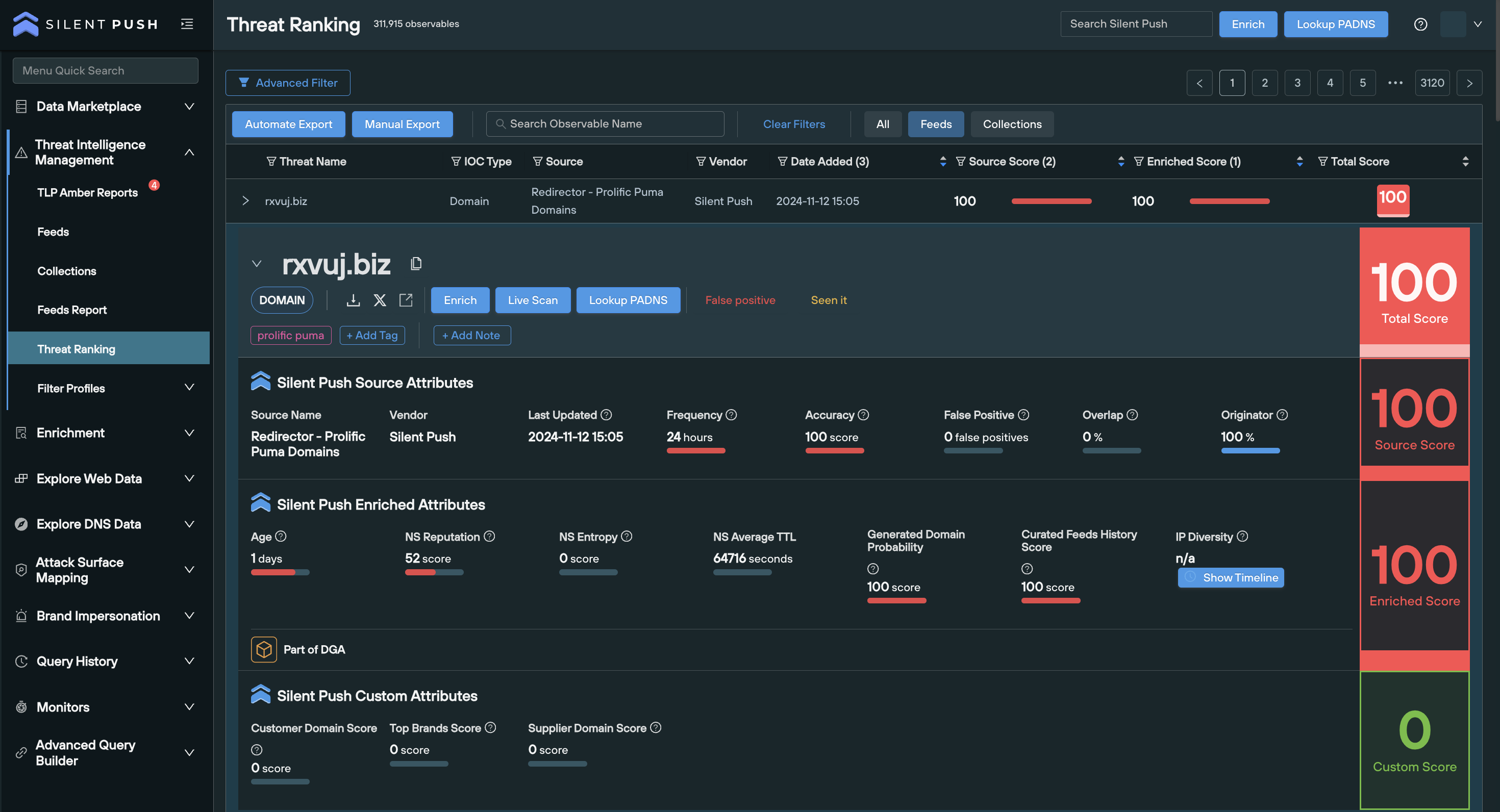
Our analysts have constructed a Silent Push IOFA Feed that provides a partial list of Payroll Pirates Indicator of Future Attack domains focused on their scams, along with an IOFA Feed containing suspect Payroll Pirates IPs.
Silent Push IOFA Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform featuring a range of advanced offensive and defensive lookups, web content queries, and enriched data types, including Silent Push Web Scanner and Live Scan.
Click here to sign up for a free account.
Here is a sample list of IOFAs – our full list is available for enterprise users. Silent Push Enterprise clients have access to a domain and IP feed containing the Payroll Pirates’ infrastructure.
Building on the work of the DEA, Silent Push Threat Analysts have used content similarity and page metadata scans to reveal approximately 2,500 unique Indicator Of Future Attack (IOFA) domains and dedicated IPs actively hosting illegal pharmacy content.
The websites are actively engaged in numerous criminal acts, including the sale of illegal drugs and Counterfeit or Falsified Medication (CFM).
Domains are largely hosted via US-based ASNs and dedicated IPs, using Dynadot and Russian nameservers.
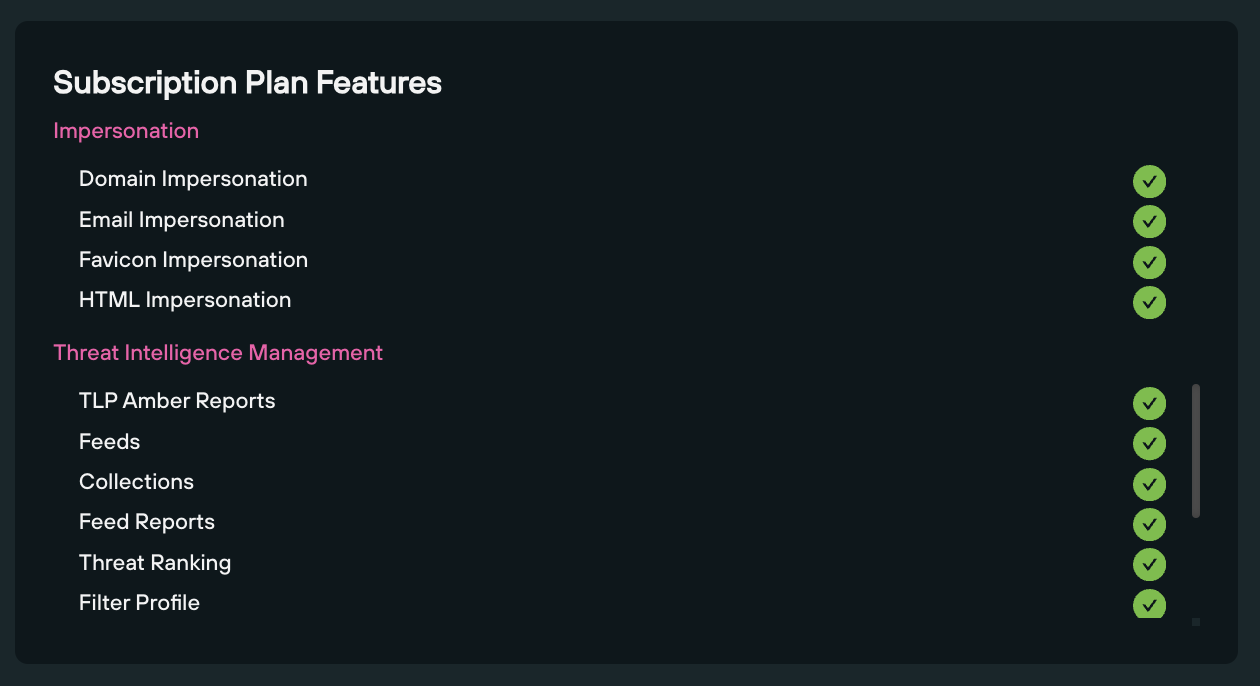
Silent Push Enterprise users have access to two dedicated IOFA Feeds containing all the true positive domains and IPs we gathered during our research.
