- Company
Silent Push Inc. ©2025
Silent Push Threat Analysts recently discovered two hostnames, api2.cloudns[.]net and web2.cloudns[.]net, belonging to ClouDNS, that pointed to an IP address managed by threat actor Prolific Puma.
ClouDNS is a hosting company based in Bulgaria that appears to work with numerous enterprise organizations like Hostway, KIA, Der Spiegel, Houston Community College, and more. When we contacted them, ClouDNS quickly updated the DNS records for the affected hostnames.
While we were not able to detect malicious activity around this discovery, we want to make our community aware of potential vulnerabilities:
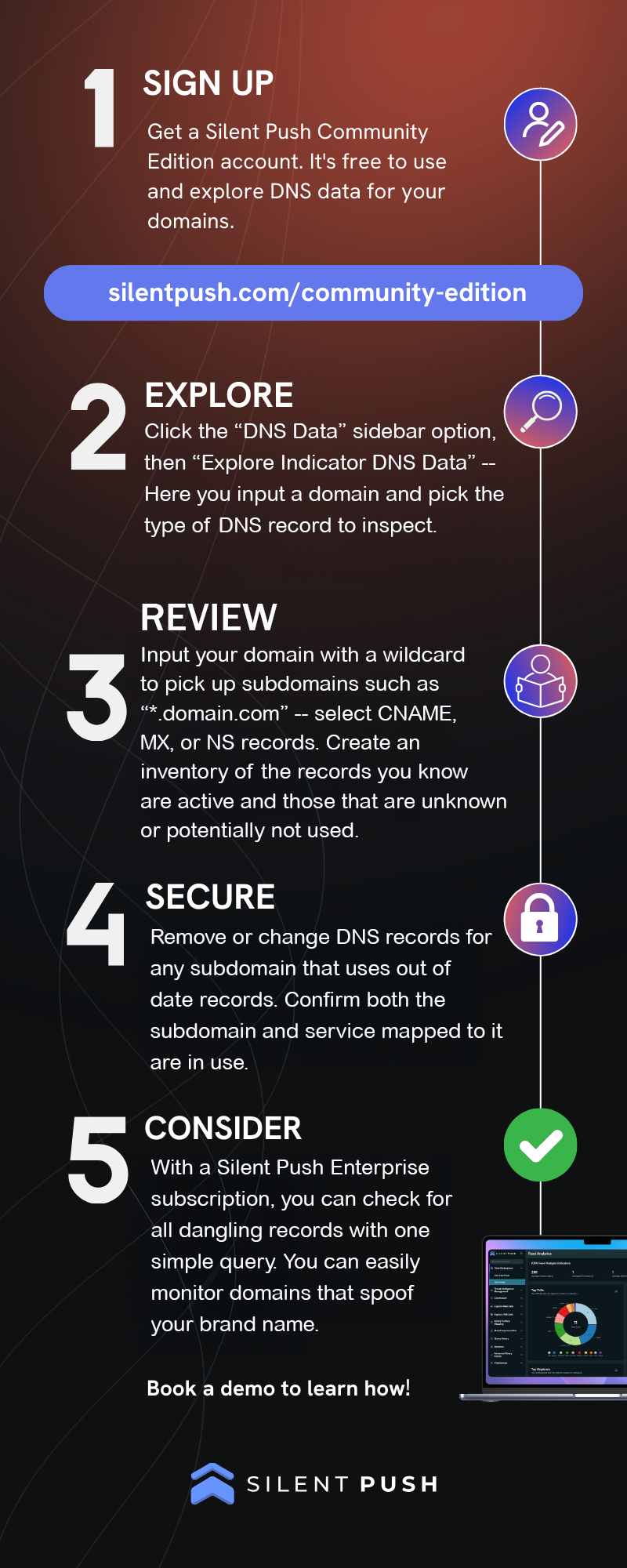
We encourage organizations to regularly check their DNS settings for hostnames pointing to IP addresses they don’t control or might not be using. Silent Push makes this process simple, enabling users to easily check DNS settings of interest by using our free Silent Push Community Edition account.
While the nature of this public-facing blog is to make our community aware of vulnerabilities associated with forgotten domains, Silent Push believes all domains associated with Prolific Puma offer some level of risk.
Our analysts have constructed a Silent Push IOFA™ Feed that provides a list of Prolific Puma Indicators of Future Attack™ (IOFA™). Silent Push threat researchers continuously track over a thousand active domains for Prolific Puma as we observe and monitor changes to this actor’s infrastructure. New discoveries, campaigns, and TTP changes will be immediately reflected in our feeds.
For operational security reasons, we are unable to publicly share the exact details of how we are tracking Prolific Puma infrastructure.
Silent Push IOFA™ Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA™ Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition offers free access to our threat-hunting and cyber defense platform, featuring a range of advanced offensive and defensive lookups, web content queries, and enriched data types, including both the Silent Push Web Scanner and Live Scan.
Watch our presentation at mWISE 2024 to learn more about how we track threat actors like Prolific Puma.
Silent Push is the first and only provider to reveal unique threat patterns of all attacker infrastructure existing on the clear net and dark web.
We go beyond Indicators of Compromise (IOCs) and expose IOFA™ through our proprietary behavioral threat modeling. This allows security teams to reveal attacker campaigns before they even start – neutralizing threats and preventing damage.
Request a demo today to see how your team can block threats before they become problematic.
In this blog, we’ll demonstrate how you can use Silent Push Community Edition to scan across the dark web using 50+ unique parameters, and obtain timestamped intelligence that reveals Tor infrastructure linked to activity on the public web.
Silent Push Community Edition is a free threat hunting and cyber defense tool featuring a range of advanced queries and lookups – built on a powerful first-party database of enriched DNS data – that allows users to locate known and hidden threat infrastructure on the public web and dark web.
The dark web is a hidden corner of the internet that is not accessible through standard browsers and search engines.
Dark websites reside on the the deep web, which refers to all online content that is not indexed for search, such as private databases, online banking sites, and password-protected content.
Domains on the dark web are commonly referred to as “onion” sites, due to the the top-level domain “.onion” that’s used by websites on the Tor network – a specialized web browser used to navigate the dark web, that serves the vast majority of hidden websites.
Other dark web top-level domains do exist – such as .i2p on the Invisible Internet Project Network – but for the purposes of this blog, we’re going to focus on the Tor network.
Onion sites use “hidden services” and encryption methods that rely on Tor’s built-in directory to locate and load a website, instead of the standard DNS resolution methods used to navigate the public web.
This complex routing scheme provides a high level of anonymity for anyone who uses the dark web, making it a digital haven for cybercriminals involved in all manner of threat activity – including the selling of confidential company data obtained during a security breach, typically as part of a ransomware attack
Stolen data is offered for sale on the dark web in exchange for cryptocurrency, on illegal marketplaces – such as the infamous Silk Road site that was shut down by the FBI and Europol in 2013 – along with drugs, counterfeit goods, access to illegal software, and other illicit services.
Due to the sheer volume of illegal activity it hosts, the dark web can be reliably called a “target rich environment”, but its architecture makes it incredibly difficult for law enforcement and security teams to proactively locate threat infrastructure on the Tor network as they would do on the public internet, and investigate Advanced Persistent Threat (APT) groups that take advantage of the dark web’s secretive and decentralized nature.
Cybersecurity tools that monitor .onion sites for stolen data and authentication details are relatively commonplace, even within small scale IT support operations, but these utilities are limited to passive searches that don’t allow security teams to hunt for specific elements of dark web infrastructure linked to a set of identifiable Tactics, Techniques and Procedures.
Dark web scanning in Silent Push is the process of proactively locating (rather than passively monitoring) Tor sites linked to threat activity that targets an organisation, brand, or supply chain, and allows teams to make attributable links between .onion sites and associated clear web activity, aiding in the public identification criminal behaviour.
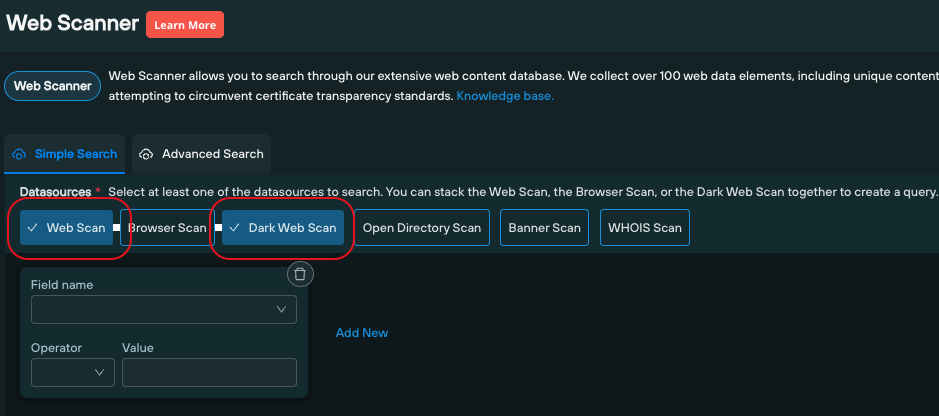
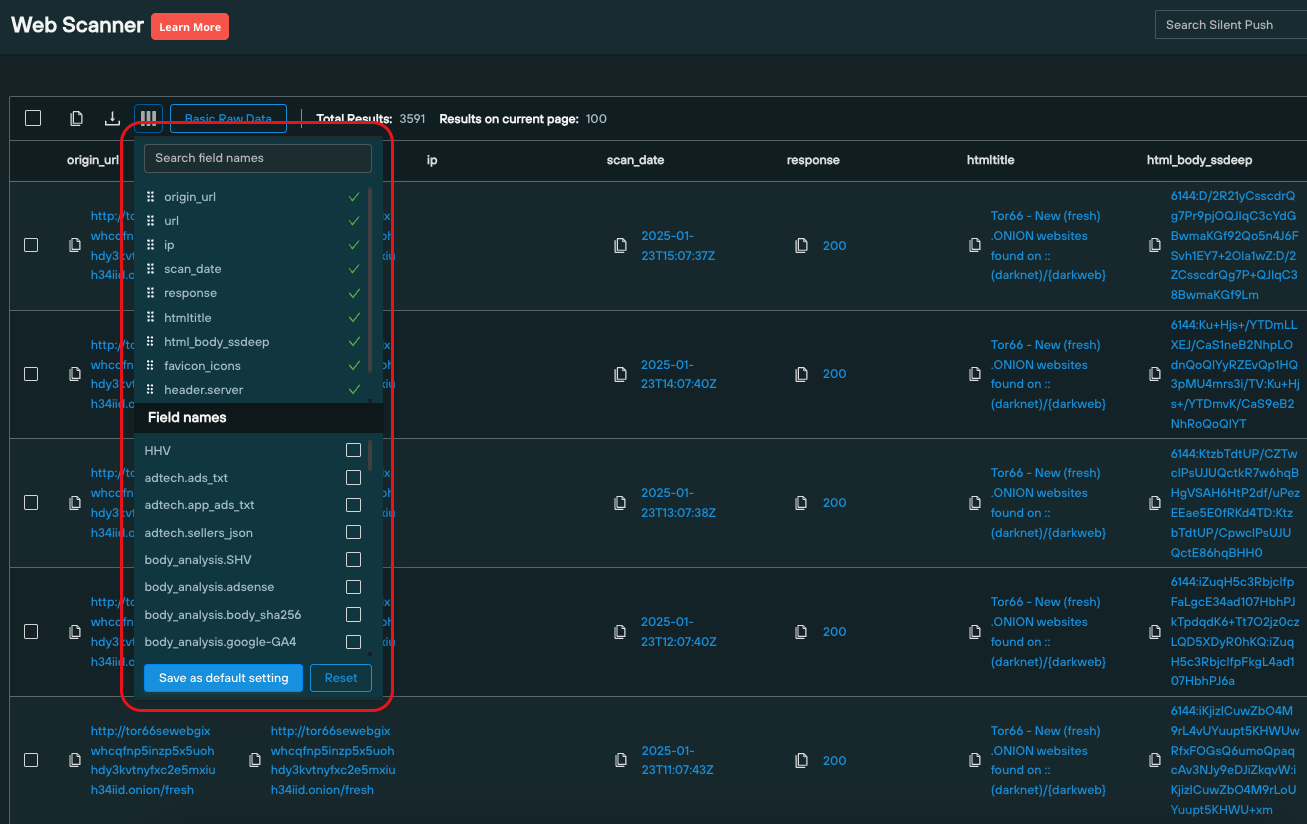
Silent Push Community Edition contains a dedicated dark web scanning utility that breaks .onion sites down into 50+ categories (including HTML body data, the favicon used, a real-time snapshot, and a range of JavaScript parameters) that mirror the parameters we use to collect data on standard public websites, which can be searched across within the same tool – Silent Push Web Scanner.
