Winning the AI War: Why Preemptive Cyber Defense is the Only Viable Countermeasure for CISOs
The escalation of AI-driven cyber threats has fundamentally broken the traditional security lifecycle. For decades, the industry has operated on a reactive cadence: an attack occurs, indicators are gathered, and defenses are updated. This model assumes that defenders have time to react.
In an era where threat actors leverage Artificial Intelligence (AI) to automate the creation and deployment of malicious infrastructure, that assumption is no longer valid. AI has granted adversaries the ability to operate at machine speed and infinite scale.
To a CISO, the strategic imperative is becoming clearer by the day. You cannot defeat an automated enemy with a reactive defense. The only way to combat AI-driven threats is to adopt a Preemptive Cyber Defense posture that neutralizes infrastructure before the attack is ever launched.
The Asymmetry of AI-Driven Attacks
AI and advanced automation have shifted the balance of power by solving the two biggest constraints for attackers: cost and complexity.
- Infinite disposable Infrastructure: Automation allows threat actors to spin up thousands of unique domains, subdomains, and IPs for a single campaign. These assets are “disposable.” They are used once for phishing or malware delivery and then abandoned immediately.
- Hyper-evasion: AI tools can instantly generate infinite variations of web content and code. This allows attackers to bypass signature-based detection systems by ensuring that no two attacks look exactly the same, even if they originate from the same group.
In this environment, waiting for an alert means you have already lost. The speed at which AI-generated campaigns are deployed and discarded outpaces the speed at which reactive security tools can ingest and distribute Indicators of Compromise (IOCs).
Moving Left of the Launch
To survive this new threat landscape, security strategies must move “left” of the attack launch. This is the core mandate of Preemptive Cyber Defense.
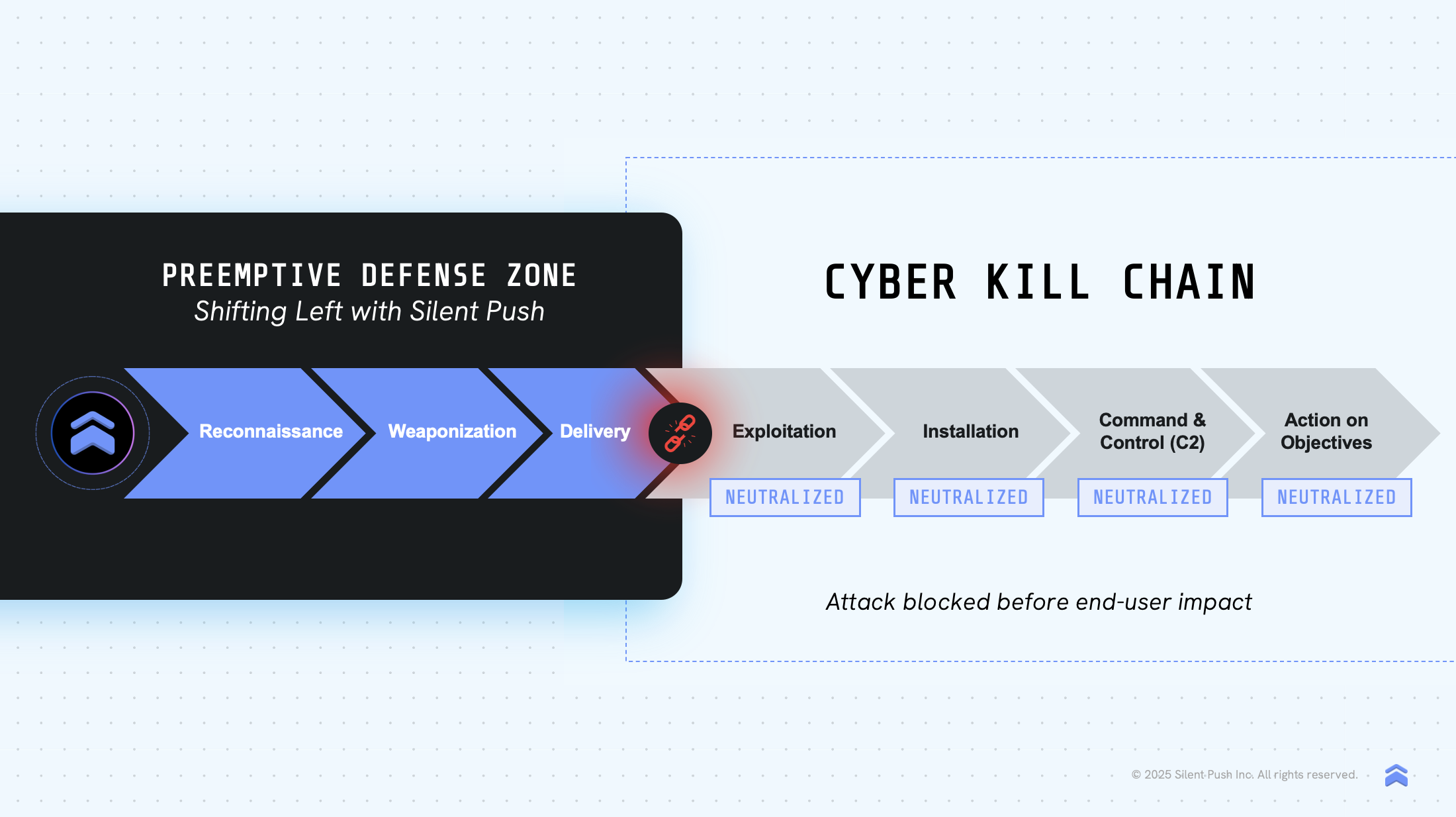
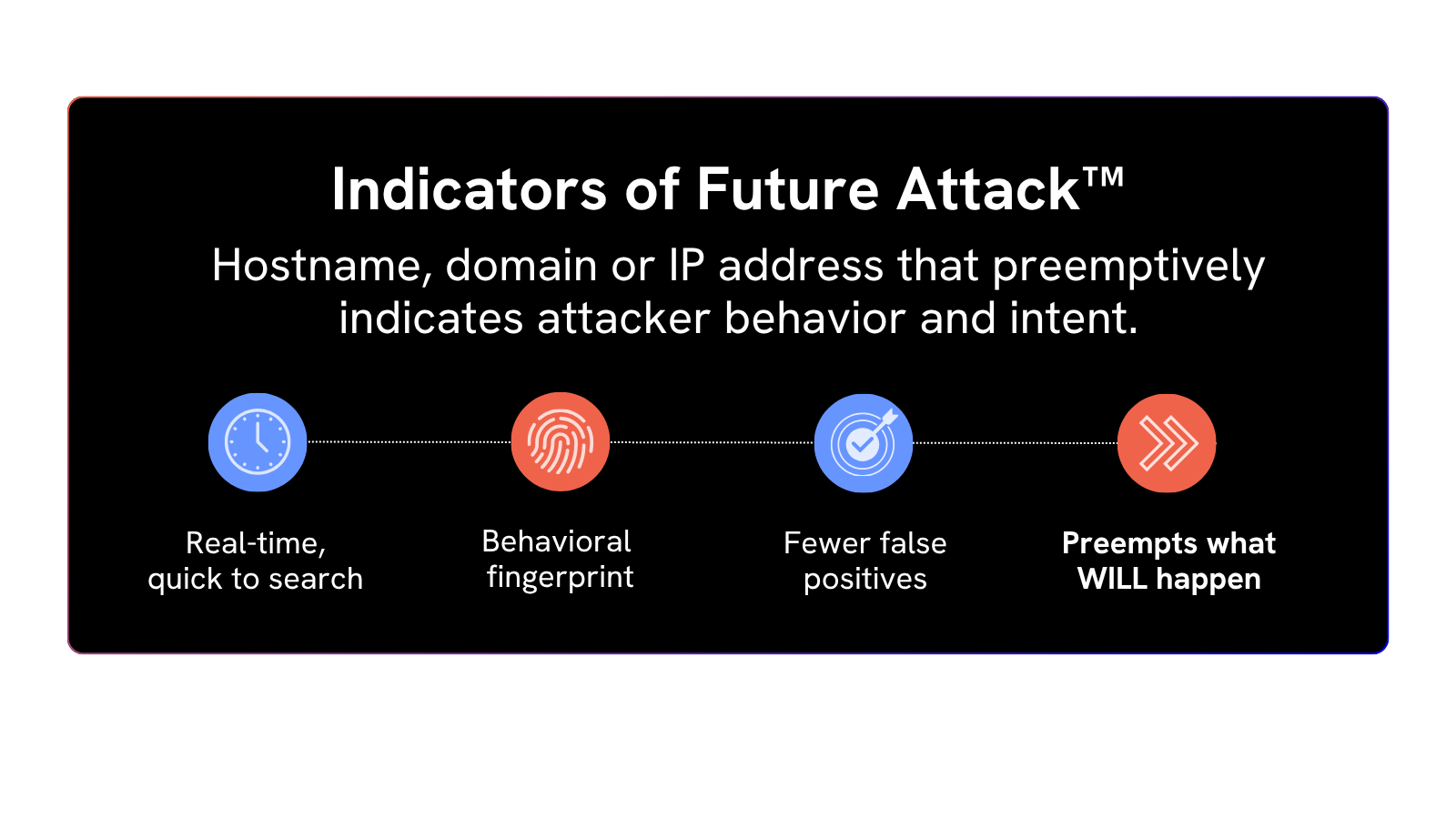
The goal is no longer to detect a payload as it hits the network. The goal is to identify Indicators of Future Attack (IOFA™). These are the traceable digital footprints that adversaries leave behind while they are still staging their infrastructure.