For operational security reasons, we are unable to share the exact specifics of each query and pivot utilized. Silent Push Enterprise customers have access to a dedicated Illegal Pharmacies TLP Amber report, which contains all the relevant data types and pivot points we used to track the CFM infrastructure referenced in this blog.
Silent Push Community Edition is a free threat hunting, DNS and scanning toolkit that contains all the queries and lookups we used to locate and traverse the infrastructure included in this blog.
Sign-up here.
According to a 2017 Frontiers in Pharmacology report, Counterfeit and Falsified Medicine can broadly be described as medicines that “contain substandard active ingredients, which are low quality and/or an incorrect amount, either too high or too low, and have not been properly evaluated by authorities in terms of quality, safety, and efficacy.”
Illegal online pharmacies that sell CFMs have existed for well over a decade. As far back as 2012, the WHO estimated that illegal prescription drug sales reached $431 billion.
During the Coronavirus pandemic, the number of illegal pharmacies dramatically increased. As concerned citizens searched for medicine online while they were in their homes during lockdown, bot spammers began polluting SEO results to redirect unsuspecting users to shady pharmacy sites.
More recently, on October 4, 2024, the DEA issued a Public Safety Alert that warned about the dangers of illegal online pharmacies, following the death of a US-based woman who ingested what she believed to be a oxycodone pill, but was in fact fentanyl.
As part of the above investigation, the DEA published details of 9 fake online pharmacies:
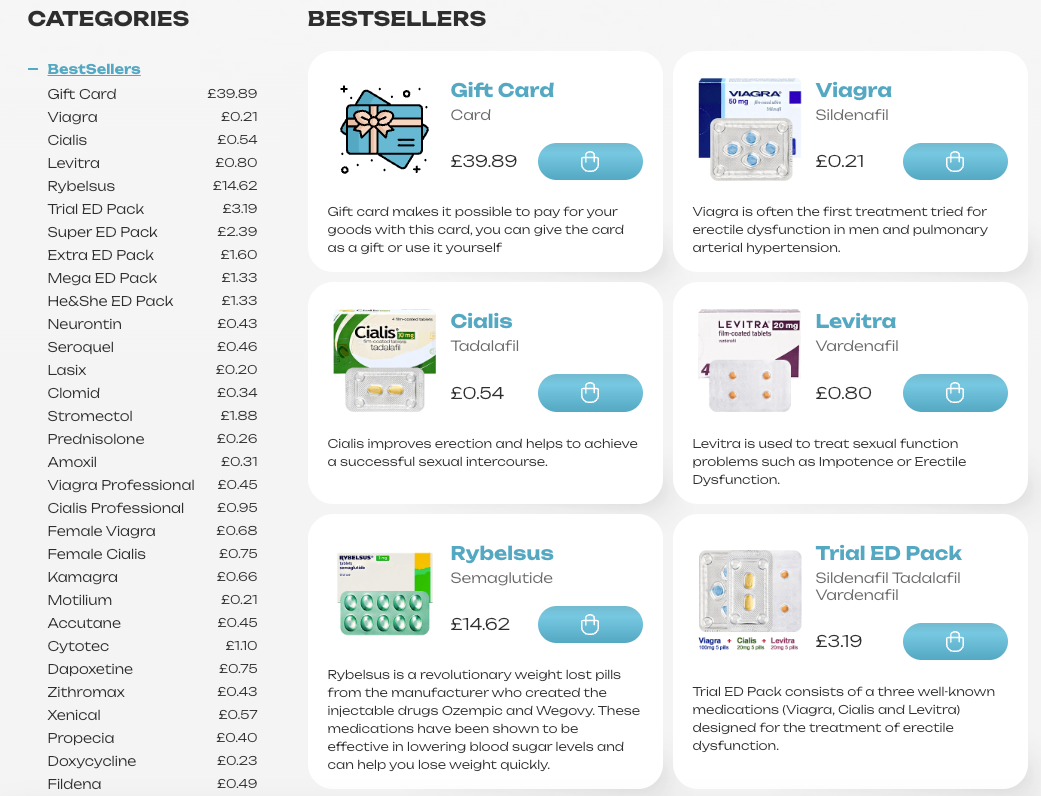
Performing a Google search for “shop + cheap viagra” returns a list of templated domains that rank due to blackhat SEO tactics, with content templates that, whilst similar, contain subtle differences.
