Post-Sanction Persistence: Triad Nexus' Operations Infrastructure Reborn as Threat Actor Distances Activity from FUNNULL CDN

Key Findings
- Following U.S. Treasury sanctions in 2025, Triad Nexus has matured its operational security, employing geographic fencing to blind U.S. investigators while simultaneously laundering its infrastructure through account muling and a rotating network of “clean” front companies.
- The network has industrialized brand theft on a global scale; its catalog includes “pixel-perfect” clones of everything from high-end luxury goods to public services.
- To counter the automated obfuscation used by Triad Nexus, SilentPush’s CNAME Chain Lookup provides a quick forensic method for multi-tiered redirection path analysis and exposing the underlying “laundered” infrastructure for real-time defense.
Executive Summary
Triad Nexus is responsible for over $300 million in daily reported losses, totaling billions annually, driven largely by sophisticated “pig-butchering” and virtual currency scams. Individual victim losses average $150,000, highlighting the high conversion nature of its operations. Despite federal sanctions in 2025, the group has reinstated its global fraud engine, shifting its focus toward emerging markets while maintaining a persistent threat to Western enterprise assets.
Triad Nexus continues to pose a direct risk to corporate brand integrity and customer trust. The group manages an industrialized catalog of impersonation assets targeting:
- Banking and Fintech: Payment portals for more than 25 global institutions (including Wells Fargo and Bank of America) used for large-scale credential harvesting and “pig-butchering” scams.
- Luxury Retail: High-fidelity clones of brands such as Tiffany and Cartier to intercept high-value consumer transactions.
- Global Logistics: Exploitation of services, including the Vietnam Post, to facilitate regional personally identifiable information (PII) theft.
Standard reactive security measures are insufficient against Triad Nexus’ automated rotation of deceptive infrastructure. Mitigation requires a shift toward preemptive cyber defense and high-fidelity visibility.
Table of contents
- Key Findings
- Executive Summary
- Background
- The Audacity of “Infrastructure Laundering”
- An Industrialized Catalog of Brand Impersonation
- Geographic Evasion and the U.S. Block
- The Rise of Clean Front Companies
- Fighting Back with CNAME Chain Mapping
- Tracking Triad Nexus’ FUNNULL CDN Infrastructure Changes
- CNAME Chain Complexity Requires New Tools – Silent Push Delivers!
- Get Started
- Continuing to Track Triad Nexus/FUNNULL CDN
Background
Triad Nexus is a sprawling cybercrime ecosystem rooted in organized crime groups across Asia. Historically identified by its reliance on the FUNNULL Content Delivery Network (CDN), the network has facilitated a massive surge in investment scams, money laundering, and illegal gambling operations since at least 2020. The illicit network serves as the primary backbone for “pig-butchering” schemes and fraudulent financial portals that target global consumers.
In addition to these fraud operations, the group specializes in high-fidelity brand impersonation, weaponizing the digital identities of Global 2000 companies to deceive victims.
The Audacity of “Infrastructure Laundering”
An effective technique in the Triad Nexus’ arsenal is “Infrastructure Laundering.” Rather than relying solely on low-reputation servers, Triad Nexus weaponizes “account mules” to steal or illicitly acquire accounts at major enterprise cloud providers. This provides its scams with the “appearance of legitimacy,” high speed, and professional performance that even tech-savvy Western audiences can’t resist.
Our team’s investigation reveals that the “bulletproof” backbone of this operation remains AS152194 (CTG Server Limited). However, to prevent total takedowns, the group segments its infrastructure into multiple ASN pools, preventing investigators from identifying the entire network.
The major providers currently being exploited in these laundering schemes include:
- Amazon (AS16509)
- Cloudflare (AS13335)
- Google (AS396982)
- Microsoft (AS8075)
An Industrialized Catalog of Brand Impersonation
Triad Nexus is linked to the majority of virtual currency investment scam websites reported to the FBI. The network has industrialized brand theft on a global scale.
Its catalog includes “pixel-perfect” clones of everything from high-end luxury brands to public services. We have documented active campaigns impersonating:
- Luxury & Retail: Tiffany, Cartier, Chanel, Coach, Macy’s, eBay, Rakuten, and Kering.