Even AI-driven automation follows rules. While an attacker can change an IP address in milliseconds, they cannot easily hide the Tactics, Techniques, and Procedures (TTPs) they use to procure, configure, and manage their network.
Silent Push: Combatting AI with Contextual Pre-Attack Data
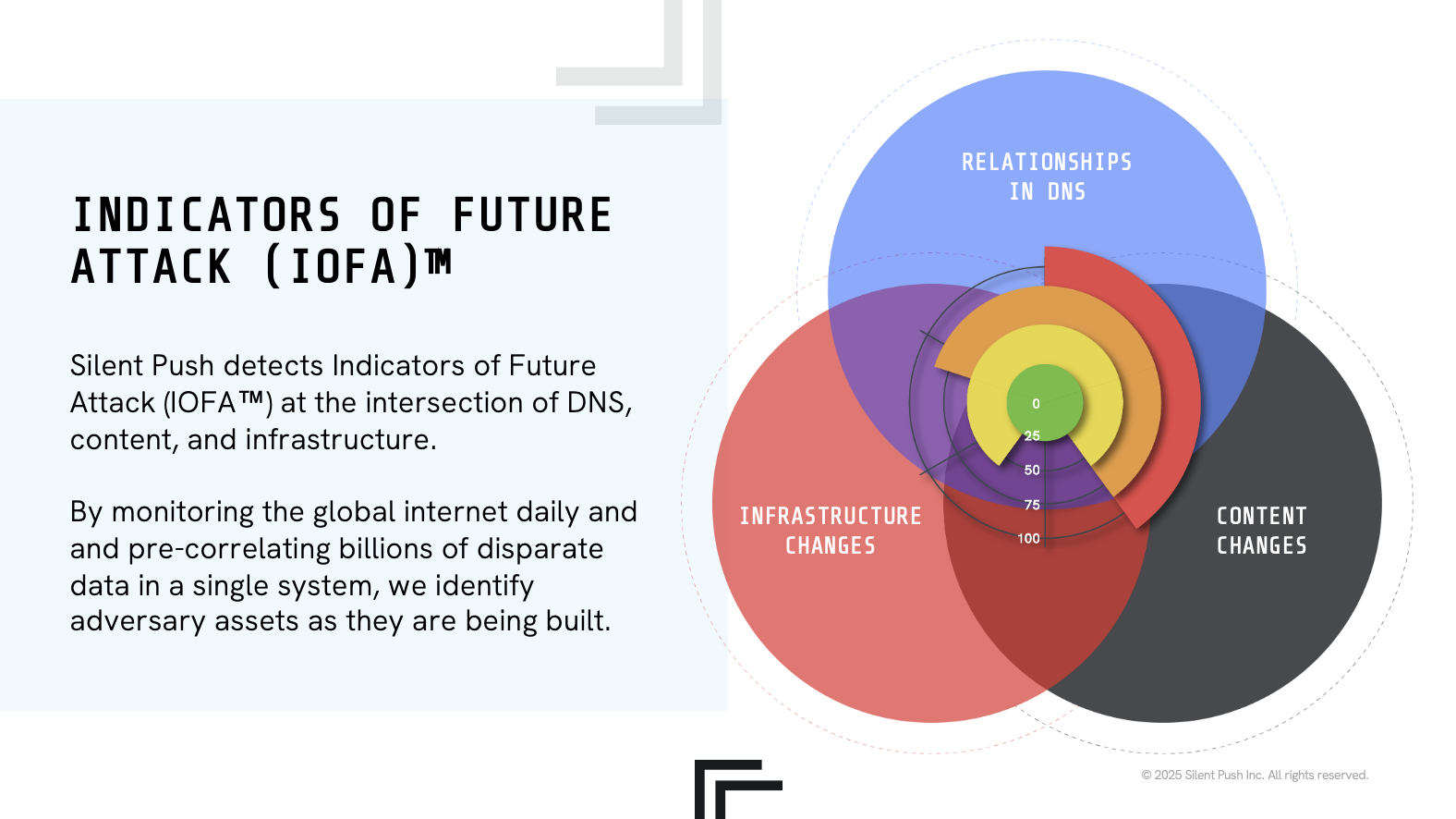
Our platform uses a unified data model that treats the internet like a living, breathing network. By tracking how every piece of data (IPs, domains, hostnames and more) relates to one another, we create a highly contextual map of global infrastructure.
This framework turns billions of raw data points into a definitive opinion, allowing us to see the “DNA” of a threat actor even when they use AI to change their behavior.
This approach counters AI velocity with behavioral precision:
- Mapping the Unknown: Silent Push scans the entire IPv4 and IPv6 space to identify the hidden attacker infrastructure that traditional feeds miss. This reveals the staging grounds where AI-driven campaigns are born.
- Behavioral Fingerprinting: By analyzing over 200 parameters, including DNS records, certificate authorities, and WHOIS patterns, Silent Push creates fingerprints of adversary behavior. This allows the platform to link thousands of seemingly unrelated, AI-generated domains and content back to a specific threat actor.
- Content Similarity Analysis: To defeat AI-generated phishing pages, Silent Push employs fuzzy hashing (ssdeep) and proprietary structural hashing. This allows defenders to identify and block entire clusters of malicious sites based on shared code structures, regardless of how the attacker tries to visually disguise them.
The CISO Advantage: Deterministic Neutralization
Adopting a preemptive approach changes the economic reality for the attacker. By blocking the underlying infrastructure rather than chasing individual IOCs, you disrupt the attacker’s ability to scale.
For the CISO, this shifts the organization from a posture of constant emergency response to one of strategic control.
- Pre-weaponization blocking: High-confidence IOFA™ feeds can be fed directly into firewalls and SIEMs to block connections to malicious infrastructure days or weeks before a campaign goes live.
- Eliminating noise: By filtering out the noise of disposable AI-generated indicators, security teams can focus their resources on verified, high-priority threats.
