The Invisible Insider: Why AML and KYC Compliance Fail Against Digital Deception

North Korean operatives and professional money launderers have been drawing six-figure salaries from Fortune Global 500 companies by exploiting a fundamental flaw in identity verification.
The Silent Push preemptive cyber defense team has found domestic U.S. IP addresses being used by North Koreans, likely as part of their efforts to appear as suitable candidates for jobs with major U.S. corporations.
Traditional KYC (Know Your Company) and AML (Anti Money Laundering) protocols rely on static document validation. These processes fail when an adversary presents a legitimate, stolen identity that is backed by a clean residential IP address.
When organizations cannot distinguish between a local user and a Keyboard-Video-Mouse (KVM)-over-IP relay, their payroll systems become vulnerable to funding sanctioned entities.
Traditional tools only see the local address used to hide a connection. Traffic Origin unmasks the hidden upstream infrastructure used to spoof locations, identifying if a connection actually starts in a high-risk or sanctioned country instead of just the domestic IP where it ends.
The Obfuscation Gap: Why Traditional Tools Fail
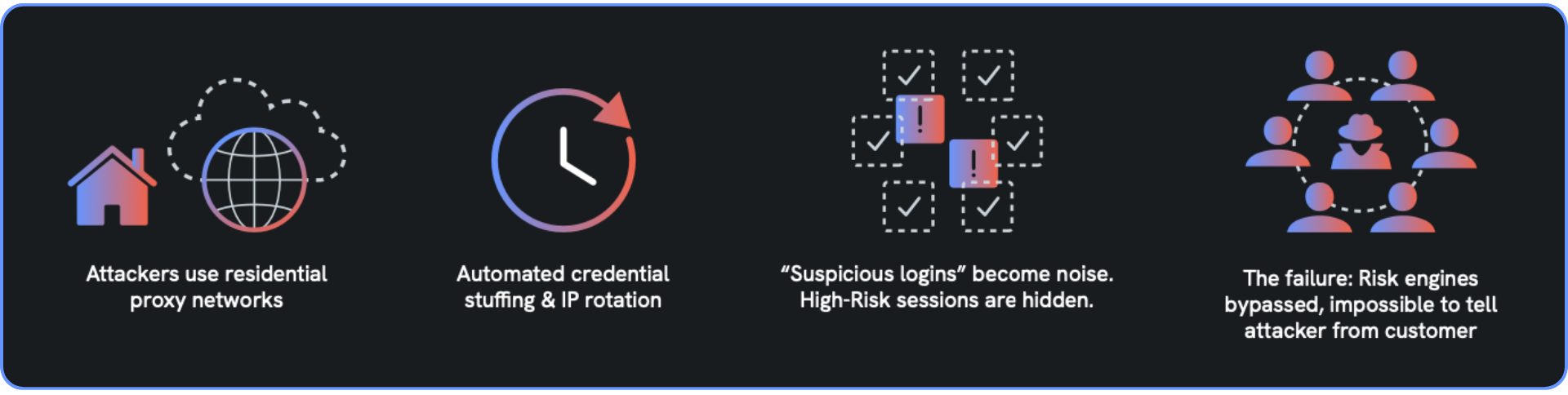
Traditional security tools too often rely on historical databases to flag known malicious actors. This reactive approach fails against modern adversaries who constantly rotate infrastructure.
According to recent Department of Justice (DOJ) enforcement actions, thousands of highly skilled cyber operatives have deployed into the global digital workforce using fraudulent identities. Standard security stacks are particularly vulnerable to the tactics they use, including:
- Residential Proxy-as-a-Service (RPaaS): Fraudsters and sanctioned actors use residential proxies to appear as legitimate domestic customers. This allows them to bypass geo-fencing and pass initial KYC checks undetected.
- Laptop Farms and KVM Switches: Adversaries host physical hardware in a domestic residence and access it remotely via KVM-over-IP hardware.