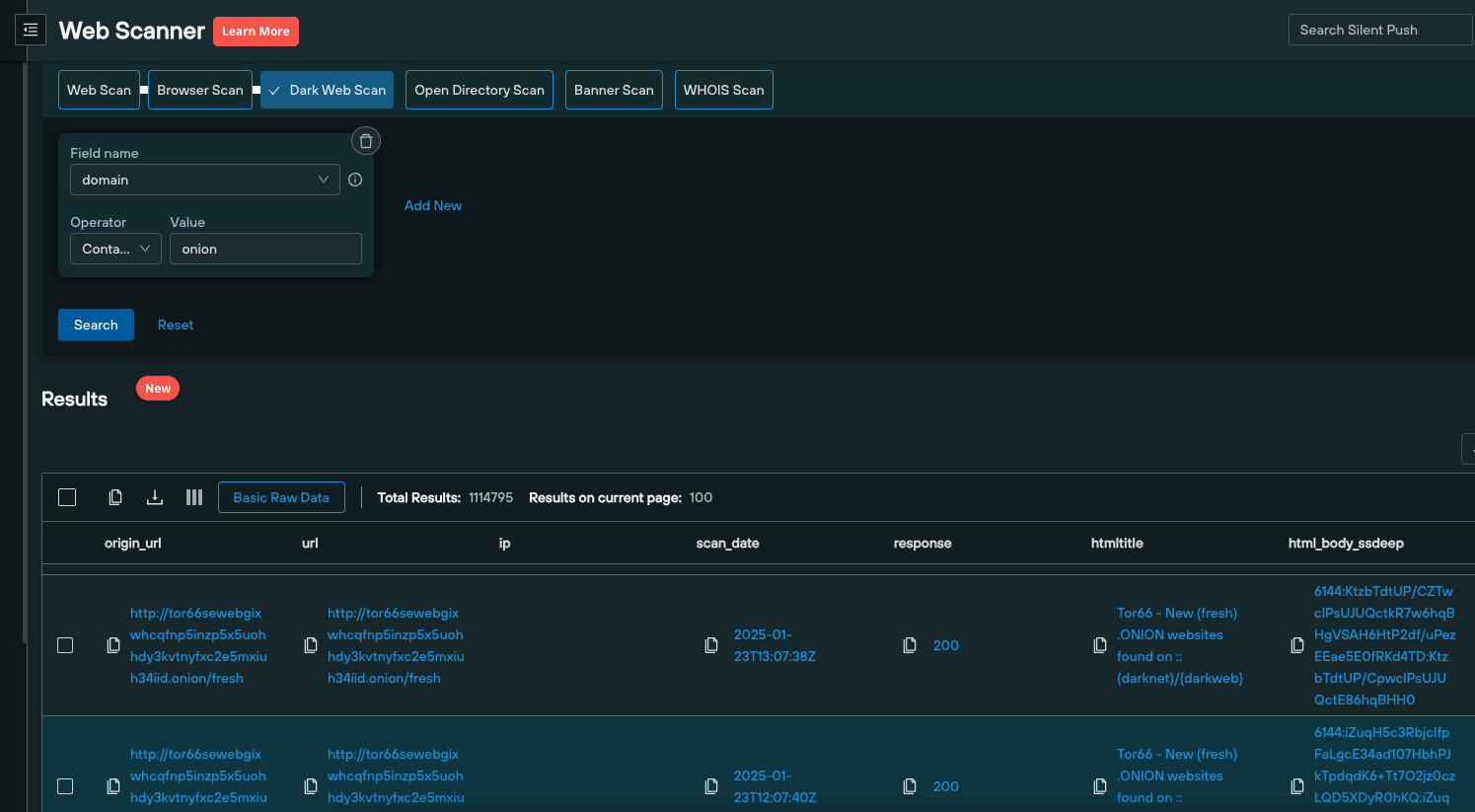
This allows teams to create a behavioral fingerprint of attacker activity that can be used to search across historic and real-time clear web and Tor website datasets for matching content, using a single query, to facilitate the public unmasking of dark web threat activity.
Let’s take a look at a few examples…
Here’s a .onion site selling illegal access to PayPal and eBay accounts.
First, we executed a Live Scan to gather a real-time screenshot, and capture additional on-page data to use in a pivot:
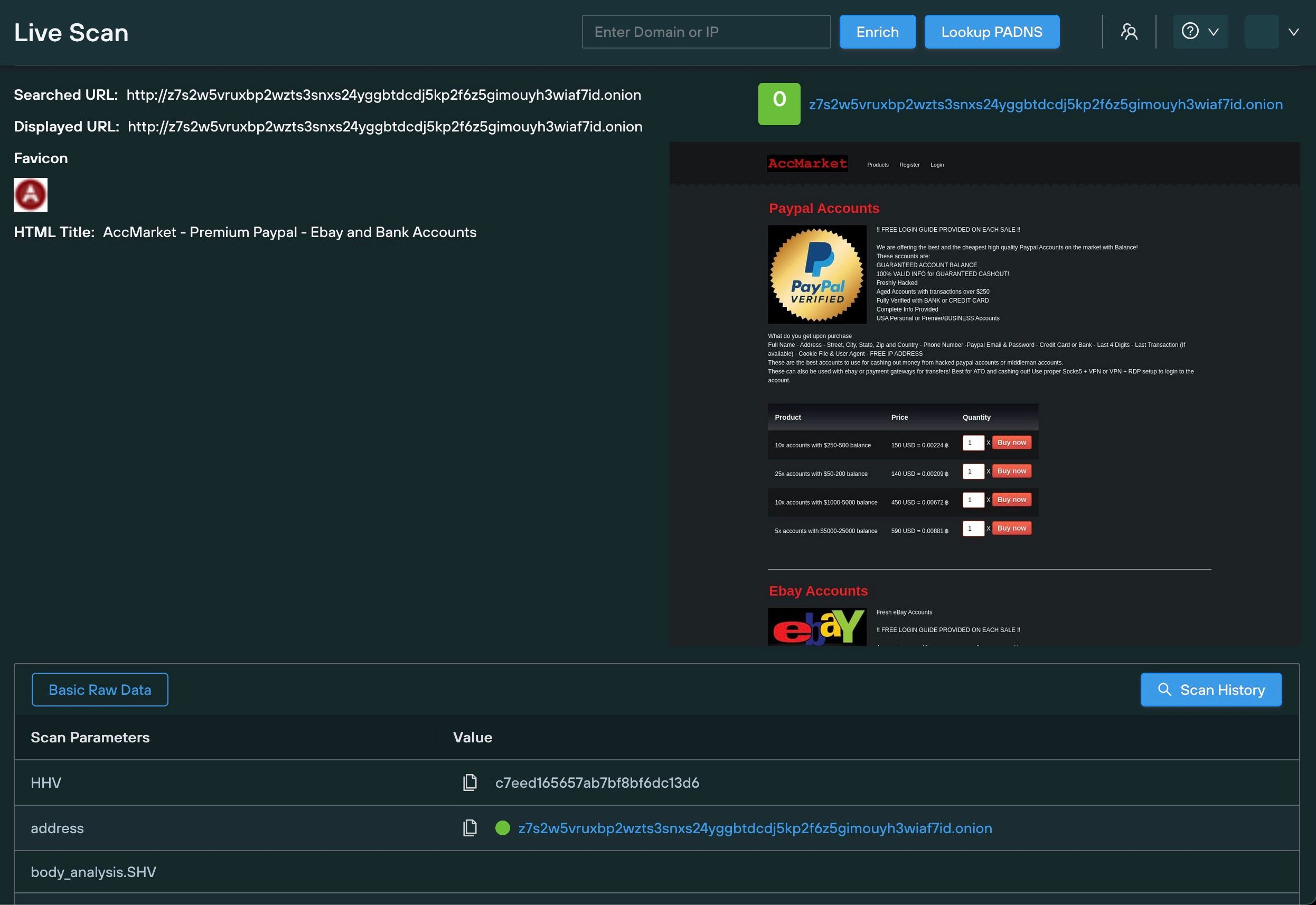
Once we’d established a dataset, we executed a Web Scanner query that cross-referenced the MD5 hash of the dark web favicon with our public web dataset, to find matching results, including an IP address linked to an Apache server:
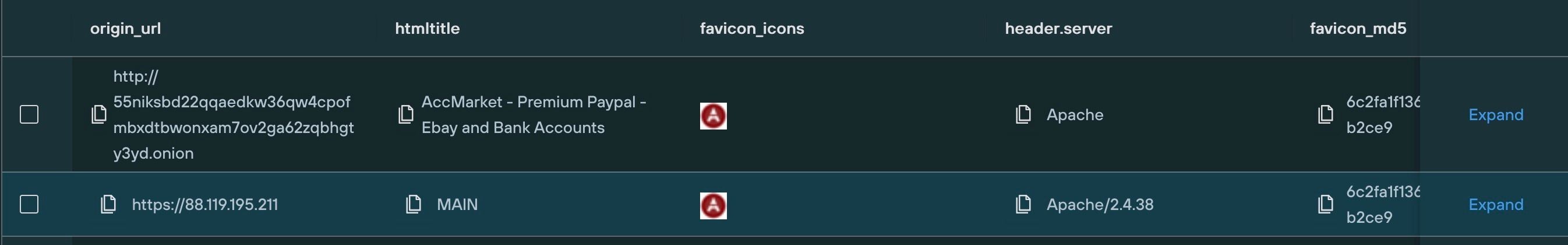
Based on the distinctiveness of the hash – and the absence of any other IPs associated with this particular favicon – it’s possible that the public IP hosts the hidden Tor service in question.