- Financial & Investment: iTrustCapital, Western Union, MoneyGram, and Etsy.
- Public Services: TripAdvisor and a sophisticated, deceptive clone of the Vietnam Post (vietnampost[.]vn).
To facilitate its rapid fund siphoning, Triad Nexus sites offer payment portals linked to over 25 global financial giants, including Goldman Sachs, Royal Bank of Canada, Bank of America, and Wells Fargo.
Its cryptocurrency acceptance is equally broad, supporting not only BTC and ETH, but also USDC, TRON, MATIC, and TRC20 tokens.
Geographic Evasion and the U.S. Block
In a cynical attempt to evade law enforcement monitoring post-sanctions, Triad Nexus implemented a counterintuitive “U.S. Block.” Visitors attempting to access many of their sites from U.S. IP addresses are being met with a “451 Unavailable for Legal Reasons” error message stating, “The region has been denied.”
As the network continues to withdraw from direct U.S. exposure to avoid detection, it has been pivotally expanding into the Spanish, Vietnamese, and Indonesian markets. Using localized templates to target these regions, its goal is to ensure its illicit profits continue to flow even as it hides from the U.S. Treasury’s primary gaze.
The Rise of Clean Front Companies
Before the May 2025 sanctions were issued, Triad Nexus was already taking steps to further distance itself from the tainted “FUNNULL” brand. The group launched a series of “clean” front companies—entities that use professional branding and egregious lies to manufacture trust. They include:
- Bole CDN (cdnbl[.]com): In a classic case of temporal fraud, the site claims to have served 10,000 clients since 2015. Domain records, however, prove it was registered in March 2025.
- CDN1[.]ai: This front falsely claims to work with global brands such as Nestlé to lure in legitimate developers.
- Other Fronts: Investigators have identified Yunray[.]ai, CDN5[.]com, and CTGCDN as part of the network’s shell game.
The fronts often rely on human operators for recruitment, specifically utilizing the Telegram account t[.]me/sara5433 to communicate with prospective buyers. Because they lack any visible “FUNNULL” branding, the entities are nearly impossible for the average user to identify as malicious.
Fighting Back with CNAME Chain Mapping
As Triad Nexus adopts automation in its infrastructure defense, we documented a shift from using nine primary, stable CNAME domains for routing traffic to over 175 randomly generated CNAME domains, each of which connects clusters of malicious client websites to acquired IP addresses.
Mapping the infrastructure now requires the CNAME Chain Lookup.
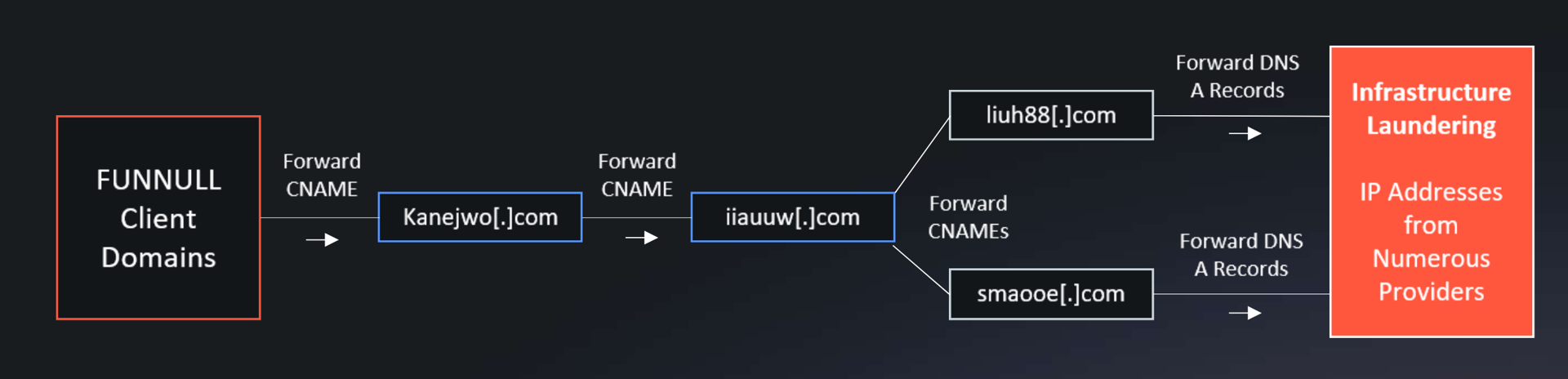
Traditional lookups only show a single link, but CNAME Chain Mapping reveals the entire automated path used to hide the final destination. A typical malicious chain now looks like this:
- Client Domain (e.g., tripdsdvjea[.]com)
- Intermediary CNAME 1 (e.g., kanejwo[.]com)
- Intermediary CNAME 2 (e.g., iiauuw[.]com)
- Final A Record (The laundered IP address, often found on AS152194)
Tracking Triad Nexus’ FUNNULL CDN Infrastructure Changes
Triad Nexus’ FUNNULL CDN clearly takes “infrastructure as code” to heart, as it automates CNAME domain changes across vast amounts of client domains.