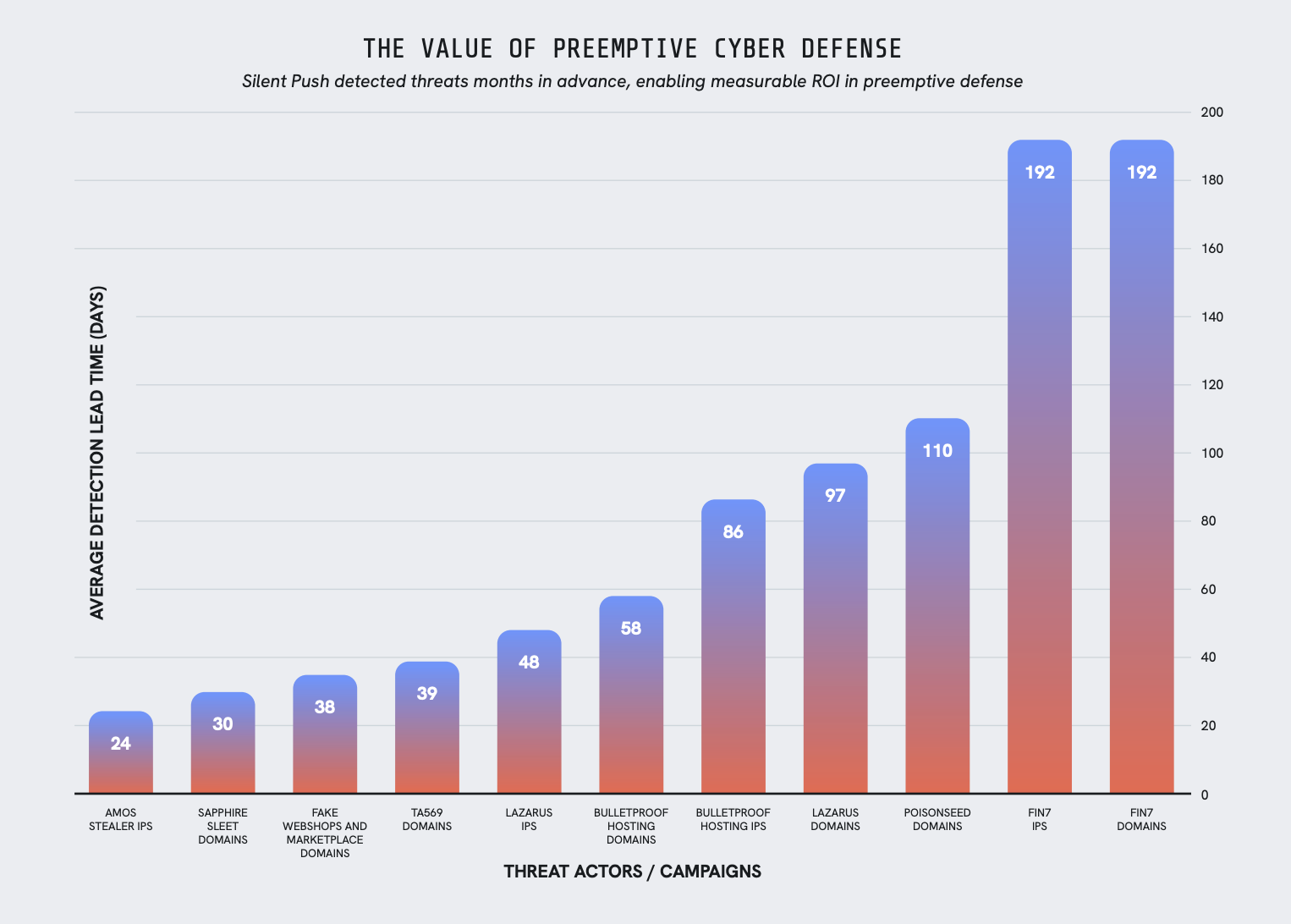
In the era of AI-driven attacks, hesitation is a terminal risk. Traditional defense is mathematically incapable of keeping pace with automated scale. To win, we must move beyond existing security approaches and embrace a truly preemptive posture, neutralizing infrastructure before it is weaponized.
The Economics of Preemption vs. Reaction
Automated attacks create a scale problem that reactive budgets cannot solve. When threats move at machine speed, relying on an IOC-and-respond cycle leads to unpredictable spending and avoidable downtime.
Neutralizing infrastructure before it is weaponized stabilizes the security budget and removes the operational volatility inherent in reactive security models.
| Focus Area | The Cost of Reaction | The ROI of Preemption |
| Budget Control | Linear growth: You pay for every attack via incident response, forensics, and legal fees. | Cost avoidance: Neutralizing infrastructure early stops the billable hours of a breach before they start. |
| Operational Uptime | Recovery mode: Success is measured by how fast you get back online after a hit. | Stability-based: Success is measured by the attacks that never reached your network in the first place. |
| Resource Allocation | SOC burnout: High-tier talent is wasted triaging thousands of automated “noise” alerts. | Strategic focus: Filtering threats at the source allows your team to focus on high-value architecture and strategy. |
Why this matters for the bottom line
In an AI-driven threat landscape, the gap between “compromise” and “encryption” is shrinking to seconds. If you are still relying on a human-led response to an automated probe, the ROI will always be negative.
Traditional defense manages the damage; preemptive defense manages the risk. Shifting to a preemptive posture ensures that your security budget is spent on maintaining growth rather than chasing ghosts.