- Company
Silent Push Inc. ©2025
Our research team has discovered an active phishing campaign targeting players of the multi-player video game Counter-Strike 2. Along with attempts to compromise players’ Steam accounts, part of the campaign’s attack tactics also includes abusing the names of a professional eSports team called Navi.
Built around the creation of seemingly convincing fake browser pop-up windows that prominently display the URL of the real website, the campaign’s goal is to make a visitor feel safe, believing the pop-up windows are part of the actual (real) sites. Once the potential victim tries to log into the fake Steam portal, the threat actor steals the credentials and likely attempts to take over the account for later resale.
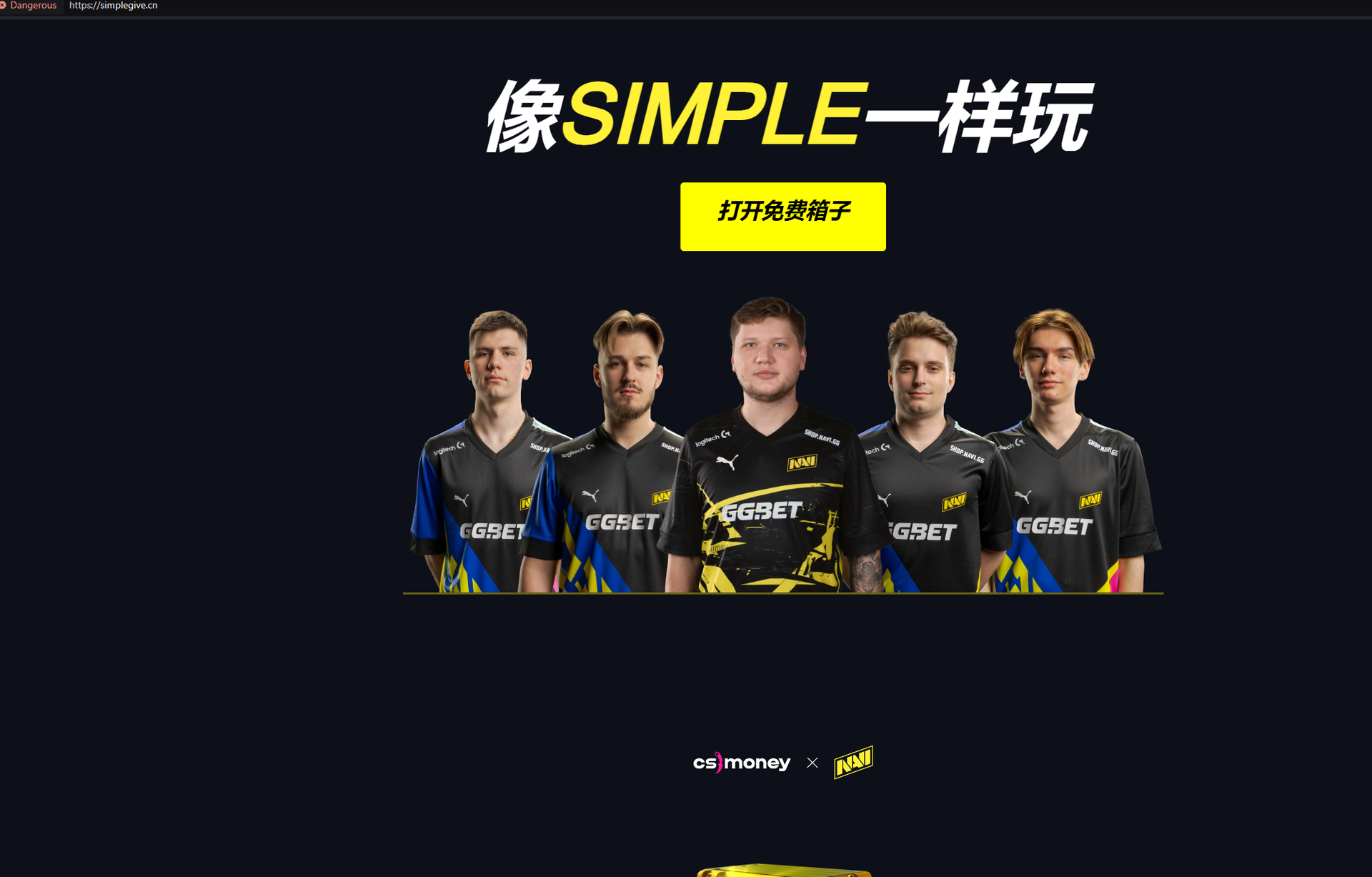
All of the websites our team has found so far were in English save one Chinese site, simplegive[.]cn, which was created in Mandarin, with some English wording, and used the top-level domain (TLD) “.cn”
We want to use the discovery of this threat against gamers as an opportunity to introduce our readers to the free Silent Push Community Edition to get started with threat detection, protection, and prevention.
Register now for our free Community Edition to use all of the tools and queries highlighted in this blog.
Browser-in-the-browser attacks are simple but clever phishing techniques. Threat actors emulate trusted services with fake pop-up windows that resemble the actual login pages. While many theoretical attacks describe browser-in-the-browser tactics, it’s rare to actually catch a threat actor deploying this process.
The new phishing campaign our team discovered targets Counter-Strike 2, a free-to-play tactical first-person shooter game developed and published by Valve. Designed as counter-terrorists-versus-terrorists play, Counter-Strike 2 was released in September 2023 for Windows and Linux on the Steam digital distribution service and storefront. Also developed by Valve, Steam is the largest digital distribution platform for PC games, and public reports estimate it to have 75% of the market share.
From our team’s research thus far, it appears these threat actors created phishing kits targeting Steam, Counter-Strike 2, and the Navi esports team after conducting research into gaming communities.