One example of an interesting Triad Nexus FUNNULL client domain that provides visibility into the technique of new CDNs and CNAMEs naming conventions is alicdn9858[.]com (Total View), which actually has CNAME records from FUNNULL dating back to 2022 alongside 11 different FUNNULL CNAME domains, the first of which was mapped in July 2022, from funnull[.]vip.
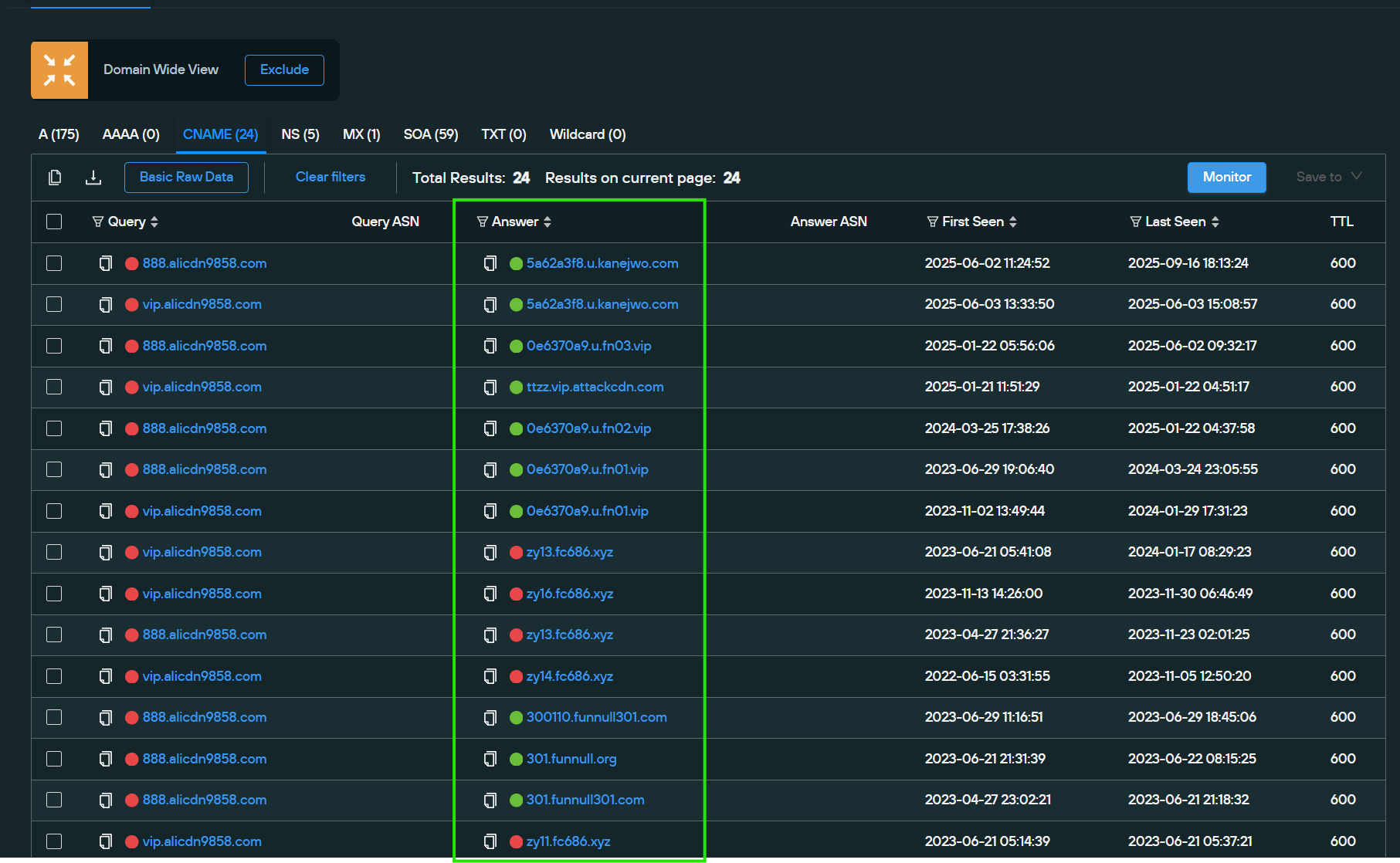
In the image shown above, we can see that the domain rotated through the following CNAMEs:
- funnull[.]org
- funnull[.]vip
- funnull6[.]com
- funnull301[.]com
- fn01[.]vip
- fn02[.]vip
- fn03[.]vip
- fc686[.]xyz
- dns888[.]xyz
- kanejwo[.]com
- attackcdn[.]com
From the list above, it is clear that significant pattern diversity is at play here. “FUNNULL,” “FN,” or “FC” are no longer referenced in the new CNAME domains, a previously typical pattern.