Here’s a few examples:
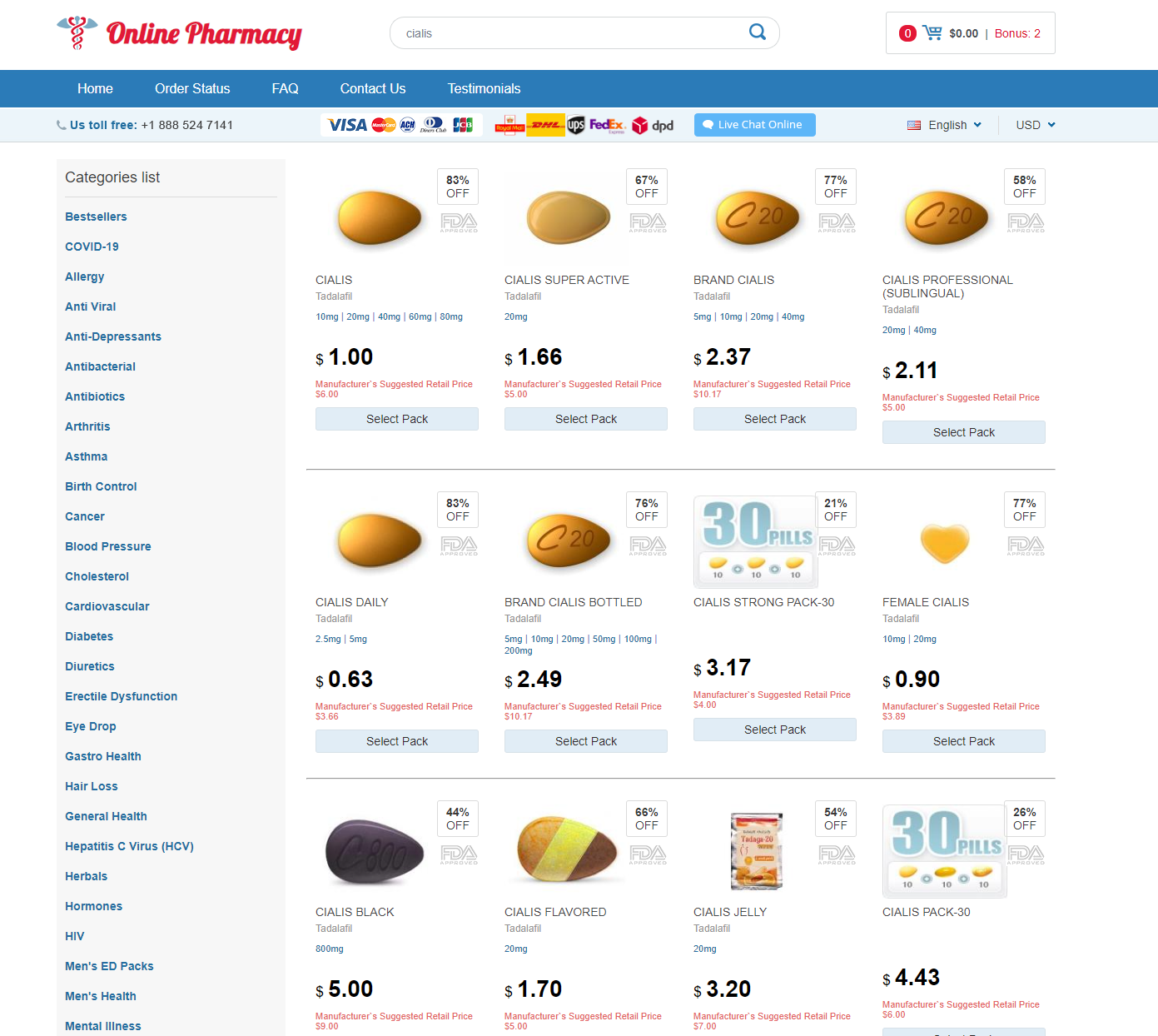
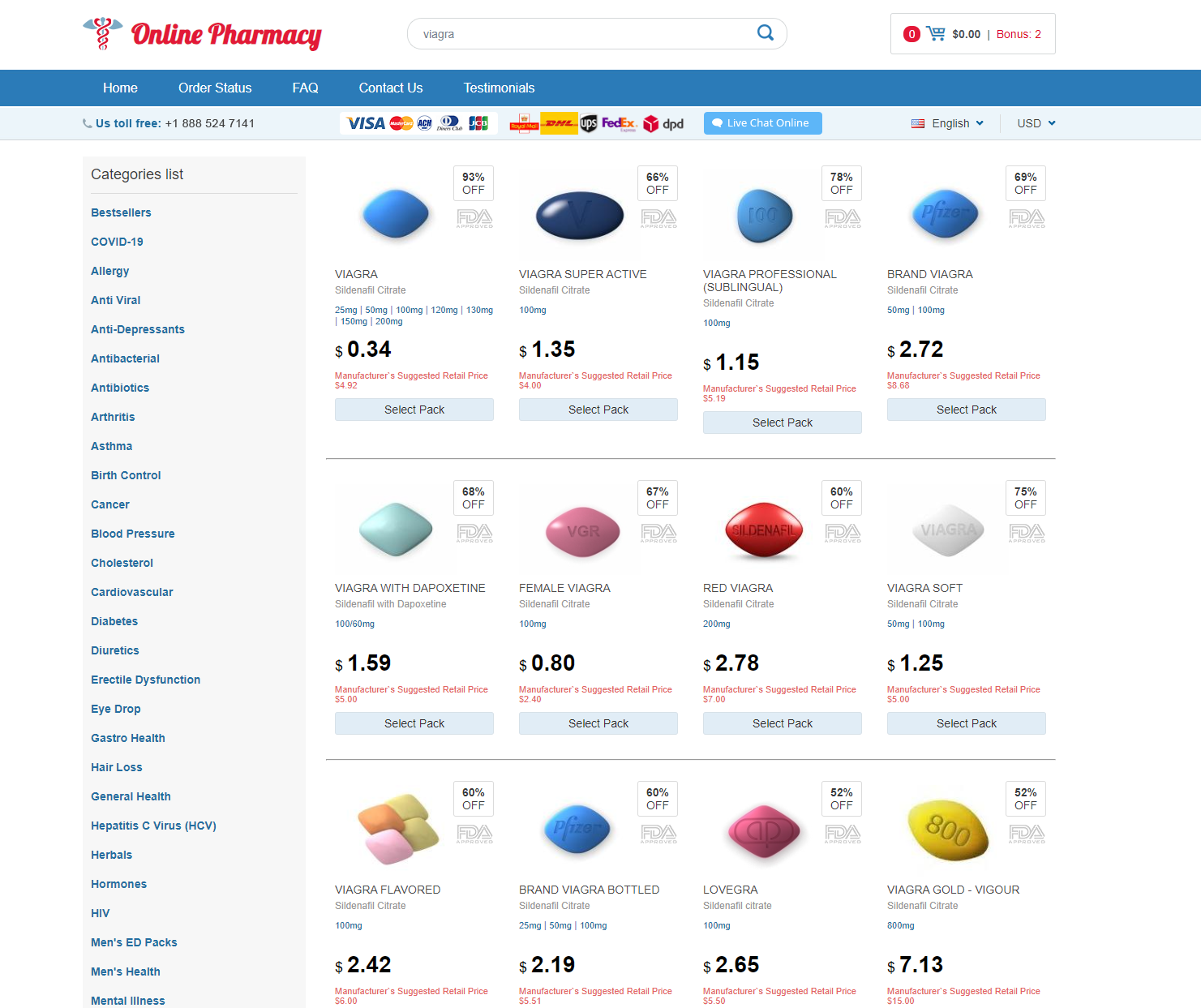
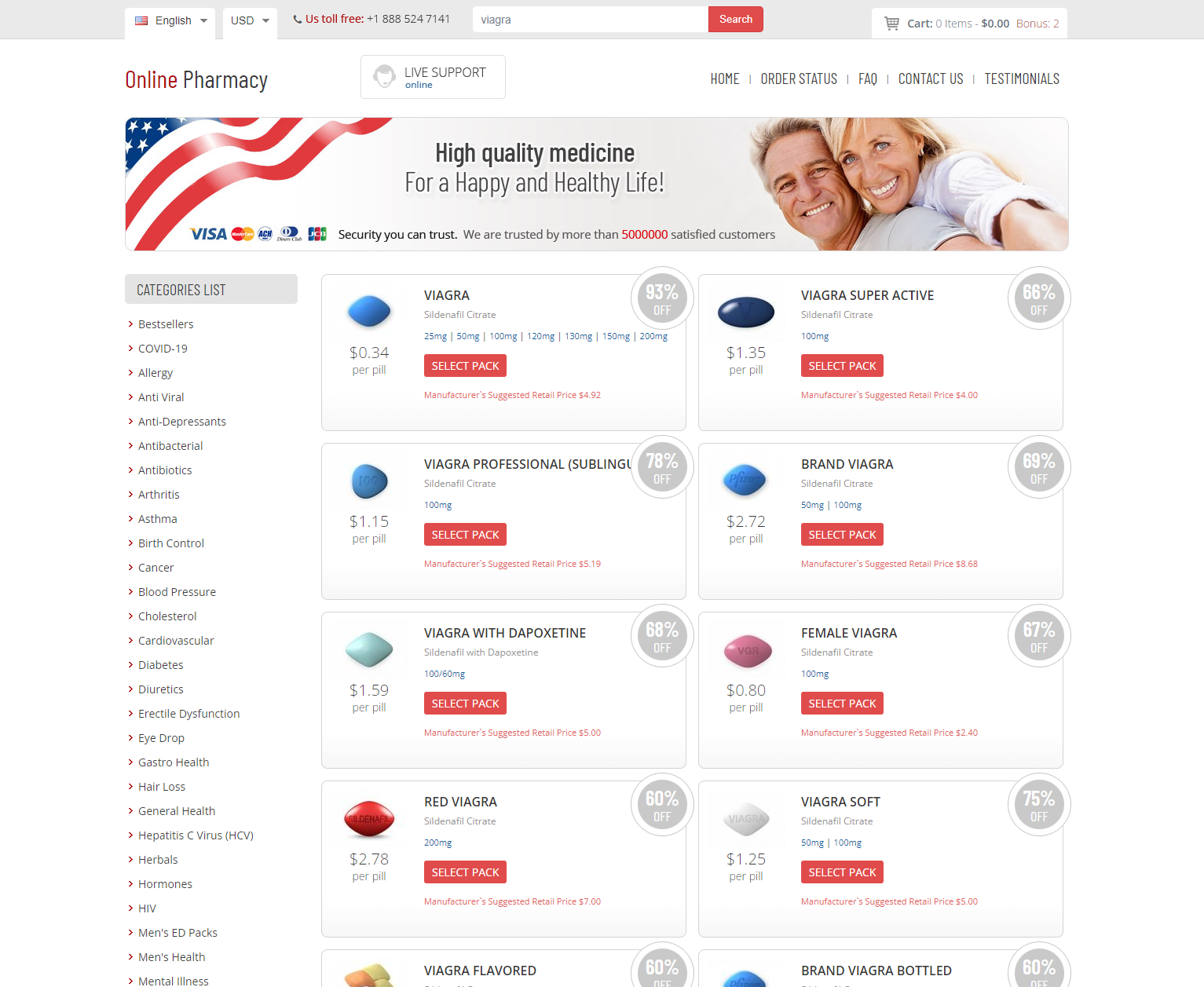
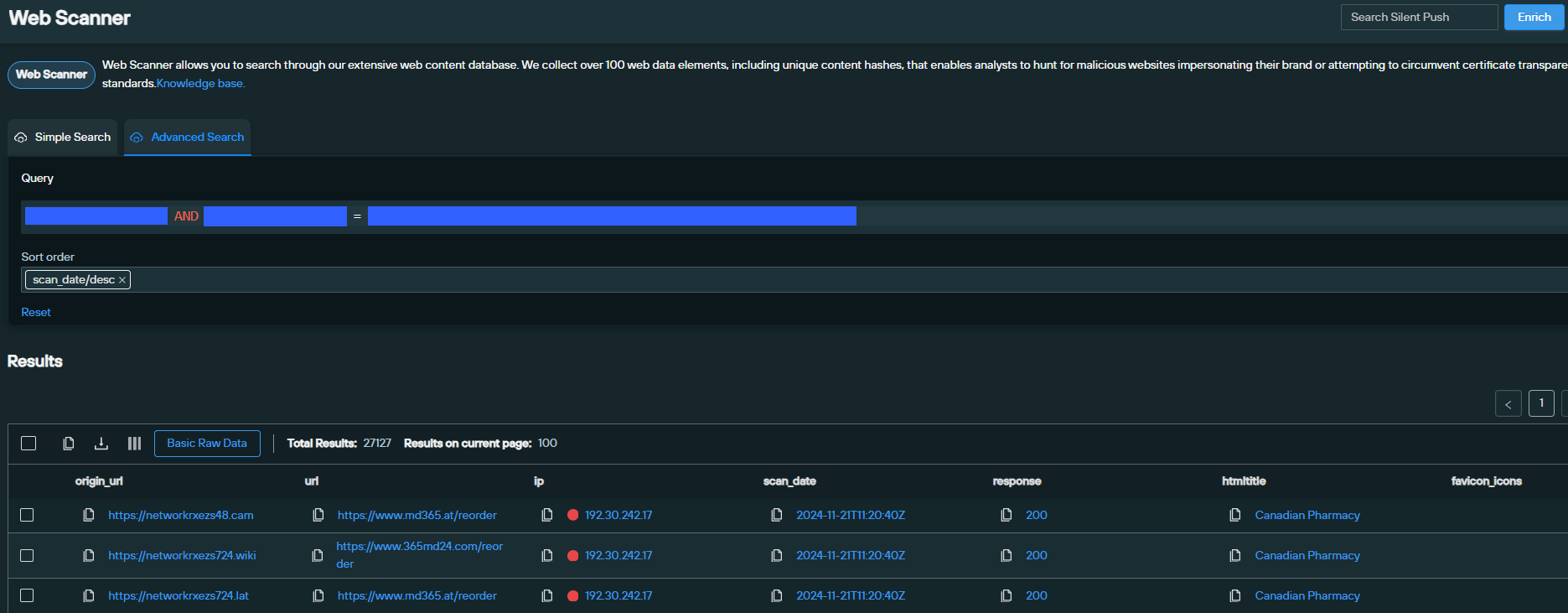
After analyzing the domains returned, our team identified several key on-page elements that we were able to use as parameters in a Silent Push Web Scanner query, in order to reveal linked infrastructure.