The threat actor behind the new phishing campaign singled out the professional eSports team Navi to “feature” in its attacks. The screenshot below shows the threat actor’s phishing web page offering a “free case” – essentially video game skins as a lure:
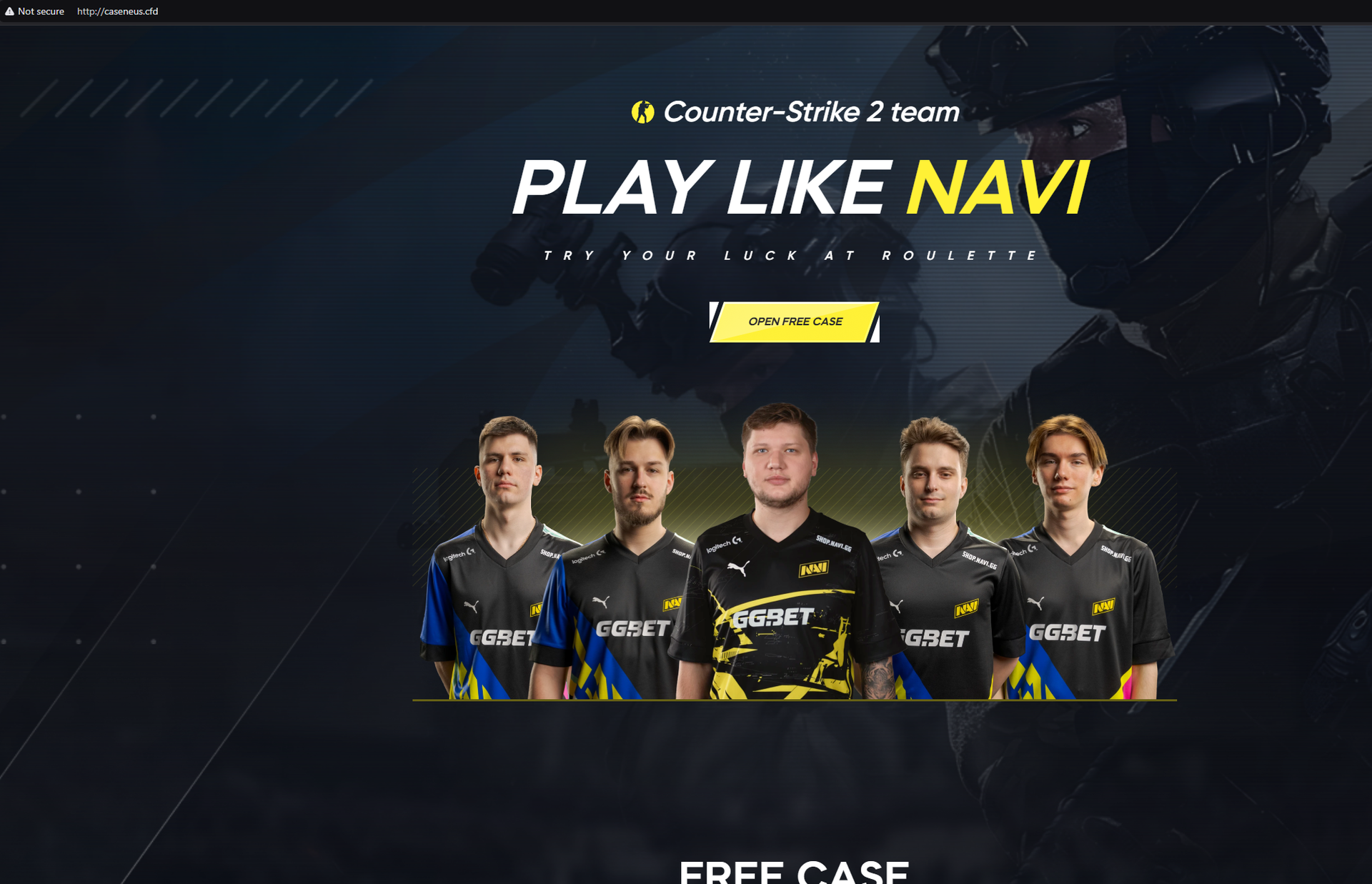
caseneus[.]cfd
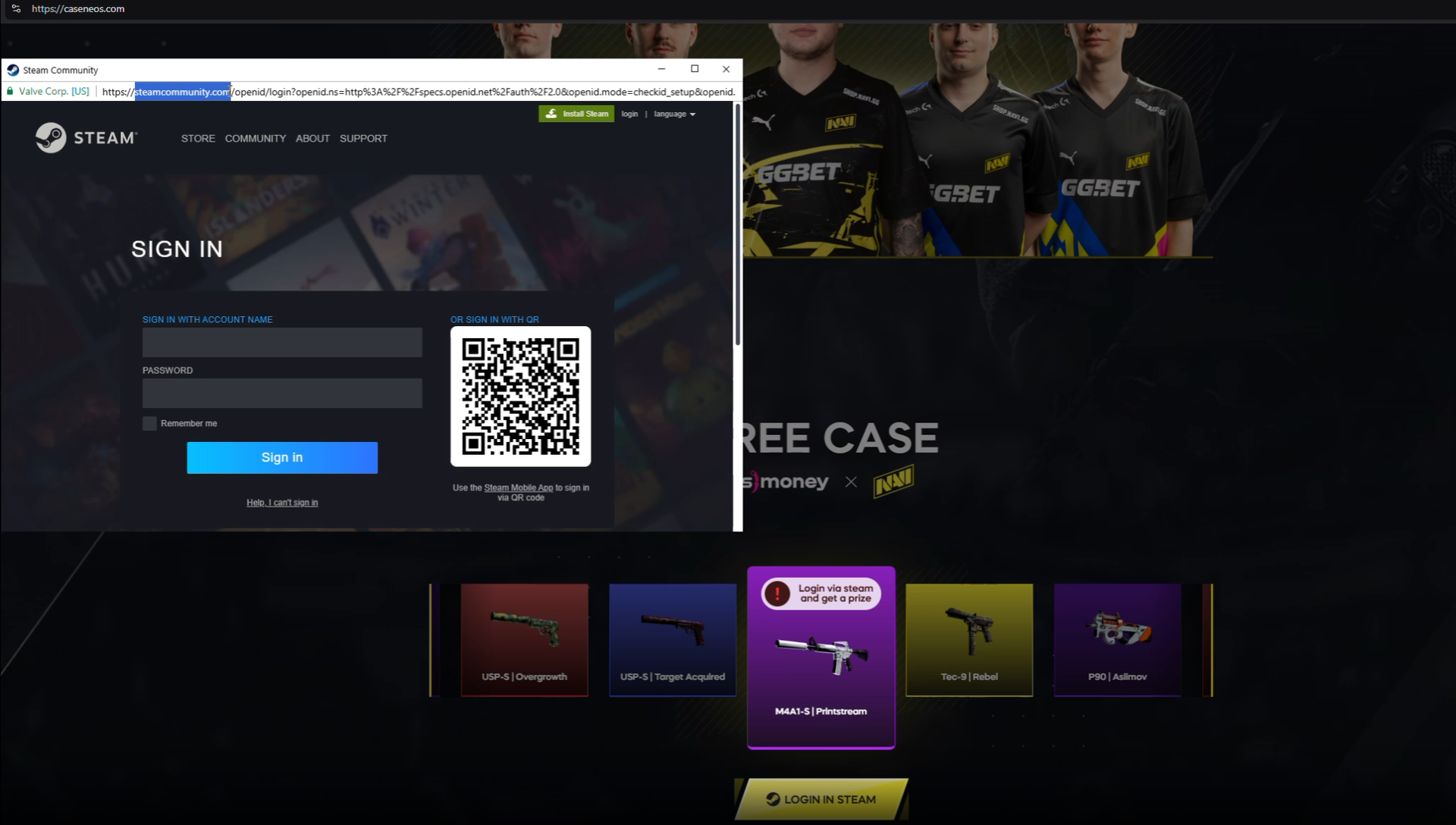
As referenced previously, our threat team was particularly interested in this phishing effort (watch the video below to larne more) because the threat actor is using a “Browser in the Browser” orchestrated attack. In the attack, the URL of the real site (in this case, Steam) is prominently displayed, leading someone to believe it’s a real pop-up window for logging in.