We can also see how Triad Nexus uniquely mapped its infrastructure to continue infrastructure laundering on trusted service providers such as Amazon, using kanejwo[.]com as an example CNAME domain. Reviewing the A records confirms that this CNAME maps to successful exploitation of Amazon’s reputation. It was detected in September 2025, when its IP addresses were mapped to the CNAME.
Interestingly, in this example, Amazon appears to have the network on its radar, as FUNNULL has seemingly stopped actively mapping stolen Amazon IPs to it.

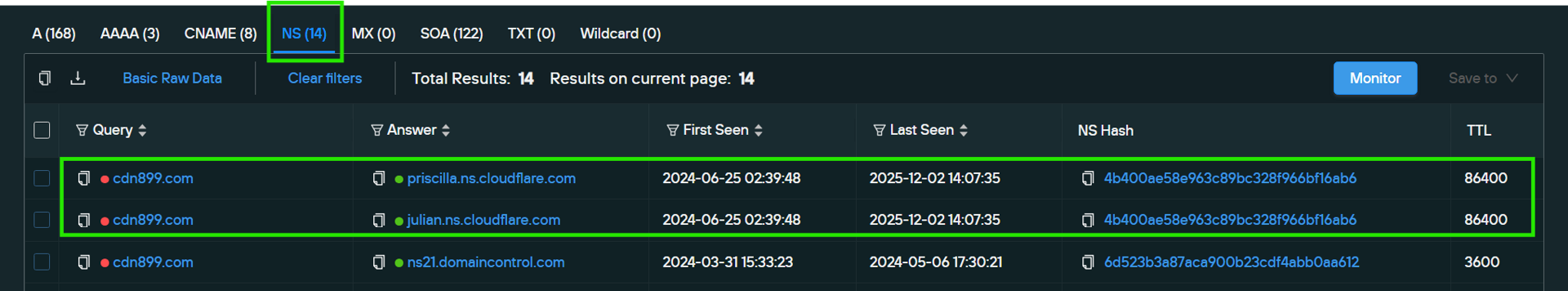
Another interesting, recently-discovered Triad Nexus CNAME, cdn899[.]com, (Total View) has a history dating back to December 2020, with this domain mapped to numerous IPs across various ASNs. In April 2024, Amazon IPs were mapped here for a month before being removed. Then, for four months, neither the CNAME nor its client infrastructure resolved.