We’ve used this Tor site and favicon as an example, but any piece of on-page data can be utilized.
Unique JavaScript hashes are another effective pivot point.
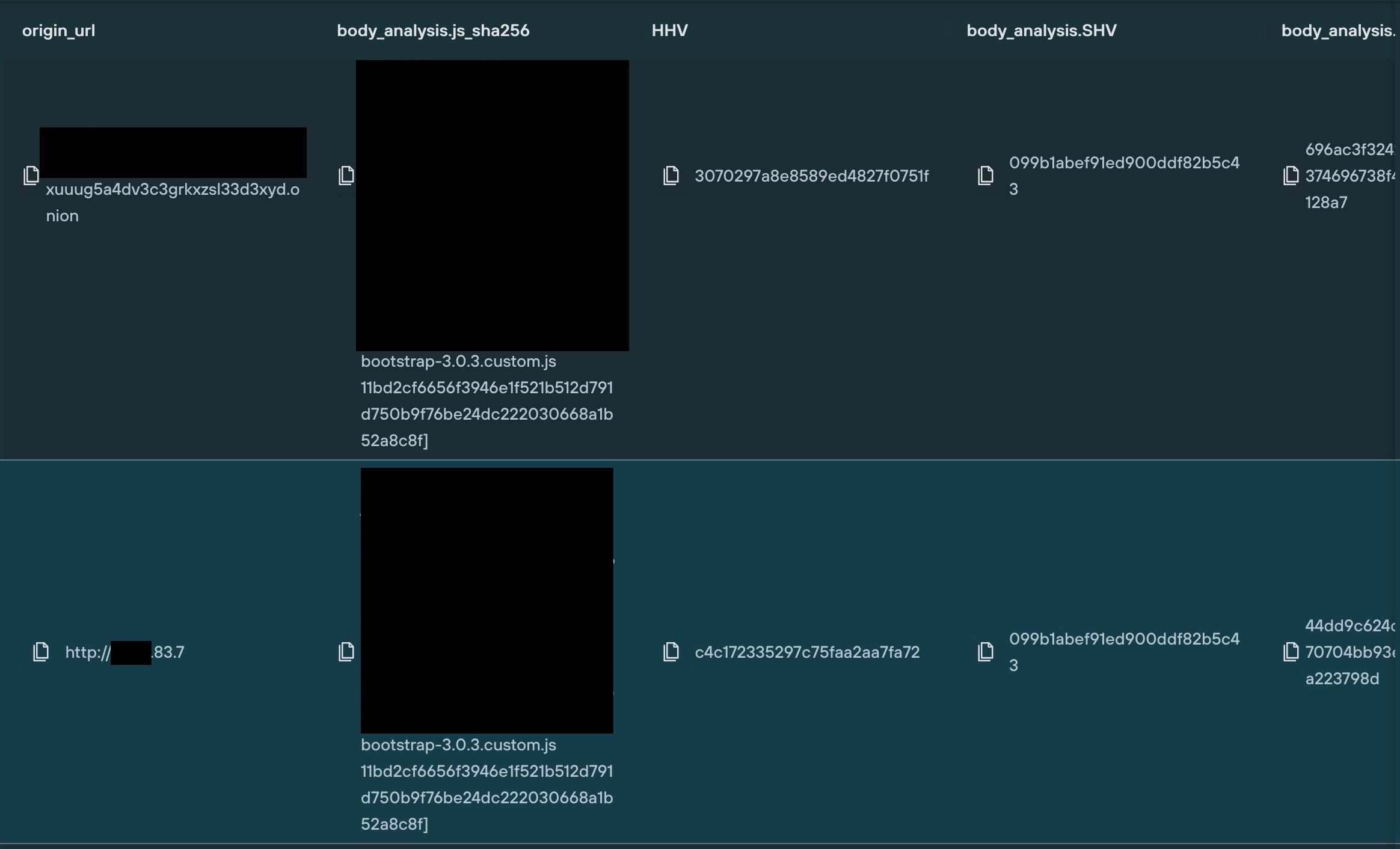
Our aggregation engine generates a searchable hash value of all JavaScript files referenced on a dark web or public web page, allowing teams to systematically search across both datasets simultaneously for JavaScript elements shared by Tor sites and standard websites.
In this example, we’ve located a .onion site containing a unique JavaScript MD5 hash (using the “body_analysis.js_sha256” field), and executed a query that locates a public web site containing the exact same JavaScript code:
Silent Push Community Edition dark web scanning provides timestamped results sets of all the .onion sites we collect data on, so that security teams can evaluate attacker behaviour over time, and analyze how threat infrastructure is being modified to avoid detection.
Here’s an example that includes multiple snapshots of a .onion site taken on the same day:
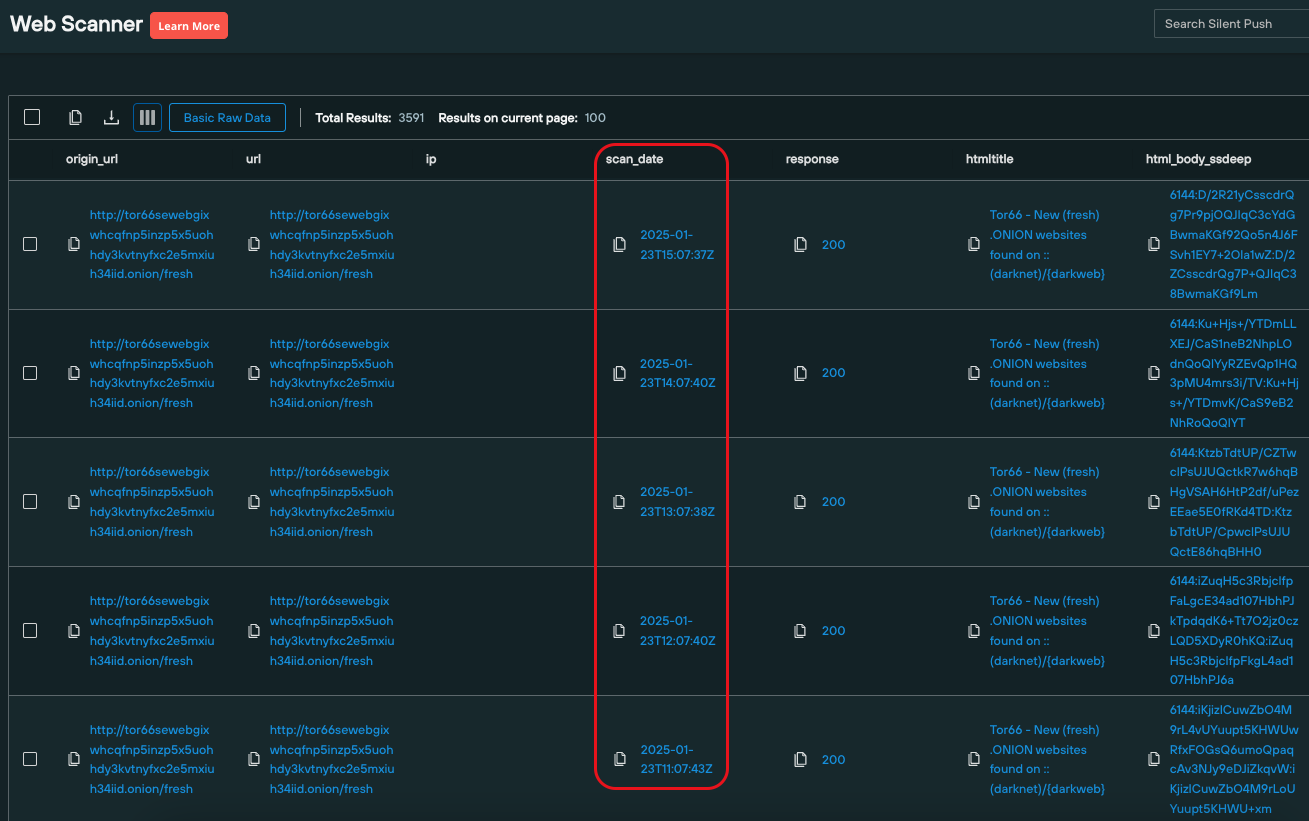
Dark web scanning results sets can also be amended to include or exclude any number of specified data categories, to drill down into hidden infrastructure for identifiable content and make tangible links with public domains.
Fields can also be searched independently of other categories, for quicker access to critical intelligence.
Silent Push Community Edition is a free threat hunting and cyber defense tool featuring a range of advanced queries and lookups – built on a powerful first-party database of enriched DNS data – that allows users to locate known and hidden threat infrastructure on the public web and dark web.
Silent Push Threat Analysts have discovered that the Araneida Scanner, which appears to be based in part on a cracked version of Acunetix, a popular web app vulnerability testing tool, is being used for illegal purposes, including conducting offensive reconnaissance on potential target sites, scraping user data, and finding vulnerabilities for exploitation.