That window looks like this:
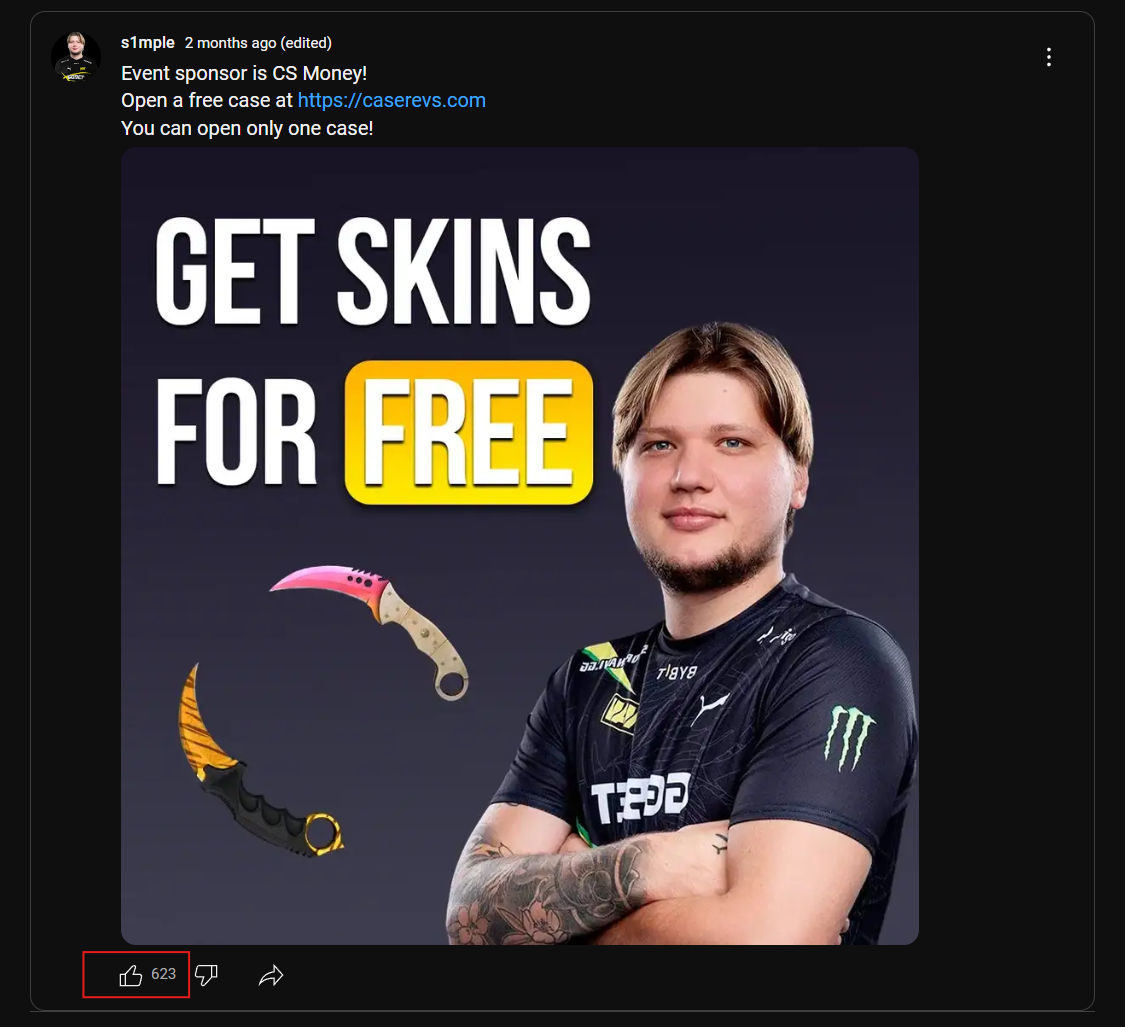
The threat actor behind this is also trying to spread their phishing scheme on YouTube. Posts like the one highlighted below from January 2025 got over 600 likes on YouTube (a potentially purchased level of engagement) – in promoting their scam domain: caserevs[.]com.
Various threat actors have launched browser-in-the-browser attacks sporadically over the last few years. However, it’s still interesting to see when these BitB attacks are found, as they indicate a threat actor who carefully studies complex phishing methods.
Potential victims who experience these phishing attacks in the wild receive a much more convincing lure than a suspicious login form on a random domain, potentially making them more effective.
These types of attacks were heavily studied a few years ago, with researchers like mrd0x largely initiating the discussion with their open-source example and larger write-up.
In June 2024, a credible BitB campaign was launched targeting Steam users from the pages[.]dev domain first reported on Reddit. The pages[.]dev domain is a Cloudflare product for hosting content, and anyone can create content there, making it a common location our threat team has seen for threat actors spinning up malicious infrastructure. Silent Push enterprise clients have access to a feed of domains with publicly rentable subdomains, and we encourage defenders to alert or block requests to these domains.
Our team believes new BitB phishing attacks will continue targeting Steam users throughout 2025. As the attacks continue, other networks and brands will likely be included as new targets.