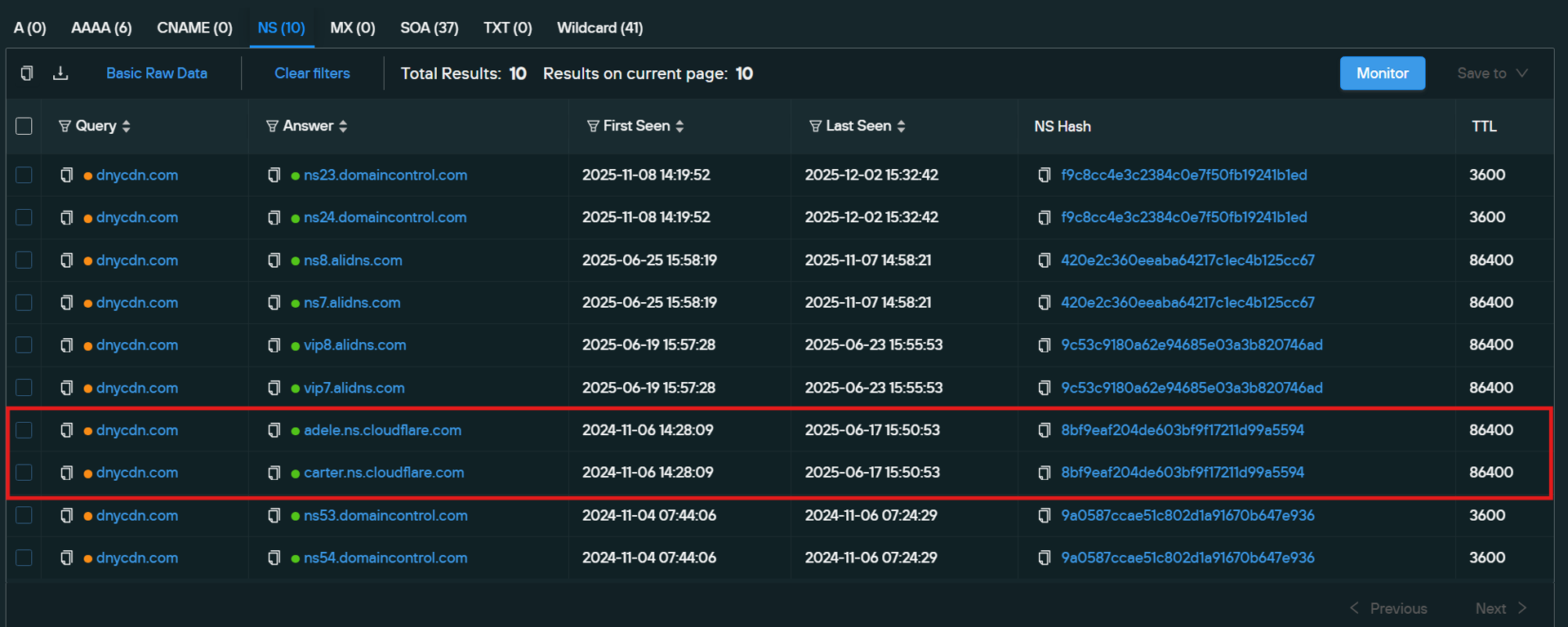
After this period, in September 2024, Cloudflare IPs were once again mapped to this CNAME, and they have been live for over 14 months as of the time of writing. The Cloudflare IPs propagate through the CNAME because Cloudflare Name Server records were set up for that cdn899[.]com CNAME domain, (as shown below):
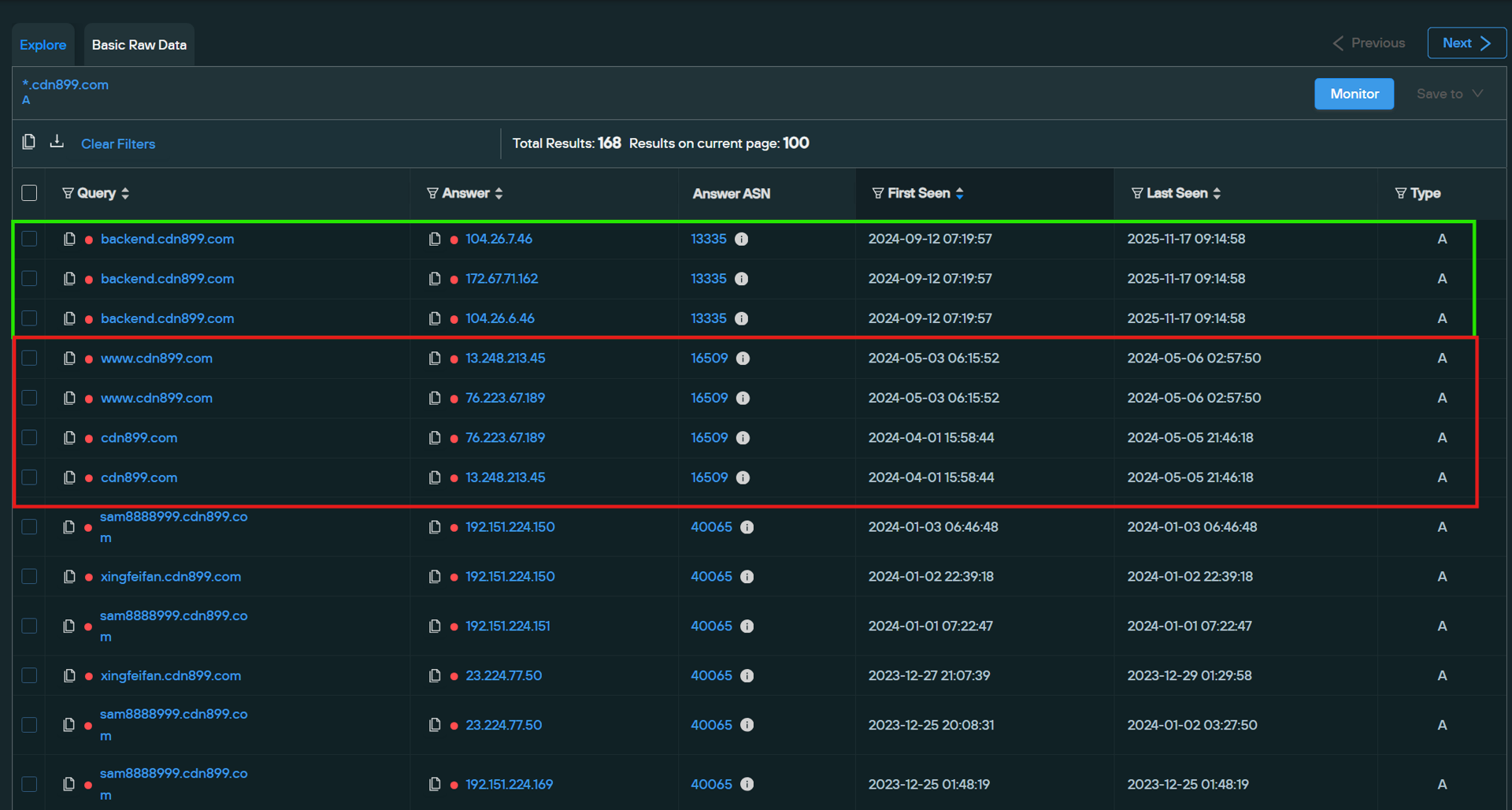
Additionally, cdn899[.]com is mapped to enterprise cloud hosts, where it can be seen assisting in the resolution of a network of fake casino websites used for money laundering alongside other low-quality adult and gambling content, all targeted to Chinese audiences.
Reinforcing the clustering hypothesis, each CNAME appears to be set up differently. This aligns with our 2024 report, in which we determined that the unique CNAMEs and CNAME subdomains themselves were what helped segment the client infrastructure. It even helped differentiate the types of scams being run, although that pattern no longer holds entirely true.
