Sophisticated threat actors seem to always be one step ahead of detection, as defense teams using traditional cybersecurity tools struggle to keep pace.
For decades, legacy security platforms have remained largely confined to the internal enterprise perimeter, focusing on post-compromise activity and historical artifacts of previous attacks.
Leading Preemptive Cyber Defense technology is evolving traditional defense methods by providing the foundational truth that feeds AI-driven security workflows. This offers Security Operations Center (SOC) teams significantly longer lead times than legacy solutions to mitigate adversary infrastructure.
“Patient Zero”
These reactive models are tied to a “patient zero” dependency. Originally defined as the “first identified” or the “primary case,” used in epidemiological medical tracking in the 1980s, in cybersecurity the term refers to a crucial step in identifying how malware entered a network.
When discussing traditional cybersecurity platforms, “patient zero” refers to the initial victim required to generate the blocklists or signatures needed for defense, since measures are typically initiated only after a compromised victim within the perimeter is found.
By the time legacy systems identify an adversary, the threat actor has already finalized its infrastructure, launched its campaign, and begun impacting targets.
To break this traditional, reactive cycle, organizations must move away from reactive models and manual correlation toward a more proactive, deterministic approach. This is accomplished with preemptive cyber defense.

Evolving Legacy Defense with AI
Preemptive cyber defense isn’t designed to replace legacy solutions, it evolves them.
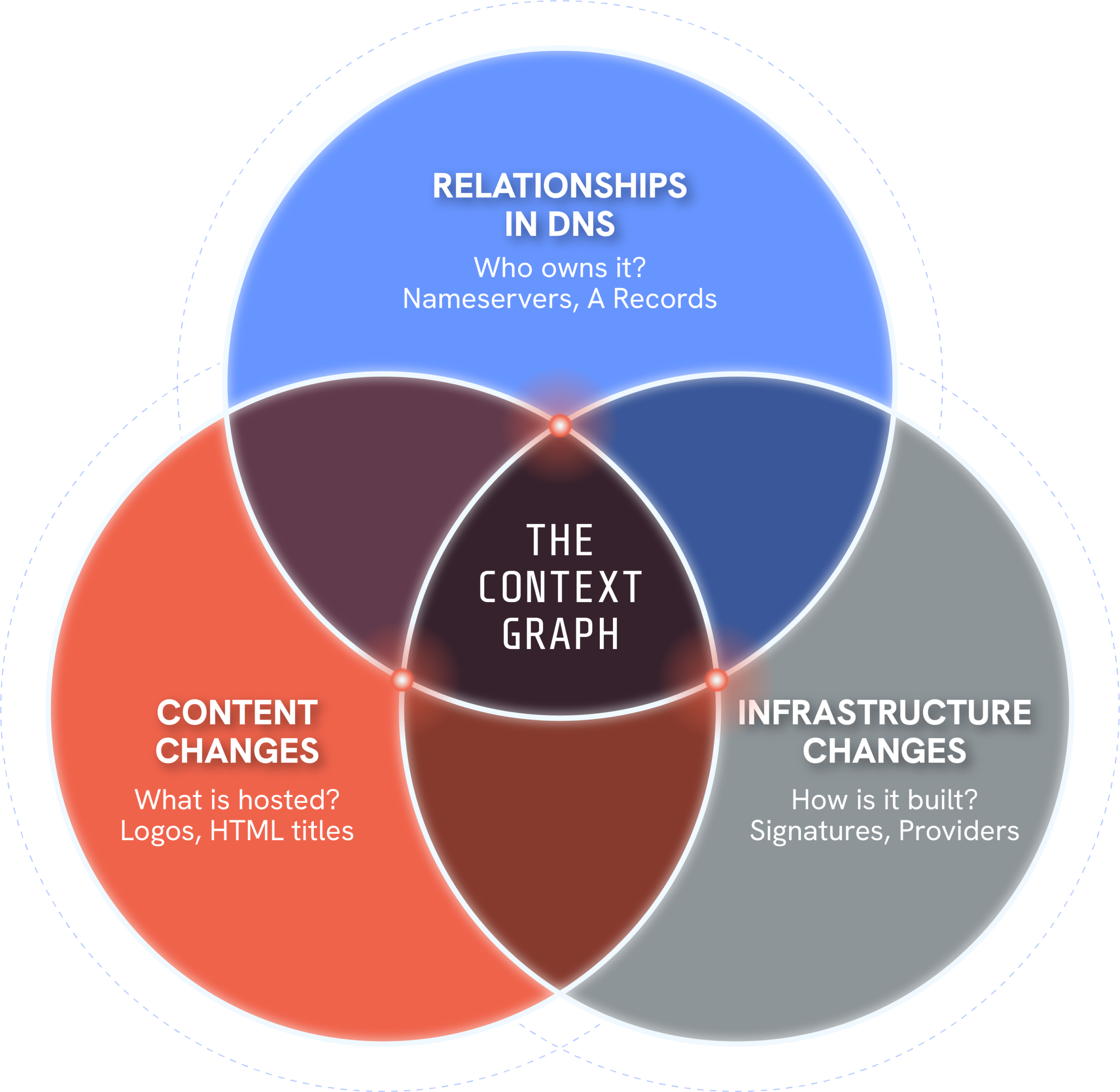
Preemptive cyber defense is designed to thwart threats before they can manifest as active attacks. Unlike traditional, reactive security, Silent Push developed a Context Graph of the internet, and a key use is for adversary infrastructure. In preemptive cyber defense, the Context Graph produces Indicators of Future Attack® (IOFA®) to map the global infrastructure that adversaries build during their staging phase, the earliest part of developing a malicious campaign.