Silent Push Web Scanner outputs data on all public-facing and darkweb sites across 100+ categories, including body content hashes, header values, embedded code configurations, and certificate data.
Our scans returned an initial dataset of 1,000+ domains and IPs, containing 100% true positive results of websites engaged in the sale of CFMs and illegal drugs.
Here’s a sample of what we discovered. As you can see, the websites are re-using content templates in line with previously observed TTPs, indicating an infrastructural link between a majority of the domains.
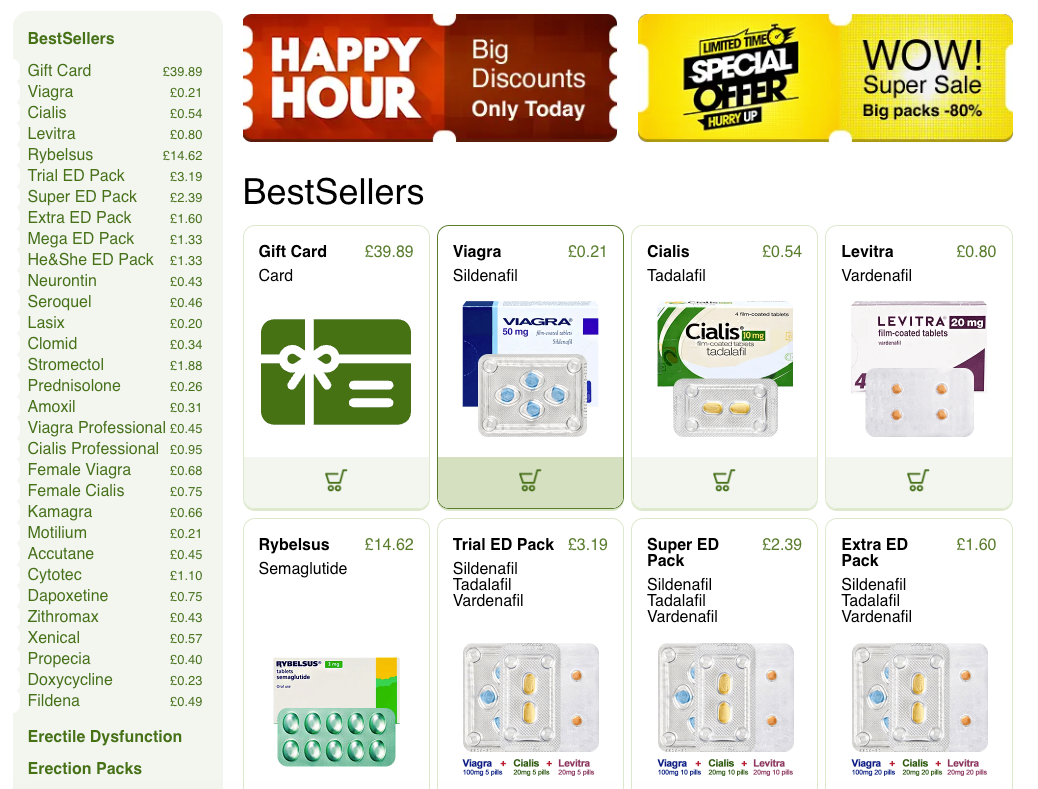
Once we knew that our datasets contained true positive linked domains, we used further Silent Push Web Scanner queries to create a proprietary behavioral fingerprint made up of back-end web infrastructure elements, that revealed yet more associated CFM websites.
This secondary pivot led to the discovery of almost 4,000 unique domains and dedicated IPs that are all part of the same active CFM campaign. Not all were active.
A large number of the dedicated IPs we discovered map to additional domains, as well as rendering a website.
Here’s a sample:
We’ve collected all the true positive CFM domains into two dedicated Indicator Of Future Attack (IOFA) feeds, available to Enterprise users.
As of writing, the feeds contain approximately 2,500 domain and IP IOFAs.
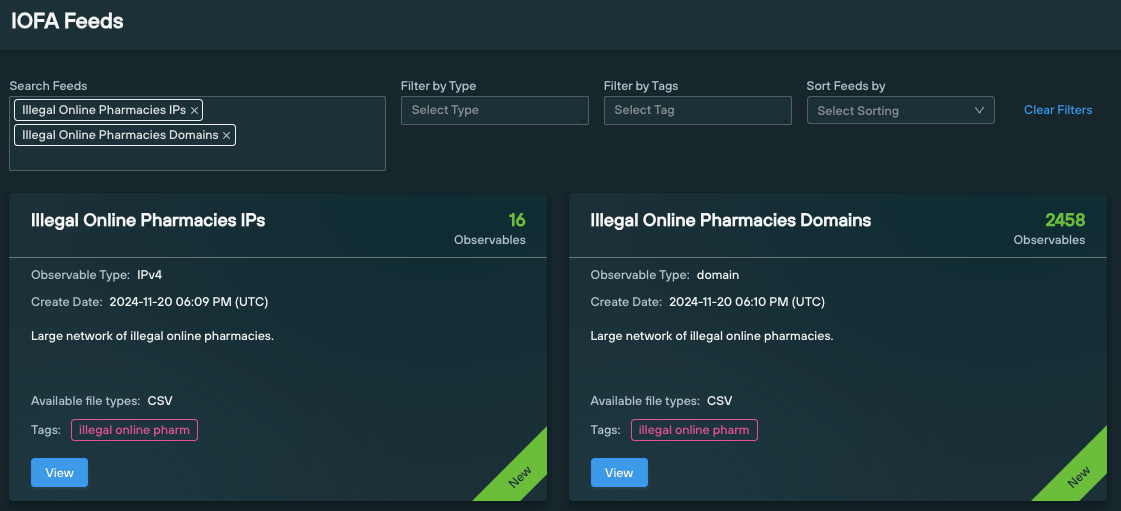
Enterprise users can ingest IOFA Feed data into their security stack to inform their detection protocols, or use enriched feed data to traverse known and unknown infrastructure, using the Silent Push API and Console.