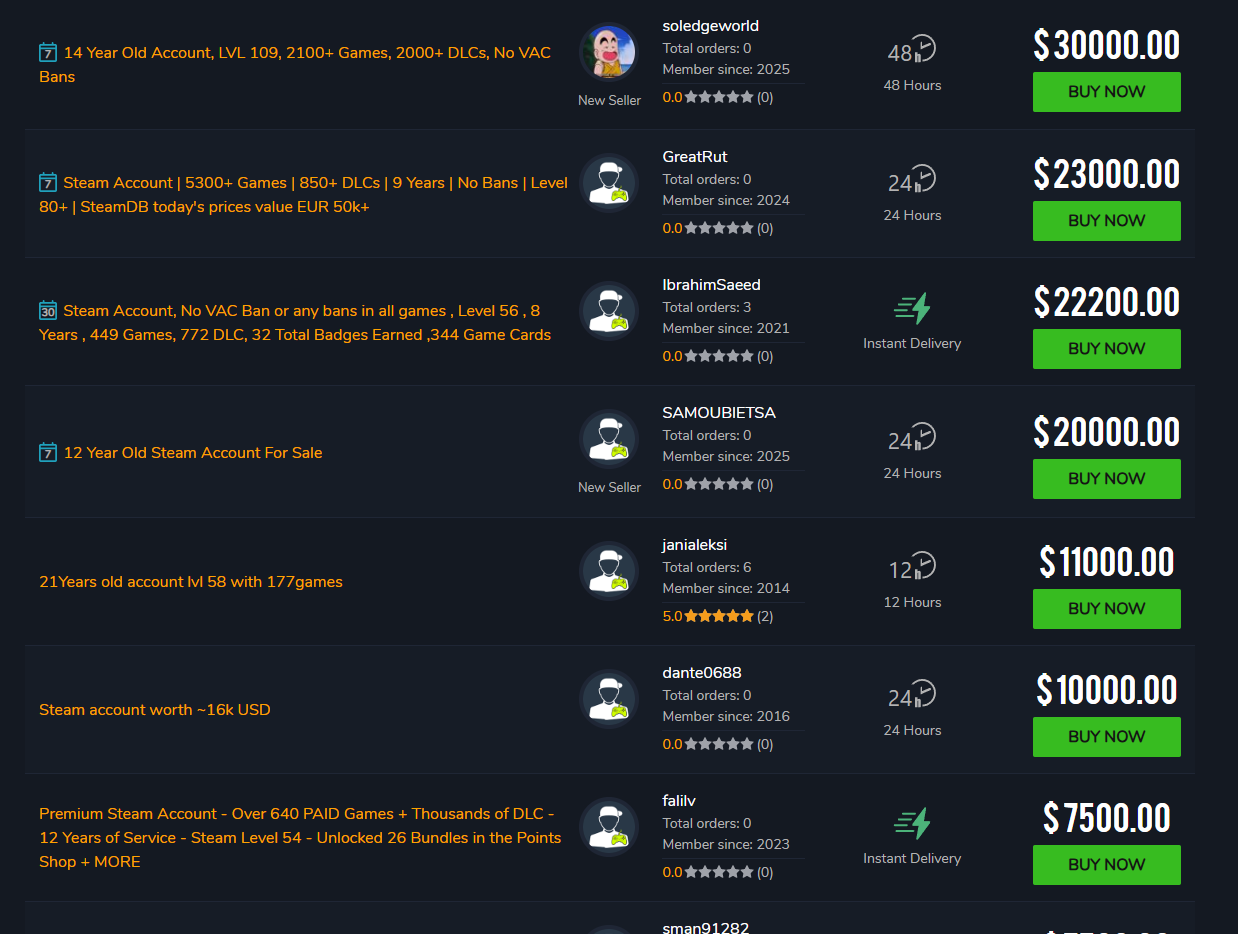
It might initially seem odd for a threat actor to target Steam accounts. However, when they contain a substantial number of games, these accounts can sell for tens of thousands of dollars. Our research team found many websites, such as playerauctions[.]com, that sell Steam accounts. Threat actors may simply be trying to sell their illicitly acquired Steam accounts on potentially lucrative sites like these.
The screenshot below, playerauctions[.]com/steam-account/?SortField=highest-price, shows the price range of Steam accounts listed for sale.
BitB attacks are most convincing against desktop users, as the pop-ups are built to be viewed on larger resolutions. The threat actors behind this current video game phishing BitB effort didn’t bother to create convincing mobile-optimized phishing pages, which indicates the targeting here follows that pattern.
Legitimate windows, including pop-ups, can be maximized, minimized, and moved outside the browser window. However, fake pop-ups, such as the login windows in the BitB phishing scheme, cannot be maximized, minimized, or moved outside the browser window even though victims can “interact” with the URL bar of the fake pop-up.
Our team encourages people to look for fake URL bars in any login pop-ups. If you see a URL bar, always try to drag that window outside the browser you’re viewing. This is the best way to easily confirm that the pop-up is real, and therefore, the URL bar would correctly display the URL of the pop-up. Otherwise, you could be experiencing a fake pop-up window related to a potential BitB attack.
If you happen to get phished by a BitB attack, we recommend immediately changing the credentials associated with the relevant account as well as taking note of any other details the threat actors may have scraped for use from that account.
Cybercriminals are always inventing new methods to steal users’ credentials, inject malware, and generally cause cyber mayhem. The good news is that Silent Push specializes in preemptive threat intelligence to prevent that.
Individuals interested in using our platform to protect themselves or their organization can sign up for a free Silent Push Community Edition account.
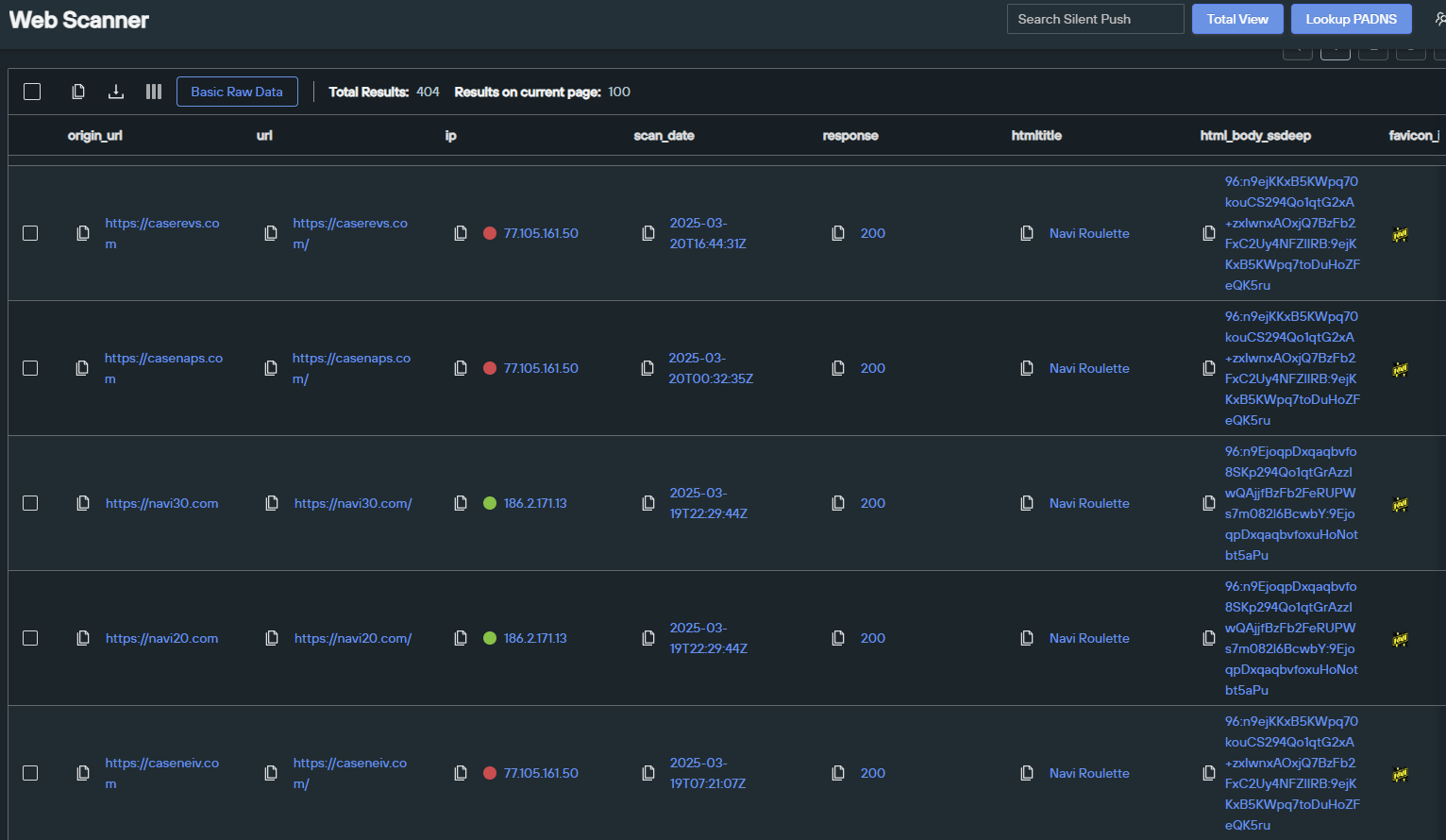
The Silent Push Web Scanner is one of our most popular and easy-to-use tools. We’ll be using that for several of the queries below. But first, a look at our Total View insights!