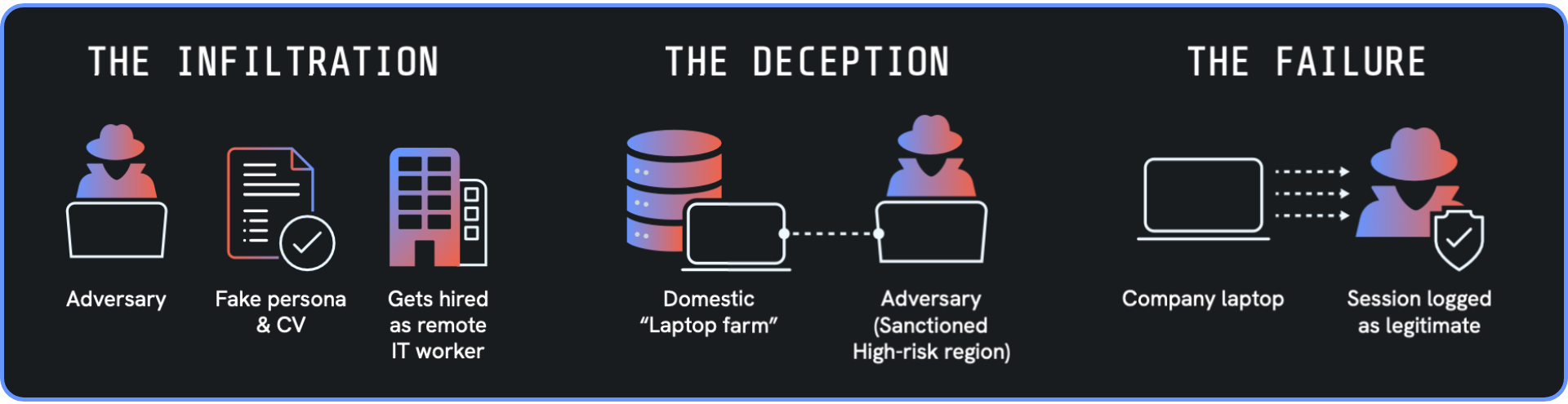
The FBI issued specific guidance on how these schemes use domestic hardware to thwart standard detection. Because the software runs on a legitimate local machine, security tools see a domestic ISP and a local MAC address.
Beyond the “Last Mile” Geolocation
Traditional identity systems are easily deceived because they only see the exit node or the “last hop.” If the IP address says “London,” an alert is dismissed. This can create a catastrophic blind spot, allowing illicit funds to be washed through banks that cannot see a transaction’s true geographic origin.
The result is a massive money laundering engine. Illicit revenue is systematically moved through shell companies and Electronic Money Institutions (EMIs) to evade international sanctions or cash out from high-risk crypto mixers.
The UK’s Office of Financial Sanctions Implementation (OFSI) has highlighted several indicators of this activity, including upstream connection mismatches where domestic IPs show active links to high-risk jurisdictions.
The KYC & AML Checklist: Spotting the Digital Invisible Insider
While identity thieves and state actors work hard to blend in, their technical infrastructure leaves distinct fingerprints. Monitoring for the following “High Risk” indicators creates opportunities for defenders to disrupt these threat actors:
| Red Flag | Technical Indicator | Risk Profile |
| Geographic mismatch | Domestic IP with an active upstream connection to a sanctioned or high-risk zone. | High (sanctions evasion) |
| Infrastructure Density | Numerous unrelated devices (High Host Diversity) appear to originate from a single residential IP. | Medium/high (proxy usage) |
| Interview & meeting friction | Persistent refusal to appear on camera, unusual audio lags, or background environments inconsistent with claimed locations. | High (identity spoofing) |
| Employment anomaly | A “highly skilled” employee who fails to complete basic tasks, refuses 1:1 video syncs, or delegates work to “partners.” | High (work outsourcing, potentially DPRK) |
| Financial redirection | Urgent requests to pivot salary payments to an EMI or third-party account shortly after onboarding. | High (money laundering) |
Traffic Origin: True-Origin Determination
To solve this dilemma, organizations must move beyond document checks to verify the technical origin of a connection. Silent Push Traffic Origin addresses this visibility gap by providing the highest-confidence attribution indicator available today.
We extend this visibility through true-origin determination. This capability provides targeted, high-confidence attribution, revealing the true geographic origin for identified high-risk infrastructure even when masked by VPNs or residential proxies. While traditional tools only see the final residential hop, Traffic Origin identifies a true upstream source.
Through deep, multidimensional analysis, the Traffic Origin platform evaluates host diversity, subnet reputation, and behavioral density to provide technical clarity.
Verification in the Age of Invisible Insiders
Trust is a liability in an era where an adversary can rent a domestic identity and a clean residential IP for a few dollars. Accurate compliance requires more than just checking a passport. It requires verifying the physical and technical reality of the connection.
Traffic Origin can protect your organization by providing the visibility required to ensure your KYC, AML, and fraud workflows are grounded in technical truth rather than digital deception.
Without the ability to unmask upstream inception points, your security posture remains reactive and incomplete. You lose the critical window to block professional fraudsters and “Invisible Insiders” before they bypass your existing gatekeepers.
Evaluate your network visibility today with Traffic Origin and IP Context to move toward a preemptive posture grounded in technical truth.
Connect with our team to see how Silent Push preemptive cyber defense can protect your organization.