Clicking the “Feed Analysis” button displays numerous additional metrics associated with the data type contained within the feed.
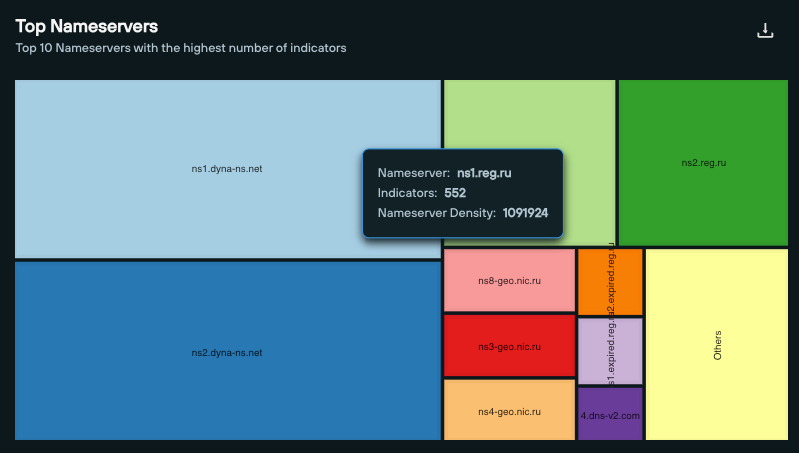
In the “Illegal Online Pharmacies – Domain” feed, we can see that the majority of nameservers are hosted via Dynadot on ns1.dyna-ns[.]net and ns2.dyna-ns[.]net, with the remainder served by a mixture of primarily Russian nameservers.
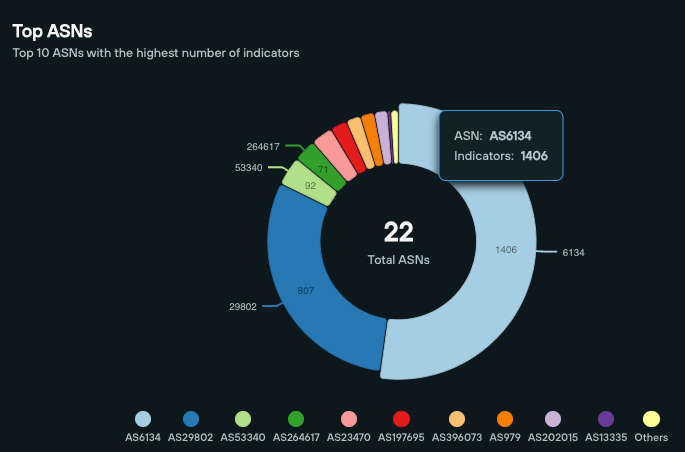
From the Feed Analytics screen, we can also see that that the majority of CFM domains are hosted on AS6134 (XNET LLC) and AS29802 (HIVELOCITY) – both of which are US-based.
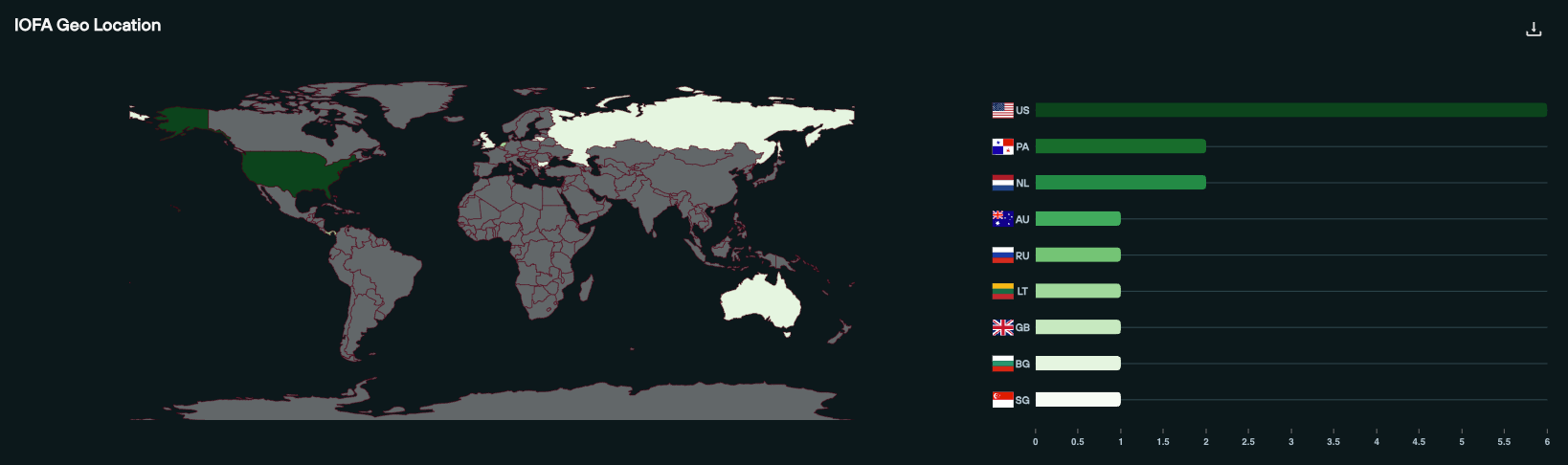
Pivoting through the IP feed, we can see that the geographic spread places the majority of dedicated IPs in the US:
It’s apparent that law enforcement authorities are aware of a certain number of domains located on the above cluster, but not all.
Several domains – such as allcentercenter365[.]ru (which redirects to www.724pharmonline[.]at) on 192.30.242[.]17 – have been seized through joint action between U.S. and European enforcement agencies:

Given that our scans revealed active domains sharing the same infrastructure, content elements and TTPs as seized domains, it’s clear that law enforcement are yet to map out the full extent of the campaign.
We’ll be passing our research on to all the relevant authorities. Law enforcement agencies can reach out to us at [email protected] for collaboration.