Araneida was recently used in a reconnaissance effort against one of our partners, which is what initially prompted our investigation.
Additional investigation has indicated that third parties are promoting Araneida on platforms such as Telegram and selling hundreds of thousands of stolen credential sets.
The Telegram channel provides guidance on using the tool for malicious purposes. Some threat actors using the Araneida scanner boast of taking over thousands of websites, using funds obtained from malicious activities to buy luxury cars, and reveling in wreaking chaos on tech websites.
Silent Push Enterprise users have access to two dedicated IOFA Feeds containing all the true positive domains and IP addresses we have gathered during our research.
For operational security reasons, we are unable to share the exact specifics of each query and pivots utilized. Silent Push Enterprise customers have access to a dedicated Araneida Scanner TLP: Amber report, which contains the relevant data types and pivot points we used to track the infrastructure referenced in this blog.
Register for our free Community Edition to use all of the tools and queries mentioned in this blog.
Silent Push Threat Analysts received intelligence from a partner organization that identified an aggressive scanning effort on their website using an IP address previously associated with a FIN7 campaign. However, we didn’t have full confidence that FIN7 controlled the IP address at the time of the scanning. The IP address featured specific metadata, “Araneida Customer Panel,” which we quickly confirmed was a key to uncovering more unique IP addresses hosting this service.
Our team discovered that a scanning tool called “Araneida – WebApp Scanner” is being publicly sold and used by threat actors to conduct offensive reconnaissance on potential target websites, scrape user data, and find vulnerabilities for exploitation.
We also discovered another cracked tool that is owned by an entity that uses Mandarin on its login page and an HTML title in Mandarin. Silent Push Threat Analysts haven’t found a public sales process for this product yet, but the same Chinese-language panel has been hosted on 20 unique IP addresses, indicating some diversity in deployments.
Both appear to be based on cracked, unauthorized versions of Acunetix, a popular web app vulnerability testing tool.
Araneida was recently used in a reconnaissance effort against one of our partners, which initiated our current investigation. Both Araneida and the Chinese language panel using this cracked enterprise software could be used for reconnaissance prior to launching sophisticated offensive attacks.
Our team has executed granular content scans in the Silent Push Web Scanner to locate and traverse Indicators Of Future Attacks (IOFAs) related to the cracked Acunetix control panel infrastructure.