Examples of FUNNULL CNAMEs more accurately showcase all three techniques: automated CNAME failover, the new CNAME naming schema, and infrastructure laundering.
- The CNAME mapping domain smaooe[.]com (Forward A Lookup), switched between DNS A records from Amazon IPs, Cloudie (ASN 55933), CTG Server (ASN 152194), and briefly one IP address from the Netherlands, RoyaleHosting (ASN 212477), all in June of 2025. It has only recently stopped having enterprise IPs mapped to it; the last one was Microsoft, which lasted from September 2025 to early October 2025. As of this writing (April 2026), the only IP mapped to it is from ASN 55933, Cloudie, based in Hong Kong.
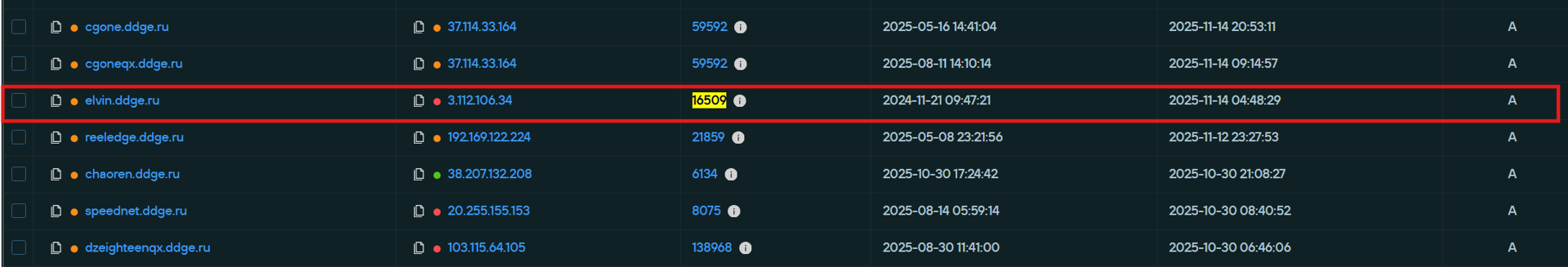
- CNAME domain ddge[.]ru (Forward A Lookup) has been mapped to IPs from nearly 40 different ASNs throughout 2025, including IPs from Amazon’s 16509 ASN. On any given week, these mappings only last about a month before they are removed. What’s worth noting about this example is the shortened timeframe. Previously, some Amazon IPs were mapped for months at a time, with one IP mapped for seven consecutive months in 2025 and another for five.

- Some of the new Triad Nexus CNAMEs are directly impersonating other major CDNs, such as the CNAME domain dnycdn[.]com, which appears to impersonate the Oracle-owned Dyn domain registration and hosting service.
- This CNAME has been mapped to multiple enterprise services; however, it has had Microsoft IPs from ASN 8075 routinely mapped to it for months at a time, with only a few Microsoft IPs mapped there from June 2025 until November 2025. Cloudflare IPs have also remained mapped there for months, with Cloudflare Name Server records remaining associated for nearly seven months.

CNAME Chain Complexity Requires New Tools – Silent Push Delivers!
While investigating Triad Nexus’ complex CNAME chains and IP address acquisition schemes, our team realized we needed a new way to map the entire CNAME chain, rather than manually performing multiple CNAME forward/reverse queries for each domain.
So we built something new!