The BitB phishing campaign uses a dedicated IP address to host their scams.
Silent Push Total View Dedicated IP Link
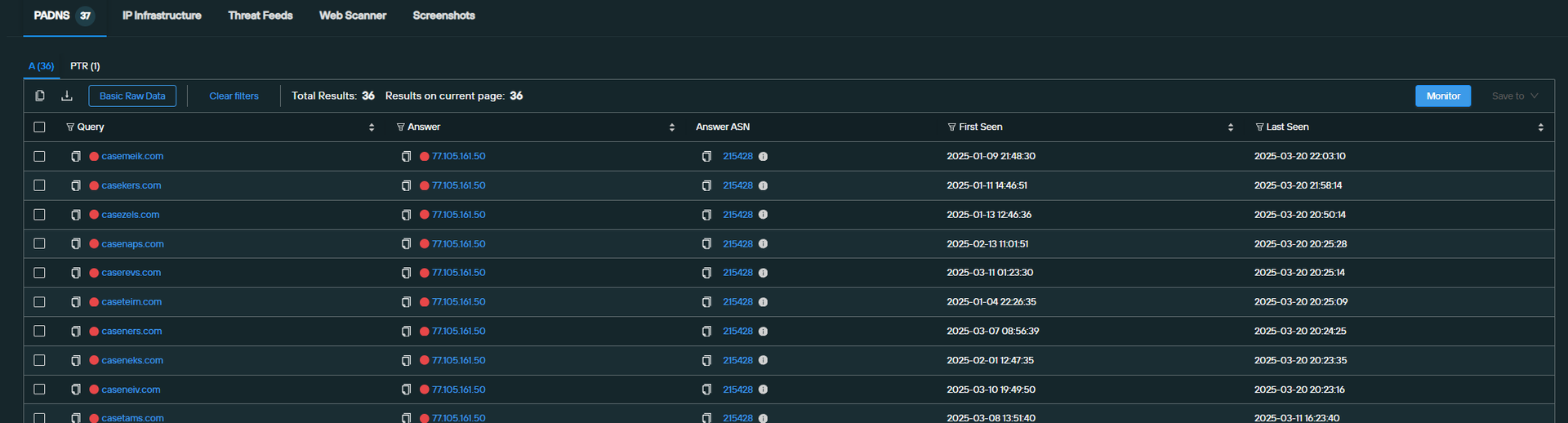
The threat actor also reuses a simple template across each of these sites, which includes reused JavaScript. We can look for this JavaScript by searching against our “body_analysis.SHV” field in the Web Scanner, which excels in pinpointing groups of perfect matches.
Here’s the SHV query for tracking this BitB campaign:
Silent Push Web Scanner body_analysis.SHV search query link
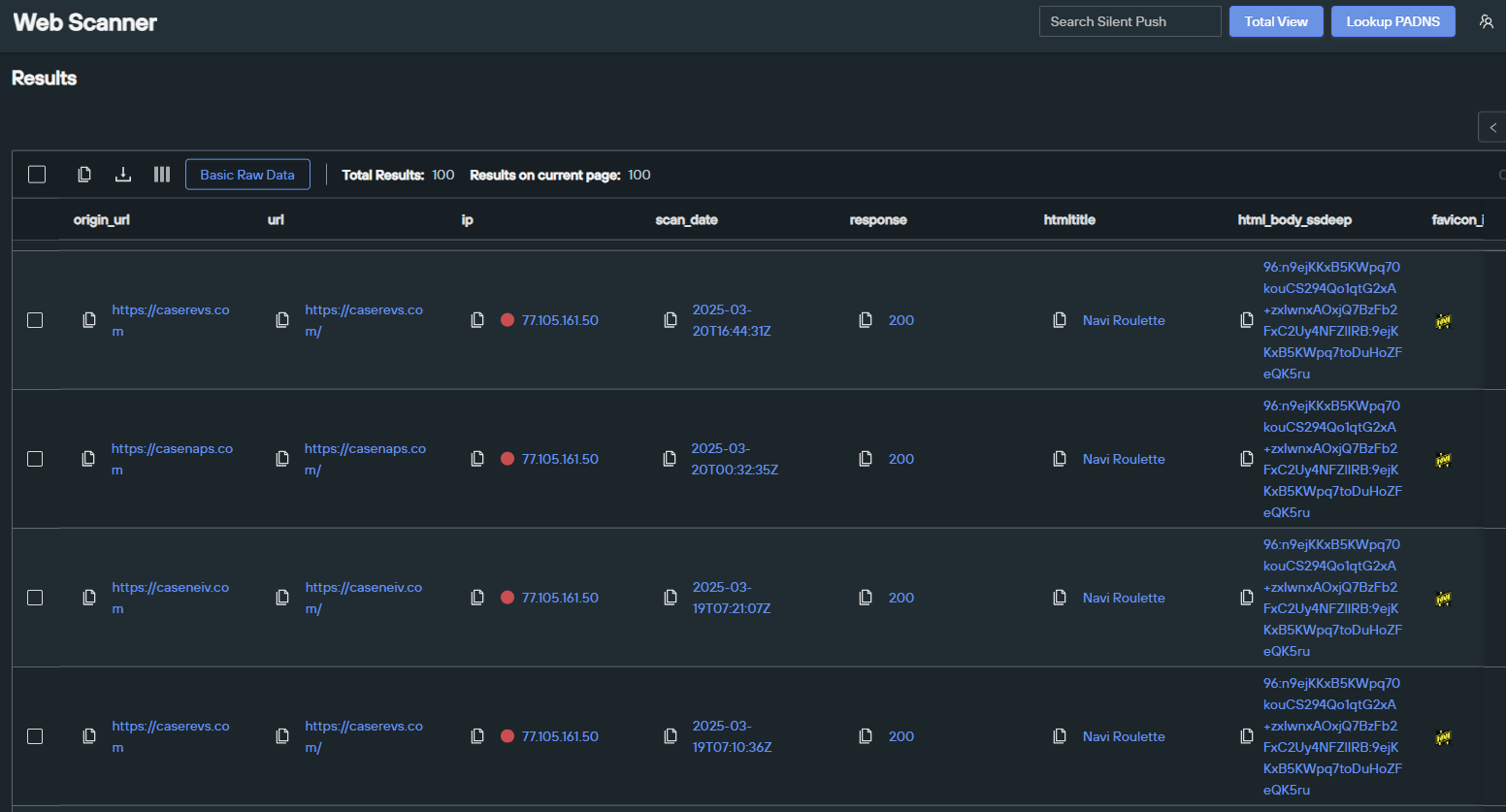
The threat actor also happens to be reusing an HTML title across all of their sites—something we can easily search against in the Web Scanner. Here’s that query:
Silent Push Web Scanner HTML Title = “Navi Roulette” search query link
Our team continues to track numerous types of phishing campaigns. As we identify new developments, we will report our findings to the security community.