Our preemptive cyber defense platform is organized into three core modules: Insight, Reconnaissance, and Defend. Together, they facilitate rapid triage, proactive threat detection, and automated blocking across various industries. Each module is designed to move security teams, including SOC, Incident Response (IR), and Cyber Threat Intelligence (CTI) analysts, from probabilistic risk scores to verifiable, deterministic facts.
By empowering tactical users with ground-truth data, the platform enables CISOs and executive leadership to achieve measurable risk reduction and strategic control, justifying security investments and maintaining organizational resilience.
Empowering SOC Teams
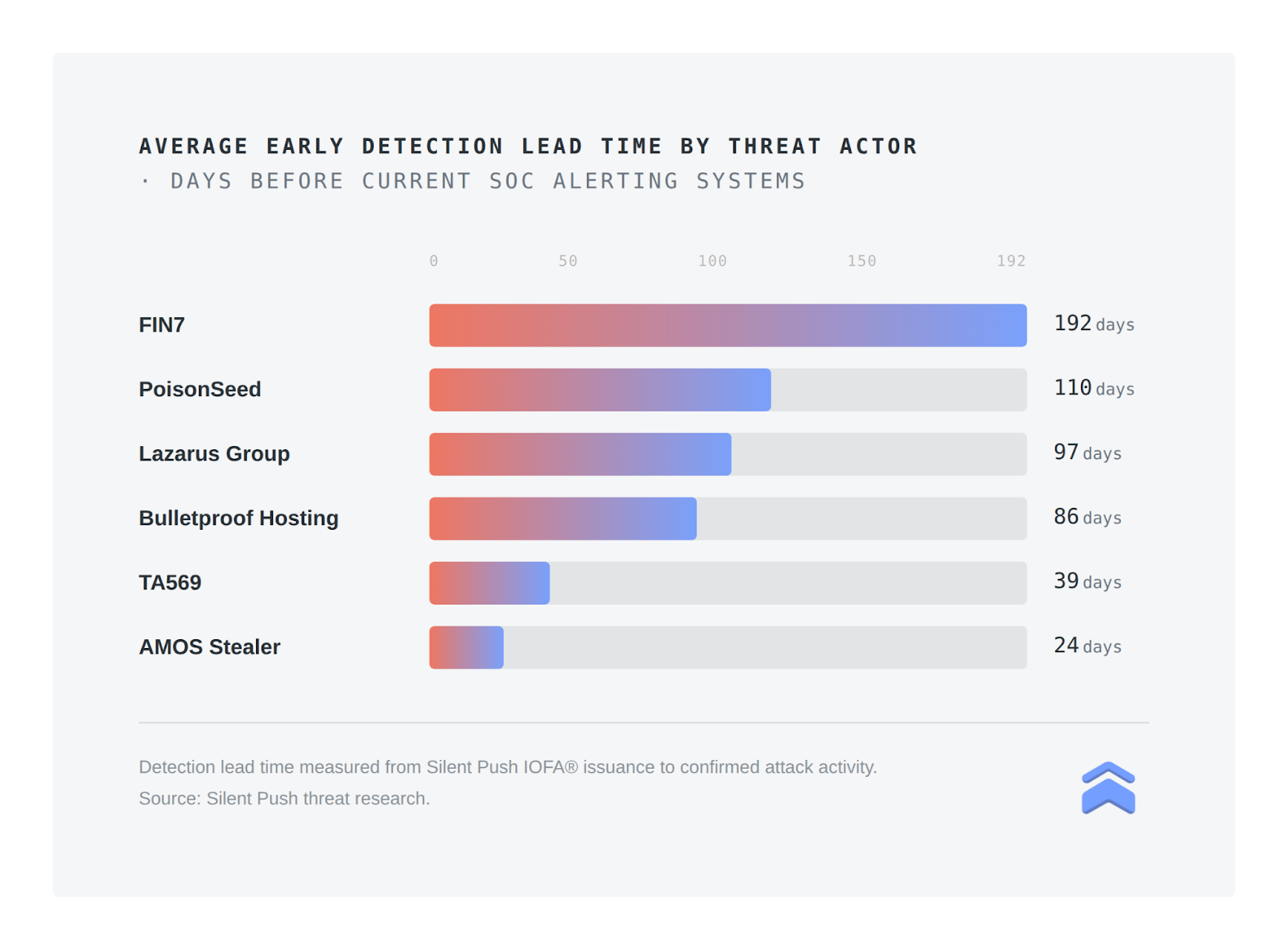
Providing game-changing lead times for SOC teams to gain significant, strategic advantages against adversaries, preemptive cyber defense empowers SOC managers with new leverage. Early detection lead times are often more than 100 days ahead of adversarial infrastructure being weaponized.