In the last release, we introduced Total View – a one stop shop for domain and IPv4 intelligence, without the need to access multiple menus at once. The new Release 4.5 offers additional updates that streamline workflow efficiency within the platform.
On one pane, users can view information about their usage, subscription details and other account information.
Read up on the latest platform tips, guides on 2FA/SSO and expanded information to help navigate the platform.
Enterprise users can now automatically download 10,000 (previously 1000) Indicators of Future Attack from the Threat Ranking page, significantly reducing the number of endpoint calls needed!
Have any questions about the new release, or would like to learn more about our Community and Enterprise Editions? Get in touch today and we’ll get back to you shortly.
In September, Silent Push Direct of Threat Intelligence Kasey Best presented at the mWISE 2024 conference to discuss using hashes and fuzzy hashes to detect adversary infrastructure. Threat actors are capitalizing on the scalability and efficiency that automation provides. Why deploy a single phishing site when you can launch five with just a few clicks?
Hashing (and fuzzy hashing) allows you to detect identical or similar malicious infrastructure as soon as it’s created.
In this video, Kasey dives into hashes, what they are, and how they can help you preemptively detect malicious infrastructure, before an attack even goes live. Kasey also takes you through several examples of using hashes to detect even the most high-profile threat actors including FIN7, CryptoChameleon, Prolific Puma and more.
Want to stay ahead of emerging threats? Discover how Silent Push’s Indicators of Future Attack can give your organization the foresight to counter threats before they strike. Request your personalized demo today and see the power of preemptive threat intelligence in action:
In September, Silent Push Senior Threat Researcher Zach Edwards presented at the mWISE 2024 conference, addressing the persistent threat posed by Raspberry Robin. Despite its initial appearance several years ago, this “initial access broker” remains a critical concern. Raspberry Robin breaches enterprises and sells access to other cybercrime groups, primarily based in Russia.
Shortly before the presentation, the Cybersecurity and Infrastructure Security Agency (CISA), the FBI, and the NSA released a joint advisory linking Raspberry Robin to actors associated with Russia’s GRU, underscoring its role in state-sponsored cyber operations. Read the advisory here: CISA, FBI, NSA Joint Statement.
Raspberry Robin uses highly advanced tactics: leveraging compromised routers, IoT devices, and obfuscating malware through multi-layer packing. They sell access to other groups, making it challenging to identify their involvement in initial breaches. Silent Push’s presentation highlighted these tactics, provided examples of Raspberry Robin domains, and offered insights to help defenders recognize and counter this evolving threat using Indicators of Future Attack.
The presentation featured insight into these tactics, with a breakdown of Raspberry Robin’s infrastructure and domain patterns. Zach showcased specific payloads, drawing on the research of security companies that have documented Raspberry Robin’s attacks.
Silent Push’s goal remains to equip defenders with the intelligence they need to preemptively detect and counter this evolving threat – as Raspberry Robin continues to prove its resilience and adaptability in the global cyber threat landscape.
Want to stay ahead of emerging threats? Discover how Silent Push’s Indicators of Future Attack can give your organization the foresight to counter threats before they strike. Request your personalized demo today and see the power of preemptive threat intelligence in action:
Silent Push Threat Analysts have discovered 2000+ unique domains that are affected by the ClickFix/ClearFake fake browser update malware.
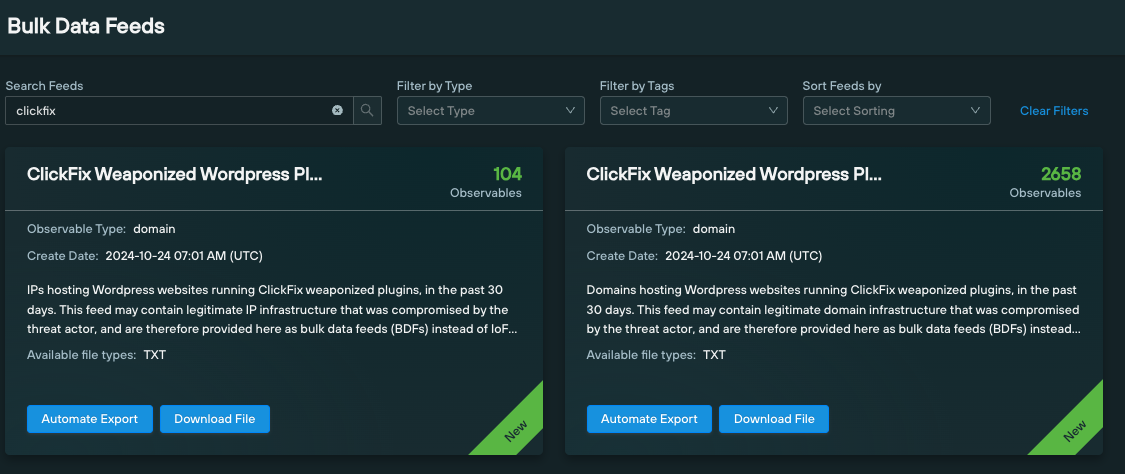
Our team has constructed two Bulk Data Feeds that track affected domains in real time, using a Silent Push Web Scanner query that scans domain metadata for infected domains and IPs.
As of writing, we have identified ClickFix JavaScript code as being active on 2,658 domains, across 104 IP addresses.
Silent Push Enterprise users can ingest this data into their security stack, and use it to identify the ClickFix exploit within their existing detection protocols.
Last week, GoDaddy researchers discovered a major increase in “swarms” of malicious WordPress plugins that infect compromised websites with fake browser update pop-ups, which use blockchain technology to distribute malware such as Lumma Stealer.
Lumma (also known as LummaC2) is an information stealer that’s been available on the dark web as Malware-as-a-Service since 2022. Last year, we published a blog exposing Lumma threat activity, and its links to Russian threat activity.
Affected websites are compromised by threat actors obtaining back-end access to WordPress control panels (usually via stolen credentials), and installing plugins that inject JavaScript containing the aforementioned ClickFix/ClearFix malware.