We will also continue to share our research on threats we discover with law enforcement. If you have any tips about threat actors engaging in criminal activities, our team would love to hear from you.
Silent Push believes all domains associated with BitB phishing campaigns represent some level of risk.
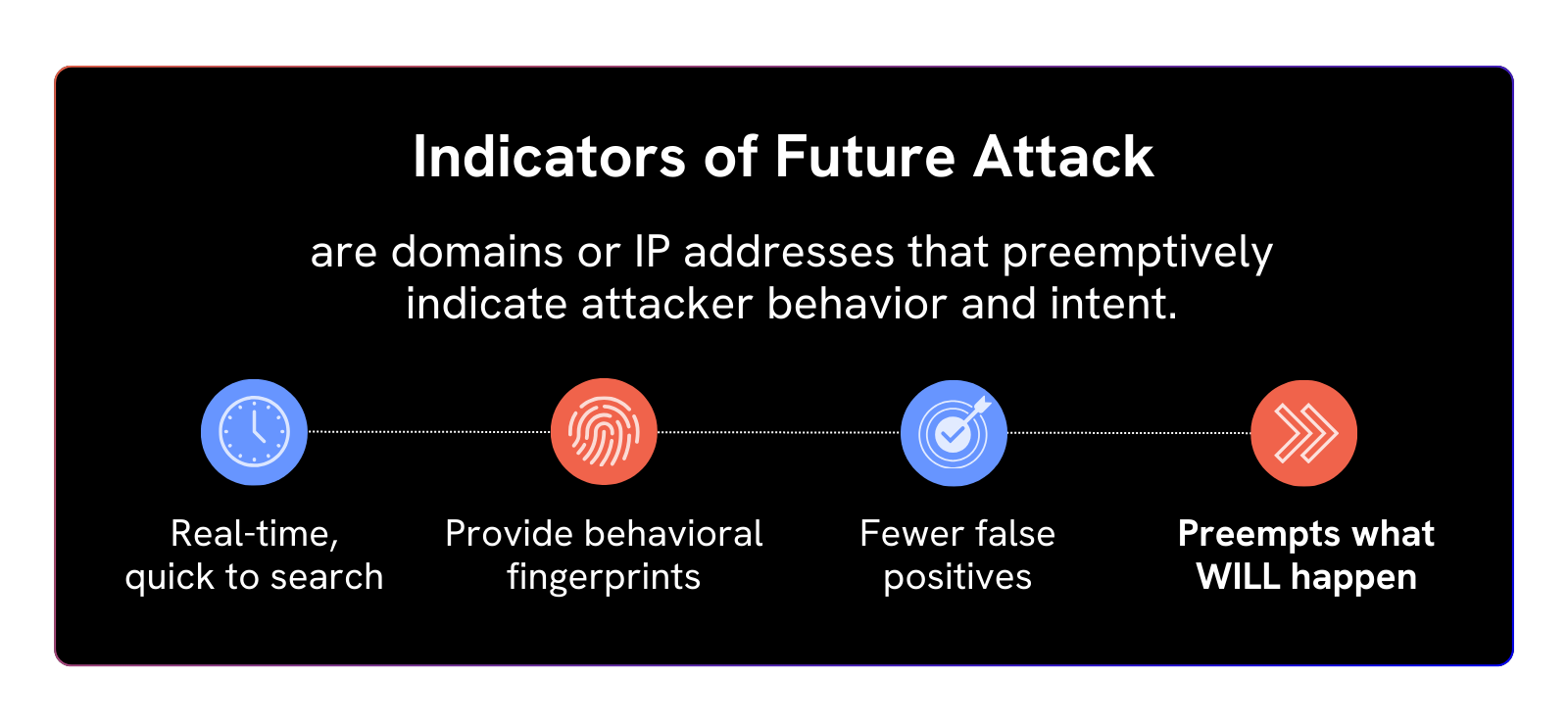
Our analysts have constructed a series of Silent Push IOFA™ Feeds that provide a growing list of Indicators of Future Attacks focused on these types of phishing efforts.
Silent Push Indicator of Future Attack™ (IOFA™) Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA™ Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform that offers advanced offensive and defensive lookups, web content queries, and enriched data types.
Silent Push is sharing a sample list of the IOFA™ we have associated with the BitB phishing campaign to support ongoing efforts within the community. Our enterprise users have access to an IOFA™ feed currently containing many times this number, with more being added in real time as our investigation continues.
Despite the arrest of seven members in 2024, Scattered Spider remains active – join our webinar to explore their evolution, current operations, and key topics including cluster analysis, live Q&A, unmasking the group, legacy tactics, phishing kit evolution, deep dives into their latest techniques, and how we build Indicators of Future Attack (IOFAs) to preempt these threats.
Who should attend:
Anyone looking for actionable strategies to proactively identify and counter threats
Ready to dive deeper into the world of preemptive threat intelligence? Begin your journey with the Silent Push free Community Edition today.
Faced with an ever-evolving threat landscape that demands time and resources to understand and overcome, security leaders across a range of industries and sectors are on the constant look-out for new solutions to the age-old problem of how to stop breaches. Enter stage right Preemptive Cyber Defense (PCD): a relatively new cybersecurity strategy that seeks to proactively stop attacks and potential threats as they emerge – rather than after they’ve been launched – and improve overall security performance.
This blog references a recent Gartner report entitled ‘Emerging Tech: Adoption Trends in Preemptive Cyber Defense’.1
In the report, Gartner perform a deep dive into how organizations view the growing field of Preemptive Cyber Defense, the value of this new approach, and what to expect in the near term.
Current projections indicate a substantial increase in the adoption rate of Preemptive Cyber Defense solutions from 5% to 35% by 2028, as organizations attempt to “leverage proactive mechanisms of defense, predictive intelligence or attack anticipation, instead of focusing on detection and response”.2
To download the full report, click here.
We’ve recently explored the concept of preemptive threat intelligence by explaining how little of global threat infrastructure is known at any one time, and how Silent Push helps organizations to reveal it using Indicators of Future Attack (IOFAs)™.
The data used in preemptive threat intelligence provides teams with the ability to proactively respond to threats and reveal known and hidden attacker infrastructure, using a Preemptive Cyber Defense-led approach.
Let’s look at some of the primary outcomes of a well-executed Preemptive Cyber Defense strategy that incorporates preemptive threat intelligence, and how Silent Push can help you to achieve them.
Gartner cite quick, reliable threat identification and mitigation as a prime concern for businesses with a range of risk profiles and regulatory obligations.