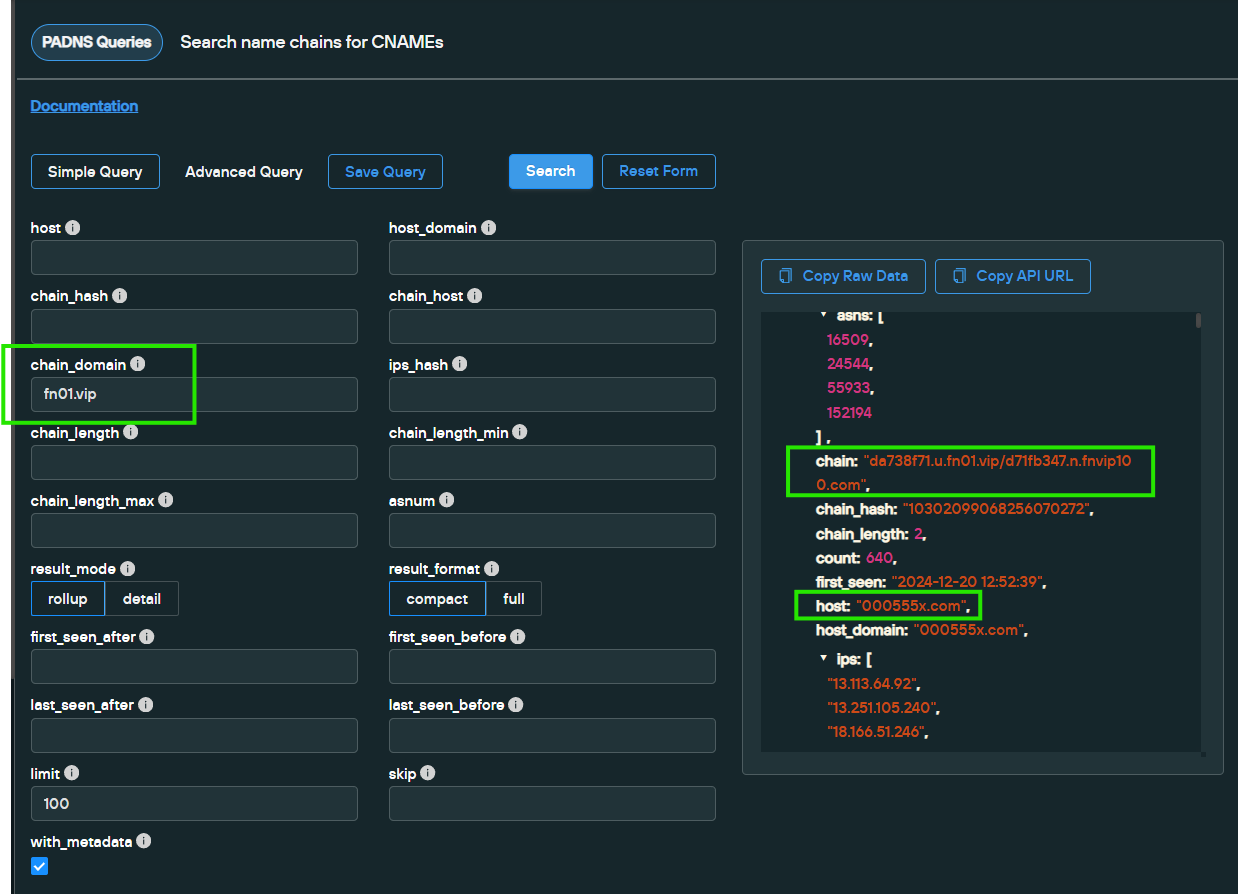
Using the new Silent Push CNAME Chain Lookup tool, defenders can now submit any of the previously seen CNAME domains into the form’s “chain_domain” field, which then returns lists of the entire CNAME chains seen, along with the host mapped through the chain and the IP addresses mapped to that host.
This new tool offers multiple search options that return the full scope of CNAME domains, CNAME chains, and the IPs used to keep a given domain online. It is, essentially, the perfect tool for researching networks that chain together client domains and their IP addresses with multiple CNAME domains.
An example of how it works can be seen here:
CNAME Chain Lookup for “fn01[.]vip” FUNNULL Domain
chain_domain = fn01.vip
Get Started
Interested in learning more about the Silent Push preemptive cyber defense platform?
Talk to one of our platform experts to see how Silent Push can help your team neutralize threats before they reach your perimeter.
We also offer a free Community Edition, giving security practitioners and researchers introductory access to the Silent Push platform and datasets.
Continuing to Track Triad Nexus/FUNNULL CDN
Our preemptive cyber defense and research teams will continue to track and report on the Triad Nexus, FUNNULL CDN, and the new cloud hosting fronts.
If you or your organization has any information to share regarding the findings in this report, we would welcome the opportunity to collaborate.