Araneida admins are also actively marketing the tool’s criminal capabilities on Telegram and selling hundreds of thousands of credential sets stolen through Araneida.
Both threat actors are using legacy Acunetix SSL certificates on active control panels, which provides a solid pivot for finding some of this infrastructure, particularly from the Chinese threat actors.
The Araneida Scanner has a unique setup that is important for defenders to understand in order to detect and block:
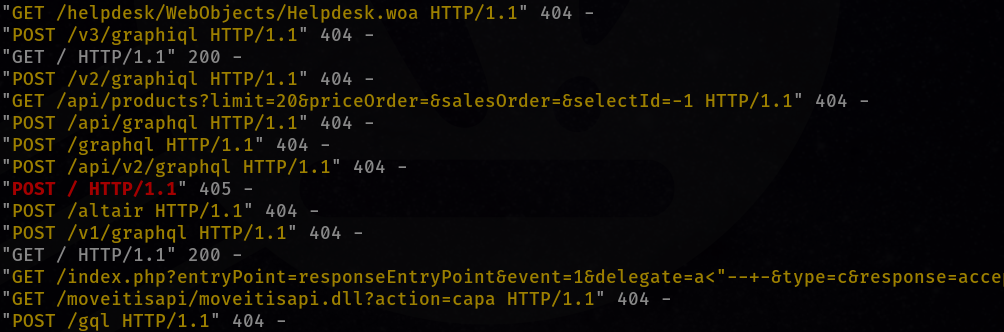
Based on the intelligence shared with us by a partner regarding the aggressive scanning effort, our team began researching an IP address that had hosted content and specific metadata.
We quickly confirmed the data and that additional websites were using this unique Araneida hosting service. Further investigation of these websites revealed they shared proprietary information associated with Acunetix.

The utility used to scan our partner’s network featured the name “Araneida” but also used information from Acunetix, suggesting the presence of cracked software.
After making this assumption, our team contacted the Invicti team, which owns the Acunetix product, and they quickly confirmed our suspicions.
The Invicti team confirmed that a cracked version of Acunetix was being sold. They also confirmed that there were no impacts on their clients—the integrity of data at Invicti was never at risk, and this is an isolated incident.
We appreciated the Invicti team’s quick and transparent confirmation and the additional details they provided.
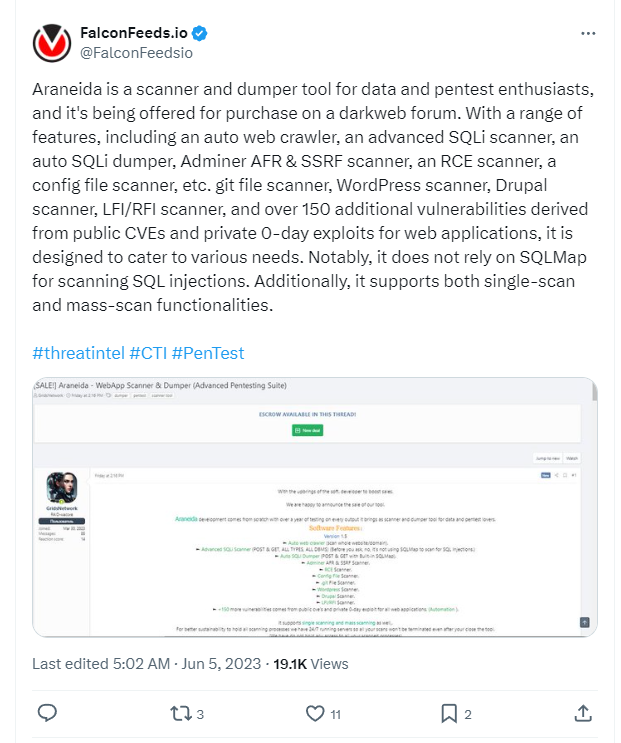
Several threat intelligence vendors and researchers discussed Araneida publicly on June 5, 2023, with FalconFeeds[.]io apparently being the first to share details:
On the same day, Chris Duggan of TLP R3D Intelligence was the first to connect Araneida to Acunetix:
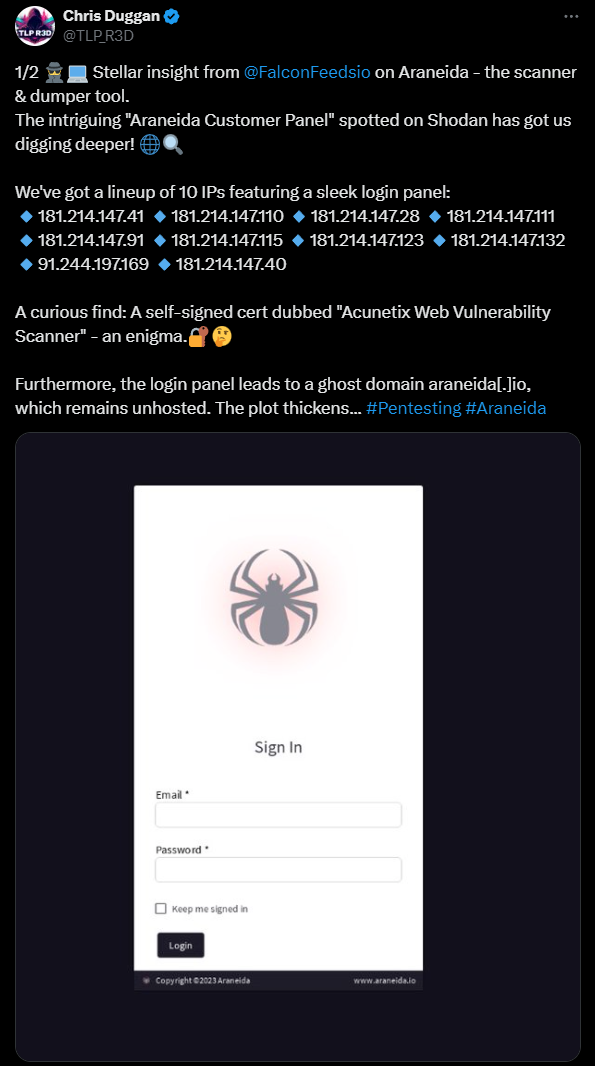
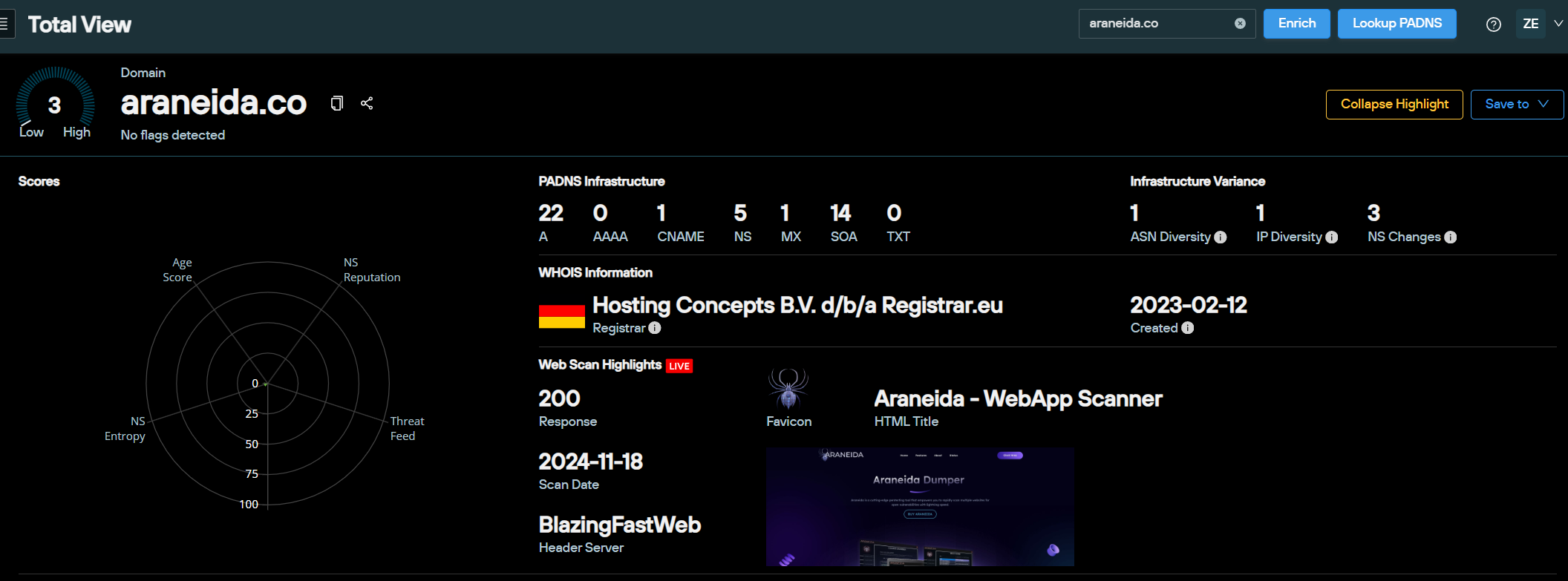
Duggan was also the first to flag the domain that is still selling the Araneida Scanner: araneida[.]co
Our team was able to determine that the Araneida Scanner is still being sold in 2024 via araneida[.]co, which was a domain created in February 2023:
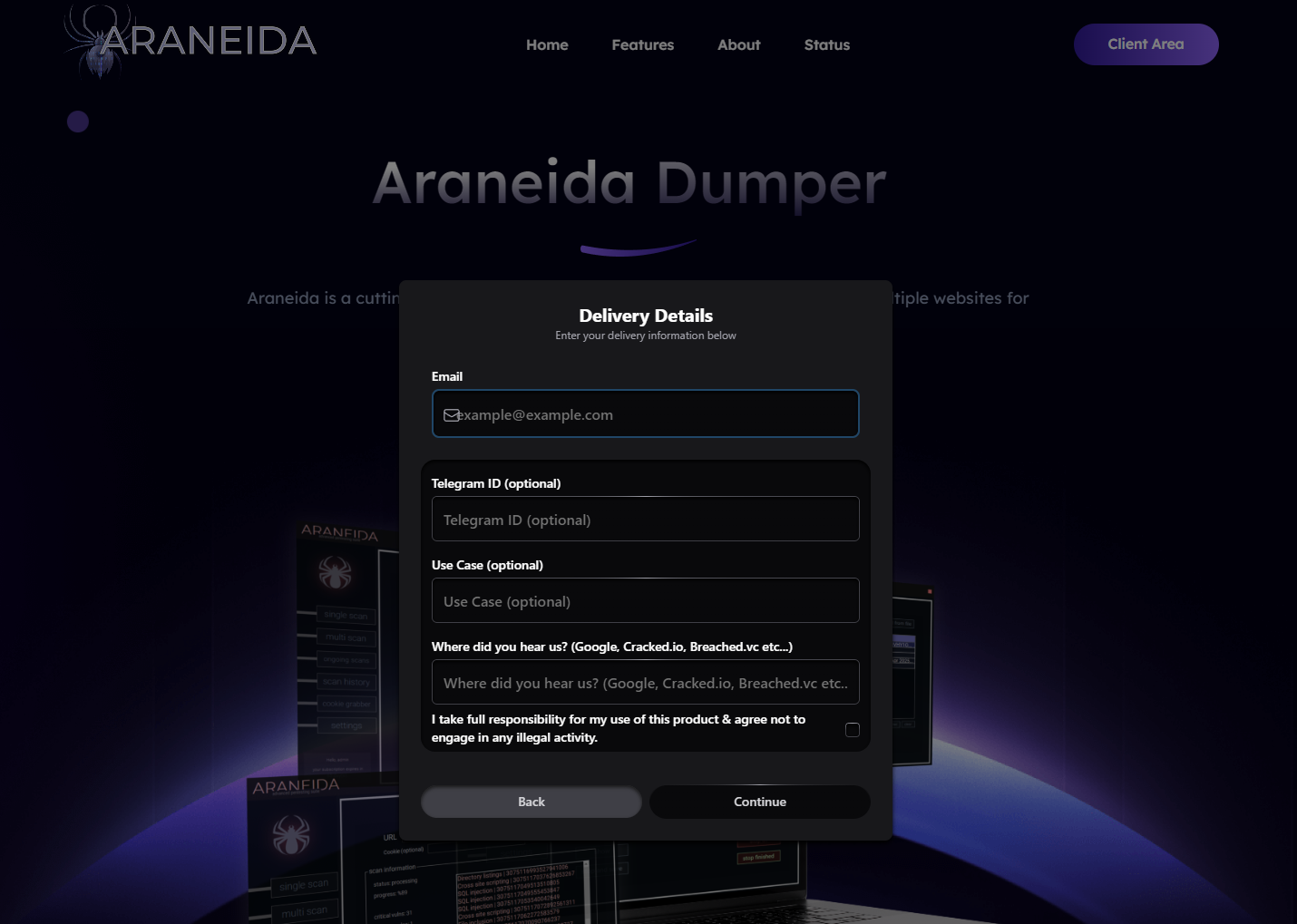
Inside the scanner product, this is what the client looks like after login:
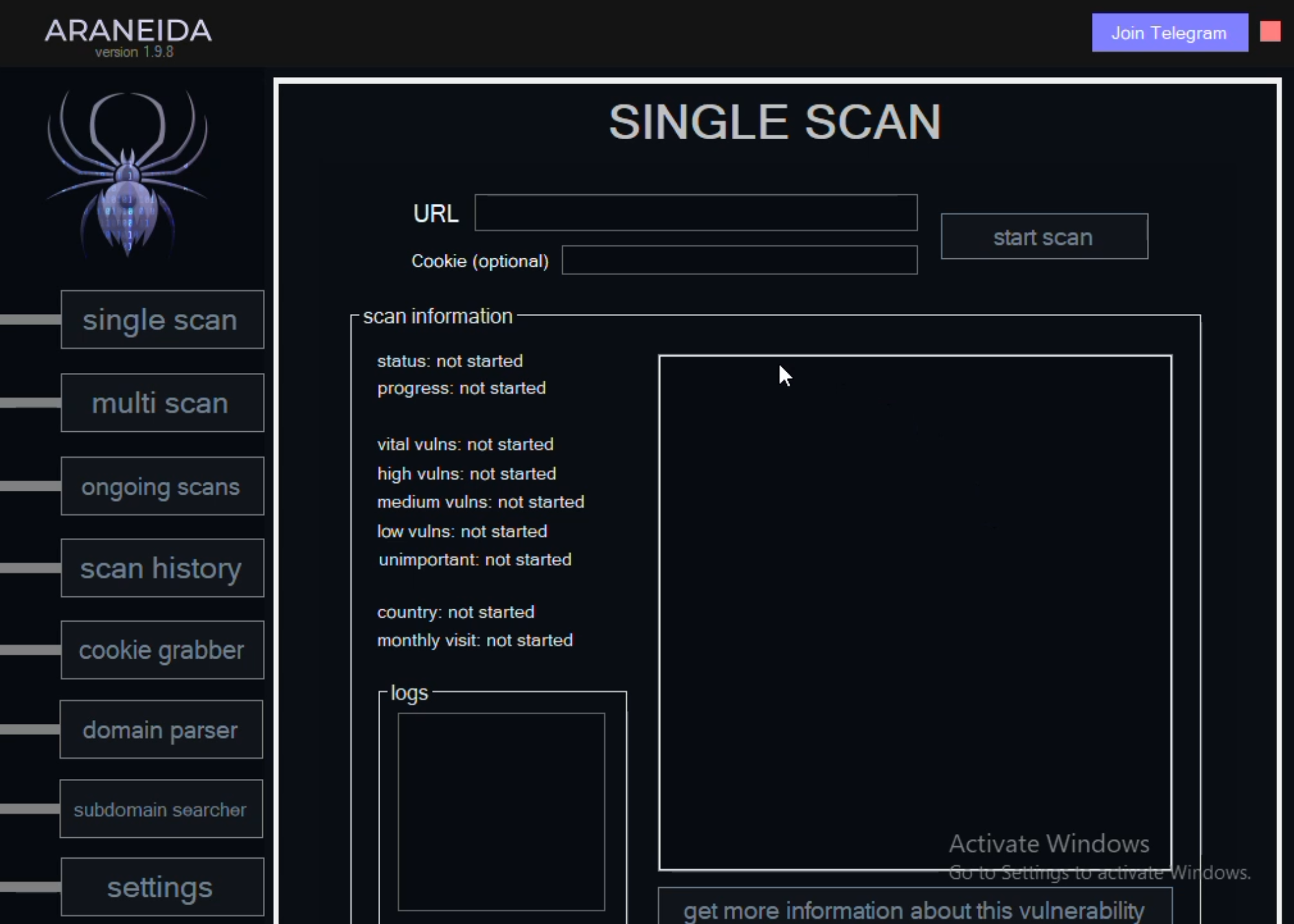
This is a brief video showing the features in the Araneida Scanner:
The video clip above highlights features in the Araneida scanning product
Between September 2023 and March 2024, 36 unique IP addresses hosted a page referencing the “Araneida Customer Panel.” The fact that we hadn’t seen any results since March 2024 indicated that the network operators changed their deployment behaviors.
During the course of our research, we realized there was a second threat actor beyond Araneida likely using a cracked version of Acunetix.
The cracked software has nearly 500 members in their Telegram channel at t[.]me/araneida_official.