Sectors such as Finance and Healthcare are considered high value targets by threat actors due to the sheer volume of highly sensitive data being processed, and how lucrative that data becomes in the event of a breach.3
Both of these sectors lead the PCD adoption curve, and derive a huge amount of value from operating with a cybersecurity strategy that doesn’t sit around and wait for an attack to occur before mitigating any damage, but instead proactively identifies vulnerabilities and new ransomware-based attack vectors so that data is protected around the clock, and the chances of a breach are kept to a minimum.4
Government and Technology organizations however, according to Gartner, have considerable “room for improvement” when it comes to proactive threat detection.5
We believe that Silent Push can help security teams execute a PCD-led approach to cyber defense, in any industry, to assist in meeting operational priorities.
In our opinion, no other vendor knows more about the distribution of global threat infrastructure than Silent Push, and no other vendor is capable of tracking the large amount of domains and IPs that usually go unnoticed during an attack, before they’re used against you, so that you stay one step ahead of the bad guys and know precisely where the next attack could be coming from.
The Gartner report highlights a persistent “lack of visibility” within modern cyber defenses that do not provide full coverage of an attack, and gives adversaries more time to probe for weaknesses, especially in hidden corners of an external attack surface.6
Once this “critical challenge” is overcome by utilizing preemptive intelligence data that maps out both internal and external datapoints in full, organizations increase their ability to detect threats quicker than a traditional IOC-led approach allows, and can take steps to block attacks at source before they cause a problem.7
Silent Push helps security teams clear the fog and break through the visibility barrier, by providing a complete view of any given threat landscape and attack surface, that provides a huge amount of insight into where the next attack could be coming from.
We achieve this by giving teams the ability to input an unknown indicator and gain an immediate appraisal of how a domain or IP address related to the rest of the internet, including how it’s hosted, what other infrastructure it’s similar to, how it’s moved across the global IP space over time, and – crucially – how to respond.
According to Gartner, Preemptive Cyber Defense strategies allow teams to build “efficient operations that ensure security teams can focus on high-priority tasks, reducing the time and effort spent on routine or redundant activities” by utilizing predictive technology, detection techniques to instantly verify threat datapoints, and do away with endless pivots that may or may not end up with reliable intelligence on any given domain or IP.
In the shift towards Preemptive Cyber Defense, organizations are benefitting from an approach that rapidly identifies threats and minimizes the potential damage caused by cyberattacks. Security teams that adopt this new approach are realizing significant improvements in the speed and effectiveness of cybersecurity workflows, including integrations.
At Silent Push, increased operational efficiency is at the forefront of what we provide to our customers. Our IOFA™ datasets give security teams all the context they need to quickly identify and understand unknown indicators, allowing them to make informed, timely decisions in high-pressure situations where every second counts.
Whether you’re in Finance, Government, Healthcare, Retail, or any other industry that considers cybersecurity an important business function, Preemptive Cyber Defense is here to stay.7
The Gartner report concludes that “Enhancing SecOps efficiency is crucial for these industries’ ability to quickly adapt to evolving threats, streamline incident response, processes and reduce the mean time to detect (MTTD) and respond to security incidents”.
Silent Push is a preemptive cybersecurity vendor that provides Indicators of Future Attack™ (IOFA)™ – domain and IP datapoints that tell teams where an attack is coming from, as well as where it’s been – that form the basis of a well-executed Preemptive Cyber Defense strategy.
Our IOFA™ are at the forefront of the Preemptive Cyber Defense revolution, providing insight into the vast amount of threat infrastructure that currently goes undetected by a traditional approach to cyber defense.
Contact us here to learn more about how we can help you adopt a Preemptive Cyber Defense strategy.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
At a recent conference, our team was approached by a multi-national media organization to help them investigate a threat campaign spoofing the Okta Identity and Access Management (IAM) platform, via subdomains.
Each online service the organization provides, across all the apex domains it uses, requires multiple subdomains to operate – everything from a customer or employee portal, to integrations with third-party technology, and retail services.
The organization’s security team needed to ensure that they had all bases covered by understanding how exposed they were – including the many thousands of subdomains they use – so that they could deal with any vulnerabilities, and minimize the chances of a breach.
No other vendor has a better view of Internet-facing infrastructure than us, powered by a proprietary DNS and web content scanning and aggregation engine that leaves no stone unturned in the hunt for vulnerable infrastructure or attack points.
To get at this data, Silent Push features a range of queries that allow you to quickly and accurately map out your organization’s presence online, including timestamped results of all associated subdomains.
One of these tools – “Discover ShadowIT” – returns a comprehensive list of third-party services set up in an organization’s name, that have the potential to be exploited.
To reveal the full extent of the Okta attack, we executed a ShadowIT query using the apex domain, and received a list of 20,000+ subdomains the organization was using to facilitate third-party services, and the IP addresses they were mapped to.
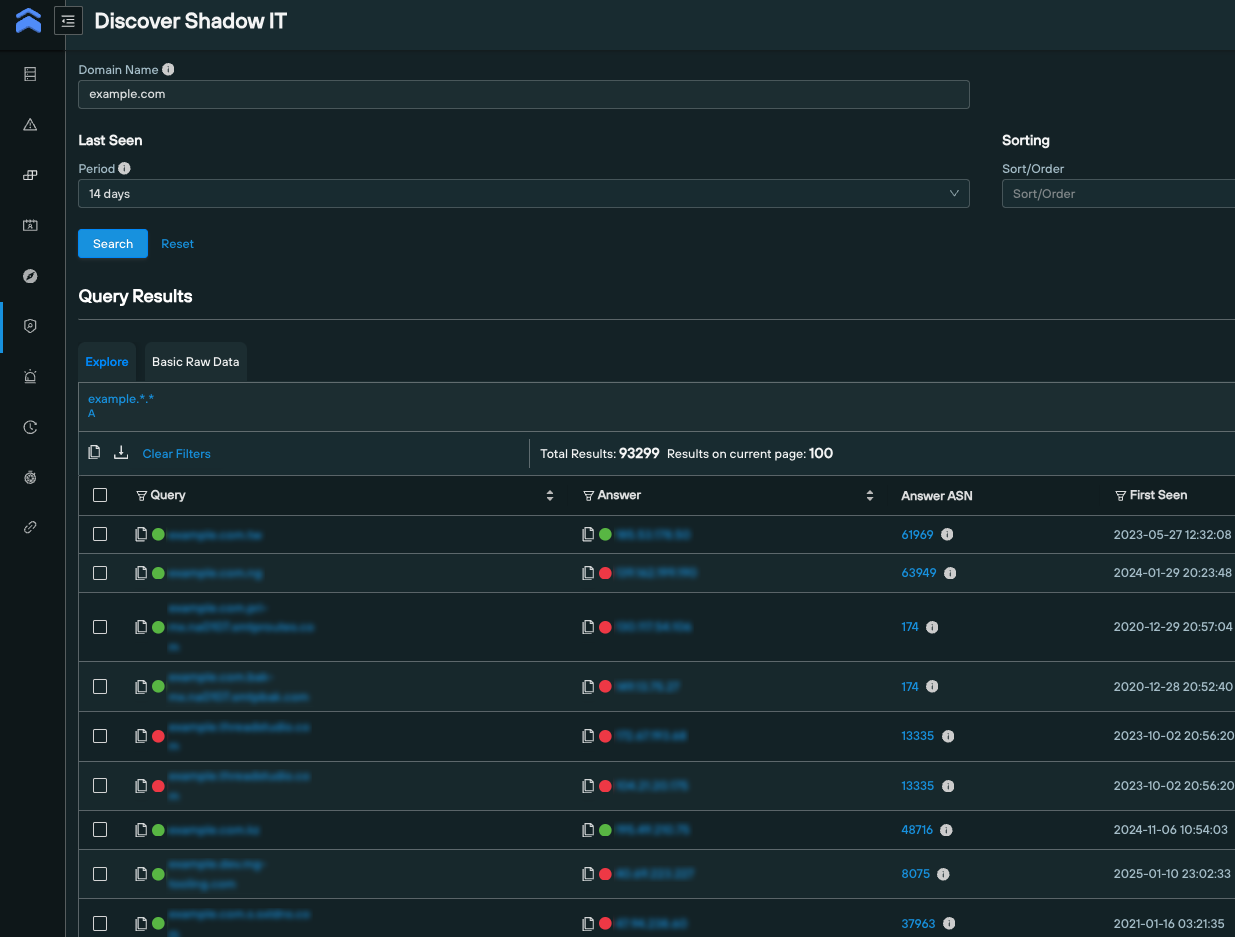
We quickly pivoted across the results for any mention of “Okta”, and discovered subdomains that were not only involved in an emerging attack, but were not on the security team’s radar to begin with.