Working with a Fortune 500 media and entertainment company, we developed a case study, “Detect Adversaries 3 Months in Advance Using Silent Push Threat Check,” to demonstrate how organizations using our preemptive model can achieve an average early-detection lead time of 104 days.
By embedding Silent Push Threat Check technology into its Security Information and Event Management (SIEM) workflows, our client transformed the way it handled security alerts.
The company’s SOC team gained weeks of earlier visibility into attacker infrastructure, streamlined investigations, and achieved measurable outcomes from its investment in our preemptive cyber defense solution.
Benefits to SOC Teams
Greater lead times enable SOC teams to improve triage times with IOFA:
- Block infrastructure before an attack.
- Defining the scope of incidents.
- Utilizing the Context Graph to enable their own IOFA creation.
- Combat alert fatigue by significantly reducing false positive rates.
Continually Improving Security Posture
Preemptive cyber defense shifts organizations from a reactive to a proactive stance, enabling them to detect and disrupt threats earlier. By combining IOFA with internal telemetry and leveraging investigative findings back into detection and prevention workflows, organizations can create a continuous improvement loop. The result is earlier visibility, faster response times, and a continually improving security posture.
Adopting preemptive cyber defense empowers organizations to do more than simply accelerate investigation and response; it enables their security teams to generate their own preemptive intelligence. Each investigation performed provides insights derived from real activity observed within its environment.
When curated and operationalized, this provides an intelligence source that compounds over time–strengthening controls, refining detections, and improving prioritization. Security becomes a feedback loop of correlation and learning rather than a series of isolated incidents.
For CISOs, this translates into measurable reductions in mean time to detect (MTTD) and mean time to respond (MTTR), with fewer incidents overall, along with greater return on existing security investments. For SOC leaders and analysts, it means less noise, clearer context, and faster action. A preemptive architecture is not designed to replace the security stack. Instead it activates it, turning today’s tools into a coordinated system that sees earlier, acts decisively, and improves continuously.
Get Started
Interested in exploring the strategic advantages of the Silent Push preemptive cyber defense platform? Connect with one of our platform specialists to discover how Silent Push empowers your SOC team to neutralize adversarial infrastructure before it reaches your enterprise perimeter.
We also offer a free Community Edition that provides security practitioners and threat researchers with introductory access to the Silent Push Context Graph and specialized datasets.
FAQs
- What is an IOFA?
Silent Push Indicators of Future Attack (IOFA) enable security teams to immediately block adversary infrastructure, which allows organizations to respond quickly and disrupt attacker actions before impact.
- How does the Context Graph differ from a threat feed?
Our Context Graph essentially represents a fundamental evolution beyond the standard threat feed by delivering a comprehensive map of the internet that reveals deeply connected, behavioral, and historical relationships between global entities.
While traditional feeds are limited to providing a static list of known malicious indicators—identifying “what” is bad (such as Indicators of Compromise (IoCs))—the Context Graph provides the ground-truth data to explain “why” a particular infrastructure poses a risk. By mapping staging activity and temporal data, it shifts SOC teams from reactive alerting toward predictive, preemptive cyber defense.
- Does the Silent Push Context Graph integrate with my SIEM?
The Silent Push Context Graph facilitates seamless integration across your security stack—including SIEM, SOAR, and TIP platforms—through robust APIs, TAXII feeds, and native integrations such as Splunk. By ingesting IOFA and rich contextual data directly into existing workflows, organizations can automate enrichment, validate alerts with deterministic facts, and significantly minimize manual investigation timelines.