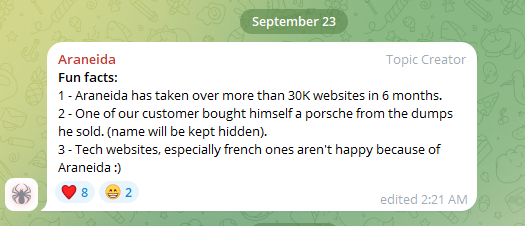
The Telegram channel provides guidance on how to use the tool for malicious purposes and boasts of having “taken over more than 30K websites in 6 months,” with operators using the funds obtained to buy “a Porsche from the dumps he sold,” and claims that “Tech websites, especially french ones aren’t happy because of Araneida :) “
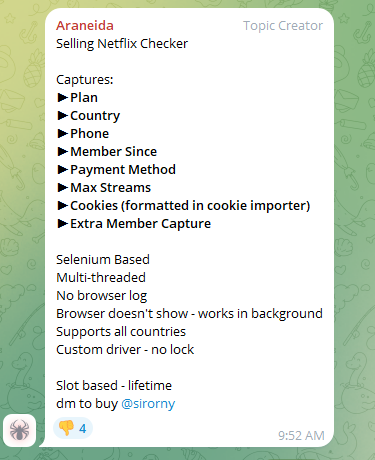
In July 2024, the Telegram channel admins also promoted a Selenium-based “Netflix Checker” tool, which scrapes cookies, payment information, and personal details from Netflix accounts:
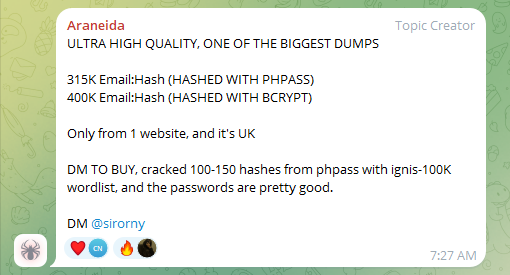
The Telegram channel operators also sell email and password dumps that are likely acquired using their tool, such as the example (below) with hundreds of thousands of login credentials obtained from a UK website:
Continuing our research soon led to the identification of a version of the hosts with the legacy Acunetix SSL, which used Mandarin on their login page.
The first results for this legacy Acunetix SSL on a page with Mandarin language appeared in 2023, and many of the websites are still live, hosting a login portal (as of December 2024):
The page translated into English:
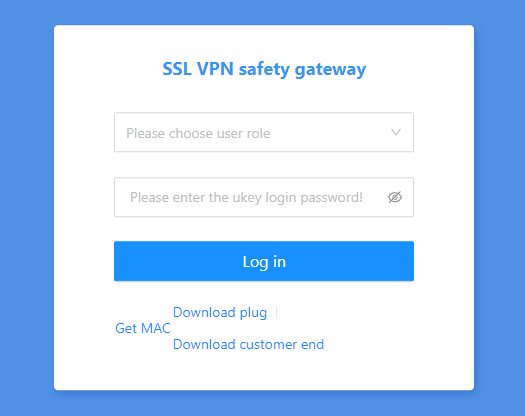
On these login pages, there are two files available for download. One file appears to be a “plugin” labeled “UkeyService_pre” and the other is labeled “Customer End” with a .exe file called “FlkVPN“
These hosts feature a self-signed SSL certificate issued by Acunetix three years ago, which appears to be different from the certificates used on the legitimate Acunetix corporate infrastructure:

Several instances of threat actors misusing Acunetix have been reported since as recently as 2020.
In November 2020, a joint advisory from the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) reported that an Iranian advanced persistent threat (APT) actor was using an Acunetix vulnerability scanner to target U.S. state and election websites to obtain voter registration data.
In March 2024, Lumen reported that the Faceless proxy service had one IP address being used as a relay to communicate with “Moon and/or Faceless C2s” and that it had an Acunetix web vulnerability scanner service running on two ports.
More recently, in May 2024, APT41, the Chinese Cyber threat actors, were highlighted by Natto Thoughts in using Acunetix in their offensive reconnaissance efforts. Natto Thoughts cited a U.S. Department of Health and Human Services Health Sector Cybersecurity Coordination Center (HC3) report, which lists Acunetix as the first “well-known security tool” used by APT41:
“APT41 also uses well-known security tools, such as Acunetix, Nmap, JexBoss, Sqlmap, a customized version of Cobalt Strike, and fofa[.]su, which is roughly a Chinese equivalent of the popular website Shodan.
To conduct reconnaissance, they are known to use the previously-mentioned Acunetix and Nmap, as well as Sqlmap, OneForAll, subdomain3, subDomainsBrute, and Sublist3r. They frequently use spear-phishing as an infection vector, but are also heavily reliant on SQL injections to initially penetrate a target organization.”
The Chinese organizations using a cracked version of Acunetix could be associated with APT41 but we currently have no additional details connecting the efforts.
Silent Push threat researchers will continue to observe and monitor changes to this actor’s infrastructure. New discoveries and TTP changes will be immediately reflected in our feeds.
We’ve also published a TLP: Amber report for Enterprise users that contains links to the specific queries we’ve used to identify and traverse the cracked Acunetix Scanner infrastructure—including proprietary queries and specific analysis that we have omitted from this blog.
Silent Push believes all cracked Acunetix Scanner hosts offer some level of risk.
Our analysts have constructed a Silent Push IOFA Feed that provides a list of Araneida Scanner Indicator of Future Attack domains focused on their scams, along with an IOFA Feed containing suspect Araneida Scanner IP addresses.
Silent Push IOFA Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform featuring a range of advanced offensive and defensive lookups, web content queries, and enriched data types, including Silent Push Web Scanner and Live Scan.
Click here to sign up for a free account.
157.254.237[.]94
163.5.169[.]250
163.5.169[.]45
163.5.210[.]49
163.5.32[.]179
163.5.32[.]202
163.5.32[.]203
163.5.32[.]204
163.5.32[.]72
205.234.181[.]204
23.26.77[.]145
Tokyo, Japan, Dec 17, 2024. Machina Record Co. Ltd., a cyber threat intelligence consultancy, announced its partnership with Silent Push to offer early global threat detection services to its customers to block attacks and reduce the risk of reputational loss.
Threat actors continue to advance their strategies leveraging GenAI to quickly form an attack. Without preemptive cyber defense, companies are exposed and vulnerable to hidden adversary infrastructure. Silent Push provides a complete view of emerging threat infrastructure in real-time, revealing cyber-attackers and malicious intent all within a single platform.
Yusuke Gunji Machina Record CEO, stated, “Silent Push shares in our mission to make the world a safer and more secure society. Together we can enable our customers to stabilize and protect their organization by stopping attackers before they strike. Effective cyber intelligence goes beyond collecting and analyzing large amounts of information from the Internet. The unique approach from Silent Push is delivered with precision and speed to help you stay ahead of adversaries.”
“Too often legacy solutions just rely on Indicators of Compromise (IOC) with limited visibility and missing data. We go beyond IOCs and expose Indicators of Future Attacks through our proprietary behavioral threat modeling; allowing security teams to identify detailed and unique patterns that reveal attacker campaigns before they even start—neutralizing threats and avoiding damage, said Ken Bagnall, Silent Push CEO. We welcome this partnership with Machina Record in Japan to help organizations quickly pinpoint malicious actors and disrupt their plans,” added Ken Bagnall.
Machina Record encourages its customers to experience the power and effectiveness of the Silent Push platform through the free community edition. Learn more here.
Machina Record is a cyber threat intelligence consultancy. Its leading data aggregation platform collects and organizes vast amounts of publicly available data from across the internet, providing organizations with a comprehensive view of individuals, entities, and online activity. Machina Record partners with emerging and innovative partners to provide the most impactful solutions across the globe. For more information, visit www.MachinaRecord.com.
Ready to dive deeper into the world of preemptive threat intelligence? Begin your journey with the Silent Push free Community Edition today.
When it comes to tracking threat actors, Silent Push Threat Analysts understand this process can be complex, and it’s not uncommon for certain organizations to track one threat actor more effectively than others. These types of cases generally occur due to gaps in visibility or a lack of access to certain intelligence.
Conducting a simple process to look up which IP address is hosting a domain and then investigating that IP address for other similar domains, however, is not a complex task. It’s a beginner pivot, something any junior threat analyst can accomplish.
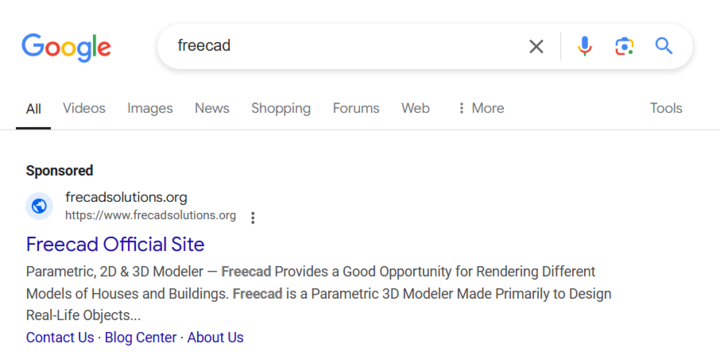
And yet, it appears that the Google advertising team is not even going that far to stop a series of malvertising campaigns that have been going on for nearly a month, targeting graphic design professionals.
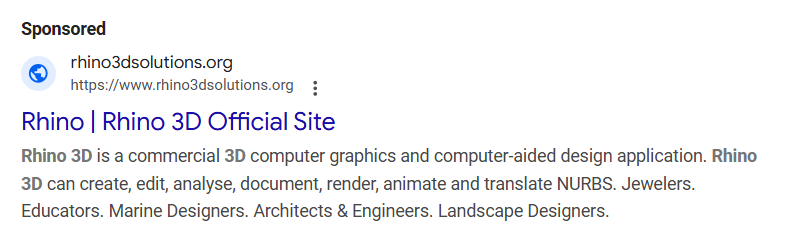
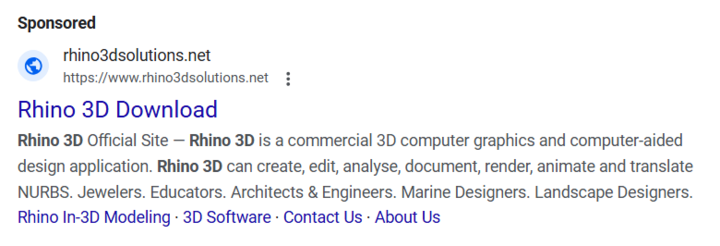
Domains have been launched day after day, week after week, since at least November 13, 2024, for malvertising campaigns hosted on two dedicated IP addresses: 185.11.61[.]243 and 185.147.124[.]110.
Sites stemming from these two IP ranges are being launched in Google Search advertising campaigns, and all lead to a variety of malicious downloads, according to our research partners.
In the last month, Silent Push Threat Analysts have documented at least ten distinct malvertising campaigns, launched via Google ads, that make use of domains mapped to one of these two IP ranges.
Register for our free Community Edition to use all of the tools and queries mentioned in this blog.