GoDaddy researchers have identified the following malicious plugins as carrying the JavaScript payload:
| Plugin name | Injected script |
| Admin Bar Customizer | admin-bar-customizer/abc-script.js |
| Advanced User Manager | advanced-user-manager/aum-script.js |
| Advanced Widget Manage | advanced-widget-manage/awm-script.js |
| Content Blocker | content-blocker/cb-script.js |
| Custom CSS Injector | custom-css-injector/cci-script.js |
| Custom Footer Generator | custom-footer-generator/cfg-script.js |
| Custom Login Styler | custom-login-styler/cls-script.js |
| Dynamic Sidebar Manager | dynamic-sidebar-manager/dsm-script.js |
| Easy Themes Manager | easy-themes-manager/script.js |
| Form Builder Pro | form-builder-pro/fbp-script.js |
| Quick Cache Cleaner | quick-cache-cleaner/qcc-script.js |
| Responsive Menu Builder | responsive-menu-builder/rmb-script.js |
| SEO Optimizer Pro | seo-optimizer-pro/sop-script.js |
| Simple Post Enhancer | simple-post-enhancer/spe-script.js |
| Social Media Integrator | social-media-integrator/smi-script.js |
Silent Push Web Scanner collects data on all public facing websites, including HTML titles and body content, certificates, favicons and server data, and allows users to execute queries that return linked malicious infrastructure using 100+ categories.
Our team used the above JavaScript plugins to execute a Silent Push Web Scanner query using the following syntax, that located all affected websites active after September 20:
body_analysis.js_sha256 = ["admin-bar-customizer/abc-script.js ", "advanced-user-manager/aum-script.js ", "advanced-widget-manage/awm-script.js ", "content-blocker/cb-script.js ", "custom-css-injector/cci-script.js ", "custom-footer-generator/cfg-script.js ", "custom-login-styler/cls-script.js ", "dynamic-sidebar-manager/dsm-script.js ", "easy-themes-manager/script.js ", "form-builder-pro/fbp-script.js ", "quick-cache-cleaner/qcc-script.js ", "responsive-menu-builder/rmb-script.js ", "seo-optimizer-pro/sop-script.js ", "simple-post-enhancer/spe-script.js ", "social-media-integrator/smi-script.js "] AND scan_date > "2024-09-20"Here’s a quick tutorial video on how to execute basic and advanced web content and DNS queries using Silent Push Web Scanner.
Silent Push Web Scanner is available across all subscription types. Sign up for a free Community Edition account, to start using it.
Silent Push Bulk Data Feeds – available as part of a Silent Push Enterprise subscription – are dynamic lists of domains, IPs, URLs, and nameservers that are exportable as a text file, or as an API endpoint.
Bulk Data Feeds are distinct from IOFA Feeds, in that they can contain non-malicious indicators.
Feeds are categorized by data type, and contain information on important changes and additions across the global IPv4/6 range that organizations can use to inform their detection protocols – e.g. a list of new nameservers, IPFS nodes, and of new country code top level domains (ccTLDS).
We’ve populated two dedicated ClickFix Bulk Data Feeds with vulnerable domains and IPs obtained from the above query, so that organizations can easily identify all the domains currently affected by the explot:
Silent Push Web Scanner is available as part of a free Community Edition account. You can use the above query parameters to scan for affected ClearFix infrastructure, and add in additional data fields to create custom detection protocols based on your organizational requirements.
For tips on how to get started, Watch our Web Scanner video tutorial.
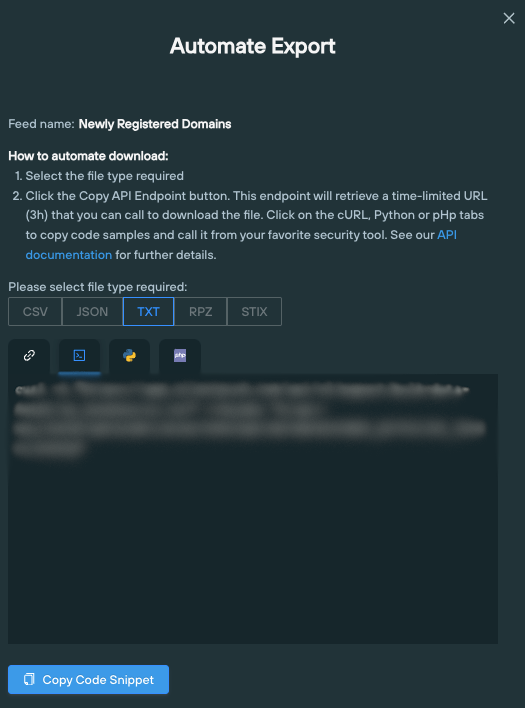
Silent Push Enterprise users can ingest Bulk Data Feeds into their security stack using a range of endpoint export options, by clicking the ‘Automate Export’ button
Silent Push Community Edition is a free threat hunting and cyber defense platform featuring a range of advanced offensive and defensive lookups, web content queries, and enriched data types, including Silent Push Web Scanner and Live Scan.
Click here to sign-up for a free account
We’re thrilled to announce that we’ve partnered with Aqaio, a specialized next generation IT security distributor, to offer early global threat detection services to its customers and reseller partners to reduce the risk of reputational loss and block attacks.
Cybersecurity tooling is complex and rarely correlates data across the entire ecosystem, to identify stealth threat behavior. Without preemptive threat intelligence, companies are exposed and vulnerable to hidden adversary infrastructure. Silent Push provides an early warning system approach delivering a global cyber defense with actionable threat intelligence to stop the attack before it launches.

Richard Hellmeier, Aqaio CEO, stated, “With the acceleration of GenAI and a global rise in breaches, we sought the opportunity with Silent Push to enable our customers, reseller partners and their clients to identify and stop attacker campaigns before they strike. Offering this innovative solution is part of our commitment to providing leading technology expertise and services.”

“Preemptive global threat intelligence starts with comprehensive data,” added Ken Bagnall, Silent Push CEO. “Too often legacy solutions just rely on Indicators of Compromise (IOC) with limited visibility and missing data. We go beyond IOCs and expose Indicators of Future Attacks through our proprietary behavioral threat modeling; allowing security teams to identify detailed and unique patterns that reveal attacker campaigns before they even start—neutralizing threats and avoiding damage. We welcome this partnership with Aqaio to better equip companies in this region to quickly pinpoint malicious actors and disrupt their plans,” Ken Bagnall said.
Aqaio encourages its customers and reseller partners to experience the power and effectiveness of the Silent Push platform through the free community edition. Learn more here.
About Aqaio
Aqaio is a partner to resellers, system integrators and OEMs. They deal with new technological developments, complemented and expanded by complementary solutions of market and technology leaders in the IT security environment. Aqaio also offers 2nd level support and training for our customers and their customers. The product portfolio includes high-end IT products that complement each other and can be combined into complete solutions. In addition, Aqaio offers services such as consulting, marketing support, logistics, training and technical support.
Ready to dive deeper into the world of preemptive threat intelligence? Begin your journey with the Silent Push free Community Edition today.