No Place to Hide: Following a Serial Ransomware Affiliate from LockBit, Black Basta, and Qilin to The Gentlemen
Key Findings
- In early February 2026, Silent Push Analysts detected a Cobalt Strike Command and Control (C2) configuration tied to a ransomware affiliate using CountLoader and Cobalt Strike payloads with a unique watermark.
- As we reviewed the Check Point Research incident response report on The Gentlemen Ransomware-as-a-Service (RaaS), we detected the mentioned Cobalt Strike IP address, which we had found 2.5 months before public reporting, and attribute this incident to the same ransomware actor that we discussed in our CountLoader research.
- Our Indicators of Future Attack® (IOFA) block downstream attacks involving Cobalt Strike, which ransomware actors and Advanced Persistent Threats (APTs) often leverage.
- We previously reported identifying more than 10,000 infected IP addresses as part of the RaaS-related SystemBC botnet malware family in our February 2026 blog and March 2026 client report.
2025
1473793097 and 1357776117 are fingerprinted to a single affiliate.2025
2026
2026
2026
We urge all organizations to take protective measures by setting up automated blocking via integrating the Cobalt Strike IOFA feed directly into their firewall, SIEM, or EDR via an API or STIX/TAXII feed.
Executive Summary
Silent Push has been tracking ransomware threat actors for several years. Following the deep-dive research and reporting in July-August 2025, chronicling our discovery of a new malware loader we named “CountLoader, on September 18, 2025, we published a public blog, “CountLoader: Silent Push Discovers New Malware Loader Being Served in 3 Different Versions,” sharing our findings.
Our analysis highlights a critical intersection between malware infrastructure and specific threat actors: the discovery of Cobalt Strike watermarks (1473793097) and (1357776117). These unique license identifiers provide the technical “fingerprint” to link the activity directly to a ransomware affiliate with verifiable ties to the Black Basta, LockBit, and Qilin attacks.
We were inspired by the recent Digital Forensics and Incident Response (DFIR) report from Check Point, which highlights an intrusion involving SystemBC and Cobalt Strike. From this, our research team was able to tie our earlier ransomware affiliate findings to the Gentlemen RaaS.
Since Cobalt Strike is often used by APTs and ransomware actors, we urge organizations to block infrastructure related to our Cobalt Strike IOFA feeds.
Incident
The Check Point DFIR report highlights the use of a Cobalt Strike C2 at IP address 91.107.247[.]163, tied to the intrusion and eventual ransomware deployment by the RaaS, The Gentlemen.
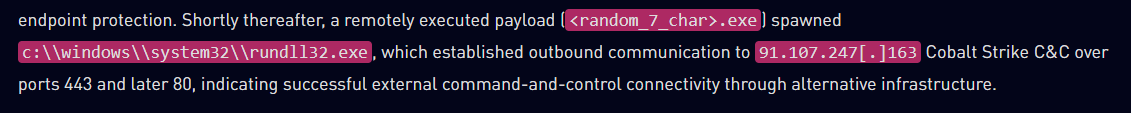
The Cobalt Strike C2 IP was flagged as an IoFA in our report on February 8, 2026.
![Screenshot of Silent Push Total View of IP Address 91.107.247[.]163](https://www.silentpush.com/wp-content/uploads/gnt-image-2.png)
We found the indicator using the same unique Cobalt Strike detection method we developed in our analysis of CountLoader. We can attribute this ransomware intrusion with high confidence to the same ransomware actor that is part of the Black Basta, LockBit, and Qilin ransomware groups. Additionally, with the DFIR report from Checkpoint, we can tie this same actor to also be leveraging The Gentlemen ransomware.
Our unique detection methodology ensures that our tracking remains persistent even when a threat actor pivots between ransomware groups; by identifying the individual behind the keyboard rather than just the brand they serve, we maintain a high-confidence trail on this affiliate throughout their three-year tenure across LockBit, Black Basta, Qilin, and now The Gentlemen.
Historic Incidents
In our CountLoader blog, we highlight external research tied to the observed Cobalt Strike watermark (and, by extension, the CountLoader campaign we have been tracking) directly to BlackBasta, Qilin, and LockBit ransomware activity. To provide additional background, we are listing several external sources to highlight the historical trail of this threat actor (below):
- https://op-c.net/blog/sap-cve-2025-31324-qilin-breach/
- https://medium.com/@Intel_Ops/hunting-black-bastas-cobalt-strike-96a81a6ea781
- https://unit42.paloaltonetworks.com/edr-bypass-extortion-attempt-thwarted/
- https://thedfirreport.com/2025/01/27/cobalt-strike-and-a-pair-of-socks-lead-to-lockbit-ransomware/
Get Started in Preemptive Cyber Defense
Interested in learning more about the Silent Push preemptive cyber defense platform?
Talk to one of our platform experts and see how Silent Push can help your team neutralize threats before they reach your perimeter.
We also offer a free Community Edition, giving security practitioners and researchers introductory access to the Silent Push platform and datasets.
Continuing to Track RaaS
Our preemptive cyber defense and research teams will continue to track and report on RaaS groups, including The Gentlemen, LockBit, Black Basta, and Qilin, as well as on the abuse of Cobalt Strike, throughout 2026.
If you or your organization has any information to share regarding the findings in this report, we would welcome the opportunity to collaborate.