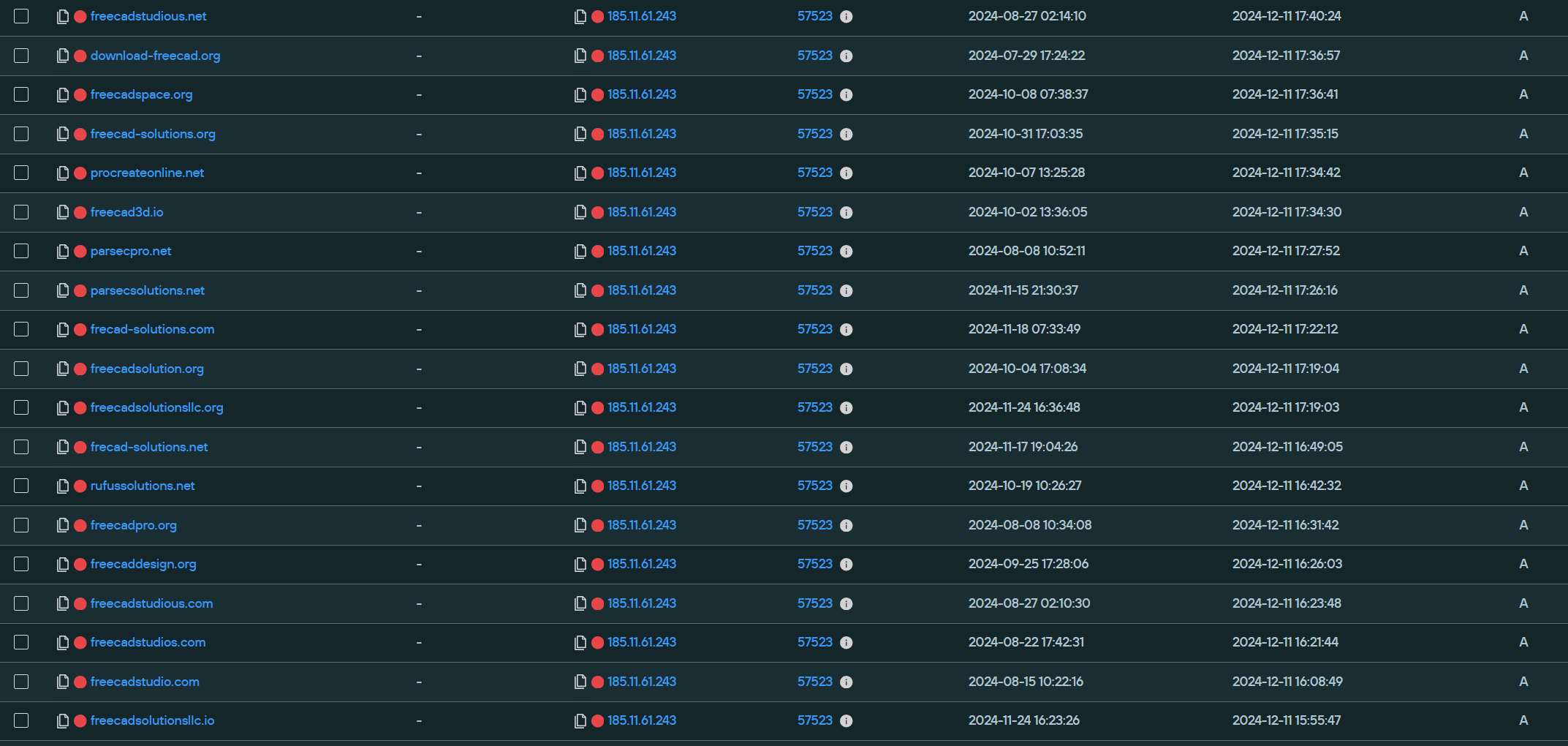
Starting with the first IP address 185.11.61[.]243, at the time of this writing, 109 unique domains were mapped to it, all seemingly for this graphic design/CAD malvertising campaign. The first domains were added on July 29, 2024, and the most recent domains mapped to it were from November 25, 2024:
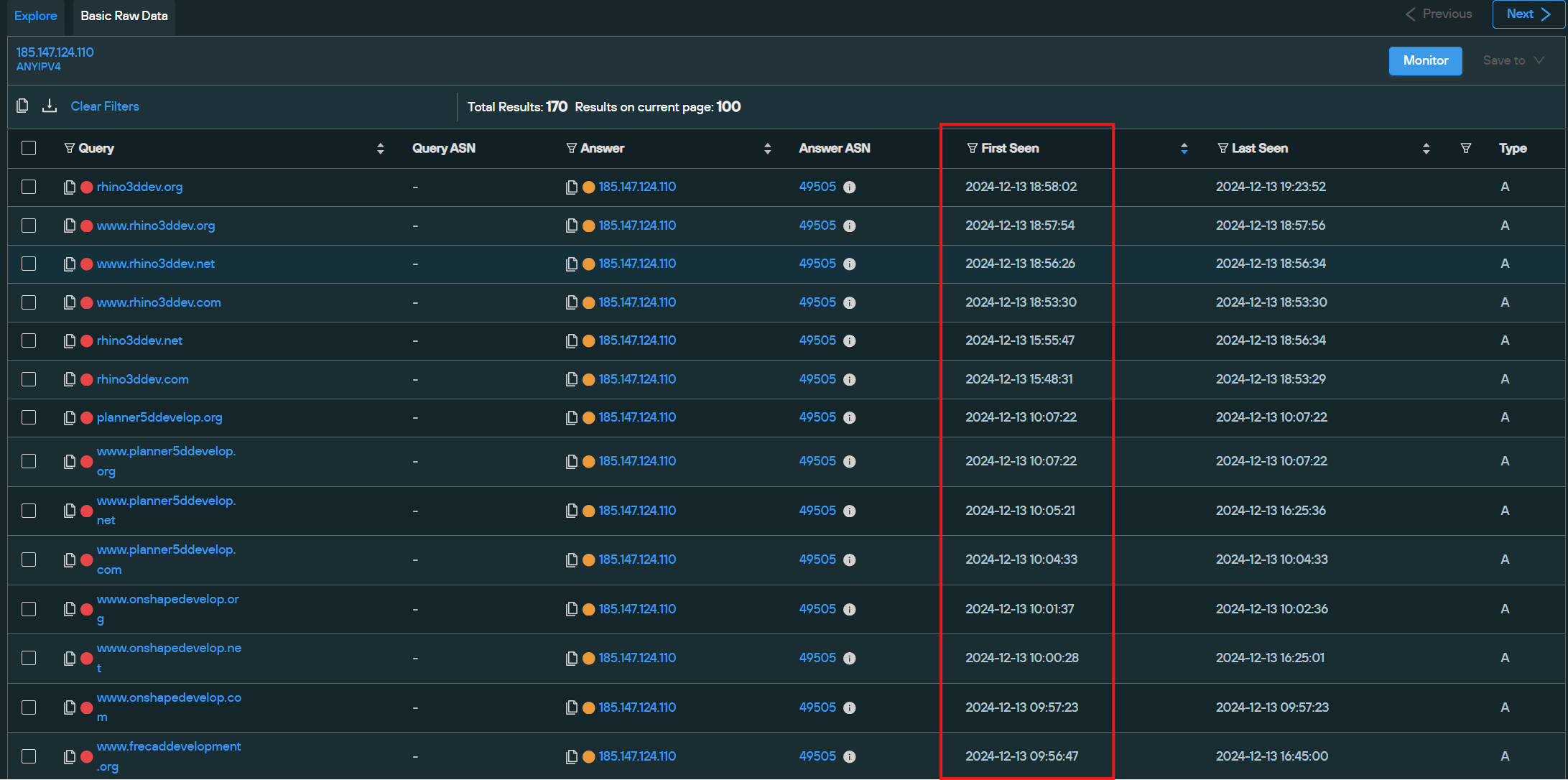
Meanwhile, 185.147.124[.]110 currently has 85 unique domains mapped to it, with the first domains added on November 25, 2024, and the newest domains mapped as recently as December 13, 2024:
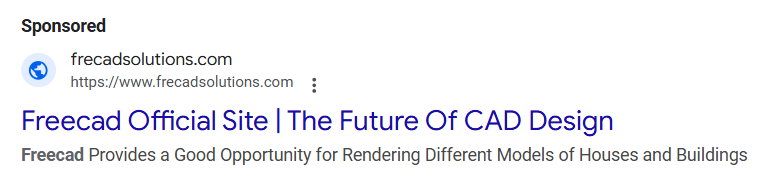
On November 13, 2024, the malvertising campaign first launched with frecadsolutions[.]com, hosted on 185.11.61[.]243 since November 6, 2024. From here, we noticed that the IP address hosted dozens of other similar domains and assumed they could be for similar malvertising purposes.