The organization was able to quickly identify all the linked threat infrastructure, and took immediate steps to close the door on future attacks.
We were also able to improve the organization’s internal workflows by ensuring that the infrastructure team were able to more effectively communicate potential vulnerabilities to the security team, allowing for a better all-around cyber defense posture.
Our team was able to provide the organization with an actionable list of subdomains that their own internal workflows had yet to flag as vulnerable, that did not require additional time-consuming pivots to verify as genuine.
The end result was a new customer, and a happy security team who were able to detect and mitigate what could have been an extremely damaging attack, and gain valuable insight into their public DNS presence that they used elsewhere in their cybersecurity operation.
How were they able to achieve this? Simple. We know more about Internet–facing infrastructure than any other threat intelligence vendor, which gives our customers the ability to fully enumerate any given attack surface or threat landscape.
Not only this, but the platform makes it easy for teams to make critical decisions in high-pressure situations, quickly analyze and validate crucial intelligence datasets, and relay information more effectively between internal teams tasked with protecting an organization’s network.
Find out how Silent Push helps you to locate hidden and known threat infrastructure, and stop digital assaults at source before they occur using Indicators of Future Attack (IOFAs)™ – domain and IP datapoints that preemptively pinpoint adversary intent BEFORE an attack is launched, and reveal searchable fingerprints of attacker activity.
Contact us here for more information.
We’ve published extensive research on Scattered Spider APT activity that uses Okta in the attack chain to steal data and propagate all of attacks using compromised credentials.
Click here to read our blog.
Silent Push analysts have been tracking North Korean hacking groups for years. We share private feeds and reports with clients, doing our best to make details public whenever it won’t compromise ongoing tracking efforts.
Our most recent research focused on the Lazarus subgroup Contagious Interview, also known as Famous Chollima. We explained there how we acquired some of their infrastructure, including log details from both the malicious operators and their victims.
Within these logs, we saw numerous references to a virtual private network (VPN) called “Astrill VPN” (astrill[.]com) that we have been tracking for some time.
We soon heard from several research sharing partners, who separately confirmed both Contagious Interview’s usage of Astrill VPN and the DPRK Fake IT workers’ continued use of this provider.
For months, it’s been public that attackers from Lazarus Group—from several of their subgroups—prefer to use the Astrill VPN to obfuscate their location during attacks.
Google’s Mandiant released details on September 23, 2024 about the DPRK fake IT worker threats and noted, “Connections to these remote management solutions primarily originated from IP addresses associated with Astrill VPN, likely originating from China or North Korea.”
And more recently, in February 2025, Recorded Future’s Insikt Group released additional details on DPRK IT worker scams, writing, “Insikt Group tracks PurpleBravo (formerly Threat Activity Group 120 [TAG-120]), a North Korean-linked cluster that overlaps with the “Contagious Interview” campaign, which primarily targets software developers in the cryptocurrency industry. …Insikt Group found evidence that PurpleBravo uses Astrill VPN to manage its command-and-control (C2) servers.”
Register now for our free Community Edition to use all of the tools and queries mentioned in this blog.
Silent Push Threat Analysts found a domain registered hours before the $1.4 billion ByBit heist – “bybit-assessment[.]com” – which had WHOIS records showing the email address “trevorgreer9312@gmail[.]com,” was used to register the domain. That email address had been found and documented in Tayvano’s GitHub repo, “BlueNoroff Research,” which is the public name of another Lazarus APT subgroup.
Details from Tayvano’s “BlueNoroff Research” folder also include two Astrill VPN IP addresses that were apparently used in the attack: “104.223.97[.]2 (an Astrill VPN IP), and 91.239.130[.]102 (also Astrill).”
After our team found this new domain that aligned with previous Lazarus research, we were able to make additional pivots (previously described in our public post) to acquire some of their infrastructure, which included admin and victim logs.
Within those logs, our team discovered and then shared 27 unique Astrill VPN IP addresses linked to test records created while configuring their setup, further confirming they heavily favor this VPN.
In this post, Silent Push is sharing a sample list of some active IP addresses in our Bulk Data Feed that are used by Astrill VPN to support ongoing efforts within the community to track VPN tools utilized by North Korean APT groups. Our enterprise users have access to a feed containing many times this number, with more being added in real time as our investigation continues.
Here is the sample list of IP addresses:
Our team continues to track Astrill VPN and will report our findings to the security community as we identify new developments around North Korean and other threat actors utilizing them as a resource.
We will also continue to share our research on threats we discover with law enforcement. If you have any tips about threat actors engaging in criminal activities, our team would love to hear from you.
While not all domains associated with Astrill VPN are malicious, Silent Push believes all domains associated with North Korean threat actors using VPNs – the Lazarus Group in particular – represent some level of risk.
Our analysts have constructed a series of Silent Push IOFA™ Feeds that provide a growing list of Indicators of Future Attack™ focused on scams supported by this technique as well as on North Korean APT groups, which are all available to our enterprise customers.
Silent Push Indicators of Future Attack™ (IOFA™) Feeds are available as part of an Enterprise subscription. Enterprise users can ingest IOFA™ Feed data into their security stack to inform their detection protocols or use it to pivot across attacker infrastructure using the Silent Push Console and Feed Analytics screen.
Silent Push Community Edition is a free threat-hunting and cyber defense platform that offers advanced offensive and defensive lookups, web content queries, and enriched data types.
Click here to sign up for a free account.