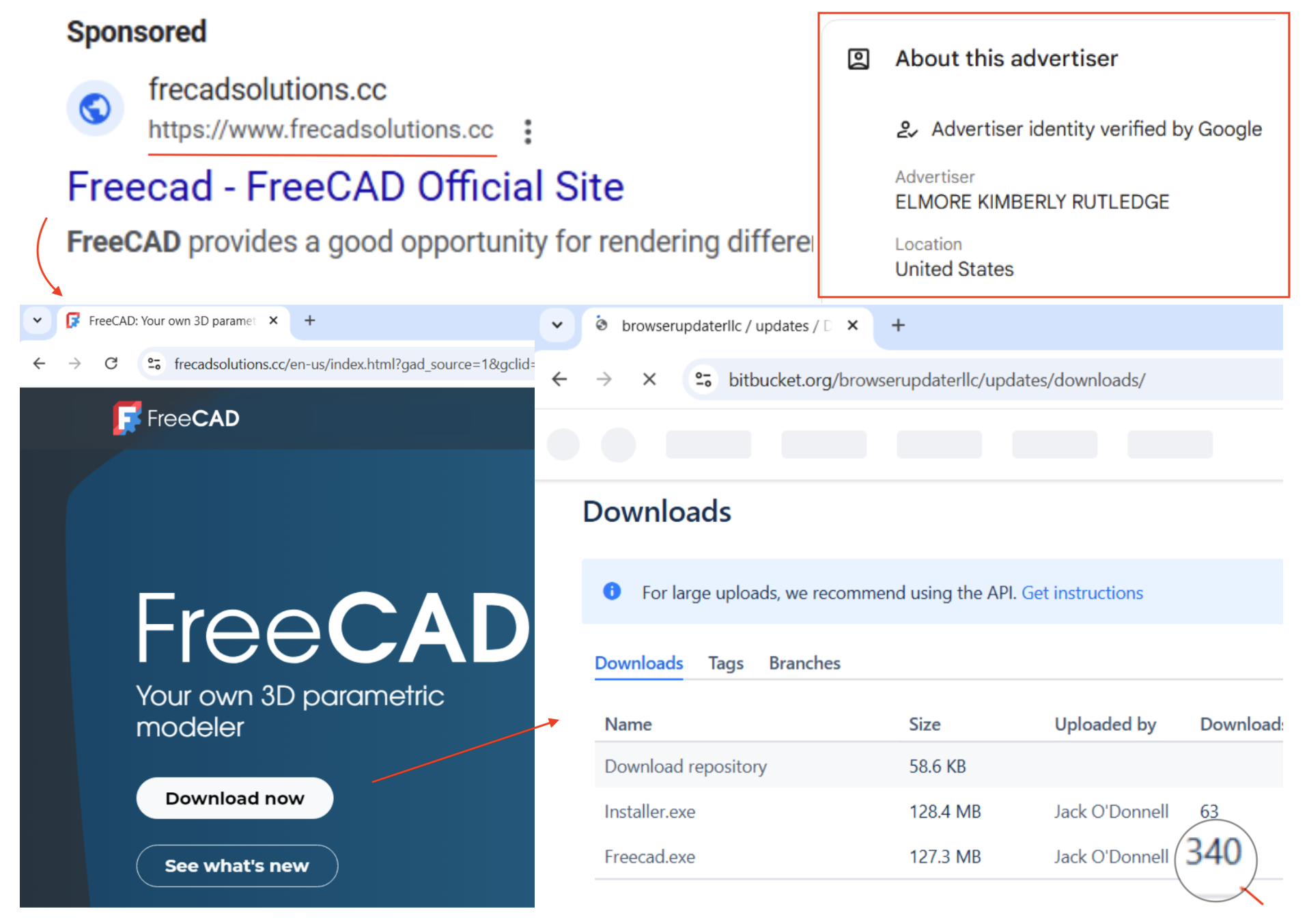
On November 14, 2024, a malvertising campaign was launched using frecadsolutions[.]cc (note the subtle TLD difference of “cc” vs. “com”), which had also been hosted on 185.11.61[.]243 since November 6, 2024. This made use of Bitbucket for its malicious download, which is normally a legitimate file hosting site.
On November 26, 2024, a malvertising campaign was launched on freecad-solutions[.]net, which had been hosted on 185.11.61[.]243 from November 1, 2024 to November 26, 2024, and then moved to 185.147.124[.]110, where it has since remained.

On November 27, 2024, a malvertising campaign was launched on frecadsolutions[.]org, which had been hosted on 185.11.61[.]243 from November 6, 2024 to November 26, 2024, and then moved to 185.147.124[.]110, where it has since remained.
On November 27, 2024, a malvertising campaign was launched with rhino3dsolutions[.]io, which had been hosted on 185.11.61[.]243 from November 17, 2024, to November 26, 2024, and then on 185.147.124[.]110 from November 26, 2024, to present.
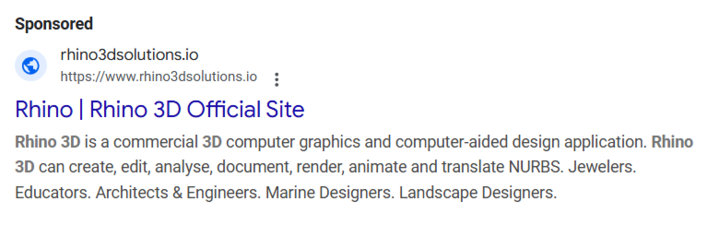
On November 27, 2024, a malvertising campaign was launched with rhino3dsolutions[.]org, which had been hosted on 185.11.61[.]243 from November 18, 2024, to November 26, 2024, and then on 185.147.124[.]110 from November 27, 2024, to present.
On November 27, 2024, a malvertising campaign was launched with rhino3dsolutions[.]net, which had been hosted on 185.11.61[.]243 from November 17, 2024, to November 26, 2024, and then on 185.147.124[.]110 from November 26, 2024 to present.
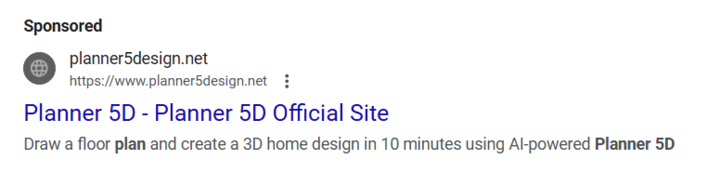
On December 5, 2024, a malvertising campaign was launched with planner5design[.]net, which had been hosted on 185.147.124[.]110 from December 1, 2024 to December 6, 2024.
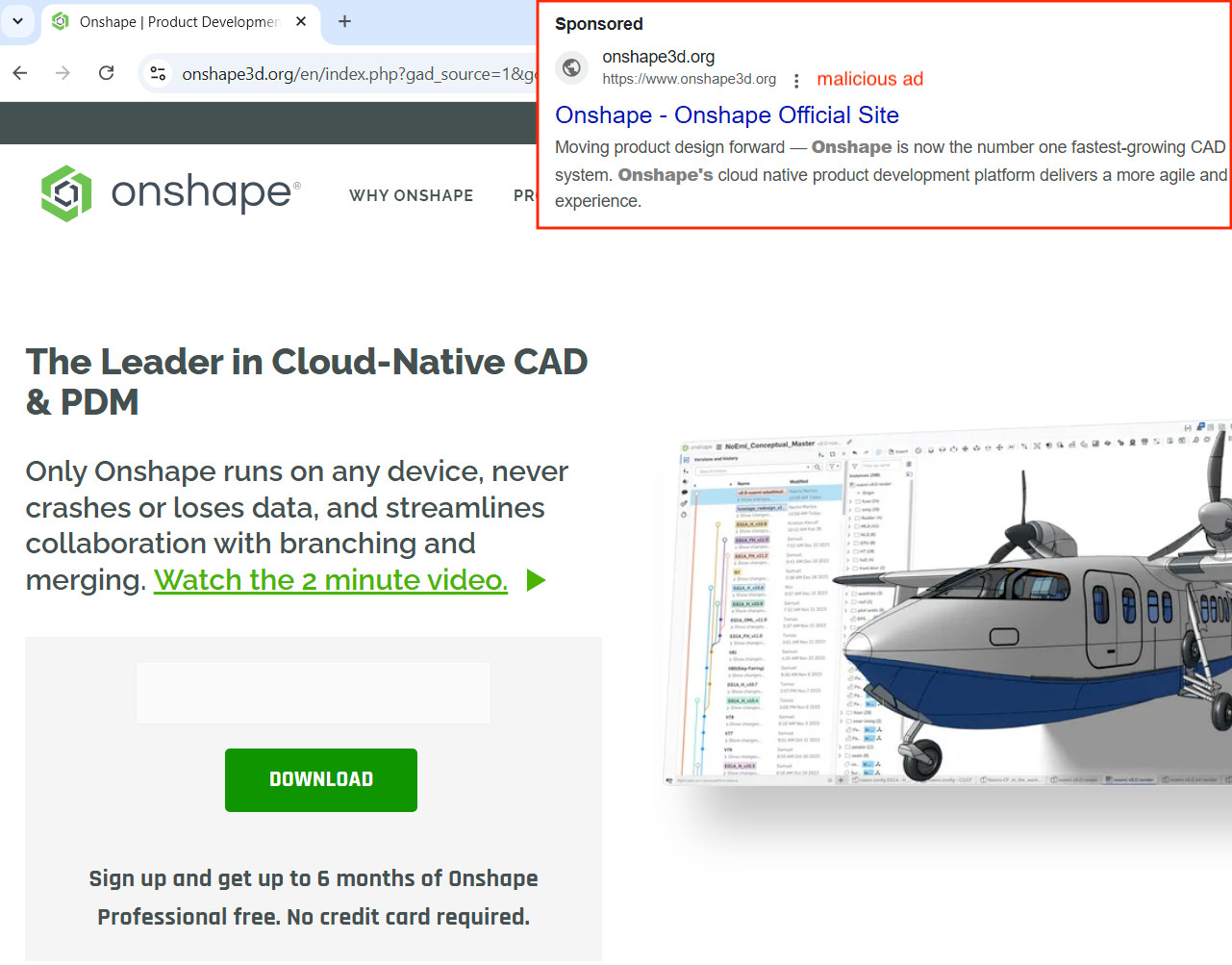
On December 9, 2024, a malvertising campaign was launched with onshape3d[.]org, which had been hosted on 185.147.124[.]110 from December 1, 2024, to present.
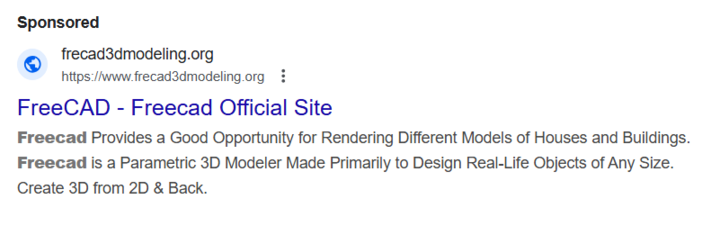
On December 10, 2024, a malvertising campaign was launched with frecad3dmodeling[.]org that had been hosted on 185.147.124[.]110 from December 8, 2024, to present.
Silent Push analysts would like to thank the collaboration with our research partner, Jérôme Segura from Malwarebytes, who initially highlighted these malvertising domains. By partnering together in trusted research-sharing circles, we’re able to find and highlight complex threats such as these – and for those efforts, we salute you.
If you are interested in joining a research-sharing effort or simply have interesting threats to share that you would like our help with, please feel free to reach out to us at info@silentpush[.]com.
Silent Push believes all malvertising domains pose significant risks, especially to corporate environments.
Our analysts have constructed a Silent Push IOFA Feed that provides a list of Indicators of Future Attack domains focused on malvertising, along with an IOFA Feed containing suspect Malvertising IPs.
Silent Push IOFA Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform featuring a range of advanced offensive and defensive lookups, web content queries, and enriched data types, including Silent Push Web Scanner and Live Scan.
Click here to sign up for a free account.
Here is a sample list of IOFAs – our full list is available for enterprise users. Silent Push Enterprise clients have access to a domain and IP feed containing this malvertising infrastructure.